
Filing Analysis Search Results


How To: Here's the Ultimate Guide to Becoming a Data Ninja
Data analytics is crucial to the operations of every modern business. This trend is going to continue: in three years, 71% of global enterprises predict a rapid increase in data analytics. Experienced professionals that can project manage data initiatives are in high demand.
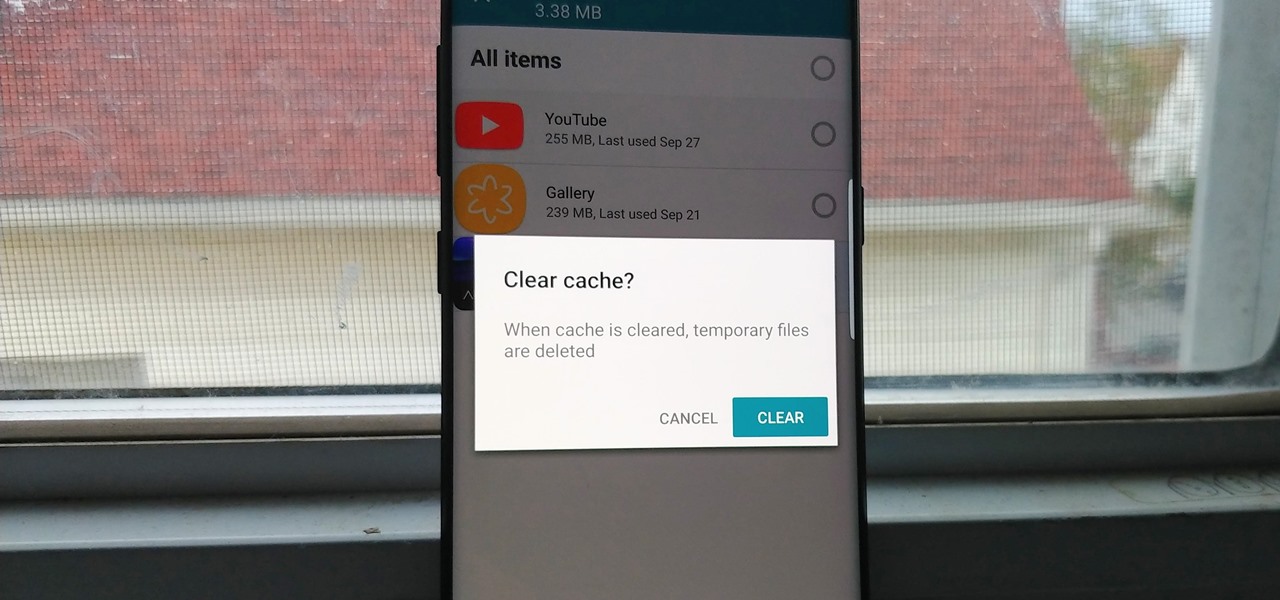
How To: Most File Cleaners Are Trash — Here's Which Ones You Can Trust
Since the release of the T-Mobile G1, the Play Store has been flooded with apps that claim to improve performance by clearing cache and storage. These apps are typically useless, rarely providing more than a temporary fix which Android undoes immediately. As Android has continued to improve cache and storage management, such apps have become more trivial. However, there are few decent ones out there.

News: Change of Tune? Not Everyone Needs to Finish That Course of Antibiotics
After years of telling patients to finish any prescribed course of antibiotics completely, a group of researchers in the UK say it is no longer necessary, and could even be harmful if we want to preserve the antibiotics we can still use.

Hack Like a Pro: Digital Forensics for the Aspiring Hacker, Part 12 (Windows Prefetch Files)
Welcome back, my aspiring hackers! In this series, we continue to examine digital forensics, both to develop your skills as a forensic investigator and to avoid the pitfalls of being tracked by a forensic investigator.

Hack Like a Pro: Digital Forensics for the Aspiring Hacker, Part 11 (Using Splunk)
Welcome back, my neophyte hackers! Digital forensics is one of the fields often overlooked by aspiring hackers. In a rush to exploit every and any system they can, they often ignore learning digital forensics—the field that may lead to them being traced.

How To: Harness the Power of Big Data with This 10-Course Bundle
You don't need to work as an executive at Google to understand and appreciate the importance of large-scale data analytics in today's world. Whether you're interested in joining the ranks of a major tech firm or want to improve your company's marketing campaigns through consumer analysis, knowing how to work with large sets of complex data is paramount.
How To: Supercharge Your Excel Skills with This Expert-Led Bundle
We've already highlighted the importance of learning Microsoft Excel from a hacker's standpoint, but it's also just a good skill to have as you'll likely come across the number-crunching powerhouse at school and work, as well as in other areas of your life, such as budgeting.

News: Apple Surpasses 13 Million ARKit Downloads Within Six Months, Report Says
A report from app data firm Sensor Tower reveals that more than 13 million ARKit apps have been installed on iPhones and iPads within the first six months since the toolkit launched with iOS 11.

Market Reality: Boeing HorizonX Takes Flight with AR Investment
Welcome to the maiden voyage of our new Market Reality column. Each Friday, NextReality will give you a roundup of news briefs from the financial end of the augmented and mixed reality industry. We'll cover funding news, market analysis, and more.
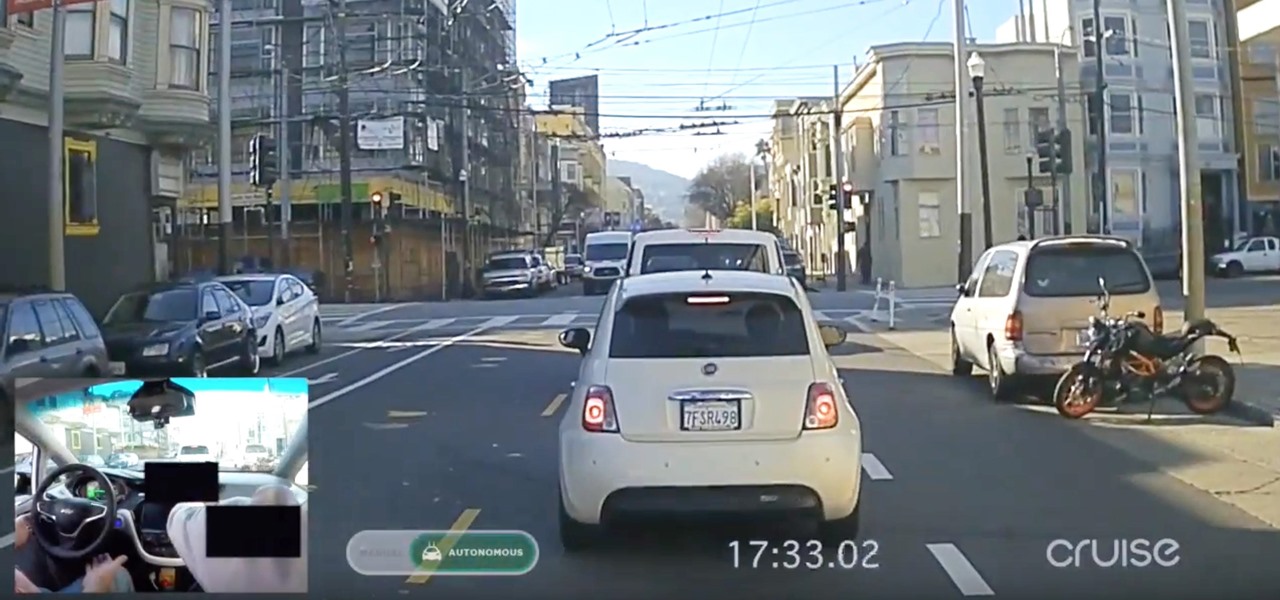
Video Analysis: New GM Cruise Self-Driving Video Shows More Mastery of SF Roads... This Time with PiP Proof
A couple weeks ago, GM's Cruise Automation released a remarkable self-driving video from the streets of San Fransisco that Driverless analyzed in detail. And now they've just released a new one giving more insight into their growing mastery of the complex roads in San Francisco, specifically, the Potrero Hill and Mission Dolores neighborhoods.

Hack Like a Pro: Snort IDS for the Aspiring Hacker, Part 3 (Sending Intrusion Alerts to MySQL)
Welcome back, my hacker novitiates! If you have been following this new Snort series, you know that Snort is the world's most widely used intrusion detection/protection system. Now a part of the world's largest network equipment company, Cisco, it is likely to be found everywhere in one form or another. This makes a compelling argument for learning how to use it, as it will likely be a necessity in any security-related position.

How To: Find a tennis grip
Welcome to a tennis lesson from FuzzyYellowBalls, the the best place to learn how to play tennis online. Our free video tennis lessons teach you how to play the game in a new way that combines technical analysis, visual learning, and step-by-step progressions.

How To: Practice a toss & backswing on a tennis serve
Welcome to a tennis lesson from FuzzyYellowBalls, the the best place to learn how to play tennis online. Our free video tennis lessons teach you how to play the game in a new way that combines technical analysis, visual learning, and step-by-step progressions.

How To: Master your tennis kick serve progressions
Master your tennis kick serve progressions. This tennis lesson video series lays out the 4 steps to tennis kick serve progressions. Be sure to click on all the video chapters to view the entire tutorial.

How To: Employ the tennis footwork ready position
The ready position is the position you want to be in when you're waiting for your opponent to hit you the tennis ball. It's the foundation for tennis movement in general. From this position you can employ the various footwork patterns that let you move around the tennis court correctly. The ready position is very similar to an athletic stance in basketball. Your feet are a little bit wider than shoulder-width apart, your knees are slightly bent and the weight should be on the balls of your feet.
How To: Use proper footwork in tennis
Footwork is probably the most important part of tennis. Unfortunately, it is also one of the most underrated areas of the sport. Learning to move around the tennis court correctly is EXTREMELY important. Correct footwork lets you use correct stroke mechanics when you hit. Correct footwork is what typically sets advanced tennis players apart from everyone else.

Use tennis footwork move: back foot up
Bringing your back foot up after you hit the tennis ball puts you in position to recover back to the middle of the tennis court. The key, as we explain in this video, is to get your body facing the net after you hit (similar to the ready position). This will let you side shuffle back to the middle of the tennis court.

How To: Use the tennis backhand follow through
The fourth thing that every high-level tennis player does when hitting a backhand is follow through. Extend out in the direction you are hitting the ball, then smoothly bend the elbows and wrap the racket up over your shoulder.

How To: Use shoulder rotation on a windshield wiper forehand
This video explains how the amount of shoulder rotation you get during a windshield wiper forehand can differ from a classic forehand. After you hit the tennis ball, you typically have to rotate a little bit more than you otherwise would on the windshield wiper. There are a number of reasons for this, but in this video we keep our focus relatively narrow.

Do tennis forehand stances: the Open, Neutral & Closed
Every time you hit a tennis forehand you choose how you position your feet -- what stance you will use. You can hit a forehand with an open, neutral, or closed stance, but you should stay away from the closed stance if possible. This last stance makes it difficult to rotate your upper body through contact, making it difficult for you to use correct forehand mechanics.
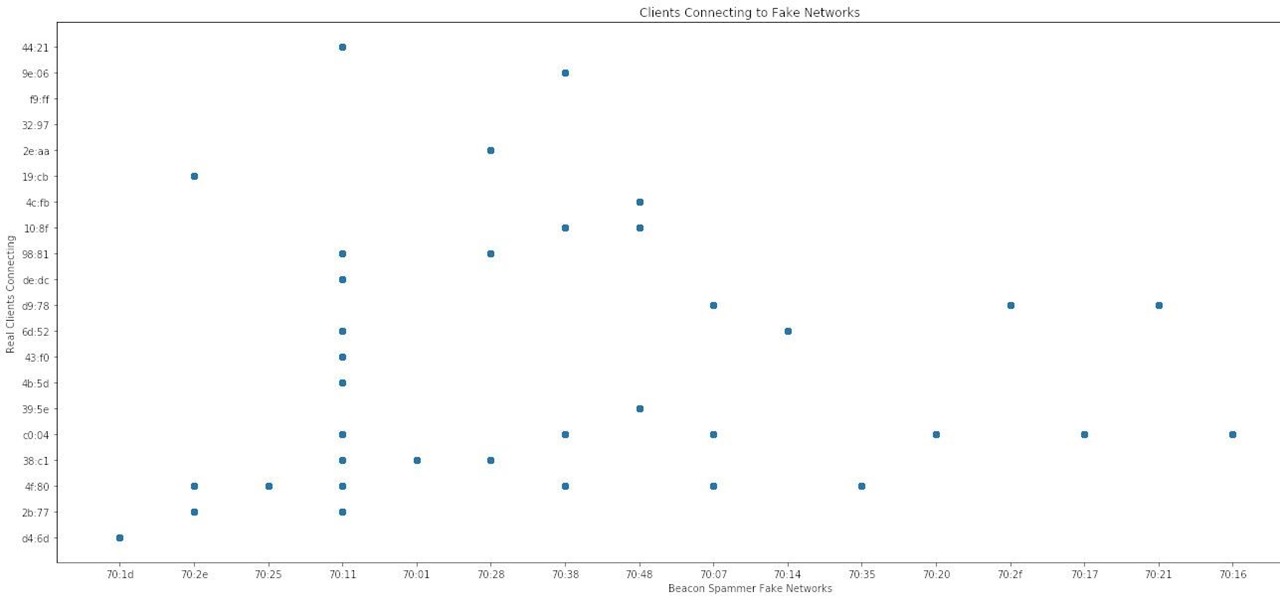
How To: Analyze Wi-Fi Data Captures with Jupyter Notebook
When it comes to sniffing Wi-Fi, Wireshark is cross-platform and capable of capturing vast amounts of data. Making sense of that data is another task entirely. That's where Jupyter Notebook comes in. It can help analyze Wi-Fi packets and determine which networks a particular phone has connected to before, giving us insight into the identity of the owner.

Market Reality: Niantic & WaveOptics Locate More Funding for AR, Cheddar Spreads to Magic Leap, & Tesla Files AR Patent
Investors continue to bet on augmented reality, both for short-term returns and long-term plays. This week, Niantic reportedly picked up another round of funding from Samsung and others, based on the success of PokémonGO and the prospects for future revenue. Likewise, investors see value in WaveOptics, whose waveguide displays could make consumer smaller AR smartglasses possible within the next year.
Market Reality: Magic Leap Gets New Cash & NBA Deal, AR Supplier's Apple Rumor, & HoloLens Gets into Rental Business
While the company is adamant that the Magic Leap One: Creator Edition will ship this year, currently, it seems its CEO is more interested in striking deals with content partners than releasing details about the headset.

How To: Reverse Engineering with Radare2 (A Quick Introduction)
In this article, we will explore the basics of radare2, a powerful package that comes with Kali. We are going to write a simple program, and then disassemble it, to see what is really doing in the processor.

How To: Security-Oriented C Tutorial 0xFD - Software on Steroids - Upgrading Our Malware
Welcome back to a tutorial on malware. We'll be discovering a method to beef up our little trooper. Without further ado, let's jump right in!

How To: Security-Oriented C Tutorial 0x01 - Hello, World!
Welcome back, reader! In this tutorial, we will be covering our first program! So let's get to it. We all know the unspoken tradition of the first program when learning a language and of course, here we will respect and complete it. Fire up your favorite text editor (be it vim, emacs, gedit, it's all the same to me, no h8) and try to keep up.
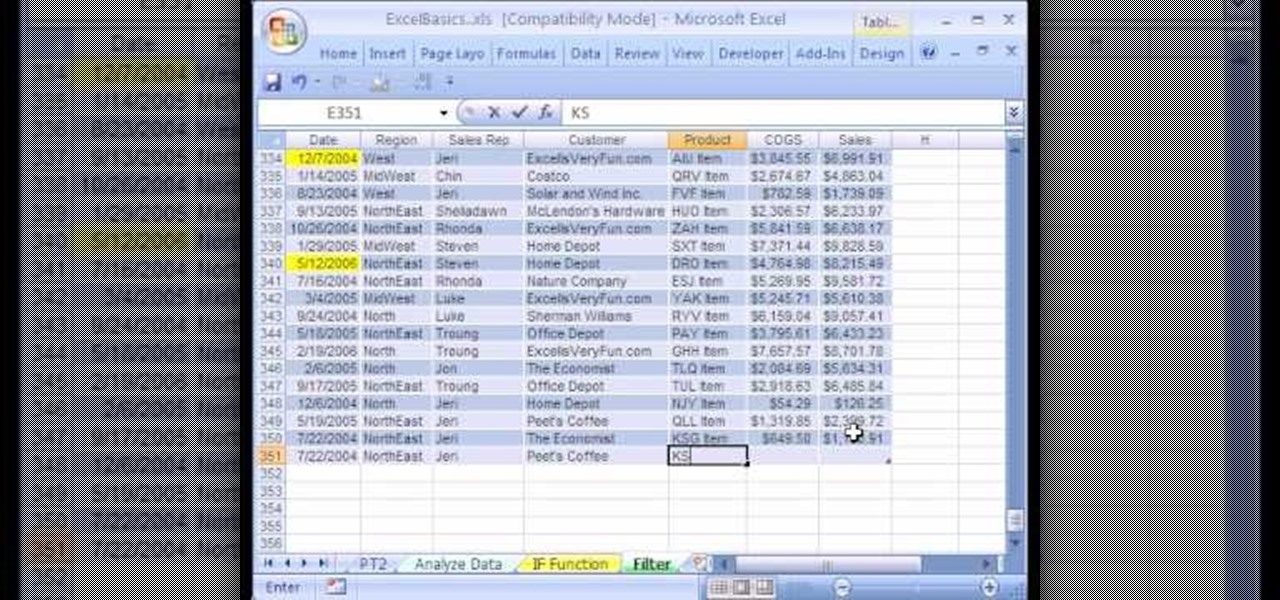
How To: Use Excel data analysis filter & dynamic ranges
We're on sheet, tab, filter. We want to talk about filter, but we also want to talk about an Excel table or list. It is simply a data set with field names at the top, records in rows, no blanks anywhere and no other data sets touching this data set. When we convert to a table, it does a lot of amazing things. The new keyboard shortcut is "Ctrl T". If data is set up correctly, it will work. Click Ok. You can build a function based on a column of data, i.e. "Alt =" which is the shortcut for sum...

How To: Make a talking robot mask using an iPhone
This video describes how to make a talking robot mask using iPhone. For that you need Reading scale, Cutter scissor, Box to fix into head, Cutter Knife, Screw Driver, Glue, Cello tape, Aluminum Foil, Pen, 2 Bottle caps, used paper and an iPhone with mouth analysis software. First take together, now take that Box and have to two parts for make it convenient to wear into head by sticking both using Cello tape, now we have to make the mouth with size of "50mm by 75mm" which will fit with iPhone’...

How To: Become a Productive Microsoft Apps Power User with 97% Off This Course Bundle
You may think you know Microsoft's apps, but did you know that you could be using them as a power user and make yourself way more productive in the process? Thankfully, the easiest way to master them from home is on sale right now, as The Premium Microsoft Office & Data Apps Certification Bundle is on offer for just $39.99 — a huge 97% off the regular price of $1,782.

How To: It's Time to Finally Learn Microsoft Excel & Power BI — This Training Deal Is Too Good to Pass Up
Data analytics is crucial to the operations of any modern business these days. This trend is going to continue: in three years, 71% of global enterprises predict a rapid increase in data analytics.

Market Reality: US Army Chooses Microsoft Over Magic Leap & Niantic Puts Its Money on Consumer Smartglasses
The recent announcement of a $480 million US Army contract awarded to Microsoft over Magic Leap for supplying 100,000 augmented reality headsets shows just a how lucrative the enterprise (and government) sector can be for AR.

How To: Security-Oriented C Tutorial 0x19 - Functions Part V: Passing by Reference
Hello there! This will probably be the final tutorial on functions where we will be looking over a method called pass by reference. This technique allows us to modify large amounts of data without the overhead and return multiple values. Let's go!

Hack Like a Pro: Digital Forensics Using Kali, Part 3 (Creating Cases in Autopsy & Sleuth Kit)
Welcome back, my tenderfoot hackers! In continuing my series on digital forensics using Kali, I want to introduce you to two complementary tools, both built right into Kali Linux. These are Brian Carrier's tools Autopsy and Sleuth Kit.

Hack Like a Pro: Digital Forensics Using Kali, Part 2 (Acquiring a Hard Drive Image for Analysis)
Welcome back, my aspiring hackers and those who want to catch my aspiring hackers! As most of you know, this series on digital forensics is inspired by the motivation to keep all of you all out of custody. The more you know about the techniques used by law enforcement and forensic investigators, the better you can evade them.
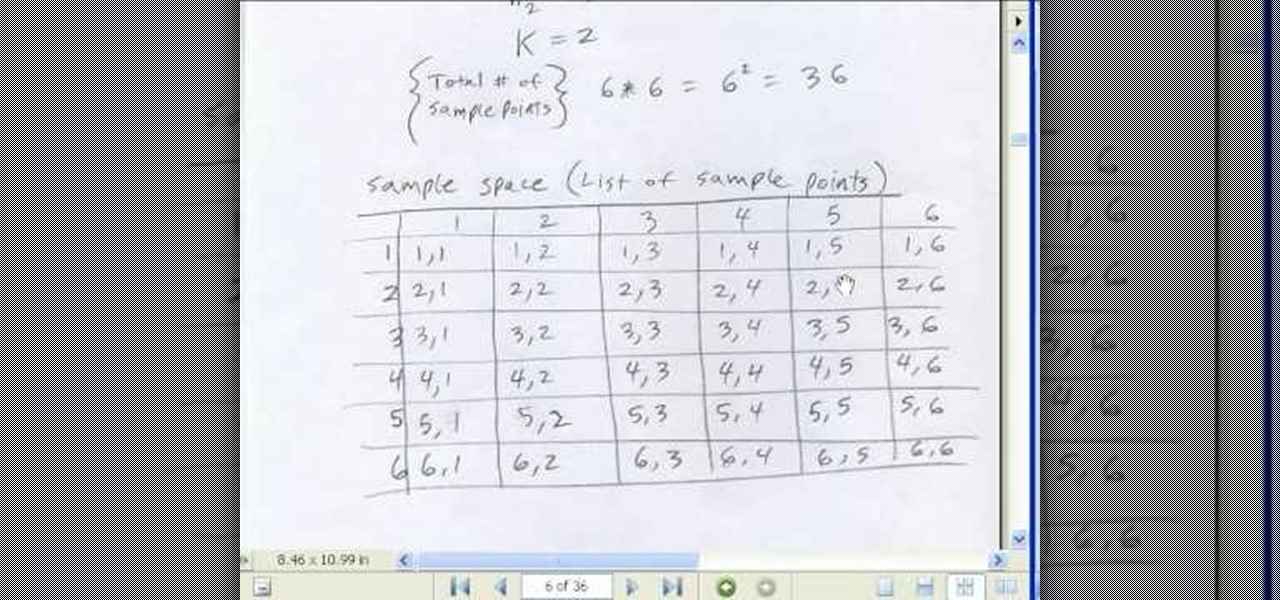
How To: Work with probabilities in Microsoft Office Excel
If you use Microsoft Excel on a regular basis, odds are you work with numbers. Put those numbers to work. Statistical analysis allows you to find patterns, trends and probabilities within your data. In this MS Excel tutorial from everyone's favorite Excel guru, YouTube's ExcelsFun, the 50th installment in his "Excel Statistics" series of free video lessons, you'll learn the basics of probability:

How To: Write a landing page that converts
Starting up a website can be daunting if you know nothing about web design or setup, but there are some tips to get the right people finding, looking, and returning to your site. A good landing page gives visitors exactly what they are looking for, and converts them from browsers to customers.
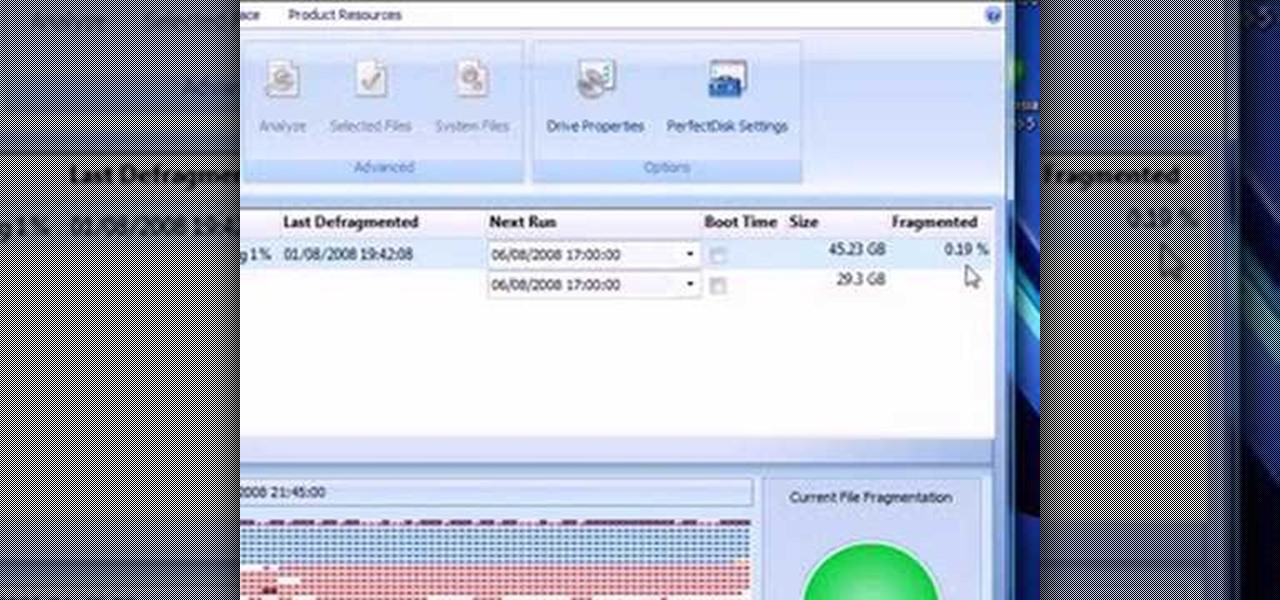
How To: Shrink a Windows Vista partition and install iATKOS
This video presents how to defragment and shrink a Windows Vista partition using Perfect Disk 2008 Professional program.First you need to download and install software application named Perfect Disk 2008.Type Perfect Disk 2008 into Google search engine, choose first link from the list.On the Raxco software home page choose Free Evaluation option from the list to the right.Download and install Perfect Disk 2008 Professional.Once it is installed, run the application. From Menu choose Analyze op...

How To: Build a mini multi-touch table and photo stitch
Hak5 isn't your ordinary tech show. It's hacking in the old-school sense, covering everything from network security, open source and forensics, to DIY modding and the homebrew scene. Damn the warranties, it's time to Trust your Technolust. In this episode, see how to build a mini multi-touch table and photo stitch.
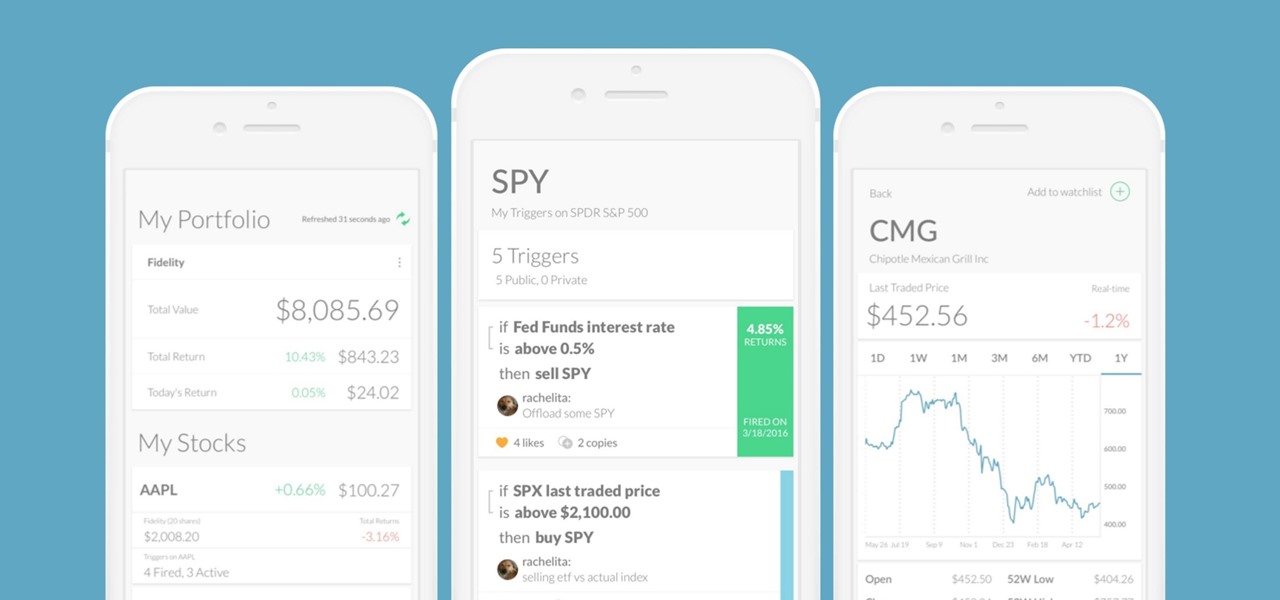
News: This App Notifies You Every Time a Trump Tweet 'Triggers' Your Stocks
Every time Donald Trump tweets about a stock you own, Trigger Finance, or just Trigger—the app founded on the "if this, then that" rule to track and invest in the stock market—alerts you with a notification for real-time analysis of financial data.

