In this Labrats video tutorial the instructors Andy Walker and Seab Carruthers show how to undelete the deleted files and recover them. When you save data to your computer, the computer stores the data in the binary format on the hard disk. To keep track of the files, the Operating System maintains a file table that shows the location of the data on the hard disk for a specific file. There are many file formats like FAT, NTFS etc. So when you are erasing the file only the entry in the file ta...

sorry for no music youtube blocked it i should put a temp music. Cheat engine download link: www.cheatengine.org
http://www.etsy.com/storque/how-to/how-tuesdays-spooky-shadow-puppets-by-crankbunny-2827/
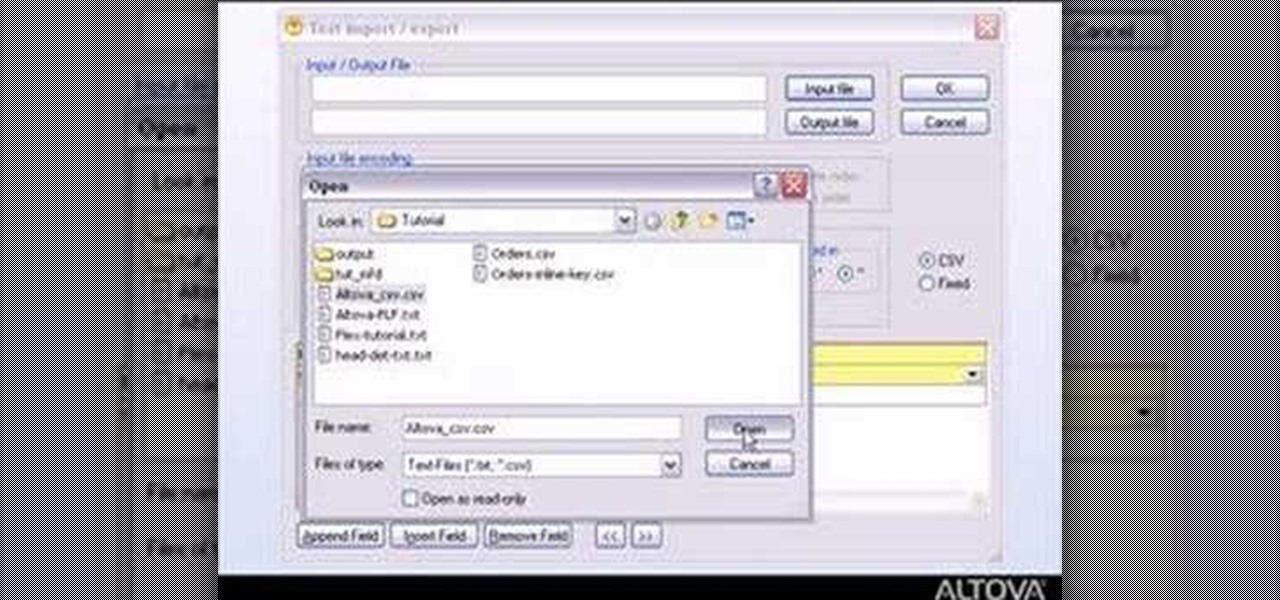
MapForce supports flat files as the source and/or target of any mapping involving XML, database, EDI, web services or other flat file data. In this how-to, you'll find instructions for mapping data from arbitrary text files (such as log files, CSV, fixed-width, and other legacy data sources) to databases and XML files.
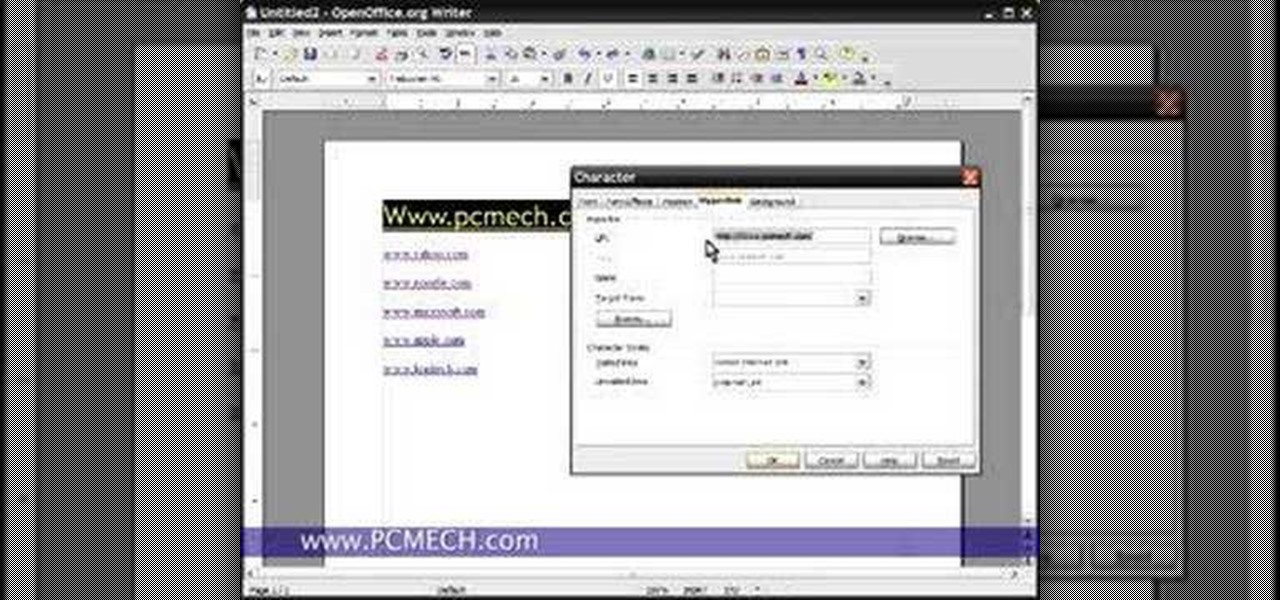
Wondering how to handle links, or hyperlinks, in OpenOffice Writer? This tutorial will show you how to create, edit, remove and navigate to hyperlinks in the OpenOffice word processor. Take a look.

You can obtain the magic hammer earlier than the game intended by using the mirror glitch. Take a look at this tutorial and learn how to use the mirror glitch to get the hammer item in Zelda: A Link to the Past.

In Zelda: A Link to the Past, the Cane of Somaria (a recurring item in the Zelda series) could not traditionally be obtained until later in the game in the Misery Maze dungeon. Take a look at this instructional video and learn how to get the Cane Somaria early on with the mirror glitch. This trick does not work on the Super Nintendo console, only on the emulator and the Game Boy Advanced.

This tutorial electronics video will show you how to use CuteFTP pro correctly, I use it in a few of my videos so it's good to know.

Bill Myers shows how to quickly create 'retail ready' DVD case and box covers using free Photoshop Elements template.

In this video I show you how to get a Flash plugin to allow you to play videos in safari. Your iPhone/iPod Touch does not have to be jailbroken to do this. If you are having problems not getting the email make sure you look in your bulk or spam folder of your email. Just click the activation link in the email refresh the safari page and everything should work.

A tutorial on how to secure and configure a WRT54G Linksys router and also the steps needed to get default passwords and the list link.

Ted from Red Digital, and Michael from PlasterCITY, shows how to take a 4k source file, edit in real time, and make dailies in Final Cut Pro.

In this video, D.Lee Beard reviews two products: the Epson R280 6-color inkjet printer which can print on CDs and DVDs as well as 8.5 x 11 paper, and a review of the Kensington 19-in-1 Media Card Reader. He also explains how to find free books online, and viewer questions are answered on video instant messaging, and mac compatible mp3 players. Be sure to check out our http://AsktheTechies.com web site, Episode 71, for links to items discussed in this video.

This guitar lesson demonstrates how to play the recorder/keyboard intro to Stairway to Heaven as I have transcribed it on guitar. Tabs for this lesson are available on my guitar lesson website, on the "NEW STAIRWAY TO HEAVEN VIDEO" link:

It's no secret that Apple's Notes app supports attachments such as photos, videos, and web links, as well as other file types like PDFs, word documents, spreadsheets, locations on a map, and audio tracks. While images, videos, and document scans are simple to add on an iPhone or iPad, other file types aren't as easy — at least until you know how.

Apple's exclusive chat services, iMessage and FaceTime, force many of us to stay locked into iOS, iPadOS, and macOS to communicate with other Apple users, so chatting with Android-using friends means SMS texts, third-party messaging apps, and third-party video chat services. However, Apple is breaking boundaries with iOS 15 so that we can FaceTime with Android, Linux, and Windows users.

Post-exploitation is often not quite as exciting as popping the initial shell, but it's a crucial phase for gathering data and further privilege escalation. Once a target is compromised, there's a lot of information to find and sift through. Luckily, there are tools available that can make the process easy. One such tool is Postenum.

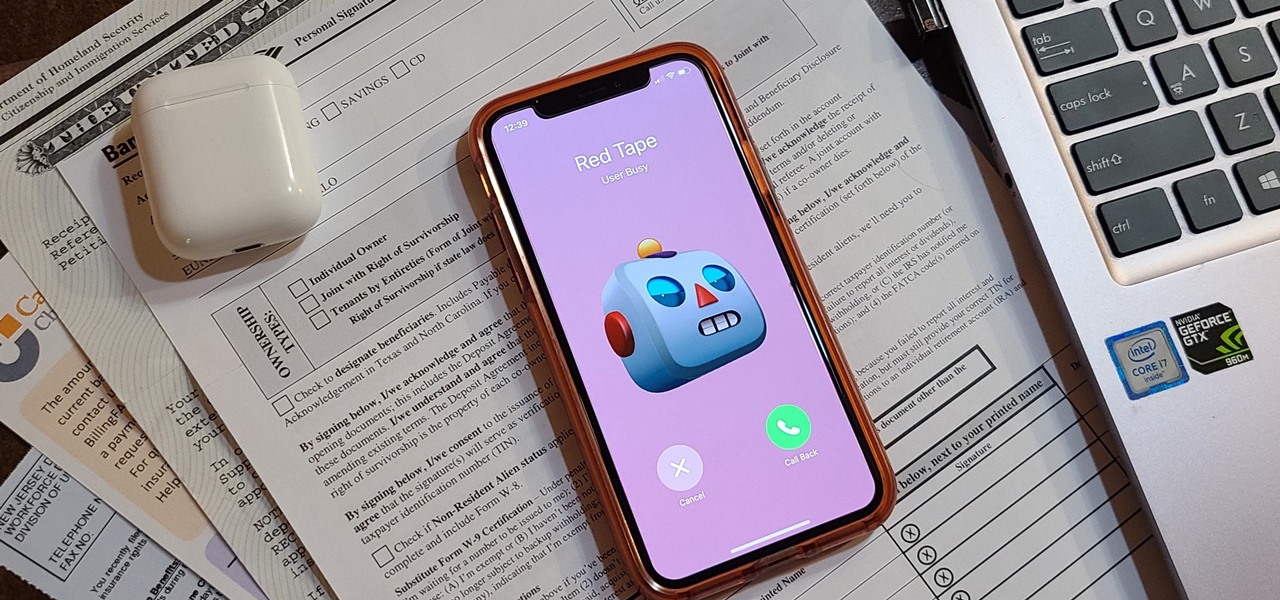
Even under normal circumstances, it's almost impossible to speak to a representative for a government agency or company in just one try. Many systems will put you on hold for long periods or ask to call you back when someone is available, but there are still some out there that just give you the busy signal over and over again. In those cases, there's a jailbreak tweak that can help.

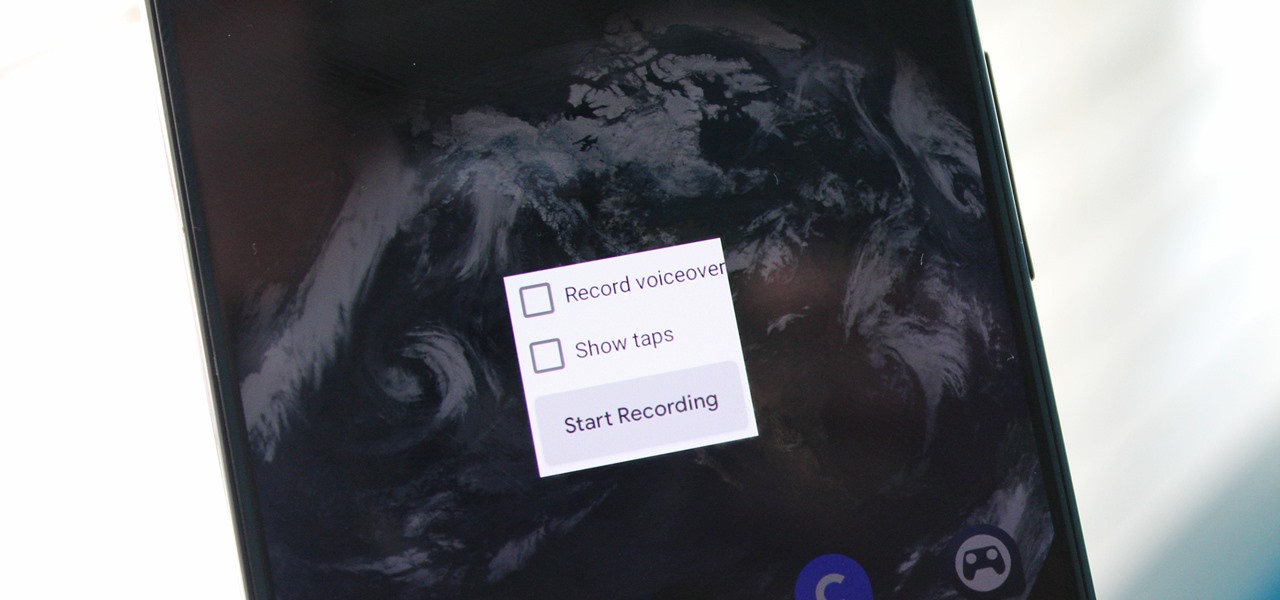
Downloading third-party screen recording apps can be dangerous. The primary function of these apps is being able to record everything on one's display, so it's easy to see how a malicious developer could exploit this for their own gain. That's why the addition of Android 10's built-in screen recording is so impactful.

In iOS 13, Apple finally took the built in Files app from an extremely rudimentary file browser to a full featured app that can serve the needs of most any user. Among the new features is the ability to compress a file or series of files into a standard ZIP archive right from your iPhone.

If you're worried about the security of your Mac, there are easy measures to prevent the most dangerous attacks. Named after the tactic of accessing an unattended computer in a hotel room, we can thwart "evil maid" attacks with Do Not Disturb and LuLu, free macOS tools by Objective-See that keep an eye on unattended computers and flag suspicious network connections that indicate a malware infection.

The Windows 10 desktop and microphone can be livestreamed without using Remote Desktop Protocol (RDP) software and without opening any ports on the target computer. A hacker with low user privileges can monitor and exfiltrate a target's every move and private conversation in real time no matter where they are. Hackers are watching and listening, and there are few ways to protect yourself.

The Android 9 Pie update brought a lot of visual changes, some of which are a little too reminiscent of iOS. There's the new gesture controls, which are okay, but then there are things like a left-justified clock and the fact that the recent apps menu now scrolls horizontally instead of vertically. Luckily, Samsung has given us a way to bring back the classic Android style.

Switching phones has never been easier. Google backs up most of your app data on the cloud, which can then be restored onto your new phone. Sadly, Signal doesn't use this feature since it could compromise your security. Instead, Signal stores encrypted backups locally, requiring a bit of work to restore these messages.

With the release of Android 9.0 Pie, Google's focusing on digital health. Digital Wellbeing is a new set of features designed to help you curb your own smartphone addiction. Starting now, the beta version is available, and Google's looking for testers.

Getting root is considered the Holy Grail in the world of Linux exploitation. Much like SYSTEM on Windows, the root account provides full administrative access to the operating system. Sometimes even a successful exploit will only give a low-level shell; In that case, a technique called privilege escalation can be used to gain access to more powerful accounts and completely own the system.

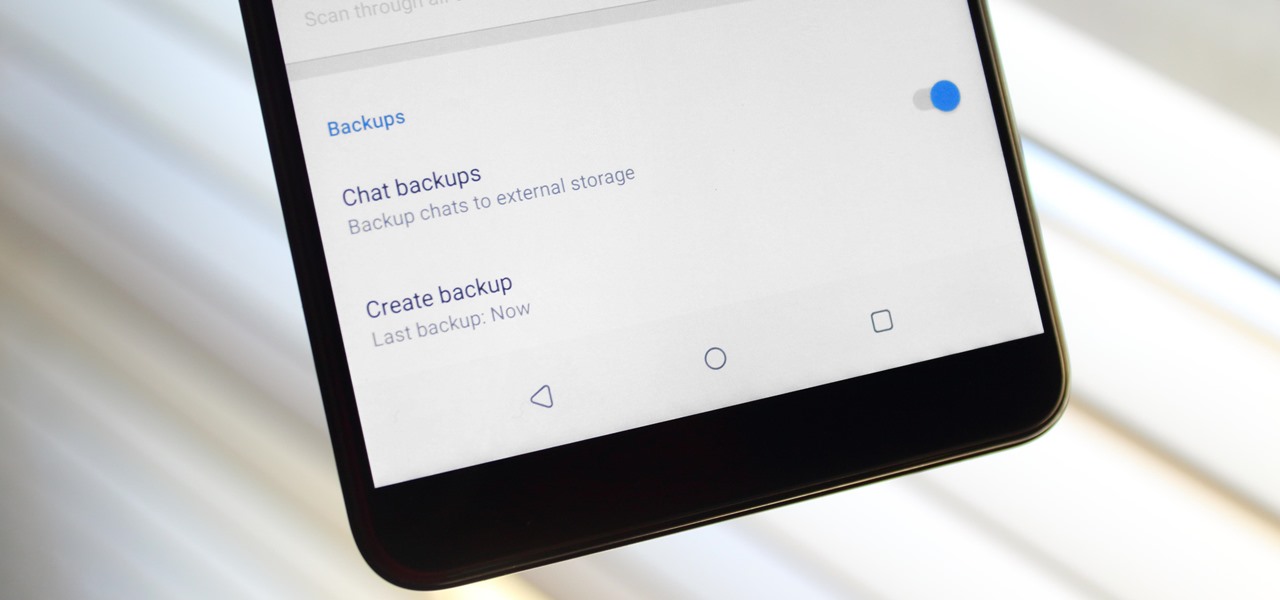
It always helps to be prepared for the worst. This applies to our phones now more than ever, as we depend on them to be our record keepers for text messages from friends, family, and coworkers. If you ever lose or severely damage your phone, having a backup of your precious texts gives you the peace of mind of knowing that you can always get them back.

Earlier this year, with the Developer Preview, we got a tantalizing glimpse of Google's upcoming Android 9.0 Pie and a whole slew of new features that comes along with it, such as iPhone X-like gestures and improved security features, to name a few. With its announcement at Google I/O, Android Pie just got a lot more accessible.

As you're surely aware, your phone can be used against you. Thanks to our cameras and microphones, a clever hacker can obtain access to your device and invade your privacy. But spying isn't limited to just these two sensors — gyroscopes, proximity sensors, QR codes, and even ads can be used to paint a very clear picture about who you are and what you're currently doing.

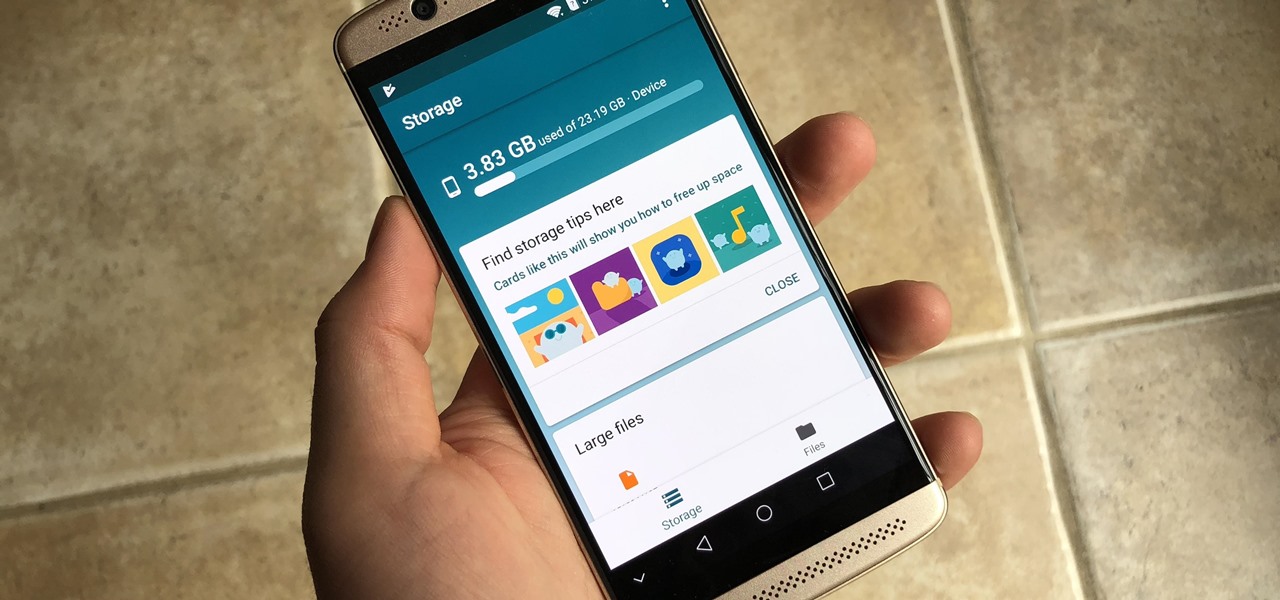
There may be many third-party file managers for Android to choose from, but until now, Google offered no proprietary option. Enter 'Files Go,' which, while initially anticipated for December, is now available for you to try.

When it comes to streaming services, Google Play Music is one of the best options for both Android and iOS. Perhaps its single greatest feature is the fact that you can upload as many as 50,000 of your own songs to Google's servers, then stream your library to any device without ever paying a dime.

When it comes to modding Android, root gets all the glory, but a good custom recovery is really the only thing you need. Not only does it allow you to back up your entire phone, install flashable ZIPs, and load custom ROMs like LineageOS, but a custom recovery will even let you root your device. For years now, the only custom recovery worth mentioning has been Team Win's TWRP.

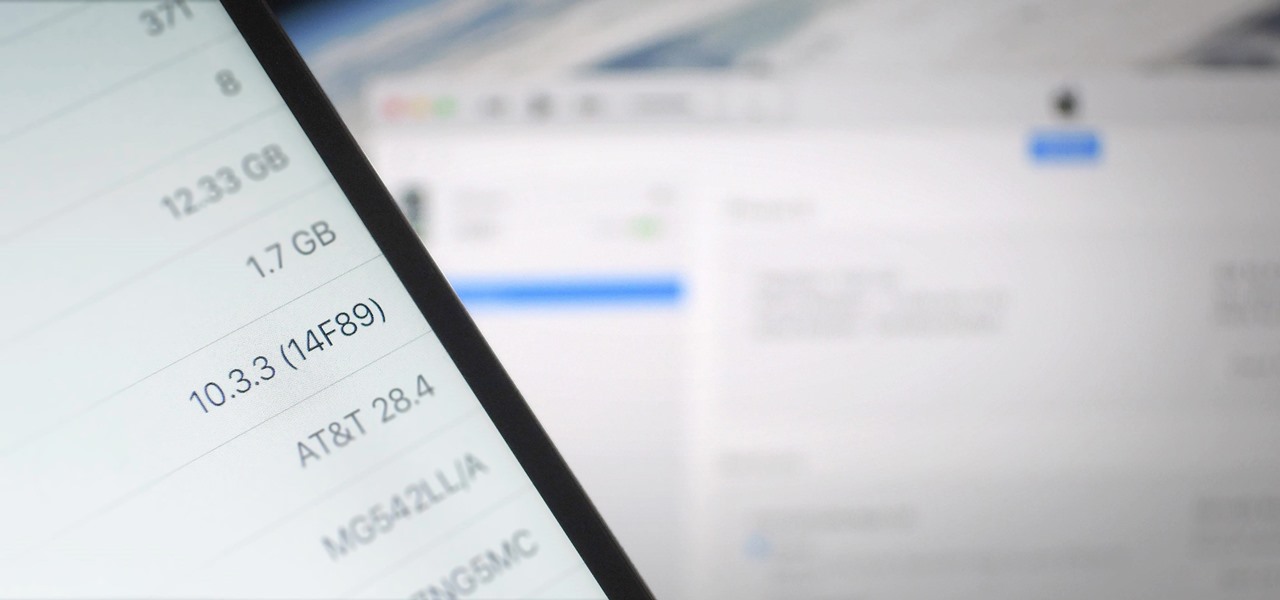
There's lots of new stuff in iOS 11, but just because things have changed doesn't mean they're better. So if you've updated to Apple's latest OS and decided it wasn't for you, you'll be happy to know that you can still go back to iOS 10.3.3.

The Shadow Brokers, a hacker group known for its dump of NSA hacking tools in 2016, has just leaked their remaining set of data which implies that the NSA compromised SWIFT, the global provider of secure financial services, to spy on banks in the Middle East.

The internet's an amazing place. The entirety of human knowledge is now accessible in an instant, and all sorts of media can be streamed directly to the palm of your hand. But, of course, that also includes the darker side of humanity, so there's plenty of NSFW content floating around out there that's certainly not suitable for children.

When it comes to modifying Android, the single, most powerful tool available is TWRP custom recovery. It's even more capable than simple root access when it comes to changing the look and feel of your software, and you can even use TWRP to root your device in a few simple steps.

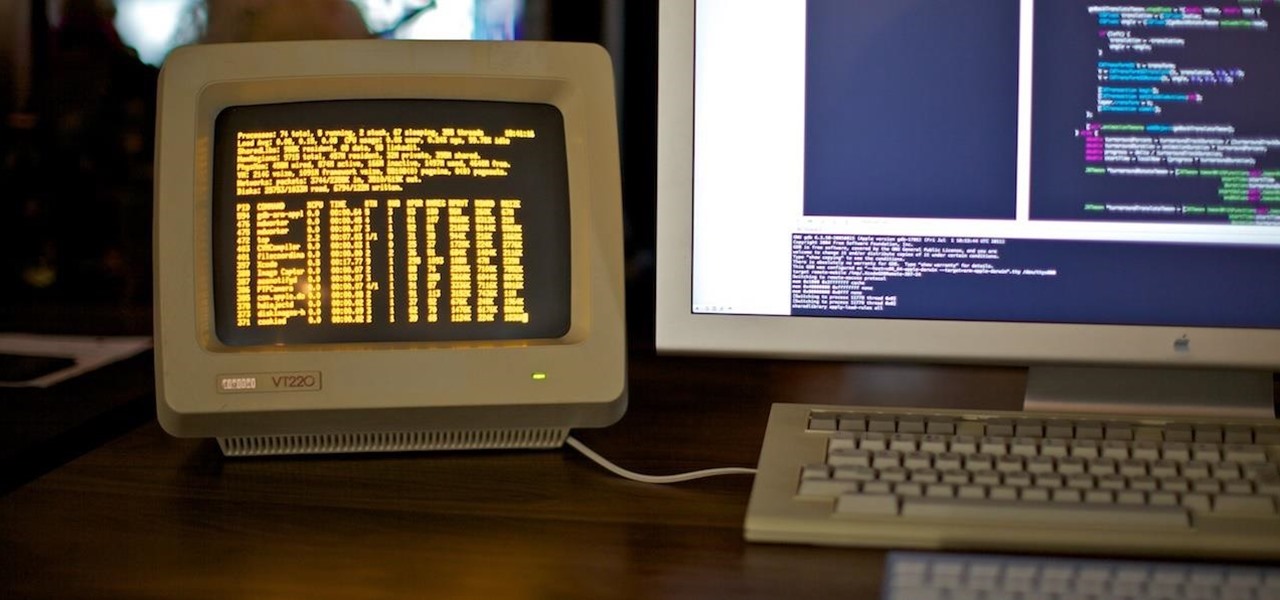
Now that we've talked about encryption and managing your passwords, let's continue this series on getting your Mac ready for hacking by turning our attention to the terminal.

Google makes Android, but now, Google makes its own phones, too. Until this point, they've always stayed on the software side of things and let Samsung and friends handle the hardware, but their new Pixel phones are changing all of that.

Google has already issued a few updates to Android 7.0 Nougat. There aren't many headlining features, as these minor updates are mostly bug fixes and performance improvements. But there's a few security enhancements as well, so staying up-to-date with the latest patches is important for a number of reasons.

This card is stunning and has lots of texture and a mix of items to make it unusual but still easy to create.