The Lynda Podcast teaches viewers how to composite a video using Autodesk Toxik program. First, you need to import your footage so go to file and import. Import the files that you would like to composite together. Now that you have your files, you should arrange them in the order that you want to composite them. What you want to be first, should be on top. To composite, add in a rendering not by right clicking and click add to pick list. You can pick 'Blend and comp' to composite the files to...
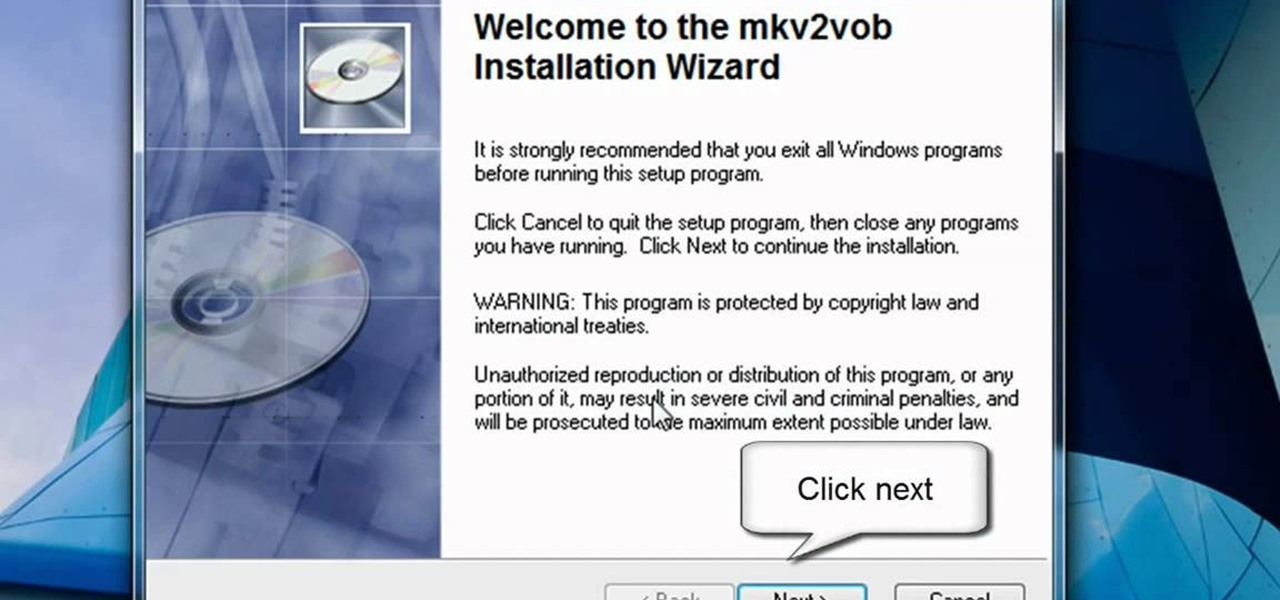
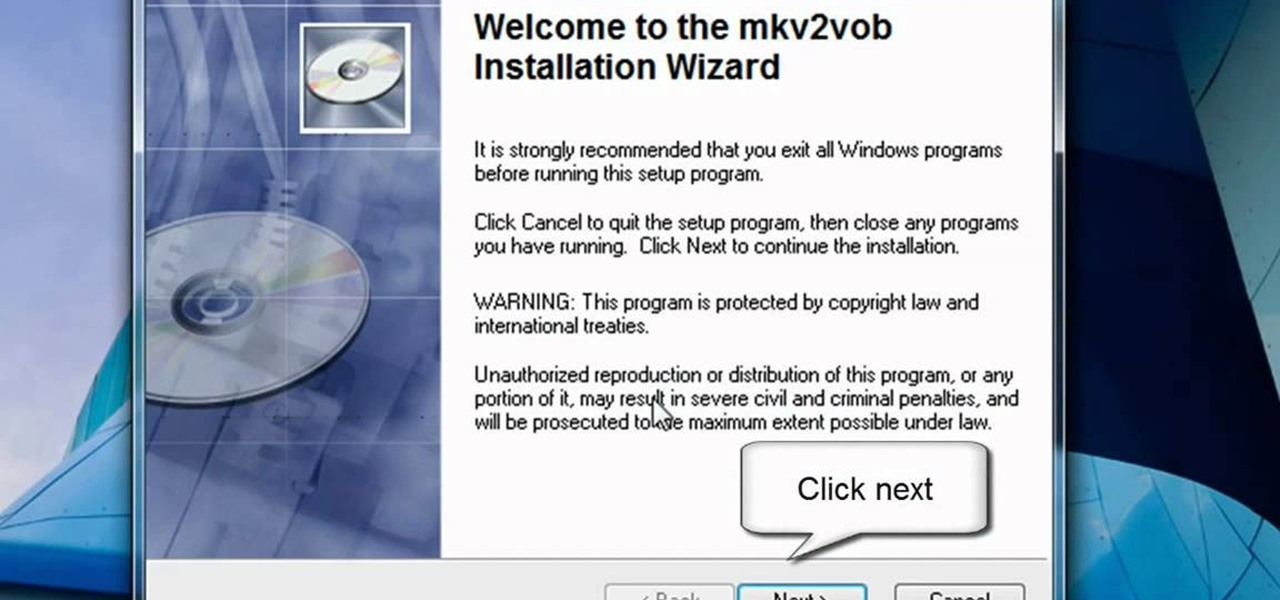
In this video tutorial, viewers learn how to play MKV videos on the PS3 using the MKV2VOB software. Begin by downloading the MKV2VOB programs from the link in the video description. Once downloaded, install it on your computer. Now open the program. Go the Configuration tab and change the setting to the same as the video. Then click on the Add File tab and select Browse under Source File. Find your MKV file and select Open. Then under Destination Directory, select where you want your file to ...

In this video the instructor shows how to choose options on a batch file. In a batch file if you write the command '@ echo off', the person running the batch file cannot see the commands being executed. You can use the 'if' condition to make the program execute either of two commands depending on the condition. While writing the if statements make sure that there is space between the 'if' and the '%' sign. If you write 'shutdown -t 30' command in your batch file, then the batch program when r...

This video teaches you how to open .zip files with a just few easy steps. First, you need to download a program Winrar. The download can be found at http://www.rarlab.com/download.html and the download should start immediately. Once the download is complete, open the program.

Do you have a hard time extracting/unzipping files using WinZip? If you follow along we will be shown a couple simple steps on how to unzip files using WinZip.
A tutorial on how to recover lost files once deleted from the recycle bin. The program illustrated in the tutorial is "Restoration". To download "Restoration", go to SnapFiles. The tutorial advises viewers to stop whatever they were doing once they realize a file is missing. Because the file is simply marked as free space, it is still present in the computer's memory but easily overwritten. To recover the file, a user will simply need to know part of the file name (preferably an extension, fo...

Stan shows an easy way to see and clean the files that are hogging hard drive space in the computer using a free software called "windirtstat". Now enter the following address in the web browser "windirtstat.info" and scroll down the page until you get the downloading and installing section. Click on the link "windirtstat1.1.2Setup(Ansi&Unicode)" which will be right after the "for all flavors of windows" this will direct you to "SOURCEFORGE.NET" download creations. This will ask you to save t...

Have some files you don’t want anyone to see? Or maybe it’s just been a while since you’ve emptied your trash bin. The trash bin function is not a permanent delete but you can erase files off your Mac with this tutorial.

This video tutorial is all about recovering the deleted files in Windows Vista. If you are using the Windows Vista and you have unknowingly deleted a file and emptied the recycle bin, then you can recover it. This can be done by using the Shadow Explorer. Shadow Explorer is a Vista program that accesses the Vista Volume Shadow Copy Service. In Vista, the shadow copy service is turned on by default. It creates backups of files on a regular basis. Shadow Explorer provides access to these backup...

Check out this cool hack from The Emo Lab. This video tutorial will show you how to do a few Windows registry hacks!

Got video files on your computer? Watch them on your big-screen TV – using your Xbox! You Will Need

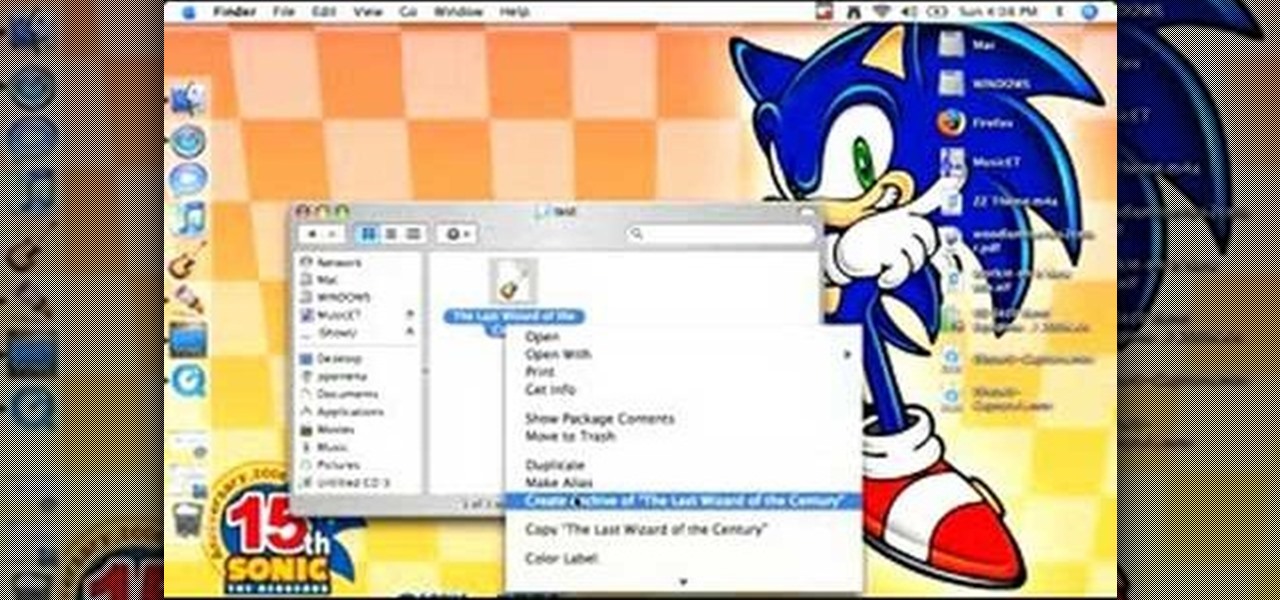
This software tutorial will show you how to email GarageBand files. Learn how to zip the GarageBand file and create an archive so you can email your GarageBand music files.

The built-in Files app on your iPhone has only gotten better since it was introduced in iOS 11, with small improvements after each new iOS version. You can manage files on your internal storage as well as in iCloud Drive, but one of the best features is being able to manage media and documents from all of your cloud storage accounts in one place.

Few things are more important than being well-versed in data analytics and interpretation when it comes to succeeding in today's increasingly data-driven world. As a data scientist, these skills are the key to a high-paying career. For hackers, there's no better way to defeat the enemy than to become the enemy.

Whether you're looking to add a substantial coding foundation to your hacking skill set or want to get a job in programming and development, knowing one or two programming languages just isn't going to cut it.

File permissions can get tricky on Linux and can be a valuable avenue of attack during privilege escalation if things aren't configured correctly. SUID binaries can often be an easy path to root, but sifting through all of the defaults can be a massive waste of time. Luckily, there's a simple script that can sort things out for us.

OnePlus phones are easy to root, but that also means they're easy to brick if you get trigger happy with your superuser privileges. If you find yourself in this situation, you'll quickly realize the OnePlus firmware download page doesn't provide files you can flash in Fastboot mode.

When you export an image from the Photos app in macOS, you may not be getting the whole deal. In the export menu, you need to select either JPEG, TIFF, or PNG, and if you don't make any adjustments to the quality settings, it'll likely be compressed. If you need the original full-resolution file or want to get the video that's attached to a Live Photo, there's a simple way to do it.

Following up on the initial tease over three months ago, Snap Inc. is finally letting the public get its hands on its new Spectacles 3 wearable device.

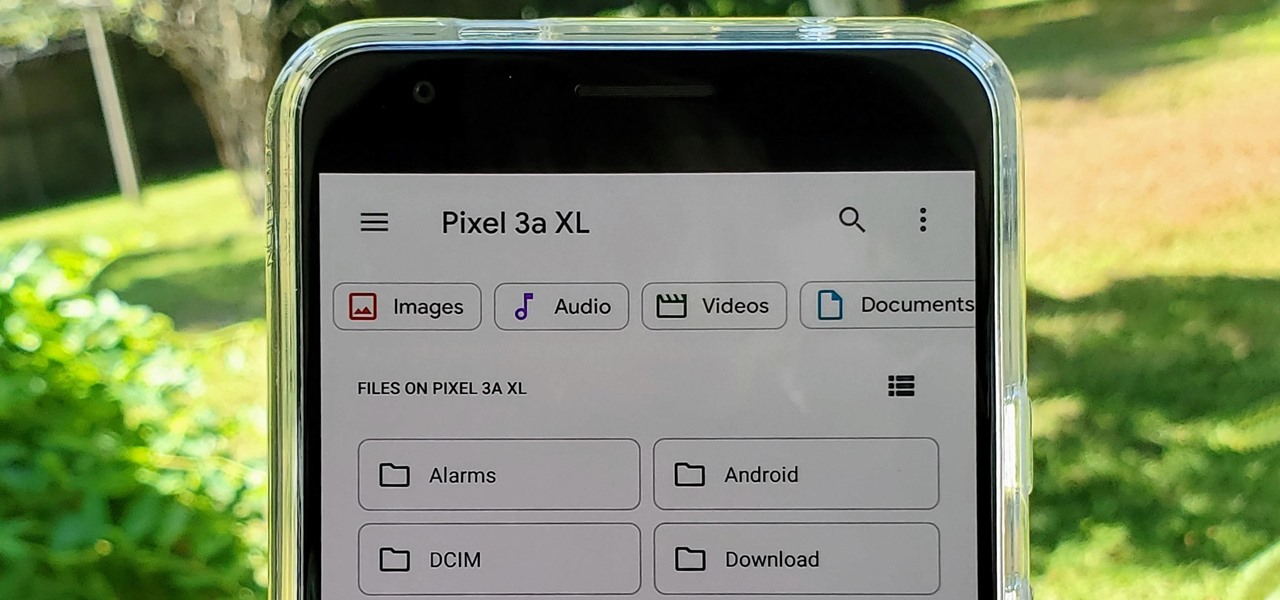
With the files on our devices getting more important as the years go by, the need to keep things organized continues to rise. The longer you have a device, the messier the internal storage might become. Having a file manager would be extremely useful in this situation. You could also reorganize the folder structure as well, just like you could on a desktop computer.

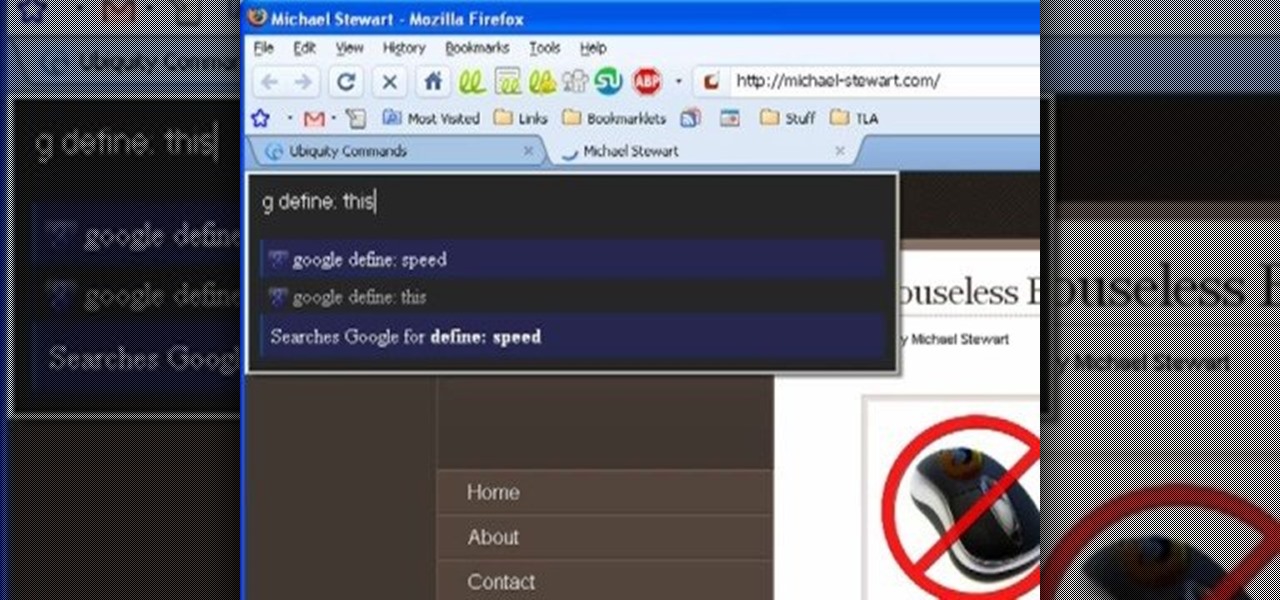
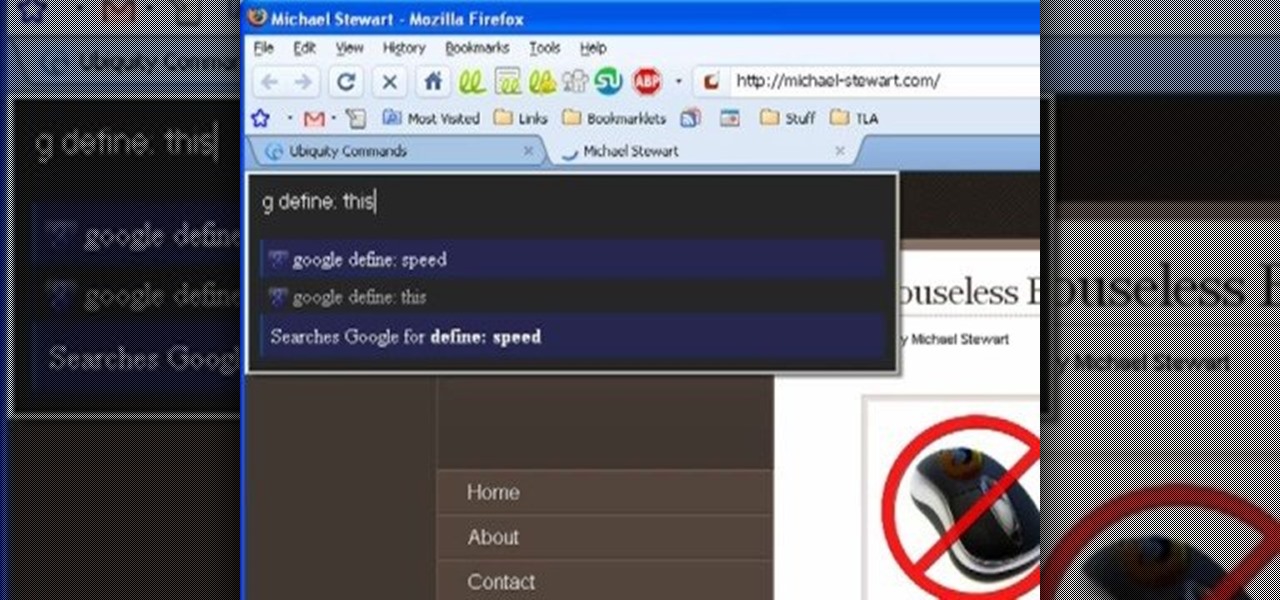
Google is an incredibly useful database of indexed websites, but querying Google doesn't search for what you type literally. The algorithms behind Google's searches can lead to a lot of irrelevant results. Still, with the right operators, we can be more exact while searching for information that's time-sensitive or difficult to find.

It's no secret that Samsung is working on augmented reality hardware, as the company has been candid about its intentions. However, what we don't know is exactly how many AR projects the company is working on, as patent filings and reports revealed two more over the past week.

It is said that the best way to avoid detection when hacking is to leave no trace, and often that means not touching the filesystem at all. But realistically, in most cases, it's impossible not to interact with the filesystem in one way or another. The next best thing to do to throw off any investigators is to change the file attributes to hide activity. We can do this with Metasploit's Timestomp.

The enterprise sector is where the money is for augmented reality at the moment, and remote assistance apps are the go-to app for many enterprise customers. We took a look at the leading apps and platforms from this category, from the top contenders to the underdogs with unique features.

When we reviewed the best file managers on Android, MiXplorer easily topped our list with its abundance of features, including tabbed browsing, support for up to 19 different cloud services, file and folder encryption, and much more. The only major complaint we had was the fact it couldn't be installed from the Play Store, but now, that is no longer the case.

Owners of Google Pixel devices now have a plethora of imaginary friends to play with thanks to the Playground augmented reality app.

Magic Leap's recent L.E.A.P. conference was free to all who registered in time, but if you weren't able to make the trip to Hollywood, the company just released video of some of the sessions that took place over the course of two days.

A simple security flaw can allow an attacker to gain a strong foothold with little effort on their part. When a web application permits remotely hosted files to be loaded without any validation, a whole can of worms is opened up, with consequences ranging from simple website defacement to full-on code execution. For this reason, RFI can be a promising path to obtaining a shell.

It's not uncommon for hackers to attempt to move laterally between devices in proximity of a compromised device to maintain a prolonged presence in the network. Malware utilizing USB flash sticks to self-replicate and compromise air-gapped machines isn't a new concept.

Google Photos integrates with Google's ecosystem to bring you awesome features like the ability to identify landmarks, track down products you've photographed, and so much more. Now, if you need to translate foreign words in any of your pictures, the app has you covered as well.

Think back to when you last wanted to transfer some music or videos to your friend's smartphone and how difficult and slow it was. As powerful as our phones are, the default file sharing options are limited. There are, fortunately, some better options which make moving files easy, secure, and painless.

The Super Bowl of bicycle racing, the Tour de France, added augmented reality to its TV broadcast this year.

In most macOS hacks, a non-root terminal is used to create a backdoor into the device. A lot of damage can be done as a low-privileged user, but it has its limitations. Think twice before granting a file permission to execute — an attacker might be able to convert your harmless scripts into persistent root backdoors.

Deleted bank statements and private photos are still within an attacker's grasp, so don't think that emptying your recycling bin is enough to keep your files from coming back to life. It's possible for a hacker to recover compromising files and images from a backdoored computer completely without the victim's knowledge.

This week, two companies preparing the most anticipated augmented reality devices for consumers were the subject of reports regarding strategic moves to put them in better positions to move those products forward.

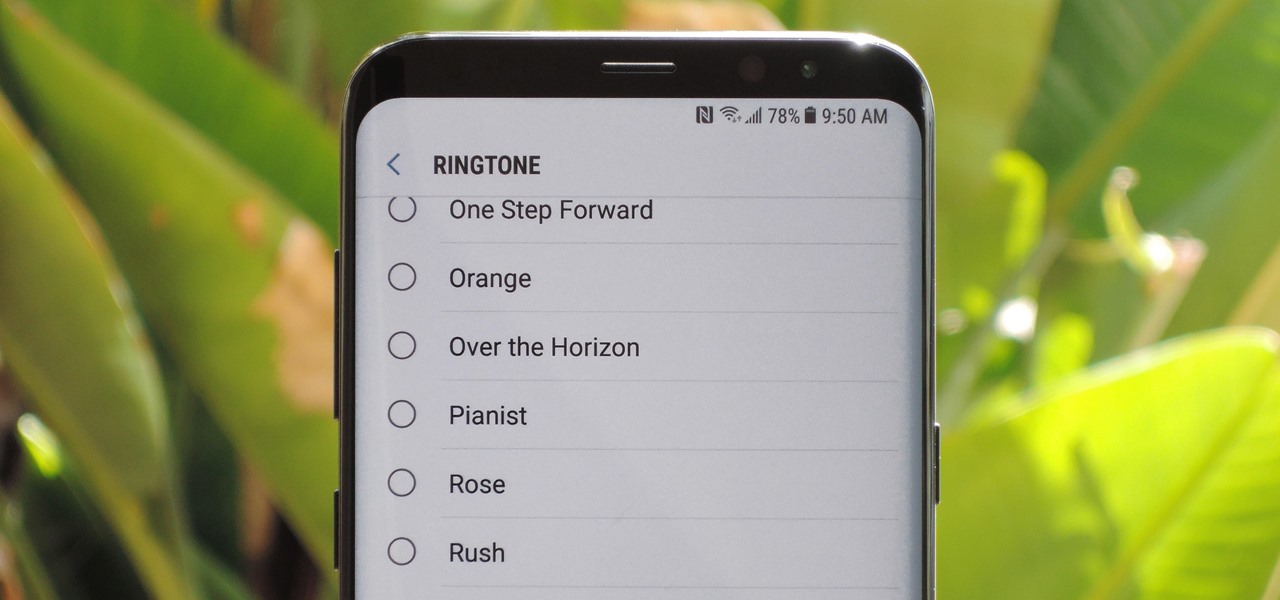
The Galaxy S9 was announced February 25, and it's jam-packed with features like AR Emojis and and a Dual Aperture camera. You really love the cut of its jib, but maybe you don't have the means to get your hands on one. Well now, you can get the Galaxy S9's notification sounds and ringtones, to help you feel like you own one.

For some, going to the dentist can be a terrifying experience, but a new use of augmented reality could go a long way toward making the trip feel more like it's worth the orthodontic angst.

Apple's codec for photos and videos in iOS 11, HEVC (High-Efficiency Video Coding), as well as the container, HEIF (High-Efficiency Image File Format), result in a reduction in size for pictures and movies without sacrificing quality. Seems like a win-win situation, but Windows-users can't open the .heic extension that these files use. In order to open HEIC files on a Microsoft Windows PC, you'll have to turn to third-party apps and tools. One of these tools, CopyTrans HEIC for Windows, essen...

File inclusion can allow an attacker to view files on a remote host they shouldn't be able to see, and it can even allow the attacker to run code on a target.

Investors are ready to throw their money at augmented and virtual use cases that demonstrate a business purpose and a return on investment.