I'm a pretty nice person, so when someone asks me to take a group picture of their friends or family, I can't easily say "no," even if I have somewhere else to be. Even worse—sometimes I'm the one asking, fully knowing just how annoying it can be. Maybe you've been told "no" before, and have had to settle for being left out of the picture, which kind of sucks.

Welcome back, my greenhorn hackers! After the disaster that was Windows Vista and the limited and reluctant adoption of Windows 8 and 8.1, Windows 7 has become the de facto standard operating system on the desktop/client.

Most people keep their ungodly sexual desires deep inside, only to be indulged in private on their computers. It makes you wonder... what secrets do your neighbors have? What kind of porn are they watching? And how much and for how long? Thanks to some public (and anonymous) data, you can now find out.

Lenovo brought out the big guns for CES 2014, with the Vibe Z showcased as the Chinese company's' first foray into the LTE smartphone space. Slated for a February release, the ultra-thin and extremely light smartphone will certainly be in the running for top smartphones of this very new year. Photo via CNET

Not particularly good looking, TouchWiz's lock screen adequately supplements the clunky and almost cartoonish-look of the infamous user interface on the Samsung Galaxy Note 2. While there are hundreds of lock screen options in the Google Play Store, I've never quite discovered one that I've thoroughly enjoyed, due to the obfuscation from so many options.

Welcome back, my hacker apprentices! I recently began a new series on digital forensics to show aspiring hackers what the forensic investigator can do and see while investigating a cyber attack. This is the second installment in that series and will focus upon network forensics. In other words, what can a network forensic investigator learn about the attacker during an investigation and how.

It's rare that a developer listens to the wishes of the masses, but that's exactly what CyanogenMod has done with their new CyanogenMod Installer, which automates the entire ROM installation process on your HTC One or other Android device. Previously, upgrading from the stock HTC One ROM to CyanogenMod required an unlocked bootloader, a custom recovery, the latest CM version, and Gapps. Let's be honest—unlocking the bootloader is a pain the ass, and probably the only reason stopping most peop...

My favorite type of video game is first-person shooters, and the one that started it all for me was GoldenEye 007. There was just something about the controls, fast-paced action, and free-roaming environment that got me hooked.

You probably know Lenovo from their low-cost Windows PCs here in the states, but something you may not be aware of is that they also make smartphones. Right now, their biggest market is in China, but a rumored merger with BlackBerry could make Lenovo a contender in North America, not to mention one of the biggest smartphone manufacturers in the world.

Welcome back, my hacker novitiates! Finding vulnerabilities in systems can be one of the most time-consuming tasks for a hacker. There will be times, though, when you'll find yourself in a position that you know that a particular port represents a vulnerable application or service.

If you want to play games that aren't in the iOS App Store, Apple makes it pretty tough for you. Usually, the only solution is to jailbreak your iPad or iPhone, but that's something most avoid because it will void the warranty and may cause potential bricking issues.

Remember that PSP you had? I pretty much dropped mine when smartphones became more prevalent in the mobile gaming scene. Why would I want to carry around a huge PlayStation Portable when I've already got an Android in my pocket?

These days, you can find a digital version of almost any form of entertainment. Being able to download or stream content is convenient for a lot of reasons—you can avoid going to the store and you never have to worry about late fees on rentals.

In the Harry Potter world, there was a character by the name of Beedle the Bard, who told a story about witnessing the three Peverell brothers building a bridge out of magic and successfully crossing a very dangerous river that had claimed many lives.

The stock music player on the iPhone hasn't changed much since its inception. Sure, with the recent iOS 6 update the design became sleeker, but it's not really what you'd expect from a top of the line smartphone. And when I say "MEH," it isn't directed towards the Kendrick Lamar album (which is awesome). It's the layout of the application, the lack of gesture control, and the sometimes tedious job of shuffling through certain albums and artists.

I know what you're thinking—taking a screenshot is super simple. While that is partly true, taking of a screenshot of the Start Screen in Windows 8 is little bit tricky, unless you're on your Surface.

Since it's October and Halloween is fast approaching, it's time for a series of articles on how to make the coolest Steampunk Halloween decorations for your home! In this installment, we'll look at some jack-o'-lanterns, skulls, and a few other things that are easy to Steampunk, but will still keep that "spooky" Halloween feeling.

If you don’t have any little children to blame for an inadvertent or misguided app, book, or music purchase from Apple, you might still have a fighting chance. Apple has a very strict return policy, specifically stating that all sales and rentals of products are final for purchases made in the iTunes Store, Mac App Store, App Store, and iBookstore. But if you play it carefully and do a little digging, a return and full refund may still be possible.

With the upcycling revolution, folks are turning their otherwise useless junk into something functional for the home. Practically anything that you would normally toss or recycle can be reused for a bigger and better purpose. Your milk jugs, chopsticks, toilet paper cardboard, glass jars, and even your old junk computer keyboards can be upcycled into something totally useful around (or away from) the home.

The final chapter of Christopher Nolan's Batman trilogy is here, The Dark Knight Rises, and if you're anything like me, it made you want to immediately don a cowl of your own and run around punching criminals. Don't forget though, one of the most awesome aspects of Batman is his never-ending supply of crazy gadgets. Unfortunately for most of us, we don't have a billion dollars, nor Morgan Freeman, so we'll just have to make do with some good old-fashioned DIY tricks. Read on for a rundown of ...

As I said before in my earlier post on how to make a two-tone doorbell, sound is more than just music. Note blocks can create a wide variety of notes and sounds, and those can be used for more than just making a stirring rendition of "Still Alive" from Portal.

In last Saturday's workshop, the tutorial was on the ABBA switch, so named because it fires redstone pulses in A-B-B-A order. While the turnout was low, it was a really productive workshop! We experimented with a lot of things and had a great time. Hopefully you'll consider joining us next time!

We've already done a tutorial explaining why buttons are superior to levers, but now I want to show you a way to make them even more useful than they already are. You can't get this sort of functionality with levers!

I always found that those safety lights for bicyclists on the market were never good enough when riding in the dark. That got me thinking about people who use wheelchairs and how unsafe the night could be when they want to go out. So here's what I came up with:

In general, hacking and information security is not just one discipline, but a number of them, and today we will look into some of the networking concepts.

A flaw in WPS, or WiFi Protected Setup, known about for over a year by TNS, was finally exploited with proof of concept code. Both TNS, the discoverers of the exploit and Stefan at .braindump have created their respective "reaver" and "wpscrack" programs to exploit the WPS vulnerability. From this exploit, the WPA password can be recovered almost instantly in plain-text once the attack on the access point WPS is initiated, which normally takes 2-10 hours (depending on which program you use).

We've all seen the breathtaking, colorful photos of the Eagle, Egg and Cat's Eye Nebulae. You may not recognize them by name, but you've seen them, whether in astronomy textbooks, magazines, websites, album covers, or tee shirts. They are some of the most striking photographs ever taken from the Hubble Space Telescope (HST).

If you loved The Da Vinci Code by Dan Brown, then listen up— there's been a new discovery found hidden within Leonardo da Vinci's most famous painting— the Mona Lisa.

Dogs are one of the simplest animal to draw. In the first step draw a small stick i.e. simple line with two arms below and a small round on the top. In the second step draw a round circle outside this one. In the third step draw semi-circle on top of the circle adjacent to the outer circle. In the fourth step draw two small circle for the eyes inside the semi-circle and make a small dot inside the small circle. In the final step draw the ears on both sides equally in the way such that it shou...

All sports require physical conditioning. Volleyball is no different. Learn how to do physical conditioning for volleyball in this video tutorial.

This tutorial teaches you how to create an animated cursor for Windows. The cursor is created with RealWorld Cursor Editor 2007.1 with 3D module installed.

If you're on the hunt for a profitable side-gig, or even a completely new way to to make money, you'll want to take a look at Upwork, a leading freelancing platform that connects skilled freelancers with clients from all over the world.

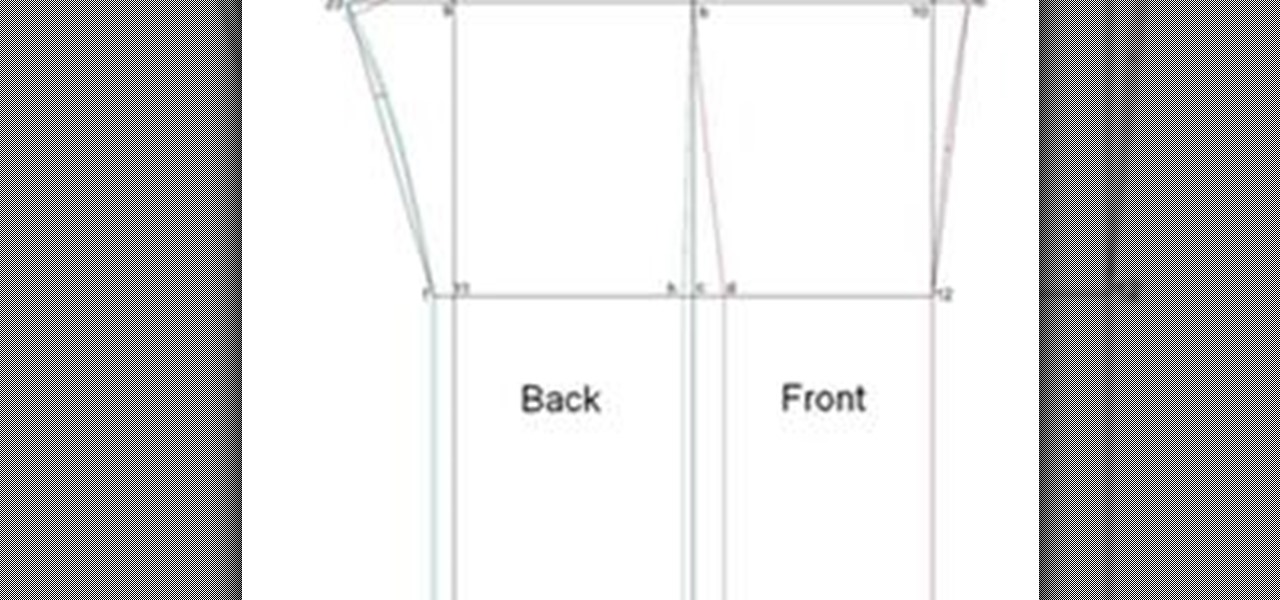
Written Instructions with accompanying video for anyone who wants to make a basic pant exactly to your measurements! Please get your correct measurements before you begin from How to Take Your Measurements.

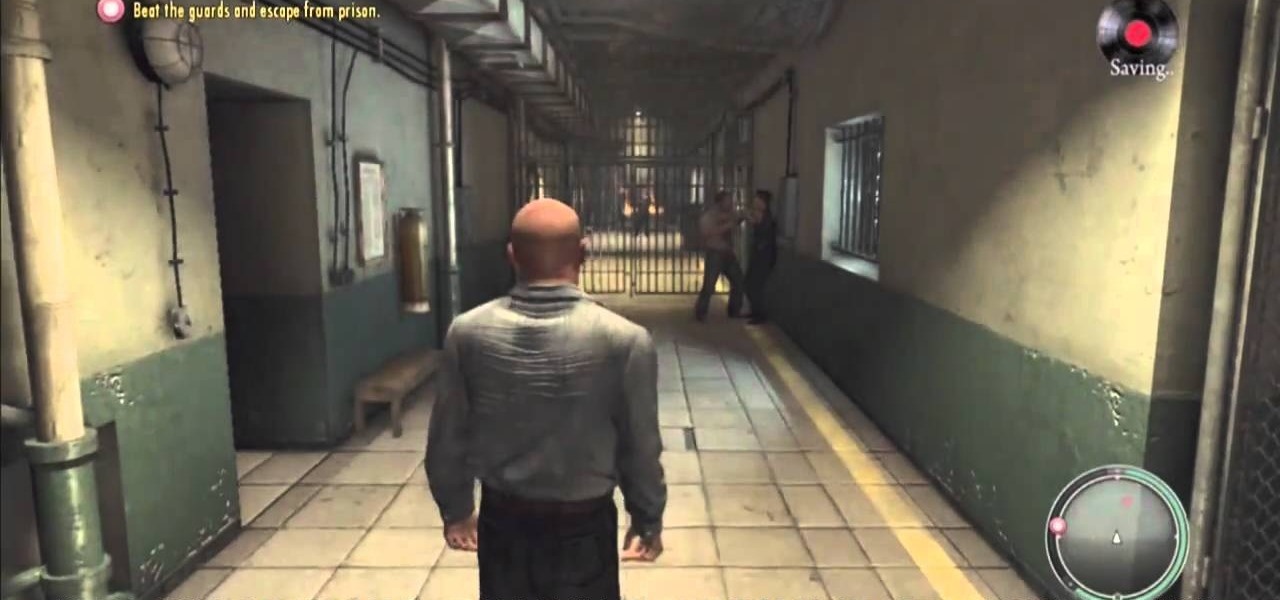
There's a new download available for Mafia II on the Xbox 360 (and PlayStation 3), and this walkthrough series will cover the entire gameplay for "Jimmy's Vendetta", which follows the first DLC for Mafia 2, "The Betrayal of Jimmy" (only available for the PS3). This is a lengthy add-on to Mafia II, so watch and learn to see everything involved with getting out alive, as both the Italians and Irish.

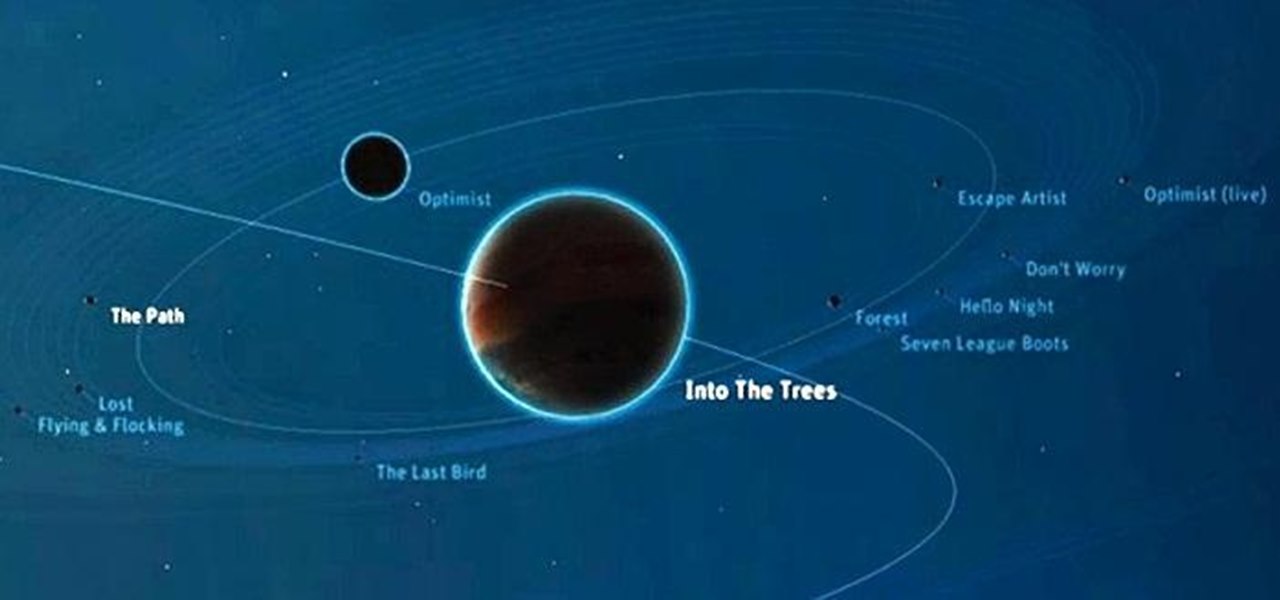
Watch a 41 part series on Spore's Space Stage. How will you create the universe? With Spore you can nurture your creature through five stages of evolution: Cell, Creature, Tribe, Civilization, and Space. Or if you prefer, spend as much time as you like making creatures, vehicles, buildings and spaceships with Spore’s unique Creator tools.

Before painting your vehicle, you'll want to sand down the primer coat. This automotive video will show you how to block-sand the primer to prepare you for the actual paint job. It's actually a pretty simple step in auto painting.

Mrs. Victoria explains us how to change the language on your Keyboard (Windows)1. Go to the control panel and select the option ‘Change keyboard or other input methods’ and a dialog box (regional and language options) pops up.2. Click on change Keyboard, and another dialog box pops up.a) In the new dialog box, click ADD Button, and select the input language you require and click OK.3. You have the feature to alter your language input whenever you want by coming to this (Change keyboard langua...

As an adult you will come a cross a point in time when you need to make the right impression by writing a formal letter. Follow the format and you will be able to be most effective at conveying the information in your letter.

Well here it is. The ending of spore. We finally made it to the Center of the Universe. We also made it to the end of the galaxy, as well. This is a walkthrough of the absolute last stage of Spore. This is both the center of the universe and end of the galaxy.

In this art video series, learn how to make wheel thrown clay pottery. Our expert will give you step-by-step instructions to make your own pottery, including basic wheel techniques like mounting the clay, shaping it and creating the opening, an explanation of the greenware and bisqueware stages, painting, and final firing of your piece in a kiln. These beginner pottery videos will help you discover the art that people have been practicing since time immemorial.