
How To: Play music on the Wii
This tutorial teaches you how to play music files on your Nintendo Wii using an SD card and the


This tutorial teaches you how to play music files on your Nintendo Wii using an SD card and the
Check out this video from Berkleemusic.com and learn how to export audio files in Digital Performer and expose your music to the world in today's most accessible format, the mp3.

A video on the basics of bittorrent technology and how to get started downloading a Bittrorrent client and torrent files.

Take that Flash SWF file with lots of open space(be it an animation walking around or maybe that slick semi opaque video, or maybe the more practical drop down menu) and use Dreamweaver, HTML, and CSS to place it on a div that floats above your site and allows you to see whatever is underneath of it.

Learn how to build a web-based form using HTML. This tutorial covers using Labels, Text Fields, Text Boxes, Radio Button Groups, Checkboxes, The Clear and Submit buttons, Drop down Menus, as well as many of the properties you can edit while building the form. The form will be ready to be linked with a PHP file for use when you are finished.

Learn how to export a Flash .SWF file and put onto your website using Adobe Dreamweaver.

Learn to use Photoshop and Imageready to add video to a graphics file.

The existing uninstall routine for the Mozilla Firefox web browser may leave profile data and a Program Files folder behind. This is how to remove it.
How to capture video from a camcorder, save file and then upload to YouTube using Windows Movie Maker.
A Cascading Style Sheets (CSS) tutorial. Learn how you can add icons or images to accompany links with common file extensions.

Adobe InDesign can create PDFs natively. In this video we'll see a rarely used feature that allows us to create rollover effects that work beautifully in PDF files. InDesign allows us to create buttons and using the States palette we can create rollover effects.

Elizabeth Jones explains how to export your finished project for the web using Windows Movie Maker. You can select Windows Media low bandwith to significantly decrease the size of your movie file.

GarageBand will recognize General MIDI program changes, so using standard midi files is even better than before. Find out how it works in this video.

The free download manager wget lets you download all the files on a page or directory with a single command. It also allows you to resume downloads after getting disconnected letting you start where you left off instead of starting the download at 0% again. Check out this tutorial and see how to install and use wget.

Find the biggest files on your computer ordered by size. Learn to order folder by filesize so you can find the ones harboring the most diskspace terrorists. Learn to clear up your private data automatically and wipe it clean from being undeleted.

Learn how to make Firefox's interface more minimal by removing the help, view, bookmarks, history, edit, and file menu buttons.

Making text look old and weathered, or rusty and corroded is a long standing effect but it's a good one to know. In this episode, Bert will show you how to do a nice, detailed weathered type from scratch. You may want to download his example files or full rez version to see a detailed view.

Don Schechter gives a rundown of system requirements and how to start, save, and choose settings for new projects using Adobe Premiere. To send your scratch disc, open the capture window by going to file and then capture.

Chances are if you’re using Adobe GoLive CS2, you’re probably also using Photoshop and maybe Illustrator too. The great thing about GoLive is that it works hand in hand with .PSD and .AI files. In this video Terry White will show you how to incorporate them into each other using Smart Objects.

It's no secret that Apple's Notes app supports attachments such as photos, videos, and web links, as well as other file types like PDFs, word documents, spreadsheets, locations on a map, and audio tracks. While images, videos, and document scans are simple to add on an iPhone or iPad, other file types aren't as easy — at least until you know how.
If you regularly run into issues opening images that use the .heic extension, the easiest solution is to convert the file into a more compatible format. Using apps like Photos and Preview on a Mac makes the process simple, but macOS Monterey just streamlined the process so that you don't even have to open an app anymore.

Samsung uses their own SamsungOne font for their Galaxy lineup. But if you're coming from an iPhone or another Android device, you might not love it. With the help of this mod, however, you're sure to find a font that's right for you.
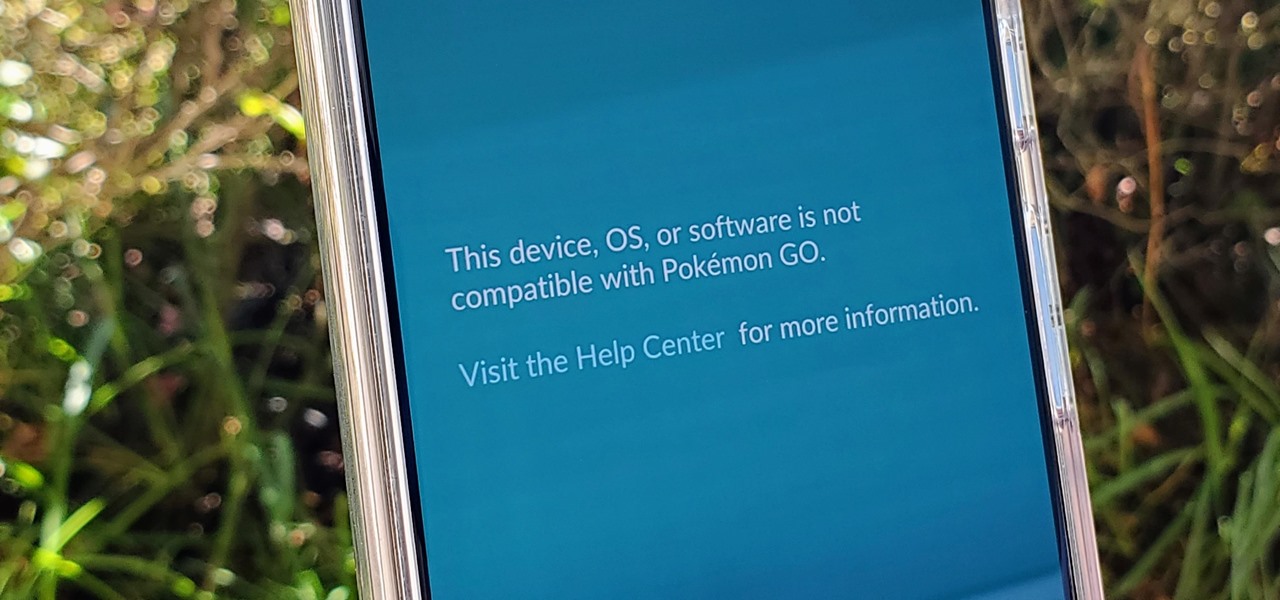
If you're a root user who has played Pokémon GO over the years, then you're probably familiar with the detection methods used to spoil your fun. The game's developer, Niantic, has publicly mentioned their ongoing battle with rooted Android phones and are unwilling to let up. They have a no-nonsense approach to try and keep you from playing, and they've stepped their game up once again.

Thanks to backups, Signal conversations can span over multiple years and multiple phones. These archives can get rather large as you share photos, videos, and other files with friends. But between the other apps and large files on your phone, you might not be able to afford to keep all those messages.

If left unattended, a hacker with a USB Rubber Ducky and physical access to the computer can infiltrate even the most secure computer. Such attacks often go undetected without the use of a tool like USBRip, which can provide you with assurance that your device hasn't been compromised.

In a stunning end-of-year twist to the Magic Leap versus Nreal legal saga, the China-based startup is now filing a motion against Magic Leap.

Samba can be configured to allow any user with write access the ability to create a link to the root filesystem. Once an attacker has this level of access, it's only a matter of time before the system gets owned. Although this configuration isn't that common in the wild, it does happen, and Metasploit has a module to easily exploit this security flaw.

Have you ever heard someone else's iPhone ringing and thought it was yours? Of course you did. iPhone ringtones are iconic, but not varied. If you're using one of the more popular iOS sounds, you'll likely encounter it in the wild multiple times. Why bother, when you can create your own custom ringtones right on your Mac.

Lenovo has done a great job preventing leaks of their new Moto RAZR. We've seen a few images here and there, but for the most part, we knew very little about the long-rumored phone. But with the announcement date just around the corner, an FCC filing has given us a look at the new RAZR from almost every angle.

While MacOS computers have been spared from some of the most famous malware attacks, there is no shortage of malicious programs written for them. To keep your computer safe from some of the most common types of malware, we'll check out two free tools. These tools can automatically detect ransomware encrypting your files and watch for unauthorized access to your microphone and camera.

KeePassX, 1Password, and LastPass are effective against keyloggers, phishing, and database breaches, but passwords managers rely on the operating system's clipboard to securely move credentials from the password vault to the web browser. It's within these few seconds that an attacker can dump the clipboard contents and exfiltrate passwords.

For many, the stock version of Android is often considered the epitome of what the operating system should look and feel like by default. It's clean and clear of unwanted extra apps that come pre-installed with the system, provides a fluid and fast user experience, and runs on just about any device that has an unlocked bootloader to install a custom ROM with the stock version ready to go.

In the latest update to the ongoing Meta Company patent infringement case, the court has responded to a request from the defendants, and the answer isn't good news.

With the number of web applications out there today, it comes as no surprise that there are just as many vulnerabilities waiting for hackers to discover. Finding those vulnerabilities can be a difficult task, but there are plenty of tools available to make the process easier. While it won't help find any zero-days, web scanners such as Uniscan will detect common vulnerabilities.

Augmented reality startup Nreal was a hit at this month's CES event, with some even calling the device a worthy challenger to the Magic Leap One.
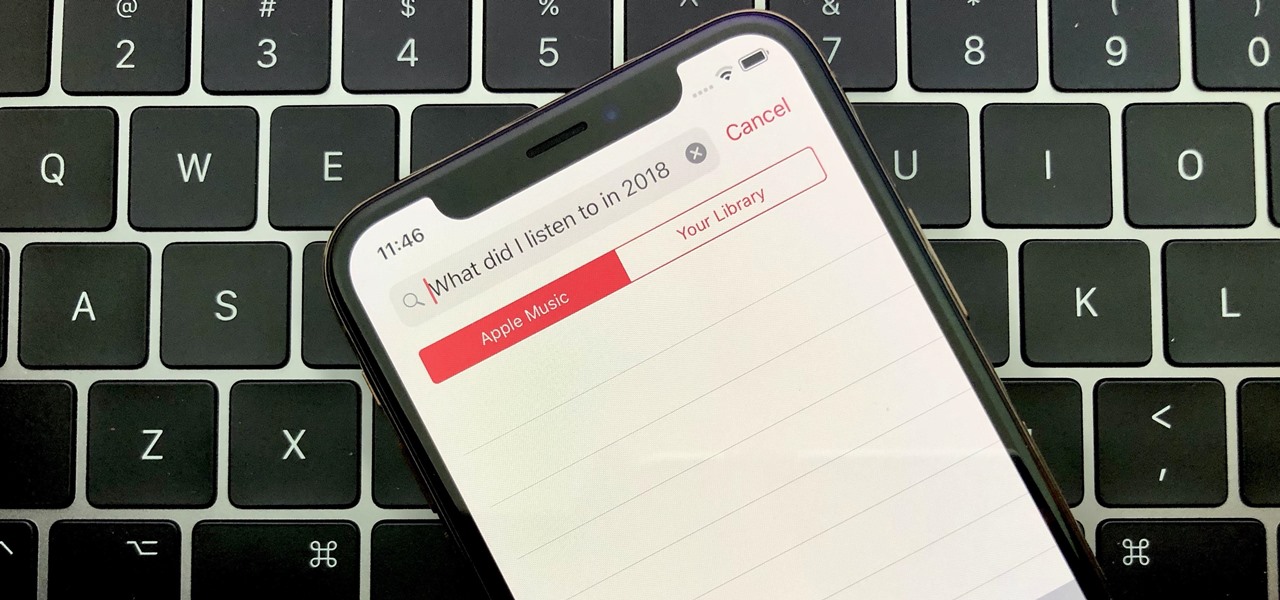
Around the end of each year, Spotify offers a year-in-review service so its users can see what they listened to the past year and share their listening histories in fun infographics. Apple Music does not have such a feature, unfortunately, but there is a way to curb that FOMO feeling this holiday season by downloading your listening history not just for 2018, but for the entire lifespan of your account.
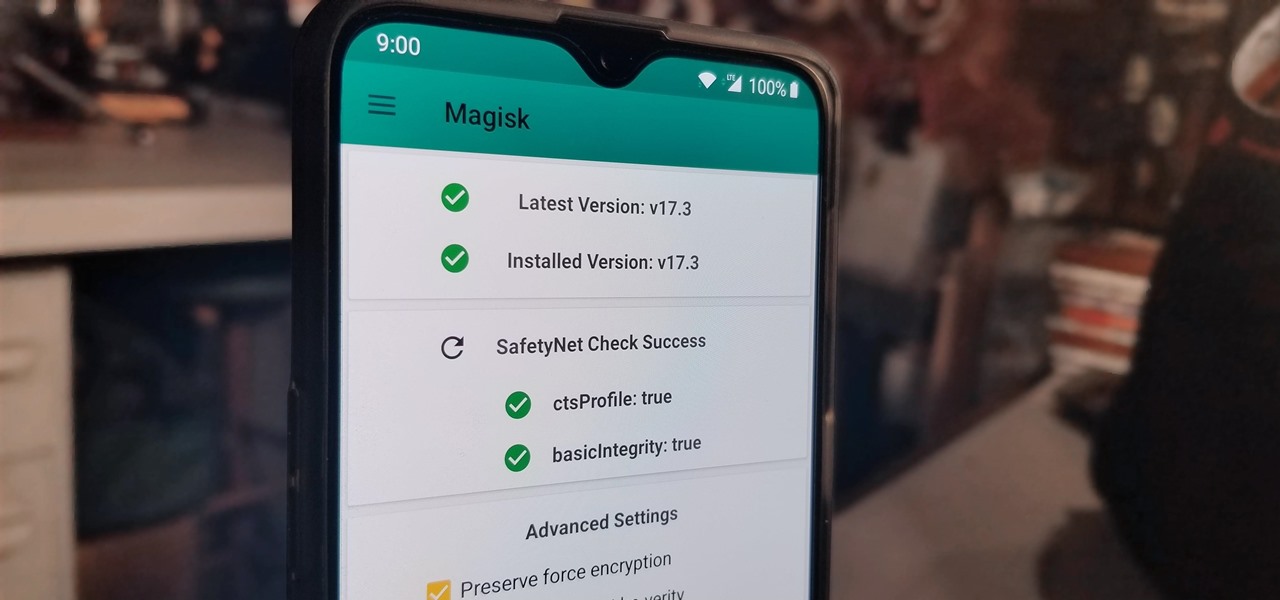
With the recent launch of the OnePlus 6T, the company continues to impress us with some of the best phones when it comes to the rooting and modding. OnePlus has made it easy enough to get up and running with the rooting process as fast as possible. The OnePlus devices follow the same core principles Google uses for their Pixels, which is excellent news for both the user and the development side of things.

In a previous tutorial, we were able to place the Mona Lisa on vertical surfaces such as walls, books, and monitors using ARKit 1.5. By combining the power of Scene Kit and Sprite Kit (Apple's 2D graphics engine), we can play a video on a flat surface in ARKit.

The ability to execute system commands via a vulnerable web application makes command injection a fruitful attack vector for any hacker. But while this type of vulnerability is highly prized, it can often take quite a bit of time to probe through an entire application to find these flaws. Luckily, there is a useful tool called Commix that can automate this process for us.

A powered-off MacBook can be compromised in less than three minutes. With just a few commands, it's possible for a hacker to extract a target's password hash and crack it without their knowledge.