
How to Train Your Python: Part 16, Basic File Input and Output
Welcome back! In the last training session we covered how to write and execute scripts. But today we'll be getting back to the code!


Welcome back! In the last training session we covered how to write and execute scripts. But today we'll be getting back to the code!

Hello readers, in this tutorial, we will be discussing how to perform file operations such as reading and writing.

This is my first How-To on Null-Byte, so I hope it's not too complicated written, because I am not a native english speaker. I don't use pictures, but this Tutorial is a good supplement for my updated Tutorial here.

Hello everyone. I've recently made the annoucement of the Null Byte suite of tools, and we've covered how to download and install it. Now it's time we cover how to submit a tool for inclusion into the suite. It's relatively simple, but we need to get a few ground rules out of the way.

Welcome back, my nascent hackers! In the conclusion of the Mr. Robot television series, Elliot and fsociety successfully completed their mission of encrypting all of Evil Corp's data with AES-128 encryption and destroying the key.

When using Linux, we often need to install new software, a script, or numerous large files. To make things easier on us, these files are usually compressed and combined together into a single file with a .tar extension, which makes them easier to download, since it's one smaller file.

This year, Google released two Nexus phones to glowing reviews, and as we've grown to expect, the Android community wasted no time in coming up with a root method for both. In fact, legendary root developer Chainfire even devised an entirely new "systemless" method for rooting that should make updating a bit less complicated, along with a few other benefits.
In this tutorial I am going to show you how to change some file metadata, this could be very useful if you want to edit or access a file and remove any evidence of your changes.

Greetings dear null byters, today we start a new series, we will start to attack users using social networking that are popular such as Facebook, Skype, and much more, and in part 1 of the series will engage users of Skype.

For years, we've had to download third-party apps if we wanted to browse or manage the files stored on our Android devices, but Google has finally included a bare-bones file explorer in Android 6.0 Marshmallow. Only thing is, it's not easy to find—but I'll show you how to access and use it below.

Welcome, in this tutorial we shall we looking at creating a safe(r) way to back up your important files. The contents we will be covering are as follows;
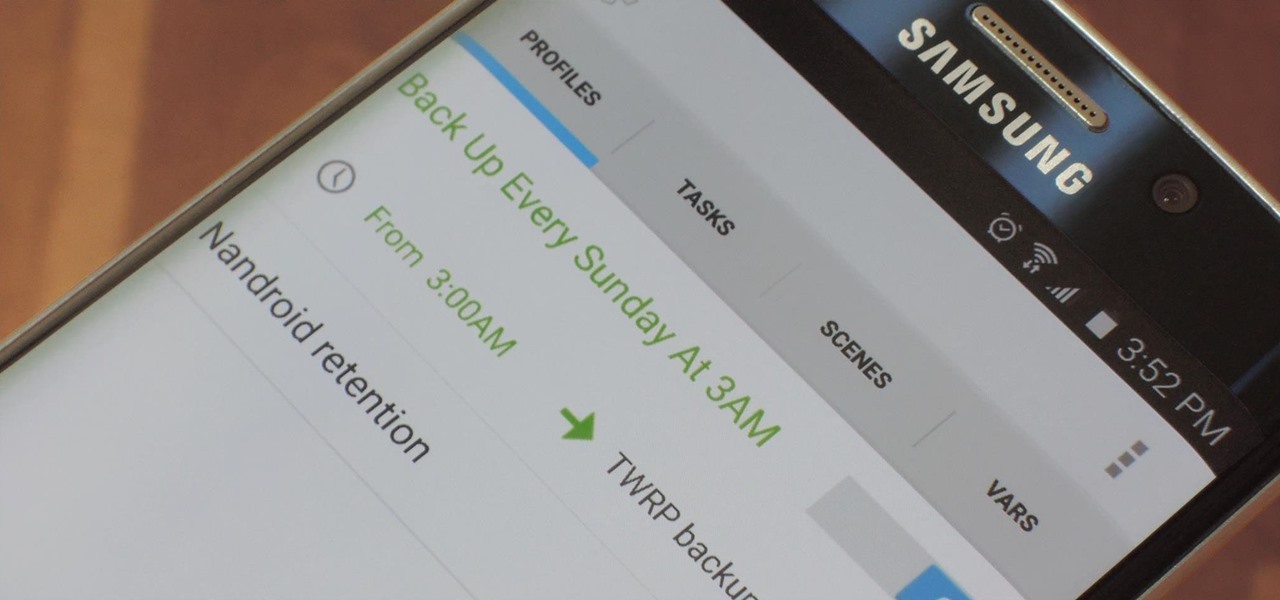
NANDroid backups are one of the best reasons to root your Android device and install a custom recovery. They're essentially a snapshot of your phone's entire operating system and all installed apps, so if you ever screw something up when installing a flashable ZIP or custom ROM, you can restore your NANDroid backup to get everything back to normal.
Hello, Hackers/Viewers! My name is nullf0x, and I have 4 years of experience as a hacker. You might see everyday that one of your friends or acquaintances get a new virus in their computer. You might think, How cool would it be if I made a virus? or How cool would I be if i could remove viruses from others computers for money or free?
If you've ever taken apart an electronic device that uses physical buttons, you already know why these types of input methods are destined to fail. The rubberized contacts used in physical press-and-release buttons like those of a gamepad or keyboard are incredibly frail and can easily wear out over time.

In the About tab, you are able to view the channel's description. Channel owners can add text as well as any links they have added to their account.
The video link included shows in text how I do it from start to finish. The description tells a little more. This particular vase is made of Aromatic Cedar and is 10 inches around.

Apple released the iOS 8 Gold Master build to developers shortly after their WWDC event ended on Sept. 9th, which is jam-packed with tons of new features for iPad, iPhone, and iPod touch. The public version comes out on Sept. 17th, but if you can't wait to test out iOS 8, you can get it right now.

Google has finally announced the newest flavor of its mobile OS, Android L (Lollipop?), and I couldn't be more excited. While we won't see its official release until the fall, there are still some features we can get our hands on right now.

Welcome back, my greenhorn hackers! In my continuing effort to demonstrate to you how to hack the ubiquitous Windows 7, we will going after that notoriously vulnerable Adobe Flash that is on nearly every client Windows system (you are not likely to find it on servers).

Video: . How to Make a Homemade Hamburger

Video: . How to Make Homemade French Fries.
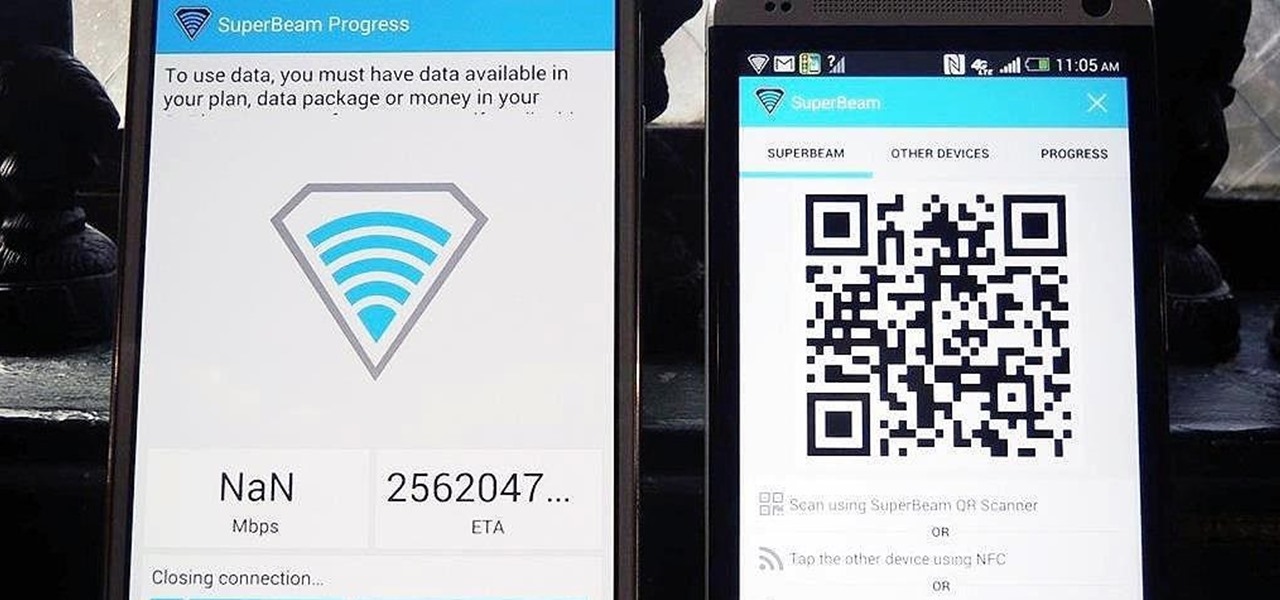
Sending and receiving files between Android devices has no shortage of options—Bluetooth, email, MMS, and Wi-Fi are just a few of the more popular ones that we use.

How to Henna Your Hair Tutorial Pt.2 Please Dont forget to Watch Pt. 1

Video: . How to Henna Your Hair Tutorial #1

Welcome back, my fledgling hackers! Awhile back, I demonstrated one of my favorite little tools, netcat, which enables us to create a connection between any two machines and transfer files or spawn a command shell for "owning" the system. Despite the beauty and elegance of this little tool, it has one major drawback—the transfers between the computers can be detected by security devices such as firewalls and an intrusion detection system (IDS).

While still extremely awesome, the Samsung Galaxy Gear smartwatch is limited as to what you can download on to it, especially apps. It also doesn't have its own internet access (only Bluetooth), so apps like Instagram, Facebook, and Vine have yet to make their way to the Gear Store.

Welcome, my hacker novitiates! As part of my series on hacking Wi-Fi, I want to demonstrate another excellent piece of hacking software for cracking WPA2-PSK passwords. In my last post, we cracked WPA2 using aircrack-ng. In this tutorial, we'll use a piece of software developed by wireless security researcher Joshua Wright called cowpatty (often stylized as coWPAtty). This app simplifies and speeds up the dictionary/hybrid attack against WPA2 passwords, so let's get to it!

The NSA's massive internet spying efforts will continue. In President Obama's latest press conference, he went public to (in so many words) say that the NSA's spying efforts will continue uninterrupted. This, coming just weeks after the Amash Amendment which would have defunded the program, was narrowly defeated in the House (you can check if your congressmen voted against it here).

In this "how to" I will show you how to install every backtrack tools in ubuntu. Video: .

This is a simple yet effective trick with you can impress people and make them laugh. They will never know how is this possible, maybe even you after watching this video and trying it yourself.

This is a video interview how the movie star C. Hemsworth was able to gain a dramatic muscle gain for the movie Thor. just in case you did not see the movie, the actor speaks about his character in the movie and how muscular he needed to be so he can play his role in the movie.
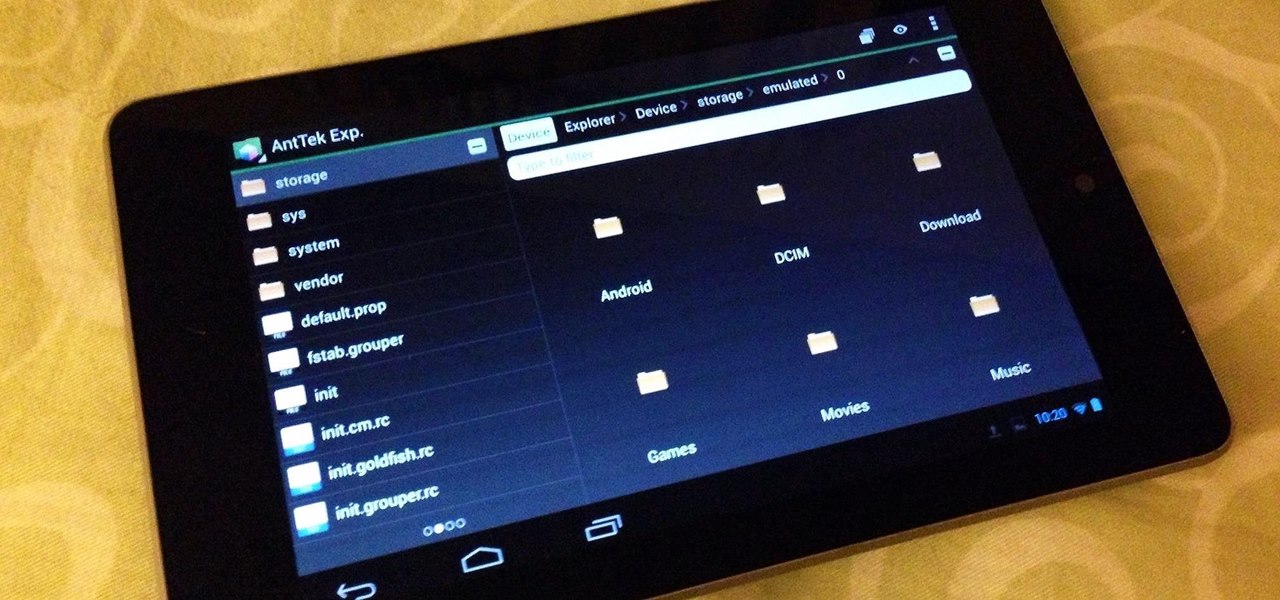
If you're always on the go, the Nexus 7 is a godsend for having everything you need at the tip of your fingers—music, videos, text documents, photos, and more. Unfortunately, as good as that is, it also means one hell of a messy tablet.

While many of the U.S. carriers have updated their Samsung Galaxy S3 devices to Android 4.1.2 already, one major absence from the upgrade is Samsung's Premium Suite. One of the coolest features from the Premium Suite is Multi-View, a function that lets you truly multitask by running two apps at the very same time—right next to each other. As you can see above in the left image, I have both Pandora and Spotify running. Why? Because why not?!? On the right, I have YouTube on top and Maps on the...
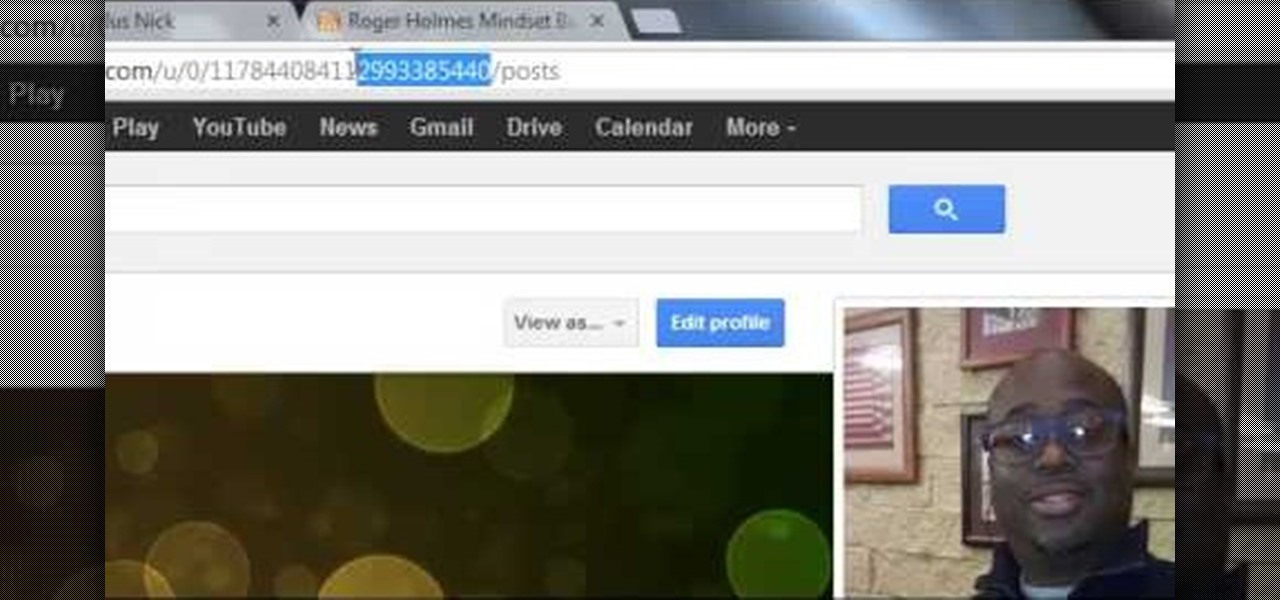
This how-to is for those of us who frequently use Google+ to connect with others, and want to have a better looking link for our profiles.
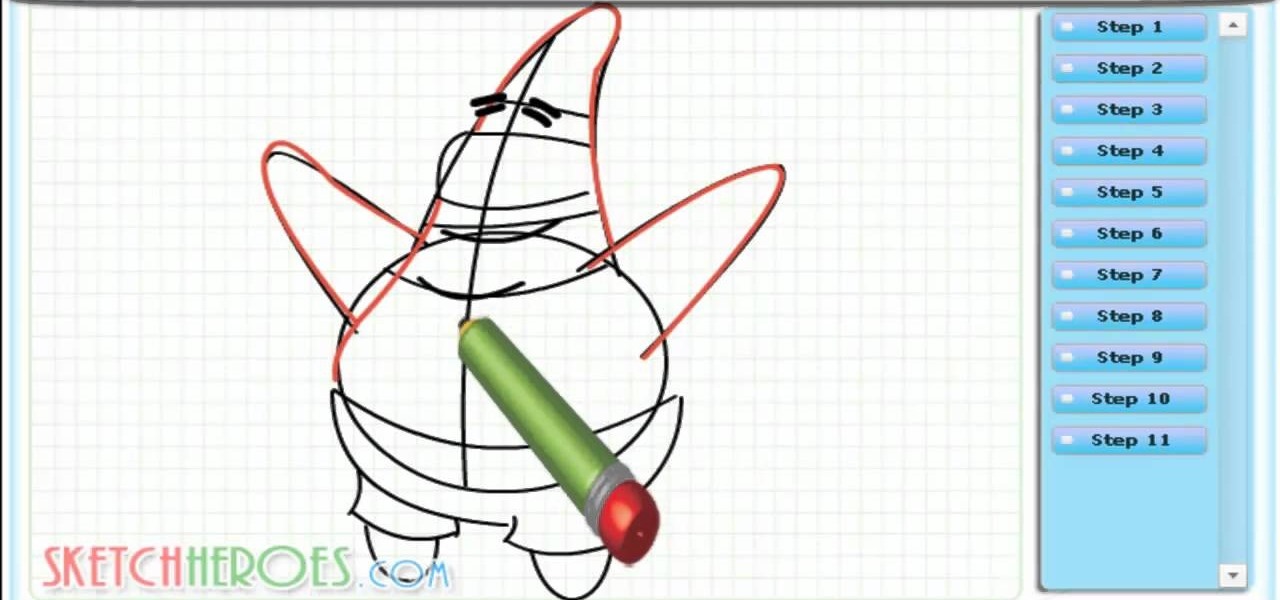
Learn How to draw -Patrick- from (Sponge Bob) with the best drawing tutorial online. For the full tutorial with step by step & speed control visit: how to draw.

There's really nothing safe about transmitting sensitive information electronically, but even if it gets there safely without being seen by prying eyes, there's no guarantee what happens to it once it reaches its destination. And let's face it, there are some things that you just don't want floating out there forever. So what can you do? Whether you want to send an email, a text, or a link, there are ways to send messages that self-destruct so that once they're read, they immediately vanish. ...
Learn link text with the best drawing tutorial online. For the full tutorial with step by step & speed control visit: how to draw.
Learn How to draw Katy Perry with the best drawing tutorial online. For the original tutorial with full control over the speed and steps please visit: how to draw.

Learn How to draw Kick Buttowski with the best drawing tutorial online. For the full tutorial with step by step & speed control visit: link text
Learn how to draw Alucard (Adrian Farenheights Tepes link text the easy way. Adrian had special powers, preordained to be stronger than any human but not potentially as strong as his father especially in the dark arts. For the full tutorial with step by step & speed control visit: how to draw.