Google and Microsoft have both established platforms and hardware for emerging digital realities, but Apple, true to form, hasn't had much to say on the subject. They've shown interest in augmented reality, and we've seen patent filings that indicate research and development, but a recent rumor points to that research ending up in your car instead of a rose gold headset.

What's up readers? Today I'll be introducing to you a new vulnerability called the Format String vulnerability (in case you missed the title). It won't be much, just a little motivation to keep you guys going. A little teaser, if you may.

When security firm Zimperium discovered Android's biggest security risk in years, it sent shock waves through the ecosystem. As a result, Google, LG, and even Samsung decided to change the way they issue updates to their devices, by pledging to release monthly security patches to plug up loopholes exactly like this one. Yeah, it's that big of a deal.

UPDATE: A patch to fix the exploit has been released. Download it here.

Copying a file's path on your Mac isn't always an easy task. Thankfully, this cool little OSX utility called Copy Path Finder helps solve this problem and lets you copy the path of a file in your file system to the clipboard so that you can paste it into a text editor later.

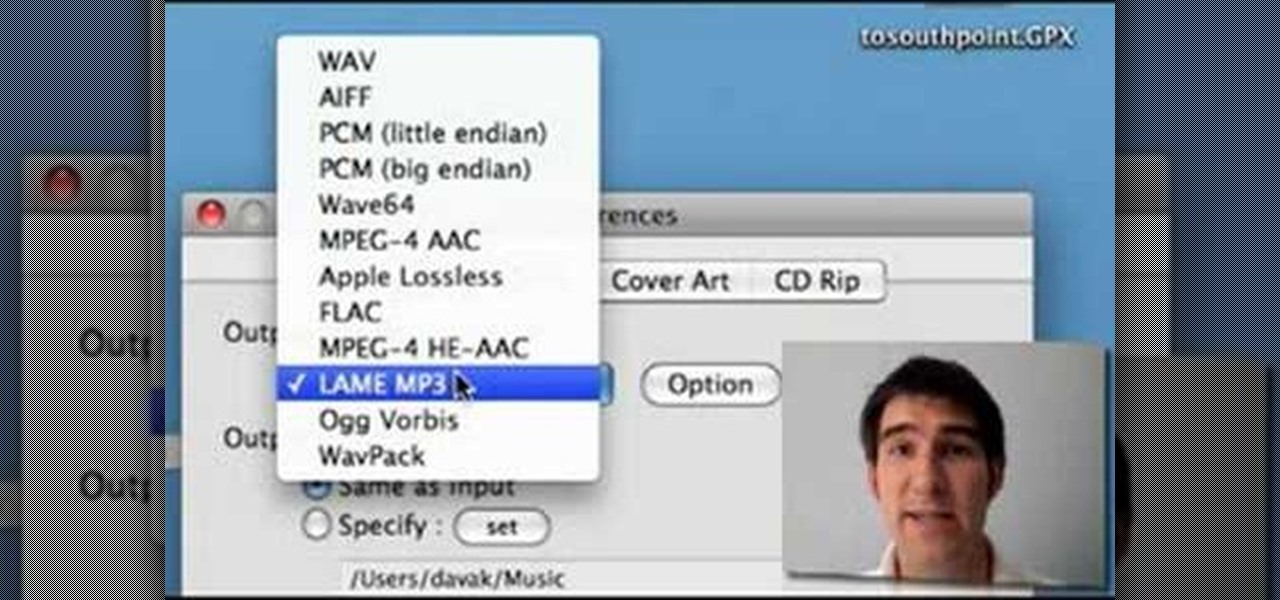
Learn how to edit audio files using Audacity of the MAC. 1 Create an audio file by using the built in recording function in Audacity. Save the file prior to starting your editing. 2 Open the file that you created earlier and test the file by playing it. 3 You can copy, cut and paste different parts of the file by highlighting the section in your file and then right clicking (or option clicking) and choosing what you want to do from the pop up file. 4 You can also add effects by highlighting a...

This week, Snapchat parent Snap came closer to fulfilling its smartglasses destiny by adding new 3D content capabilities to its third-generation Spectacles. At the same time, the now defunct Meta Company continued its fall from grace, as a judge ruled in favor of the plaintiff in the patent infringement case against the Meta 1 and Meta 2 headsets.

Developers and enterprise customers chomping at the bit to get their hands on HoloLens 2 may not have to wait much longer, as Microsoft passed one of the remaining hurdles needed to release their new tech into the wild.

What if you could easily visualize which access point every Wi-Fi device nearby is connected to in a matter of seconds? While programs like Airodump-ng can intercept this wireless information, making it easy for hackers to use and understand is another challenge. Fortunately, a tool called Airgraph-ng can visualize the relationships between Wi-Fi devices from only a few seconds of wireless observation.

Auditing websites and discovering vulnerabilities can be a challenge. With RapidScan and UserLAnd combined, anyone with an unrooted Android phone can start hacking websites with a few simple commands.

With the rise of website encryption (TLS), sniffing passwords from network activity has become difficult. However, it's still possible to quietly exfiltrate a target's network traffic in real time to extract passwords and sensitive information. Pertaining to macOS, there are two methods for retrieving traffic from a backdoored Mac.

As it prepares to ship its first product by the end of the summer, Magic Leap has managed to impress yet another high-profile investor in telecommunications giant AT&T.

The rate of preterm birth has been increasing in the United States for unknown reasons, causing increased health risks for infants born too soon. But researchers may have found a signal that could help doctors plan ahead for, or even prevent, early birth with a simple swab of the vagina and cervix during pregnancy.

Since the days of flip clocks, alarms have always had one function—make a bunch of annoying racket early in the morning to ensure that you wake up in time. And this simple MO has stayed in place while technology advances at a breakneck pace, almost in spite of the fact that today's devices are capable of doing far more than beeping at 7 in the morning.

What's up readers? We have ever so slightly touched upon this concept of scope with variables but still don't really know what it means. In this tutorial we will learn the behaviors of variables existing in our programs and within functions.

By now, nearly everyone with any type of media access is aware that Sony Pictures Entertainment was hacked on November 24th. Although there can be many interpretations and lessons drawn from this audacious act, there is one indisputable conclusion: it and its ripples across the globe underlines how important hacking has become in our all-digital 21st century. As I have emphasized so many times in this column, hacking is the discipline of the future. From cybercrime to cyber intelligence to cy...

Welcome back, my greenhorn hackers! Lately, much of the discussion here on Null Byte has revolved around evading detection and not getting caught hacking. Several of you have written me asking for a series on evading detection and forensics, and while I began a series 5 months ago on just that, we have changed hacking platforms from BackTrack to Kali, which has a much more highly developed forensic toolset.

The use of smart phones is not limited only as a mode of communication now-a-days. There are many things that can be done with the help of a smart phone.

Check out this free Windows utility that allows you to print files directly from the file system by dragging and dropping them onto an icon conveniently placed on your desktop.

There are a lot of videos out there about creating models and animating them using 3D Studio MAX. What isn't often discussed is the next step in creating a movie out of your models, adding sound and syncing your animations to the sound. This eight-part video series will show you how to do just that, animate objects and other properties with a sound file. This is very good stuff that you will need to know if you ever want to make a whole 3D movie yourself.

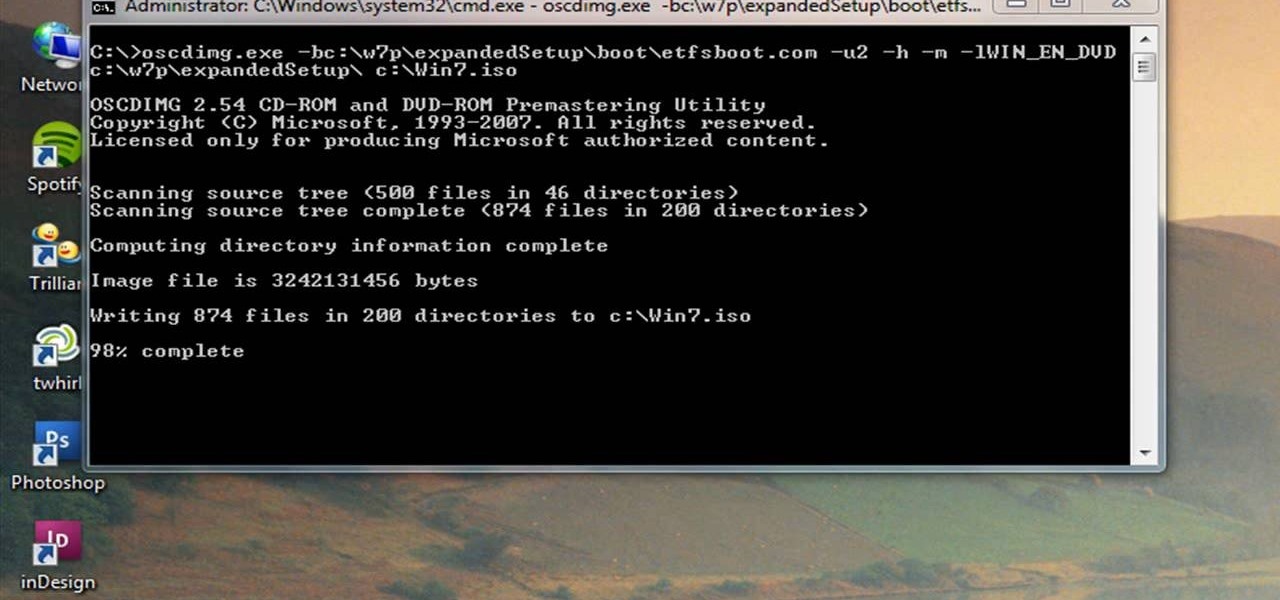
Windows 7 can be purchased online and downloaded. From the downloaded files you can create a bootable DVD. Three files are downloaded: An executable 64-bit Windows file and two .box files. Move all files to a new folder "w7p" and put the folder on the C drive. You have to download a Premastering file from here: http://depositfiles.com/files/d8zxuifur and paste it into system32 folder. Unpack .box files and click on "expanded set-up folder". Go to command prompt, enter large chunk of code (wri...

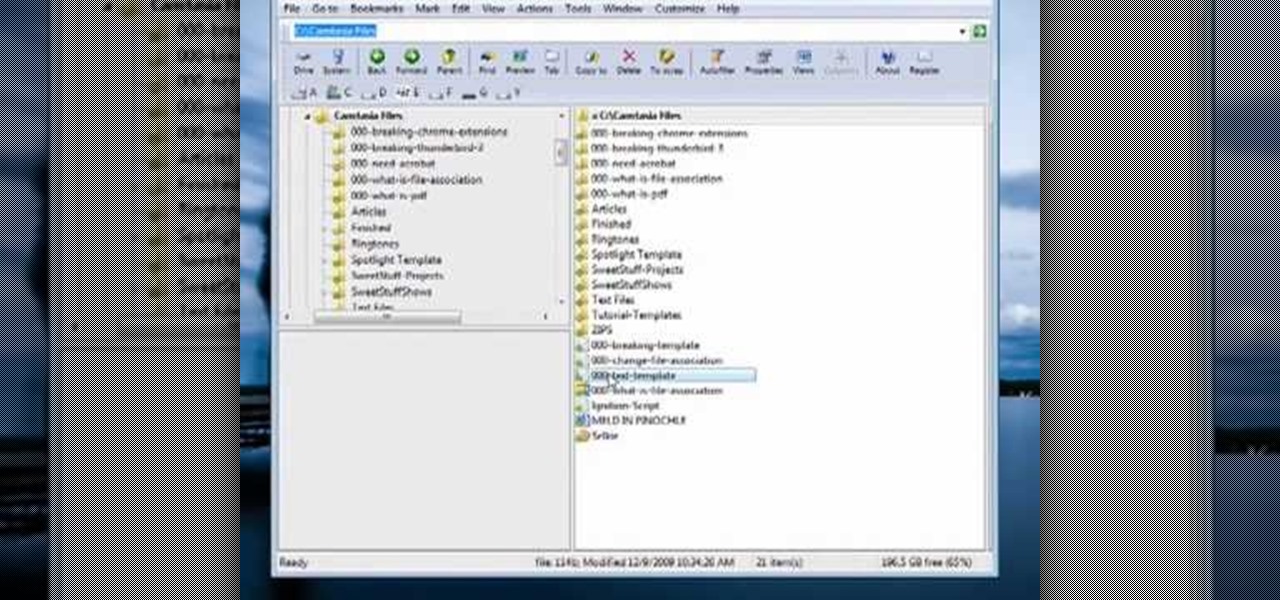
This video tutorial from butterscotch presents how to change file associations on your computer.File association is a link between a certain type of file (.doc, .gif, .txt) with a particular program.For example text files are by default associated with Notepad application.So if you double-click text file it will be automatically opened in this program.In case you want to open this file in a different type of program, you need to change the file association.To do that, right click the file, th...

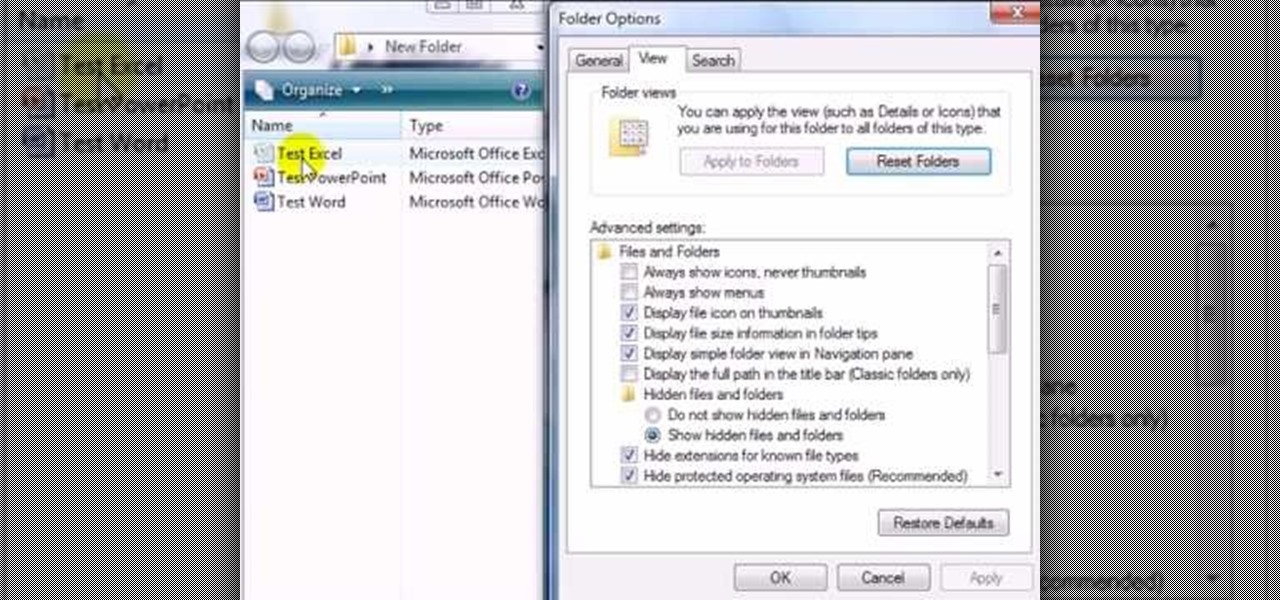
This video shows you how to easily hide or unhide files and folders and how to edit extensions of files. The first thing you have to do to hide or unhide files and folders is to open Control Panel and then open Folder Options. Next, click the View tab in the upper menu and check one of the following options: Do not show hidden files and folders or Show hidden files and folders. You can hide a file or a folder by making a right-click, then clicking properties and then check the Hidden File box...

1. Open Web Browser and go to WWW.Google.com and type crucial memory mechanic and press enter. 2. Click the first result found on the search page( i.e., lolo memory mechanic)

Learn how to make some casual, traditional, and unique dishes with tutorial help from myrecipes.com. In this video recipe, learn how to make black forest trifle for kids and the whole family. This is an awesome dessert for anyone. Chocolate cake, chocolate pudding, and dark cherries make up this easy, make-ahead dessert. And since it's low-sugar, it works with a diabetic meal plan.

In this video tutorial, viewers learn how to upload large files online for free. The website recommended in this video is Load2All It does not host any files, but it provides a interface to upload the file to several other sites at once. If the file exceeds the limit for any given site, Load2All will automatically split the file into RAR files, upload it into several mirrors and provides one download link. This video will benefit those viewers who have a large file...

Looking for an easy way to share big files over the Internet without having to pay for the privilege? With the right Internet services, it's easy. This home computing how-to from the folks at CNET TV presents an overview of a number of the better and most popular file sharing websites, some of which will permit you to upload files in excess of 1 GB. For more information, and to get started sharing your own big files over the web, watch this free video tutorial.

FLAC files are a great way to compress audi files. Unfortunately, iTunes does not support these files outright. But don't worry, you can make those files work on your Mac. This video will show you how make FLAC files compatible wiht iTunes.

Learn to restore four different types of files: deleted files, files from a damaged CD or DVD, files from a formatted hard drive, and files from unbootable hard drives.

The term "hacker" often has negative associations attached to it, yet the world is in dire need of professionals with hacking skills. White hat hackers are ethical computer hackers that use their hacking skills to pinpoint network vulnerabilities and patch them up before they can be exploited by the bad guys.

Creativity is one of our most unique features. We can dream up gods and demons and give them form through drawing. We can even take a two-dimensional surface and bring our ideas to life in three dimensions. It only takes a little training for our giant imaginations to blossom on the page.

Few things are more important than search engine optimization when it comes to increasing a brand's visibility online. Regardless of whether you're launching a new business from scratch or working as a marketing professional at a major corporation, you need to ensure that you're drawing the most people to your website and affiliate links by utilizing the latest and most powerful SEO tools and methods.

Tax season is always stressful, especially for entrepreneurs and small business owners. Rather than wait until March to get your finances in order every year, learning how to keep track of your expenses is a valuable skill that saves you and your business time, money, and plenty of anxiety.

Before the internet, acquiring enough data to analyze was challenging. Now we have the opposite problem: a deluge of data makes trying to sort through it nearly impossible. That's where data science comes in.

The overarching and expanding field of data science and analysis has become virtually inseparable from areas such as programming and development.

The augmented reality business was all about audiences this week. Vuzix looked for an audience with the Supreme Court of New York regarding a defamation lawsuit against an investor. Magic Leap held an audience with royalty, showing off the Magic Leap One in a rare public appearance. And Snapchat wanted to remind its consumer audience of all the things its camera can do.

Augmented reality business followers, we've got good news and bad news. First, the good news: Upskill closed another round of funding, this time led by strategic investors Cisco and Accenture. (Well, this is probably bad news if you're competing with them on the enterprise AR front.)

While augmented reality is a means for presenting news to their audiences to some media outlets, Bloomberg is interested in how the technology can improve the way journalists work.

With many of the companies working in augmented and mixed reality focused on the Augmented World Expo, the finance side of the industry has been relatively quiet.

Kryptowire, a company specializing in mobile security solutions, released a report on Tuesday, November 15 that exposed firmware in a number of Android devices that was collecting personally identifying information (PII) and uploading it to third-party servers without users' knowledge.