Even though iOS 6 has only been out for a day, the folks over at iPhone Dev-Team have already released a Redsn0w jailbreak that works on the iPhone 4, iPhone 3GS, and iPod touch (fourth generation). As of right now, there's only a tethered jailbreak available, which means that you'll have to connect your device to your computer every time you power it up, but an untethered version that works on more devices is more than likely on the way. Until then, tethered is better than nothing, so here's...

Want to take advantage of your neighbor's super fast Wi-Fi connection? If they're smart, they probably have it password protected (otherwise you wouldn't be reading this, would you?). But if you have an Android phone, you can get back at them for always parking in your spot and slamming the door when they get home at 2 a.m.—by stealing...er, borrowing, their connection.

Yesterday, the entire Internet was talking about how the new Kindle Fire HD was supposed to be incredibly difficult to hack. Turns out, the folks over at XDA Developers are smarter than they thought—one day later, the mystery has already been solved. The exploit is the same one found by sparkym3 in Ice Cream Sandwich, but Amazon must have forgotten to patch it. As with any root, you can cause some serious damage, or brick your device completely if it's not done properly, so proceed at your ow...
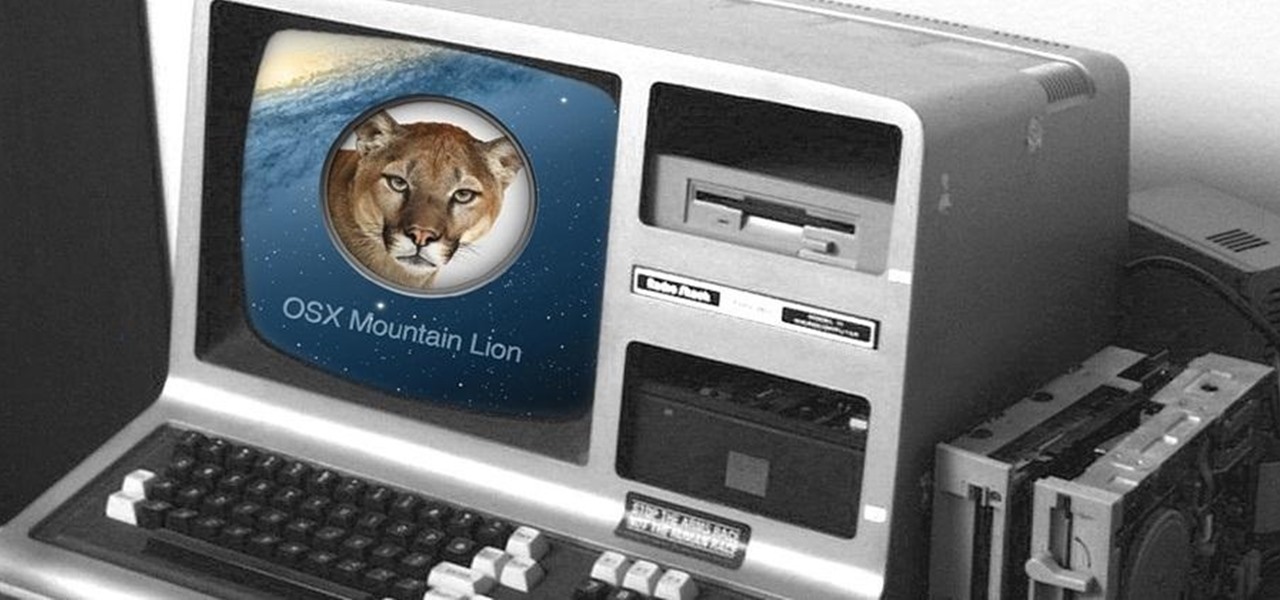
Have a PC but hate Windows? Maybe you've just heard a ton about the new Mountain Lion OS X and want to see if it lives up to expectations. Either way, you can install Mountain Lion on your Intel-based PC in a few easy steps. All you need is a copy of the OS X and an 8 GB USB flash drive. The first step is getting Mountain Lion onto the flash drive. You'll need to format the drive with one partition as Mac OS Extended, Journaled and select Master Boot Record under options so that it's able to ...

Even in the MP3 world, vinyl is still king among music lovers. Unfortunately, making your own record is nowhere near as simple as burning a compact disc or throwing some files onto an MP3 player. One clever inventor isn't letting that stop him though, putting together his own homemade vinyl cutter out of old parts. The end result—CD records!

Some of us use our smartphones for almost everything. Manufacturers know this, so they try to make their devices as convenient as possible to use, but sometimes that convenience comes with a cost to security. The very same technology that allows you to easily share music with friends and make purchases can also put you at risk. Photo by sam_churchill

You probably already know that your digital pictures have quite a bit of information embedded in them. What you might not know is just how much personal information is included in that metadata, including your camera information, and in some cases, even the precise GPS coordinates of where you took the picture.

If you want to send someone secret messages you have come to the right place. This is a way in which you can send secret messages to anyone without even making them get a clue that you have sent a secret message.

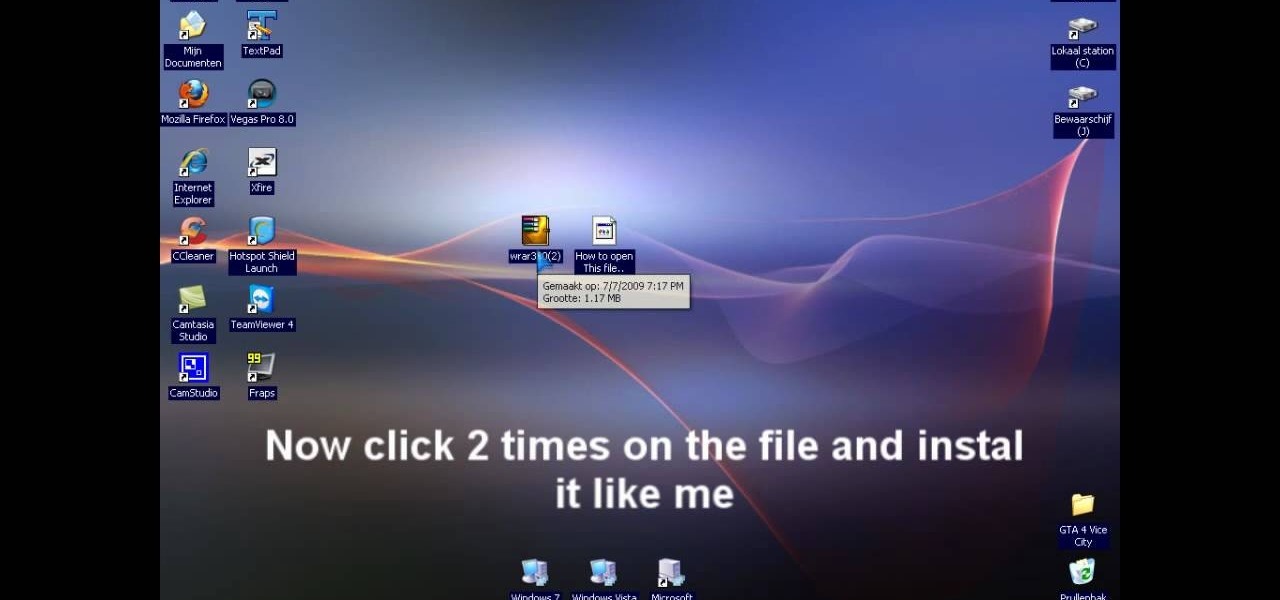
In this video tutorial, viewers learn how to extract .rar files. Begin by opening your internet browser and go to Google. Search for Winrar and select the 3rd result. Download and save the file. It is recommended to save it to the desktop to find it easier. Double-click on the file and follow the instructions to install it. Click Install and check all the file types for the program to be associated with. Once finished, open a file, select Extract To and choose the destination to save it. This...

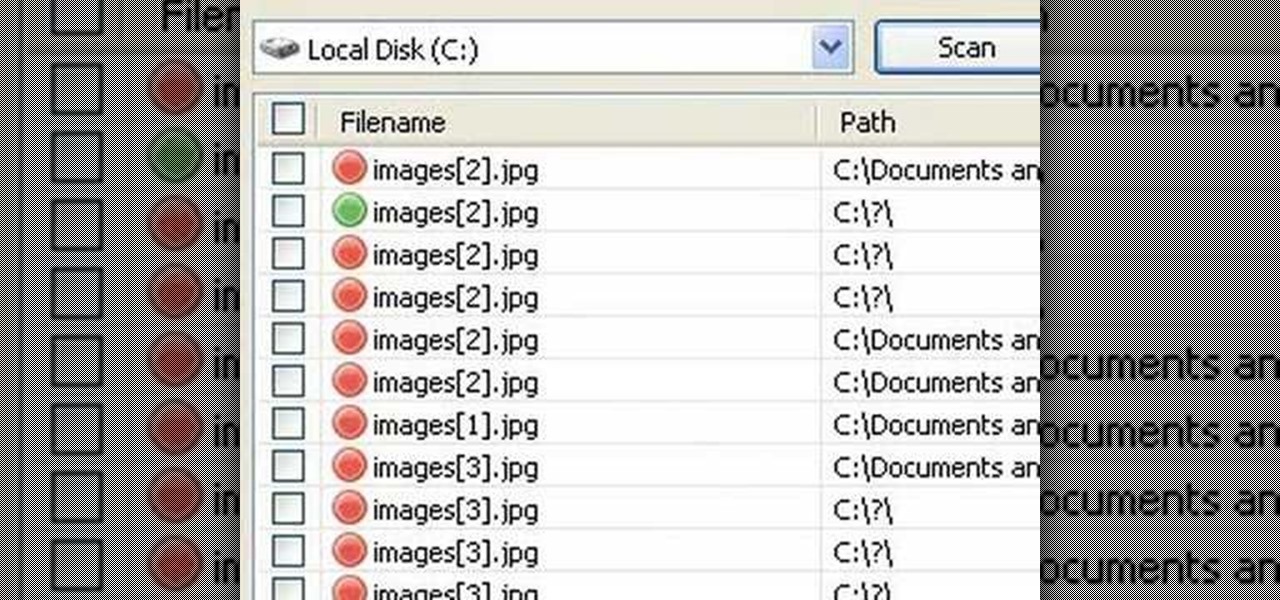
In this video tutorial, viewers will learn how to restore and recover deleted files using Recuva. Recuva is a freeware data recovery program. Recuva recovers files deleted from your Windows computer, Recycle Bin, digital camera card, or MP3 player. Begin by selecting the type of file and continue inputting the information. Then it will begin scanning the driver for the deleted files. It will then display all the deleted files. The green files are recoverable while the red ones are not recover...

If you loved The Da Vinci Code by Dan Brown, then listen up— there's been a new discovery found hidden within Leonardo da Vinci's most famous painting— the Mona Lisa.

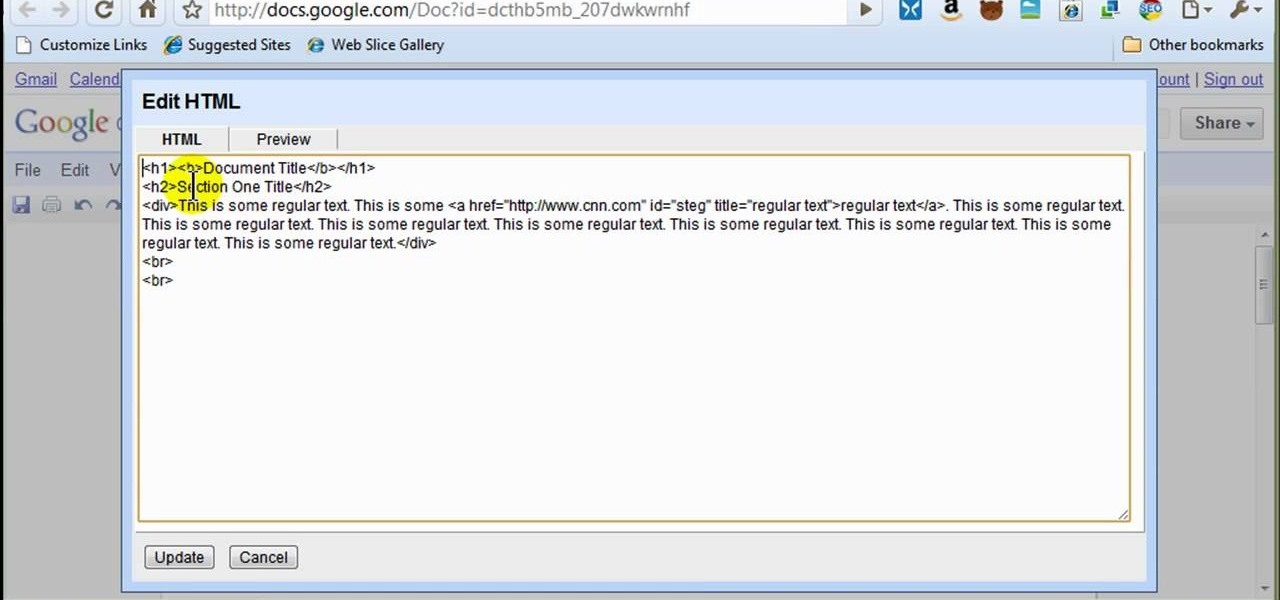
In this how to video, you will learn how to style documents with the Google Docs CSS editor. First, create a new document in Google Docs. First, click on the drop down menu for style. Type in a title in the document. Select heading 2 in the menu and type in the section title. Next, take off the style and type in the body for the content. Select some of the body text and click the hyperlink button. Type in the address and click okay. Now you can click this text to go to a website. Go to file a...

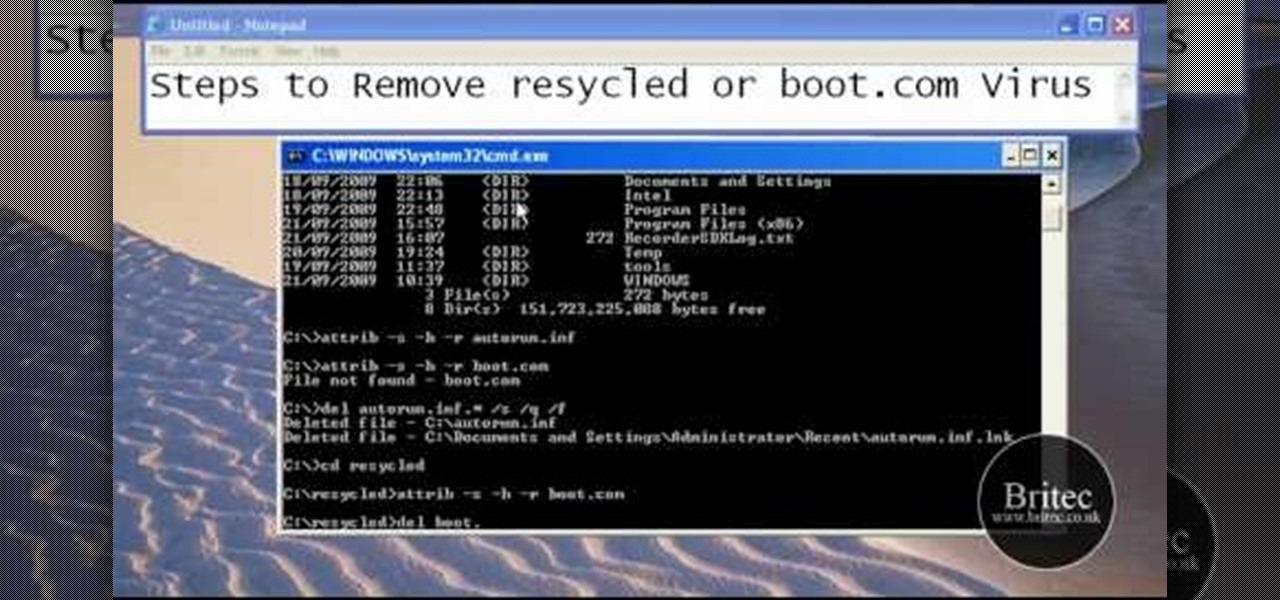
This tutorial describes the procedure to remove autorun.inf and boot.com virus. This virus is commonly called as resycled/boot.com virus, which could damage the system files and may steal important information from the system.This can be removed by any malware / spyware remover like Malewarebytes.

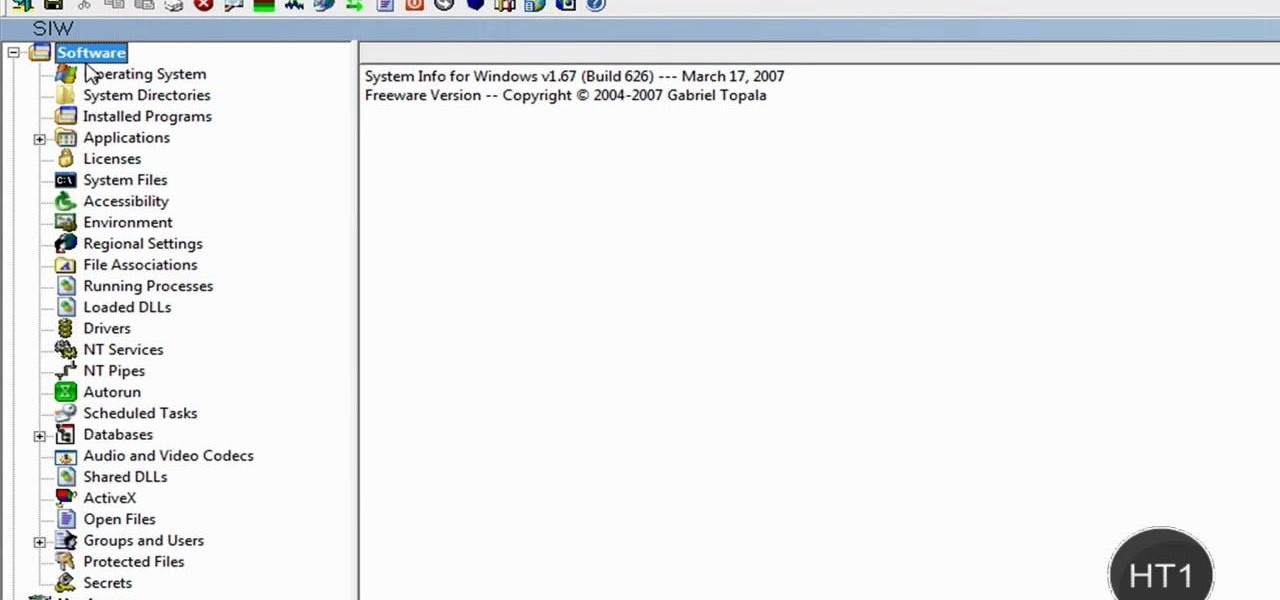
How to find out information / details about your computer? To find out the information about your computer, you need to download software from the website PC World. The following are the steps to download the software:

This video is a step by step guide for creating exposed teeth makeup . This is loosely based on the Harvey Dent character from Batman: the Dark Knight.

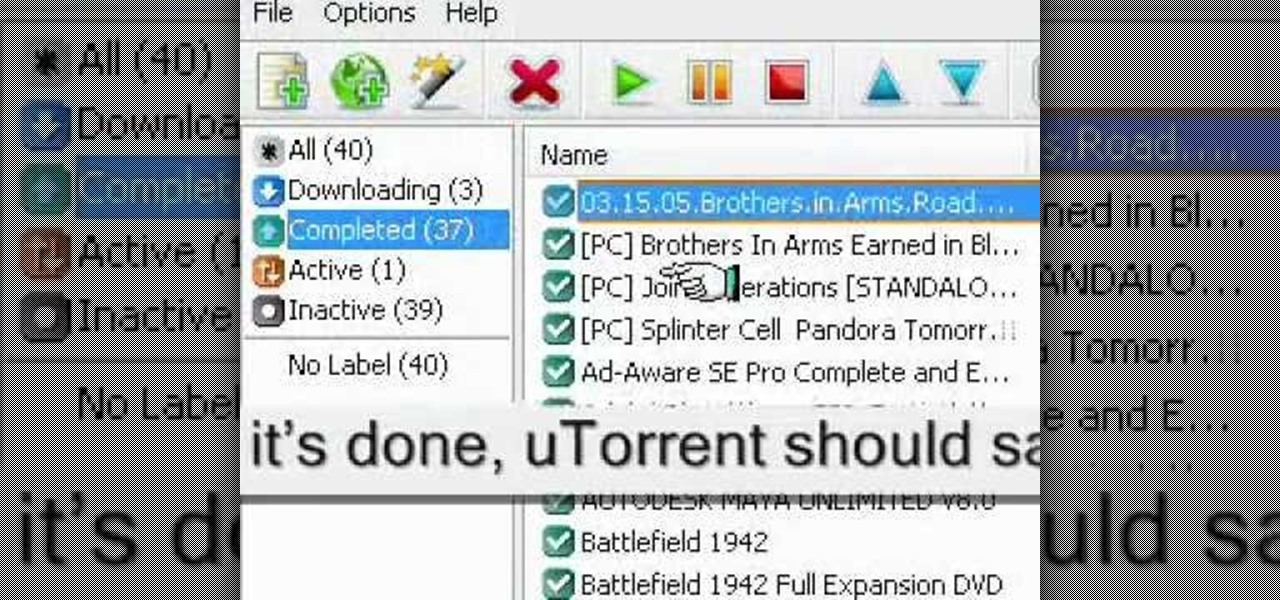
In this video tutorial, viewers learn how to seed a torrent in the u-Torrent client. Begin by downloading and saving your torrent file. Make sure that you uncheck Start Torrent when it opens. In u-Torrent, right-click on the file, go to Advanced and select Set Download Location. Now locate the torrent file and click OK. Then right-click the torrent again and select Force Re-Check. When it's done, u-Torrent should say that the torrent is 100% finished. Right-click the torrent and click on Star...

In this video tutorial, viewers learn how to unzip .rar files using Winrar program. Begin by opening your internet browser and download the program from the link in the video description. Wait for the time to pass and click Download. Select 32 bit or 64 bit, depending on your computer. Open the file and install the program by following the instructions. Once it's installed, select the file that you want to unzip. Right-click on the file and select Extract All Files. This video will benefit th...

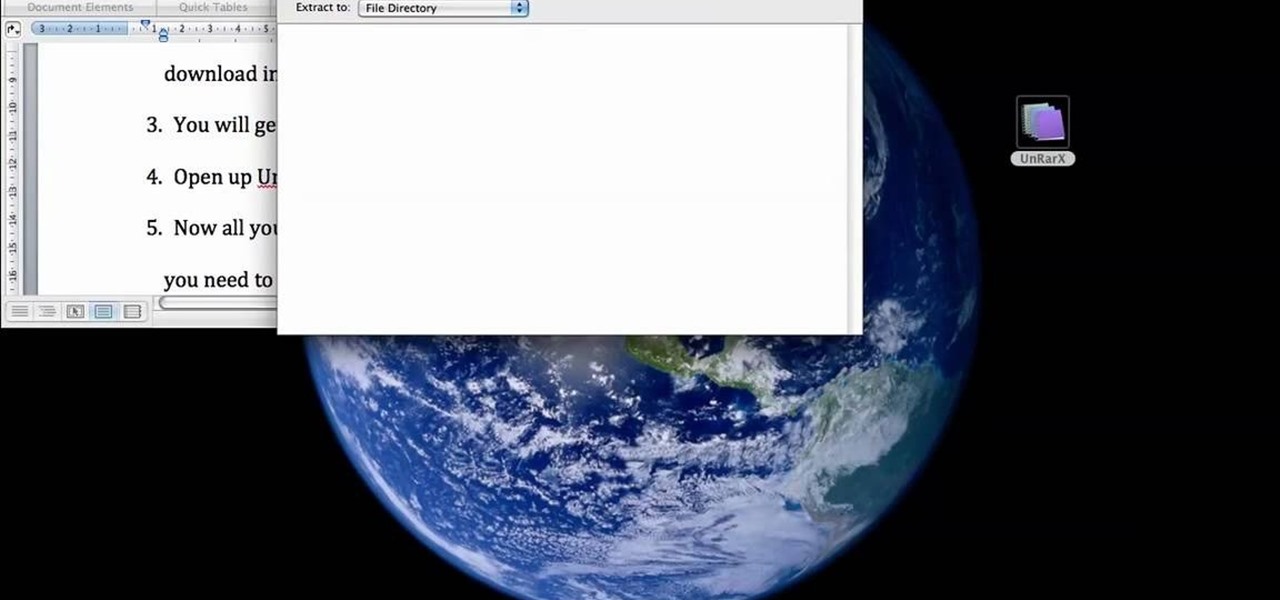
This is a tutorial that will learn you how to extract or unzip files on a Mac using UnRarX. First go on the site mentioned in the video scroll down and click on download. Go where you selected to download the file and open the program. Drag all the files you need to extract or unzip there then select the folder or destination where you want to get the files and the program will do all the work. The file you have selected to be unzipped or extracted will be in the place you selected and ready ...

The Dropbox utility can automatically sync your computer files with other devices each time you save them. In this tutorial, learn all of the steps you need to sync files with Dropbox.

gotbletu teaches you how to mount an ISO image file in Ubuntu using AcetoneISO2. You can see what's inside a regular ISO image in Ubuntu, but not when it's 'mdf'. The program you need for this is AcetoneISO2. Start the program and at the bottom of the main window you'll see a button called mount. Click on that and choose your 'mdf' file. The program also opens and mounts 'ISO', 'nrg' 'bin' 'img' files. After you've mounted your file you go at the top of the main Ubuntu screen to Places and yo...

In this video tutorial, viewers learn how to recover and restore deleted files using Recover. Recover is a freeware data recovery program. Recover recovers files deleted from your Windows computer, Recycle Bin, digital camera card, or MP3 player. Start by selecting the type of file. Continue by inputting the information. It will then take an hour to scan the drive for the deleted files. Once finished, it will display all the deleted files. The green files are recoverable and the red files are...

This video from The Survival Podcast explains how to find free eBooks and cool documents online. As an example, he Googles "permaculture" looking for PDF files. He suggests adding "filetype:PDF" to his search. By doing this, he finds more extensive information, including a 155 page document about permaculture. A PDF file is something that can be downloaded and used on a Kindle to read later. He demonstrates how to download the file to his computer. He demonstrates again by searching for "maki...

Importing entire folders of music files into FL Studio is a much more convenient way of importing files than one by one. This method imports an entire folder of samples or sounds for instant and easy access opposed to one sample at a time (wav, mp3, or whatever you may use). Watch and see how to import folders of music files easily in Fruity Loops (FL Studio).

This tutorial explains how to list files in a recursive manner within C#. It expands upon the code for writing a program that lists files, so if you can't do that yet, watch that tutorial first.

Your iPhone's clipboard can only save one item at a time, so it may seem impossible to retrieve your entire history of copied text, images, and other content. Luckily, there is a workaround you can use to find and copy your past clipboard contents, but you have to implement it first.

The legal battle between Epic Games and augmented reality startup Nreal isn't cooling off anytime soon.

The memories on your devices are precious, even if you don't often get a chance to revisit them. The worst thing in the world is when something happens to your computer or phone, and you end up losing some of those memories because your files weren't backed up or your microSD wasn't fireproof.

If you like to listen to popular songs from huge musicians and hard-to-find music from obscure indie artists, SoundCloud is for you — and you don't have to pay a dime. When you find a song you really love and want to play it back even when you're not connected to the internet, SoundCloud has offline listening, but there is a way to download your favorite tracks onto your iPhone for longevity.

Between all the streaming services you have to contend with, it's hard to want to go through the trouble of plugging in an adapter and loading up a DVD when you could find another movie without needing to move.

There's an easy way to take your PC to the next level — without any need for a hardware upgrade. The secret is in software that unlocks uses and productivity hacks you never knew you needed. Even better, right now, The Power User PC Software Bundle is on sale for just $59.99. That's 90% off the regular price of $614.

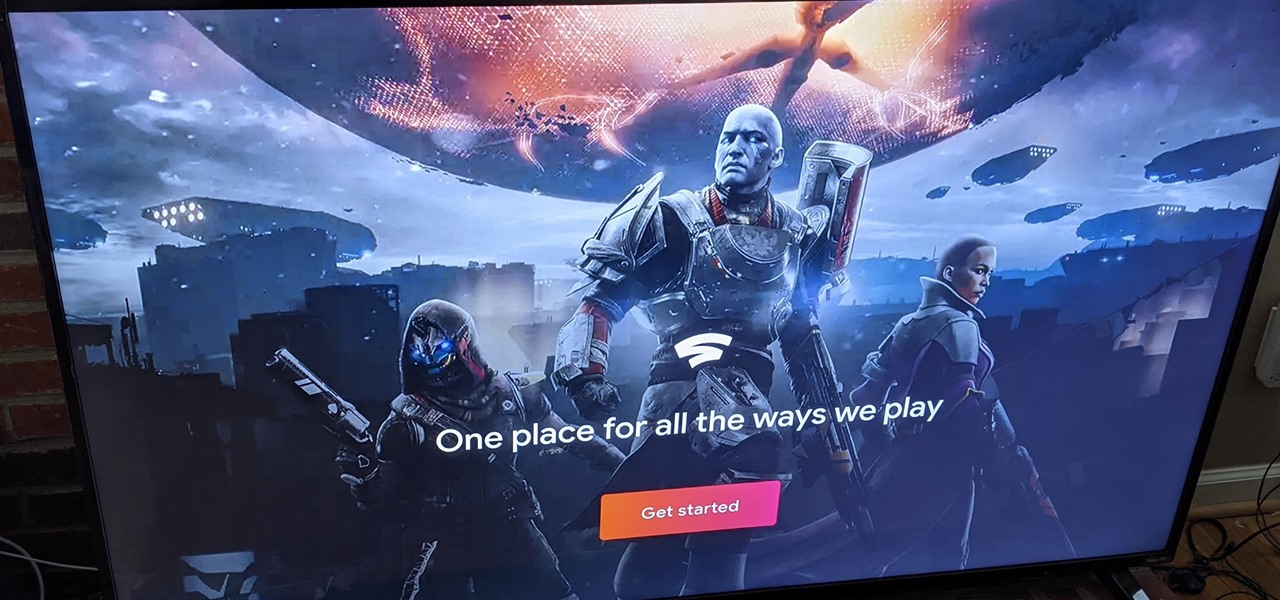
At launch, Chromecast with Google TV is fairly limited in the number of compatible apps. Many of the usual suspects are there, but there are some interesting omissions, like Google Stadia (though support is coming). However, at its core, the device runs on Android 10, which means you can sideload apps, including those that don't officially support Chromecast with Google TV.

Your iPhone's Voice Memos app is an easy tool for quickly recording lectures at school, jam sessions at the studio, or just verbal notes to yourself. While it's a straightforward app, there are several hidden features you might not know about that can improve the quality of your recordings.

Over the last few years, Apple has significantly improved and scaled up your iPhone's ability to edit photos. Using the Markup feature, which was introduced back in iOS 10, you can add doodles, highlights, important text, your signature, and arrows and other objects onto pictures and screenshots. One of the lesser-known tools in Markup lets you zoom into essential details without cropping.

For a hacker, there are a lot of advantages to creating a fake network. One advantage forces nearby devices to use their real MAC address if you happen upon a network that's stored in their preferred network list.

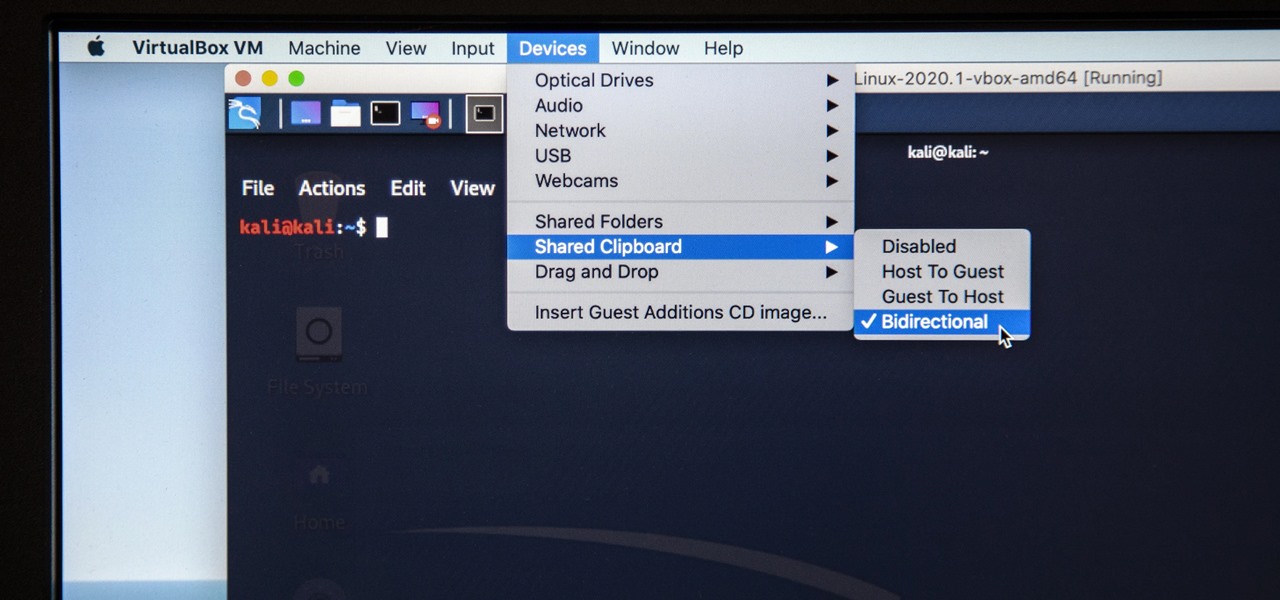
Last week, I updated VirtualBox on my computer since I had skipped a few versions, then I could no longer copy text or paste text from my Kali virtual machine to my host OS and vice versa. Installing the Guest Additions didn't seem to do anything, and the bidirectional shared clipboard was enabled, but there was one thing that did work for me that may help you out too if you experience the issue.

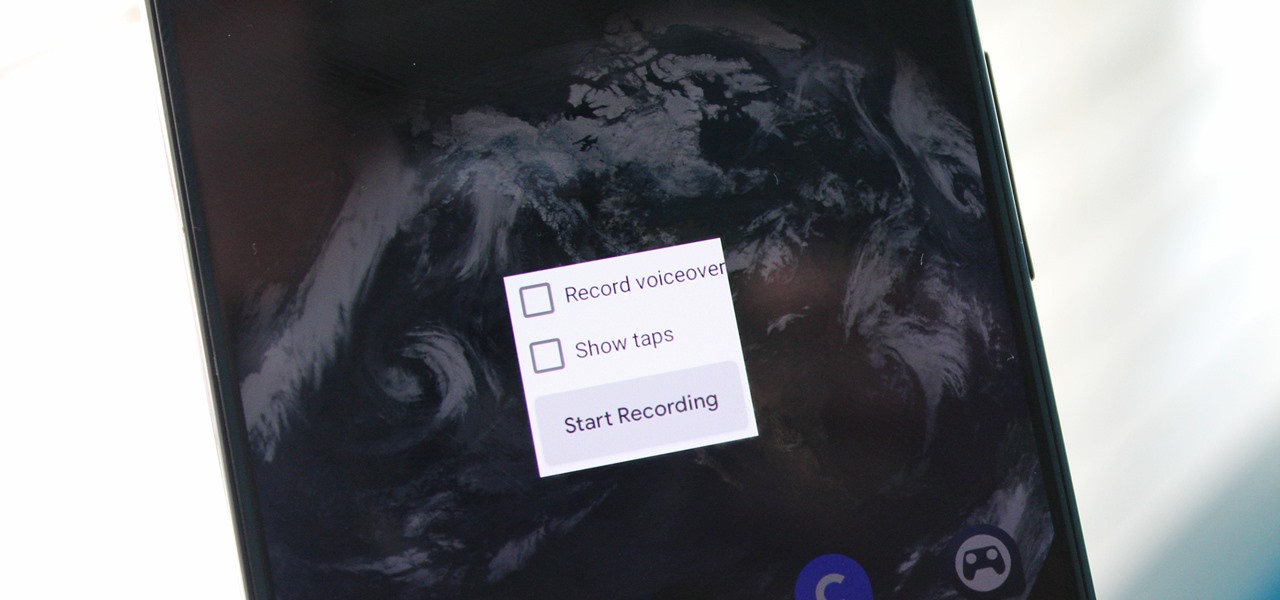
Downloading third-party screen recording apps can be dangerous. The primary function of these apps is being able to record everything on one's display, so it's easy to see how a malicious developer could exploit this for their own gain. That's why the addition of Android 10's built-in screen recording is so impactful.

A rather exciting development has recently surfaced in the jailbreaking scene for iPhone. The Checkm8 bootrom exploit was shown off to the public by axi0mX, which made way for the undefeatable Checkra1n jailbreak tool. With it, you can freely jailbreak a variety of older iPhone models without any restrictions. The success rate is quite high, too, when compared to other jailbreak methods.

One of the worst-kept secrets in the tech world is Apple's plans for consumer-grade AR smartglasses, still unconfirmed publicly and only recently corroborated through a leaked account of an internal employee meeting.

It's been said time and time again: reconnaissance is perhaps the most critical phase of an attack. It's especially important when preparing an attack against a database since one wrong move can destroy every last bit of data, which usually isn't the desired outcome. Metasploit contains a variety of modules that can be used to enumerate MySQL databases, making it easy to gather valuable information.

While SSH is a powerful tool for controlling a computer remotely, not all applications can be run over the command line. Some apps (like Firefox) and hacking tools (like Airgeddon) require opening multiple X windows to function, which can be accomplished by taking advantage of built-in graphical X forwarding for SSH.