Watch this two-part instructional video to begin carving gaming terrain and various art projects out of high density foam. This type of pink foam is called Styrospan. It's easy to carve, inexpensive and can be easily repaired with glue.

Since "The Dark Knight" is basically the biggest movie of all time, and with Heath Ledger's unfortunate death, the Joker is going to be a pretty hot Halloween costume this year, and for years to come. Fortunately, the Joker's makeup can be pretty easily recreated at home.

Scrapbooking is all about using a variety of materials to create different effects. This idea just uses simple household masking tape and watercolor paints. Masking tape can be stuck onto a glass surface or anything else where it can be easily removed, and then painted with watercolor paints. The end result is a really great finish. Watch this video scrapbooking tutorial and learn how to use masking tape and watercolor paints to create a unique look for any scrapbooking project.
This video printmaking tutorial series shows how to easily print out screens and make the screen frames, as well as transfer them onto a t-shirt. Make silkscreened t-shirts for your business or band at home by watching this instructional video.

Many regions in India have their own style of cooking kadhi, a yogurt based curry (or soup). Punjabi kadhi is easily recognizable because it has pakodas, fried dumplings made of chickpea flour. Punjabi Kadhi can be enjoyed with plain white rice or chapati. Try this tangy and delicious recipe for Punjabi Kadhi.

Watch this software tutorial video to learn how to use the Quick Look feature on Mac OS X Leopard to preview files very quickly. Mac OS X Leopard's Quick Look feature will be easy to use after you've watched this how-to video.

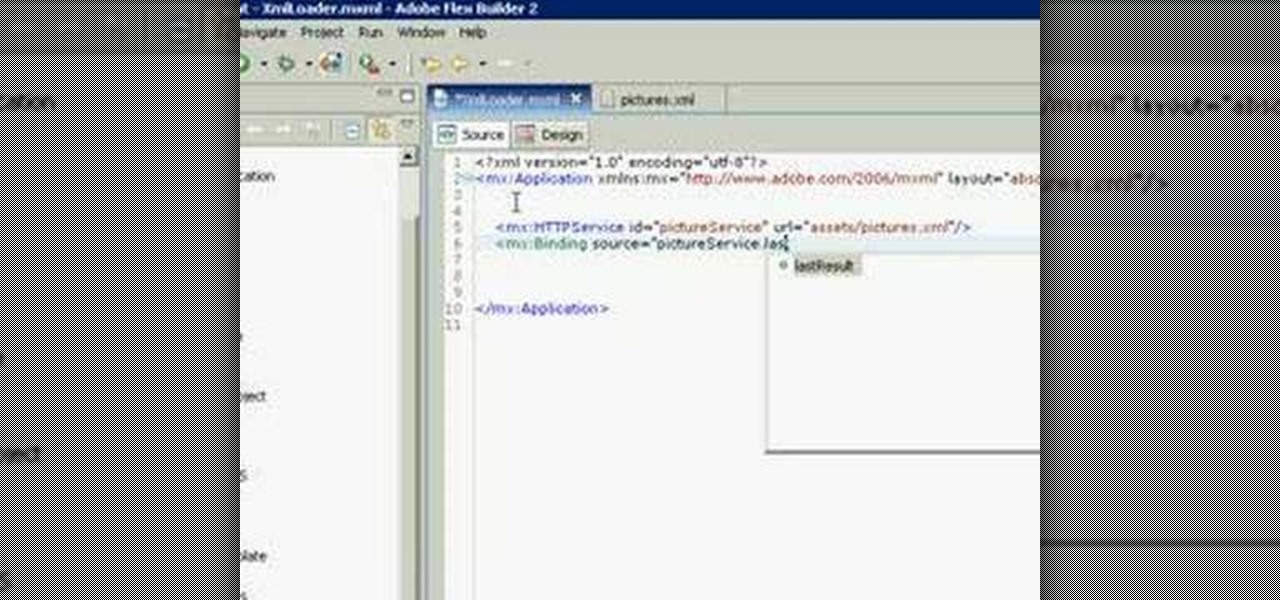
This XML video tutorial will show you how to bind an XML file in MXML in about ten lines. First you'll want to create a Flex project in Adobe Macromedia Flex Builder 2, then create an assets folder and a new XML file in MXML. Coding doesn't get any easier than this. Just watch and learn.

Follow along and see how easy it is to actually do a purl stitch! Anyone can learn to knit and it's a great craft to know if you want to give handmade gifts! This how to video tutorial will show you another stitch commonly used in knitting. It is created assuming you already know the basics of knitting. By combining the knit and purl stitches, you can create a wide variety of stitch patterns.

This video tutorial shows how to download .cut files onto Cricut software to design cards. Learn how to use this card making software, and get instructions for how to make a strawberry greeting card.

If you own a BlackBerry or any other wireless phone, then why not install the application Yahoo! Go! on it?

Learn how to get started in Photoshop Elements by importing digital photo files from your files and folders or off of CDs.

There's an easy way to get huge files with very little degradation to the file by using a little known secret in photoshop. Check it out in this video.

This walks you through how to create an animated GIF image file that can be used in websites, as avatar's, as icons, etc. You'll be using Microsoft Paint to create each frame of the animation, and an application called Unfreez (found here) to animate them together.

This is a tutorial on how to edit type in a layered file and a flattened file in Photoshop.

This experiment is intended to introduce students to hydrated compounds. These compounds have water molecules coordinated in their chemical structures. Examples CuSO4*5H2O, BaCl2*2H2O, and NaC2H3O2*3H2O.

In this video, you'll discover how to upload files to your own website or blog using FTP.

In this video tutorial we will take a look at how to import files into DVD Studio Pro. Do note that it is recommended to render your movies into a compatible format before importing to DVD Studio Pro. The author suggests to use Compressor to do the job.

Tired of wet and sloppy salsa full of watery tomato seeds? Learn how to remove the seeds and dice a tomato quickly and easily.

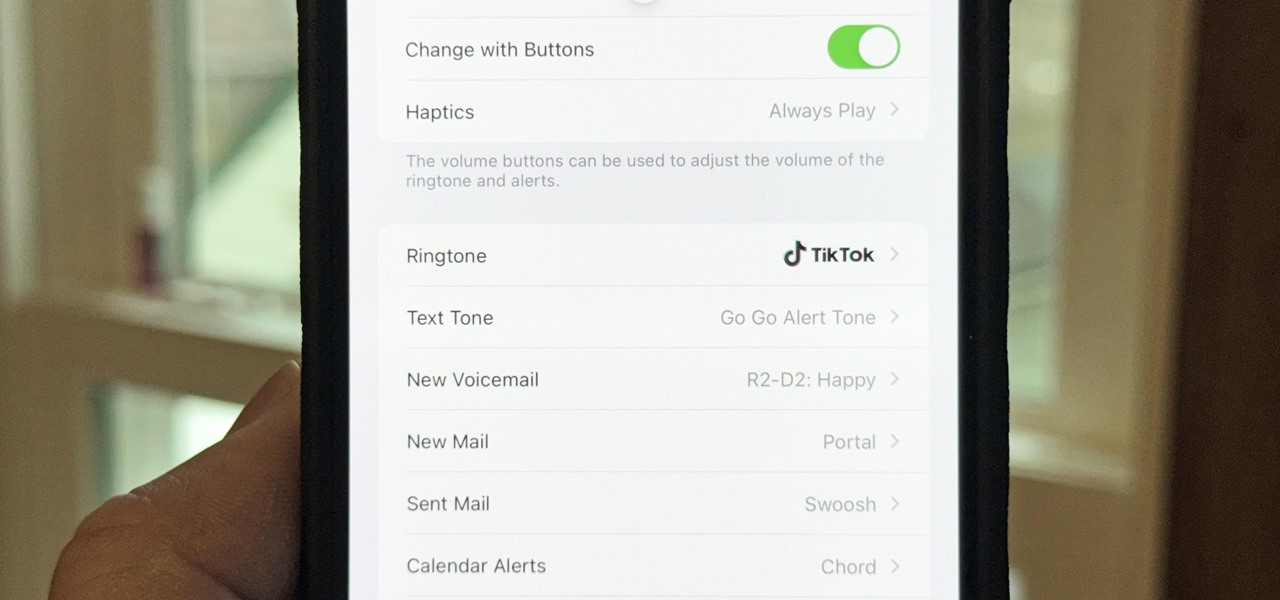
There seems to be no end to all the viral TikTok sound bites and trending TikTok songs, and there's a good reason why they are ingrained in the fabric of our pop culture. TikTok's short audio clips can evoke laughter, tears, and a wide range of other emotions, and many of them just happen to be the perfect length to add to your iPhone's or iPad's arsenal of ringtones.

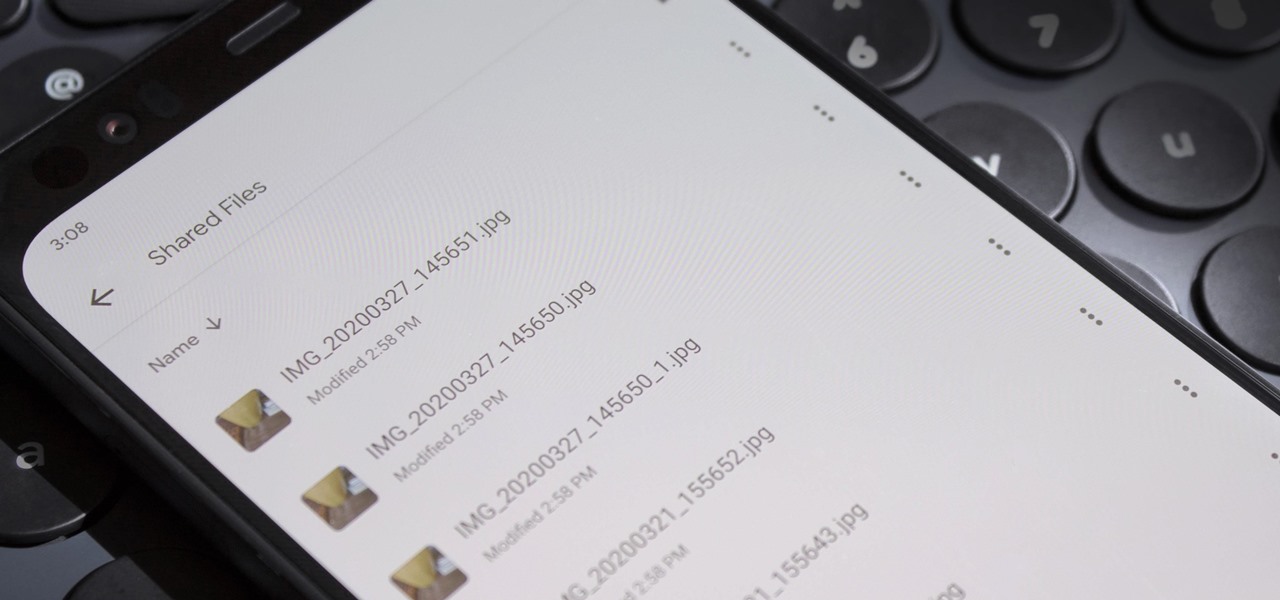
If you're not using your iPhone's Files app yet to manage images, documents, and other files on iCloud, third-party cloud services, or your local storage, it's time to start. Apple's built-in file manager is finally a powerhouse with many tricks up its sleeve in the latest software update.

The memories on your devices are precious, even if you don't often get a chance to revisit them. The worst thing in the world is when something happens to your computer or phone, and you end up losing some of those memories because your files weren't backed up or your microSD wasn't fireproof.

If you need to share something online but don't want your personal information attached to the file, use an anonymous file hosting site. By uploading files anonymously, you keep your IP address safe and won't need to create any kind of account that could provide further logging. You can do this in a web browser, but it's much easier to do using a shortcut on your iPhone.

There's an easy way to take your PC to the next level — without any need for a hardware upgrade. The secret is in software that unlocks uses and productivity hacks you never knew you needed. Even better, right now, The Power User PC Software Bundle is on sale for just $59.99. That's 90% off the regular price of $614.

You can easily remove audio from videos in the Photos app on your iPhone, but the same cannot be said about removing video and just keeping the audio track. However, another stock Apple app can help extract the sound clip, and it barely takes any work to set it up.

One of the most promising avenues of attack in a web application is the file upload. With results ranging from XSS to full-blown code execution, file uploads are an attractive target for hackers. There are usually restrictions in place that can make it challenging to execute an attack, but there are various techniques a hacker could use to beat file upload restrictions to get a shell.

I recently picked up a Pixel Slate when Google had a deal going on. I'd been in the market for an Android tablet since the Nexus 7, and this was the closest thing to it. Unfortunately, I soon learned Chrome OS and Android aren't as integrated as I had hoped.

Web applications are a prime target for hackers, but sometimes it's not just the web apps themselves that are vulnerable. Web management interfaces should be scrutinized just as hard as the apps they manage, especially when they contain some sort of upload functionality. By exploiting a vulnerability in Apache Tomcat, a hacker can upload a backdoor and get a shell.

As part of the iOS 11 update, Apple added a document scanner function that creates high-quality digital copies of physical documents, but it was only available inside the Notes app. With iOS 13, Apple has built its scanner right into the Files app, enabling you to quickly create PDFs with your iPhone and do more with them.

TWRP is a name many are familiar with since it allows your Android device to install any custom file of your choosing. You can create a NANDroid backup to keep your data safe or even use Magisk to achieve full root access. In fact, TWRP is often seen as the gateway to modding your system for creating a unique user experience.

The triple camera system on the OnePlus 7 Pro is the best setup they've ever done so far, but it could always be better. The primary sensor packs a whopping 48 megapixels, but as history has taught us, megapixels don't equal better photos by default. In fact, with where we are in terms of hardware right now, it's the software that determines a phone's camera performance.

Metadata contained in images and other files can give away a lot more information than the average user might think. By tricking a target into sending a photo containing GPS coordinates and additional information, a hacker can learn where a mark lives or works simply by extracting the Exif data hidden inside the image file.

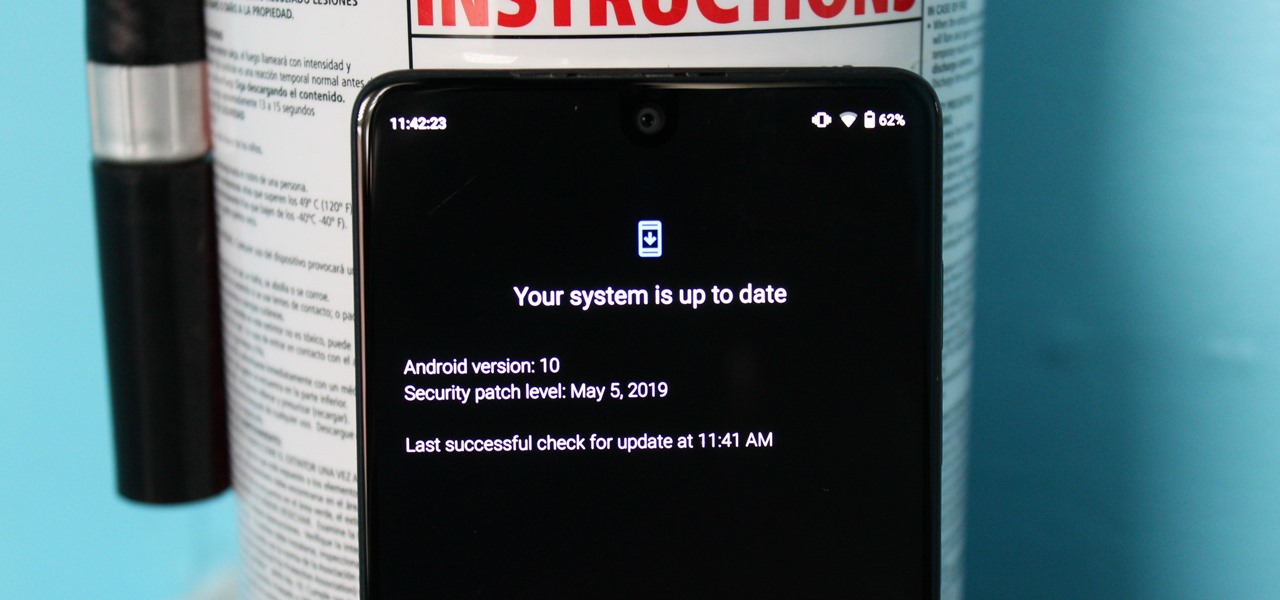
The Pixel 3a came out of nowhere and flexed its muscles to show the industry that you can have a great phone without a hefty price tag. Since Pixel smartphones are first-party devices straight from Google, you can be sure you'll have root access one way or another. For right now the method used to get your Pixel 3a rooted will take a few steps, but they go by real quick.

A hacker with privileged access to a Windows 10 computer can configure it to act as a web proxy, which allows the attacker to target devices and services on the network through the compromised computer. The probes and attacks appear to originate from the Windows 10 computer, making it difficult to detect the attacker's actual location.

Apple's Gatekeeper security software for macOS (Mac OS X) is vulnerable to remote attacks up to version 10.14.5. An attacker that's anywhere in the world can exploit MacBooks and other Mac computers by sharing a single ZIP file.

Every model iPhone since the 6s has boasted a 12-megapixel rear camera. You can take some pretty spectacular, professional-looking photos with it, especially on devices that have more than one rear lens. But the file size of each photo can become a problem when sending as an iMessage, which can eat up data.

Like last year's beta release of Android Pie, Google has allowed the Android Q Developer Previews to support some non-Pixel devices. Announced at Google I/O 2019, there are 15 non-Pixel smartphones eligible for the Android 10 Beta, including 2017's Essential PH-1.

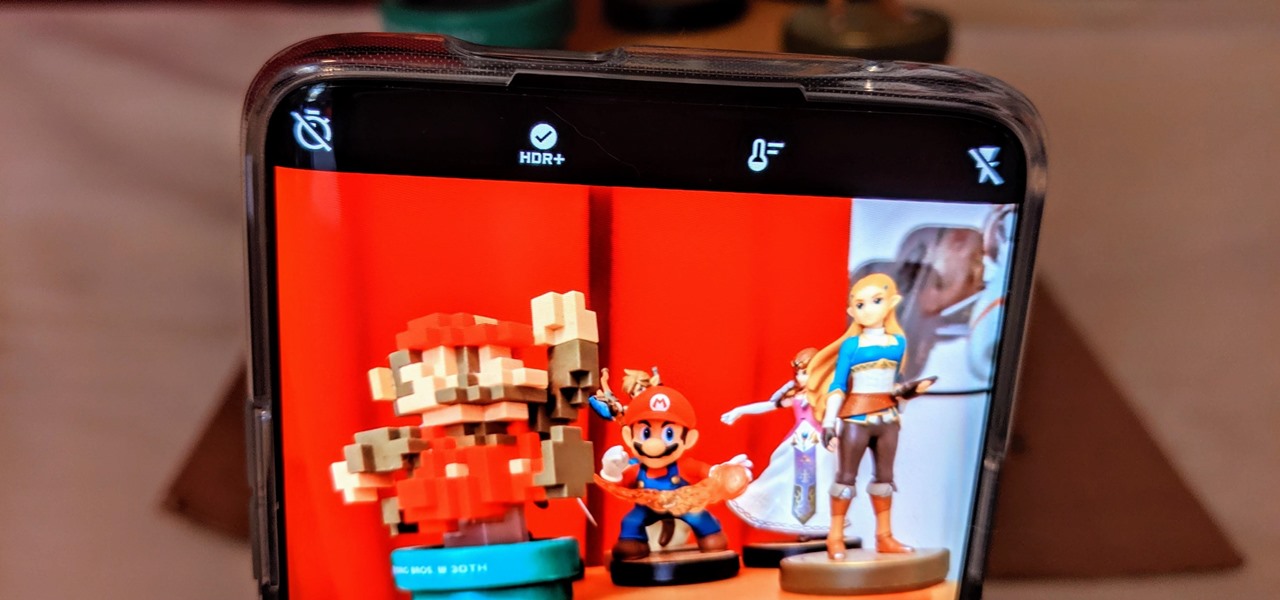
Samsung has stepped up its camera game with the Galaxy S10's dual- and triple-lens systems. But as impressive as the hardware is, the native Samsung Camera app still isn't as good with image processing and video stabilization as the Google Camera app for Pixel phones. Thankfully, you can get the best of both worlds.

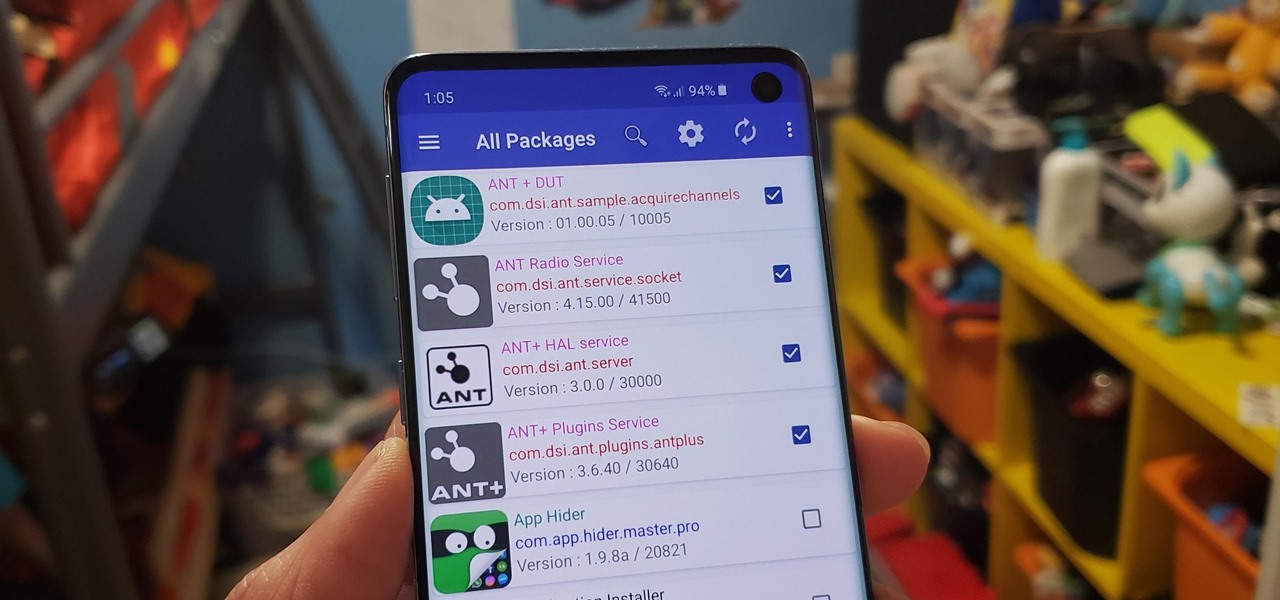
Bloatware remains one of the biggest problems with Android, especially when tied to a carrier. Removing bloatware usually requires you to take extreme measures like rooting. Unfortunately, the Galaxy S10 falls under this annoying umbrella, but there's an easy workaround.

Users are often the weakest link when probing for vulnerabilities, and it's no surprise they can be easily fooled. One way to do this is called clickjacking. This type of attack tricks the victim into clicking something they didn't mean to click, something under the attacker's control. Burp Suite contains a useful tool called Clickbandit to generate a clickjacking attack automatically.

You can easily deck out your favorite phone with great wallpapers, ringtones, and icons, but what about fonts? Not all Android skins let you change the system font, and even when they do, the options are often limited to a few choices. Certain root apps can open up the system font to customization, but some of these can cause problems now that Google introduced a security measure called SafetyNet.