It's Monday, which means once again, it's time to highlight some of the recent community submissions posted to the Math Craft corkboard. I also thought that we'd try and create something known as an "Orderly Tangle" or "Polylink".

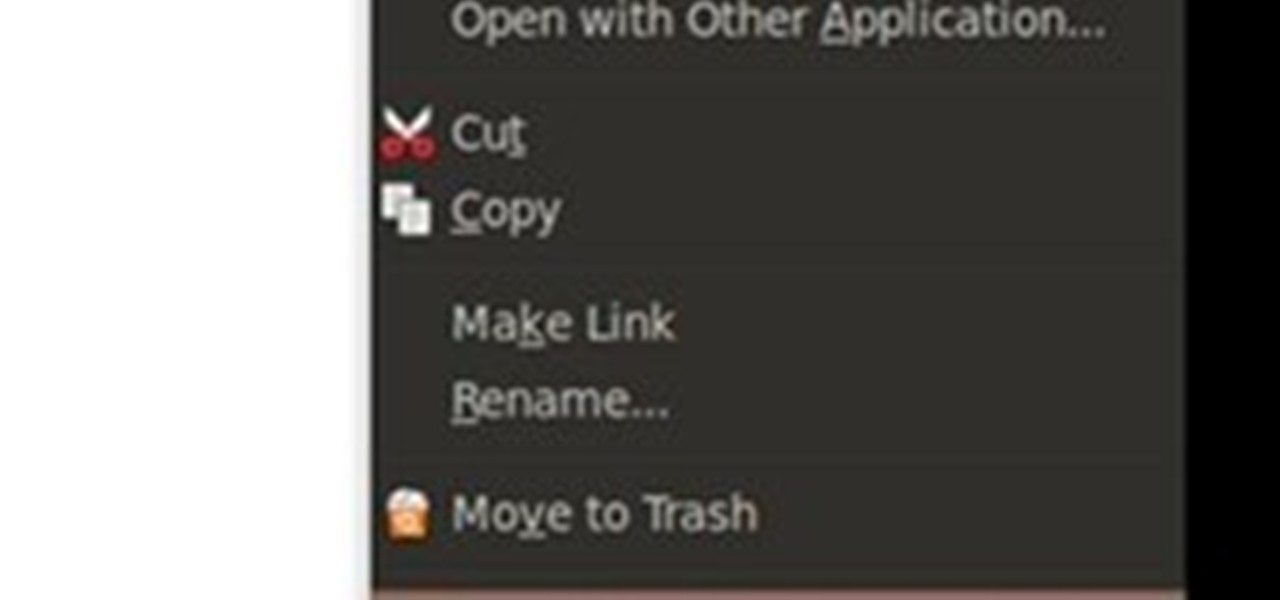
File recovery on Linux is a bit different than Windows. It requires different software than the Windows counterparts because every OS has their own file system. Windows uses NTFS, or FAT file systems, while on the other hand, Linux uses ext-based file systems. I personally use ext4 file system because it's the latest and greatest ext-journaling system and supports a large level of directory recursion and file sizes, but most installations still use ext2 or ext3. When files are deleted from a ...

Everyone has deleted a file or folder on accident before. Sometimes people even delete stuff on purpose, only to find out that they needed the files after all. If you're experiencing one of these mishaps, don't worry, file recovery is possible in most cases!

eBooks are an amazing thing, especially with Amazon's Kindle. What's irrtating about eBooks as that you have an infinite selection of books at your fingertips, but they all cost so much! Well, as always, Null Byte has a trick up our sleeves for nabbing free ebooks from Google.

A proxy is a server that lets a client to connect to it and forward its traffic. This enables a certain "layer" of protection by masking your IP. An IP address can be used to learn your location and track you on the Internet, thus eliminating any form of anonymity that you may have.

In this Null Byte, I'm going to teach you about Null Byte Injections. Null Bytes are an older exploit. It works by injecting a "Null Character" into a URL to alter string termination and get information or undesirable output (which is desirable for the malicious user).

If you've gained entry into Google+, one of the first things you should do is adjust your Google account settings. Your settings will now look quite different, and you can adjust your notifications, password retrieval methods, and more. There are many settings that you may not have been aware of before.

You've finally got an invite into Google+. Now what? At first glance, things can be a bit overwhelming. We've got some great tips to help you get started.

This article describes the very basics of compiling a program on Linux. It is targeted at the absolute beginner. Sometimes beginners search for programs on the web for their Linux systems, and is faced with the reality that they have to compile the program themselves, either because there exists no binary for their architecture, or the author of the program just doesn't release any binaries at all, but only sources.

Spam is everywhere and Facebook is no exception. In fact, spammers are constantly stepping up their game by tricking unsuspecting Facebook users to participate in quizzes, games, apps, or "new features" that are actually dangerous computer viruses, spyware, or other trojan horses in disguise. Their attempts even trick people into unknowingly becoming spammers themselves.

While a lot of internet threats are rather over-hyped, there are some serious things to be cautious of when going online. Probably the biggest risk to the average internet user is malicious software. Commonly knows as "malware," this term refers to any program that exists solely to do harm. This may include damaging your computer or accessing your data without you knowing. Viruses, trojans, and spyware are all forms of malware. Now, malware can seriously mess up your system, and the idea of s...
Type: Photography, no visual or graphic art manipulation or HDR Theme: Show Off Your School™
Type: Photography, no visual or graphic art manipulation Theme: Streetscape

Type: Photography, no visual or graphic art manipulation Theme: World's Cutest Pet
Hey has anybody tried Microsoft Office 2010 yet? It looks like they had their major Keynote today (2010-05-12). Being an IT guy I am looking forward to rolling this out in my company. I liked the ribbon when it was introduced in Office 2007 & with Office 2010 it looks like they have refined this look. One of the programs that will benefit the most from this new release is PowerPoint. PowerPoint will have new 'built-in' video editing, new transitions and a tool to show PowerPoint's over the web.

Google has caught a lot of flack for various privacy infringements over time. Google Buzz was the latest uproar, when lack of proper prior testing allowed the tool to expose a slew of information users did not necessarily want shared, resulting in massive complaints. A Harvard student even went so far as to file a lawsuit (read more).

The files section in Basecamp is where you upload and extract project files from. This is an important way to centralize all file for a project and team. Centralize files in Basecamp.

Renaming a couple of image files is easy. But what if you are dealing with dozens and even hundreds of files? In this video tutorial you will learn to solve the problems by batch renaming your image files using Adobe Bridge. Batch rename image files in Adobe Bridge.

With the updated Files app in iOS 13, iPhone users finally have decent file browser. But, as with any file browser, it can easily become crowded, making it hard to find the files you want.

Hello null byte!! I found a local local privilege escalation exploit on Exploit-db known as CVE-2015-5889: issetugid() + rsh + libmalloc osx local root by rebel. You can visit the link here or find the code on pastebin here.
You have read How to Draft a Basic Pant Pattern. It's a most useful guide, but the image is hard to read and the steps many and complex. That's why I wrote a little software program to do the hard work for you.

Most of us have what seems to be a never-ending list of articles that we want to read... someday. A new web app called SoundGecko can help you get started on that list by converting your articles with text-to-speech technology so you can listen to them instead.

Manicures are beautiful and can add class and style to any person. Here are some step-by-step instructions for giving yourself a DIY manicure.

You've had a massive hard disk failure.. ...in your PC or laptop and like a large number of people who think it will never happen to them...you did not have a backup of those 2000+ family pictures, those hundred of important Word documents, those family videos that you downloaded from the camera then erased from the cameras disk...the inevitable "I'm Screwed!'

In this two part Photoshop tutorial, Richard Harrington takes a look at the camera raw files and the camera raw interface. Many video professionals do not know much about the camera raw interface because it is a technology mainly used by digital photographers. The key advantage to using with a camera raw file is that the data is usually stored in the picture more than you can normally see in a single exposure.

Have you ever come across a cute YouTube video that you absolutely fell in love with, and wanted to share it with your friends on a big TV? Unfortunately, YouTube doesn't have a "Burn to DVD" button next to every video. But after following the steps below, you won't need one. You'll be able to rip any video from YouTube and burn it directly to DVD, just in two clicks.

Here's the English language How-To for constructing a Lightercycle using 2 cigarette lighters. Original article courtesy of WonderHowTo user rmansur.

This video is how to sharpen your chainsaw

I recommend you take a look into this issue and suggest that your friends delete their association with Gamers Unite and any other cheat providing site. This post is meant only as my advice for how to remove Gamers Unite or any other spammy app. This is all based on my personal feelings about the snag bar and websites that would hand out such cheats. I've provided this as INFORMATION ONLY. Please decide on your own what you think of the whole situation.

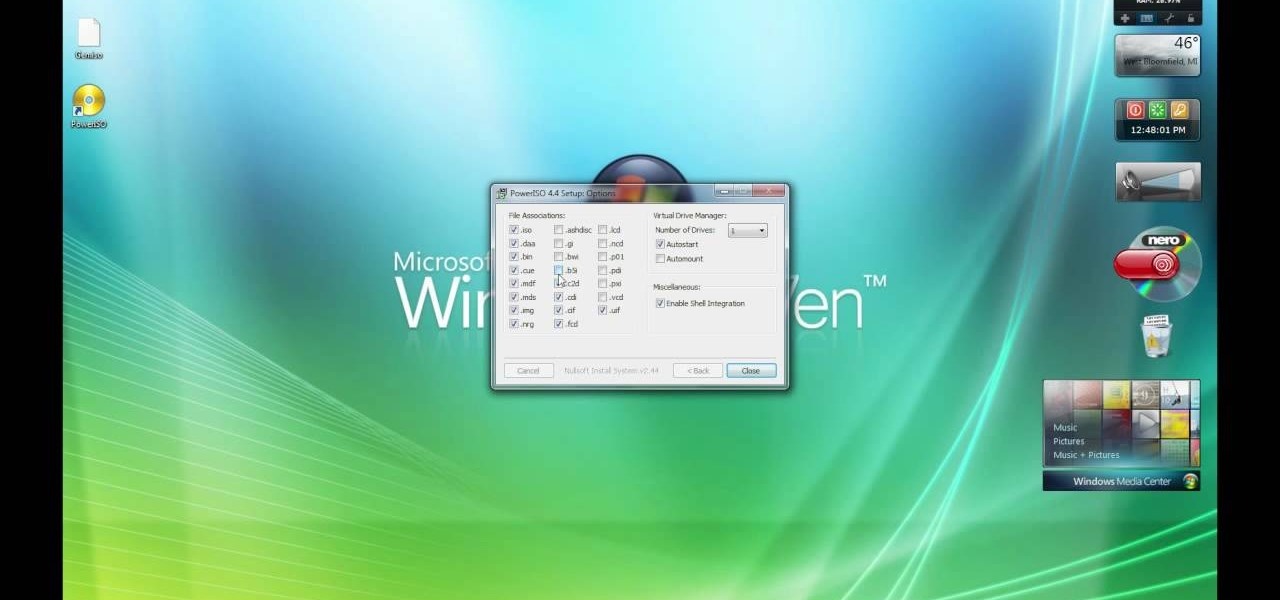
In this video, our author, Windows7User, shows us how to burn an iso file as a bootable image onto a dvd. First, please open your internet browser going to google. Next, please enter “empower iso” into the search bar.

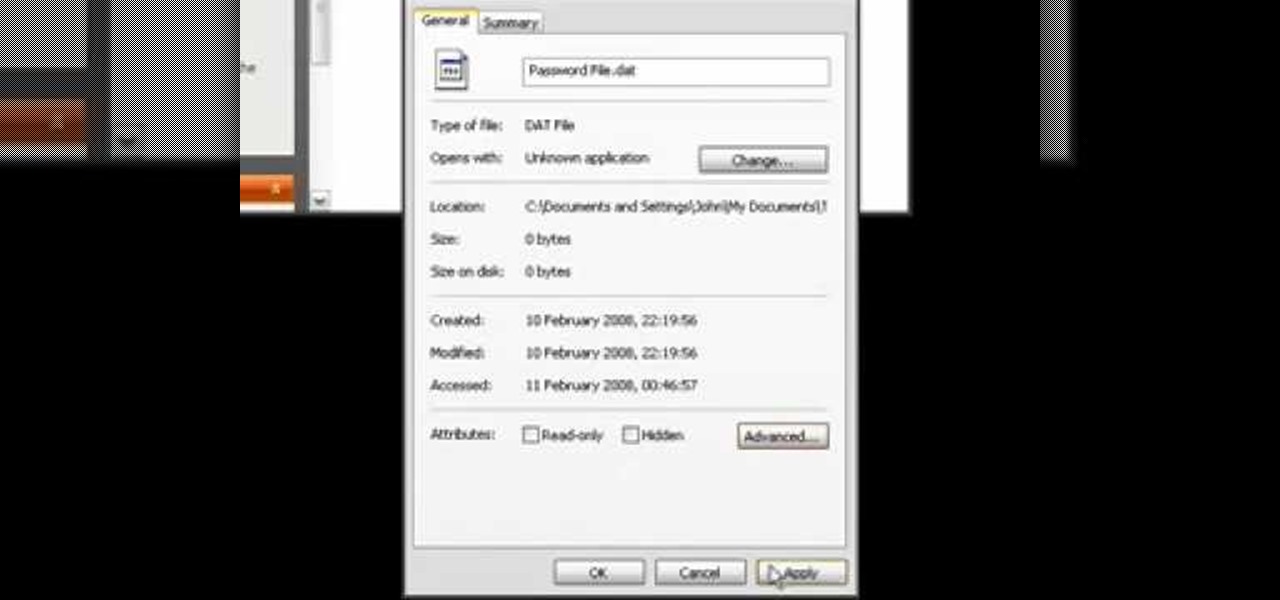
If you have files on your PC that you don't want other window's accounts to be able to access, you can encrypt them. Right click the file that you want to encrypt and select properties from the drop down menu. Once the properties page comes up, choose advanced. Now choose Encrypt contents to secure data and click ok. Now you click on apply. Select encrypt the file only and click ok. Hackers and administrators will not get an access denied message when they try to open the file. To make things...

.bat files can be quite dangerous to any machine. Creating and opening these files should be done at your own risk. Sending malicious .bat files over the internet is illegal. This video will show you how to make a virus that crashes your computer.

Follow these step by step instructions and learn to clear your history and delete temporary files in AOL 5.

Interested in creating your own dynamic, web-based applications using Visual Web Developer 2005 Express? In this installment from the Absolute Beginner's Series of Visual Web Developer C#/ASP.NET video tutorials, you will learn how to use the File Upload control on your web page to allow users to upload files to your web server. . This lesson will be particularly helpful to programmers to those with experience using both Visual Basic and simple HTML syntax. For more information, as well as ti...

A tutorial on Red workflow in Avid - Avid's Bob Russo shows how to get the Red files into the Avid while preserving the metadata. Work with Red camera files in Avid.

InDesign's integration with other Adobe products allows you to work more efficiently. You can directly export Adobe PDF files in Acrobat 4.0 or Acrobat 5.0 format. In this video tutorial you will learn to export to a PDF and save PDF presets in Adobe InDesign. Export files to PDF from InDesign.

This video covers key concepts and methods for optimizing animations. You learn how and when to cache bitmaps, depending on the construction of the FLA file. You also learn how to organize ActionScript code in your document. Optimize animations and FLA files using Flash CS3 Pro.

Are your website's graphic too small for viewing? Or too big to load? This video shows you how to preview file formats and settings in order to effectively save an Illustrator image for the web. Save files for the web in Illustrator CS3.

Have you ever worked with Photoshop and Fireworks at the same time? This video shows you how to import files from Photoshop into Fireworks. It also goes over maintaining layer hierarchy, XMP data, layer styles, and blending modes. Check out this cool video created by Tom Green now! Import Photoshop files into Fireworks CS3.

In this video tutorial you will learn to export Photoshop layers into Flash. See how to export each Photoshop layer as a PNG file so you can import each file into Macromedia Flash 8. Portable Network Graphics (PNG) format is especially useful when you have transparencies in your files. Export Photoshop layers into Flash.