One day, your car may break down and you won't be able to afford to hire a mechanic, so what do you do... you look on the web for some how-to vehicle repair videos and become your own car mechanic, that's what. You don't need any advanced training to perform repairs and simple maintenance on your automobile, but you may need a few tools. Invest in the basic tools and you'll be prepared for just about any car malfunction you can think of. These tutorials will help get you on your way, as long ...

Watch this video series to learn how to start the conversion process of an Adobe Photoshop mockup of a website, into a real live CSS based website.

As the holidays draw closer and closer, stores are getting more and more crowded, and of course, many have put off their Christmas shopping until the very last minute. Why not avoid the mall rush this holiday season and make a personalized do-it-yourself snow globe to gift to those closest to you? This is also a perfect opportunity to put of those cell phone photos that you've been snapping to use! What You'll Need

Bowling is such a fun group activity and is perfect for birthdays and other types of gatherings. However, if you are not a pro bowler the scoring system can be pretty confusing. This tutorial will walk you through the steps of keeping score so you will know a strike from a spare and everything in between.

All of these four videos are excellent. You will notice that while all the videos and articles have slightly different design dimensions, they are fundamentally very similar. I urge you to view and read everything I am serving up. Then, my final words of advice are simply....choose between a barbeque switch and a taser gun. (Hint: there is a right choice, and there is a wrong choice.)

Kiwua demonstrates how to make squares friendship bracelets. There are 3 pink threads on the left, 2 black threads in the middle and another 3 pink on the right. First, you take two from left and make a knot from left to right. Then, with the same threads, another knot from right to left. Now you take the next two, a pink one and a black one and makes a knot from right to left. She repeats this action, the same way. After that, she takes the next two threads and knots them from left to right....

Enter the game and select Stage 1. Click on the rock above you to make a snake come out. Click on the cactus and drop it on the snake to make a hat. Stage 2: Click and drag the trash to the right and click on the lamp. Click on the taxi that will appear to pass Stage 2. Stage 3: Click and drag the brick to the glass above to break it, open the door, and turn on the lamp. Grab the antenna and put it in the black hole on the edge of the building. Stage 4: Click on the boat and then click on you...

Learn how to make an origami catfish. Get a piece of square paper. Fold diagonally from the upper right tip to the lower left tip of the paper. Fold the lower right tip to the upper left tip and open it up halfway. Hold the right fold and slightly open it placing your finger inside the flap. Gently press downward to create a square-shaped fold on top. Grab the left side of the square and fold it towards the right. Grab the other fold, the one made earlier, and do the same fold as the one done...

Apple's exclusive chat services, iMessage and FaceTime, force many of us to stay locked into iOS, iPadOS, and macOS to communicate with other Apple users, so chatting with Android-using friends means SMS texts, third-party messaging apps, and third-party video chat services. However, Apple is breaking boundaries with iOS 15 so that we can FaceTime with Android, Linux, and Windows users.

At its height, the COVID-19 pandemic forced many auto showrooms to close their doors. As the pandemic persists, many consumers are still hesitant to let their socially distanced guard down.

Getting files from an Android device to a Mac or iOS device is not always easy or convenient, and the same goes for transferring content from a Mac or iOS device to an Android device. But we're here to tell you there is a better way than using USB cables, email, and cloud storage, and it gives you the look and feel of AirDrop.

Google Meet might not have virtual backgrounds like Zoom, but it hits all of the other basics, from hosting many multiples of video participants to sharing your screen, that you'd expect from a robust video conferencing platform.

No website, service, or platform is immune to being abused or exploited by hackers, and Google Analytics is no exception. To better understand how Google Analytics can help deliver payloads and bypass security protocols, one might want to learn how to use Google Analytics from a user's perspective first.

We're living in uncertain times. The sudden outbreak of the novel coronavirus and subsequent self-isolation of roughly half the world's population has led to a massive reorganization of the economy, countless layoffs, compromised security networks, and a variety of other significant disruptions that will forever alter the landscape of our daily lives.

Without admin privileges, installing additional software, or modifying the Windows 10 firewall, an attacker can alter a router and perform a variety of exploits. It's accomplished by forwarding requests from Kali through a backdoored Windows computer to the router gateway with simple SSH tunnels.

Though Microsoft has had trouble keeping up with the demand for HoloLens 2, the company has been able to supply modified headsets to the US Army.

Google has always experimented with Chrome's UI, but when they make more drastic changes, they start by hiding them in the feature flags menu. One of the latest designs makes Chrome more accessible in a world of big and tall phones.

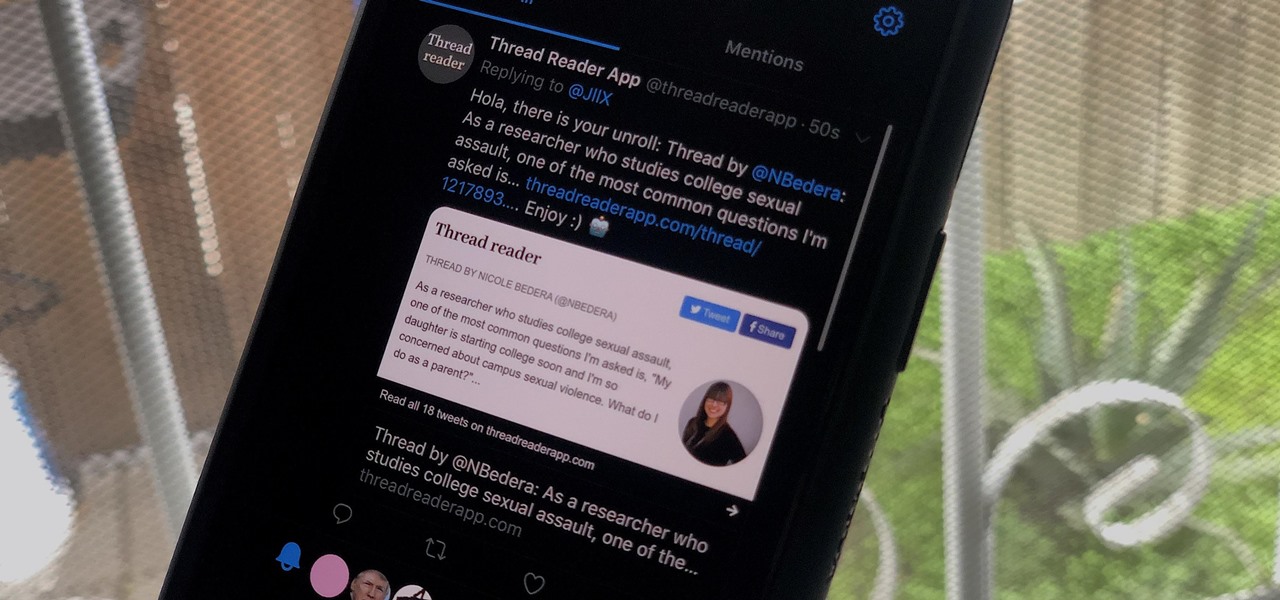
While tweetstorms were a part of Twitter since the beginning, threads, which makes tweetstorms more viable, didn't show up until late-2017. Still, threading multiple tweets at once to create long-form stories, opinions, tirades, and other lengthy Twitter posts, can be hard to digest. However, you can make reading them easier with just a single message.

Router gateways are responsible for protecting every aspect of a network's configuration. With unfettered access to these privileged configurations, an attacker on a compromised Wi-Fi network can perform a wide variety of advanced attacks.

Screen recording on your iPhone is one of the easiest ways to share what's happening on your screen with family and friends. The problem is, everyone knows it's a screen recording when you pull open Control Center to tap the record button. What if we told you there's a better way to end a recording, so what you're left with is a clean video?

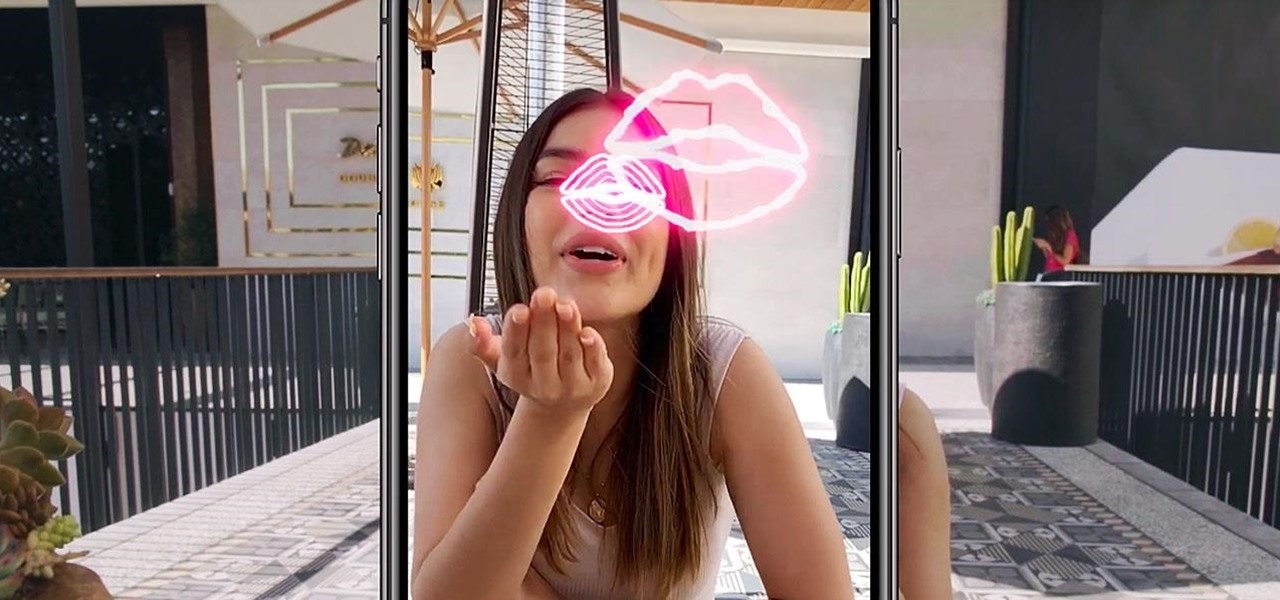
Sending Christmas cards via snail mail is so passé. Why spend the time and money for a bougie photoshoot, saccharine card design, and postage when you can use augmented reality to instantly dress up photos and videos to send to friends and family instead?

YouTube Music has been around since late 2015, but it only started becoming a viable music service in 2019. It makes sense for Google to utilize YouTube's existing library of music videos, remixes, and cover songs to create one massive music platform. But one downside is you get a lot of the music video versions of songs instead of the album versions. Thankfully, you can change this.

The longest-running children's television show in the United States, Sesame Street, hasn't survived 50 years without leveraging new technology along the way.

Bus stops can provide shelter in the event of rain, and now they also protect you from augmented reality squid.

If you have devices that run different operating systems, you know how frustrating it is that Apple's Calendar app isn't available on other platforms. If you use Siri to quickly create an event on your iPhone or Mac, you're not going to see that event on your PC or Android tablet unless you sync your calendar to another service.

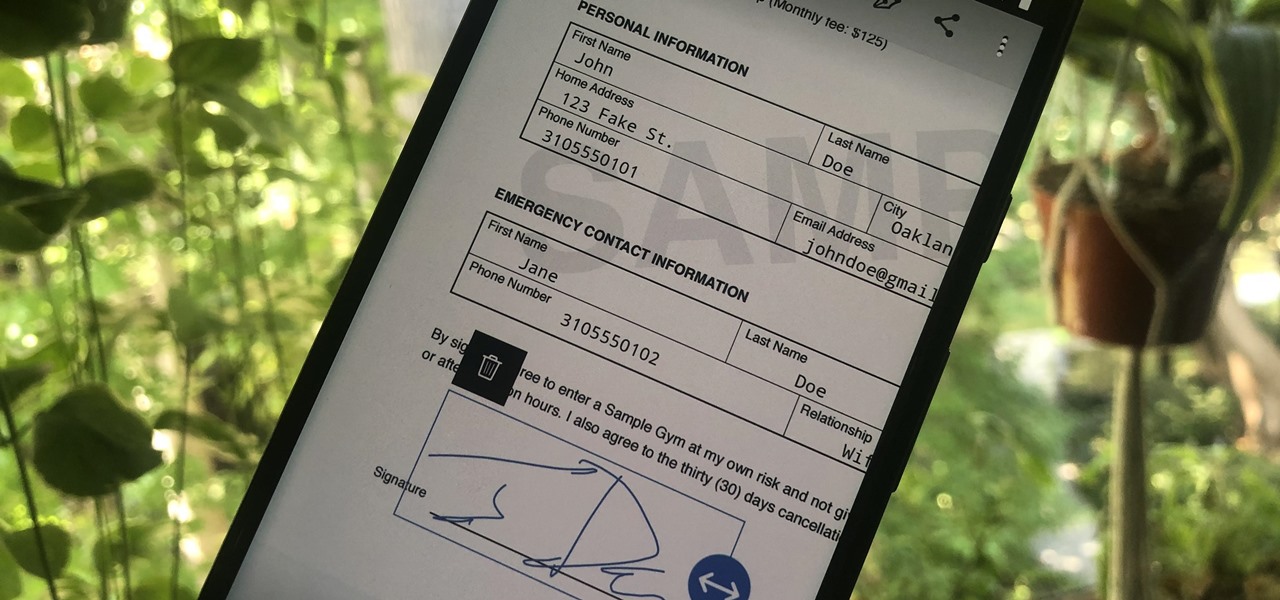
Adobe is best known for its photo and video editing software, but they also have a number of lesser-known apps that you may be interested in. Adobe Fill & Sign, available on iPhone and Android, is the best way to electronically fill out important documents on your smartphone with a third-party app.

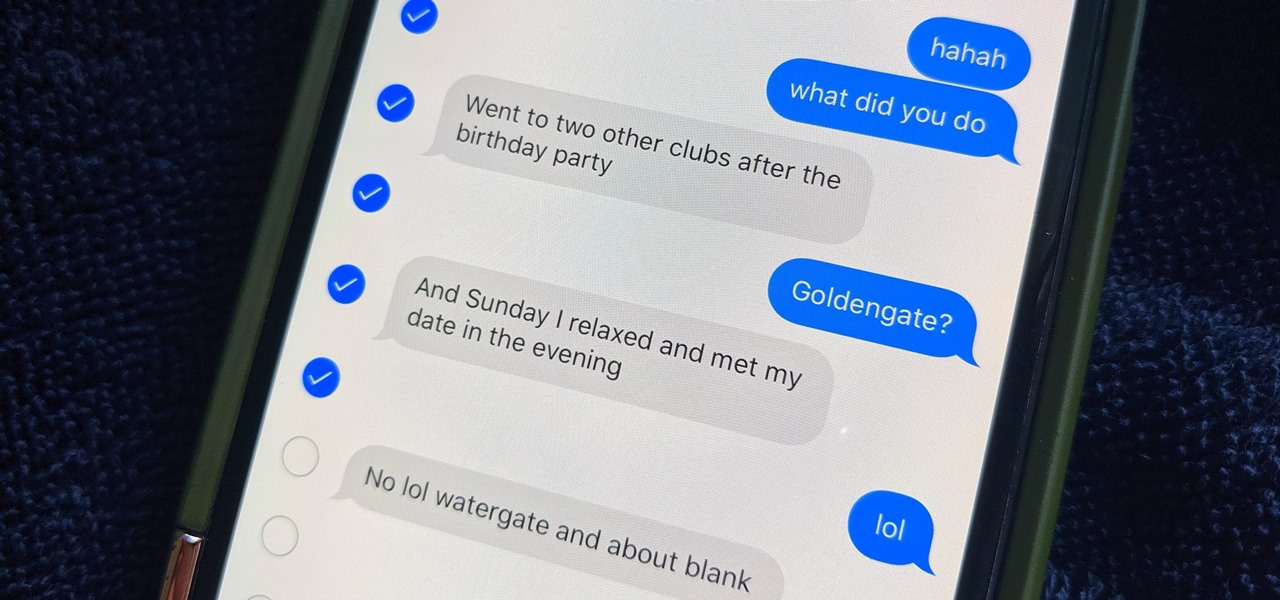
You don't need to delete an entire thread in the Messages app to get rid of a couple of texts on your iPhone. With a few taps, you can remove unwanted iMessages and texts, as well as storage-hungry photos and videos, to de-clutter a conversation. And in iOS 13, the process is even easier.

The idea of a world without passwords used to be a pipe dream. But as we inch closer to making that a reality, we have services now that securely store all of our passwords under a single master password. It's a convenient way to keep our accounts safe and sound without having to remember all of their credentials. And there's no reason to be afraid — I'll explain why.

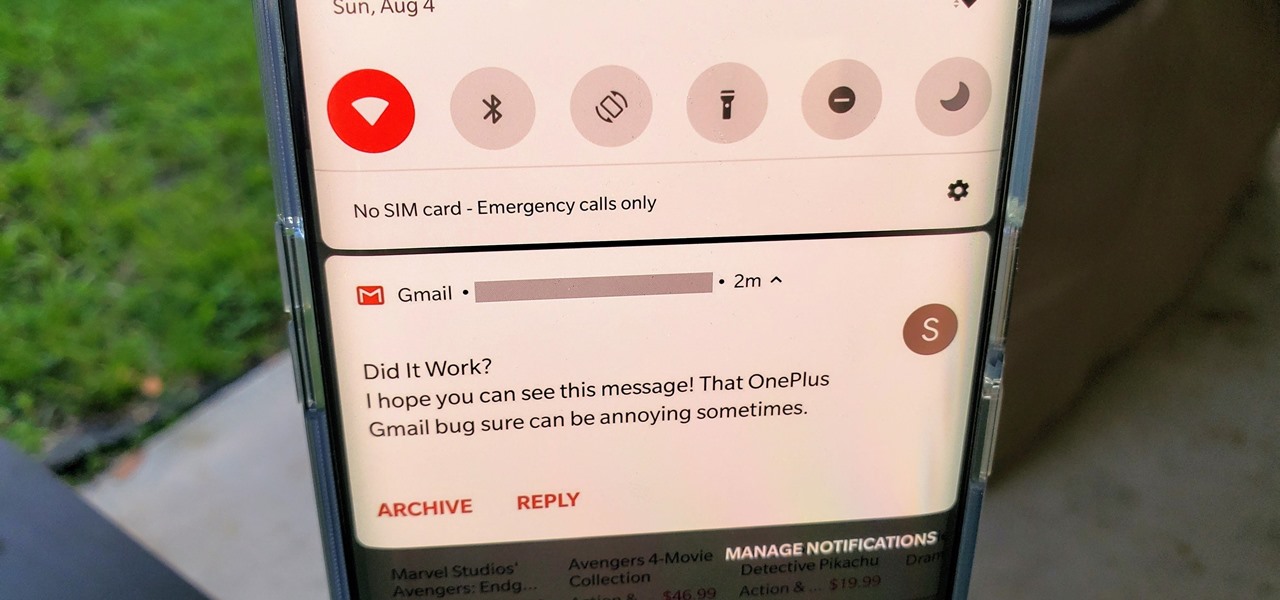
OxygenOS is often described as one of the best skins for Android on the market. It's fast, clean, and has a ton of useful features that appeal to just about everyone. However, it's also faced a significant issue for the longest time — overly aggressive battery optimizations that frequently kill background apps, including Gmail services.

With HoloLens 2 (hopefully) just around the corner, Microsoft has announced that it will no longer be providing any major operating system updates to the original HoloLens.

Fireworks are the best part about the Fourth of July and other celebrations, but they can easily cause accidental injuries. It's both safer and more fun to set them off remotely, so we'll hack some standard fireworks with nichrome wire, a relay, and an Arduino to ignite remotely over Wi-Fi using any smartphone or computer.

Metadata contained in images and other files can give away a lot more information than the average user might think. By tricking a target into sending a photo containing GPS coordinates and additional information, a hacker can learn where a mark lives or works simply by extracting the Exif data hidden inside the image file.

A hacker with privileged access to a Windows 10 computer can configure it to act as a web proxy, which allows the attacker to target devices and services on the network through the compromised computer. The probes and attacks appear to originate from the Windows 10 computer, making it difficult to detect the attacker's actual location.

While North has yet to add third-party app support to its Focals smartglasses, the company has been diligent as of late in its efforts to add more functionality to the bare-bones AR device.

Much of the excitement around the HoloLens 2 has moved on to many wondering when we'll finally be able to get our hands on what is now the best augmented reality device on the market.

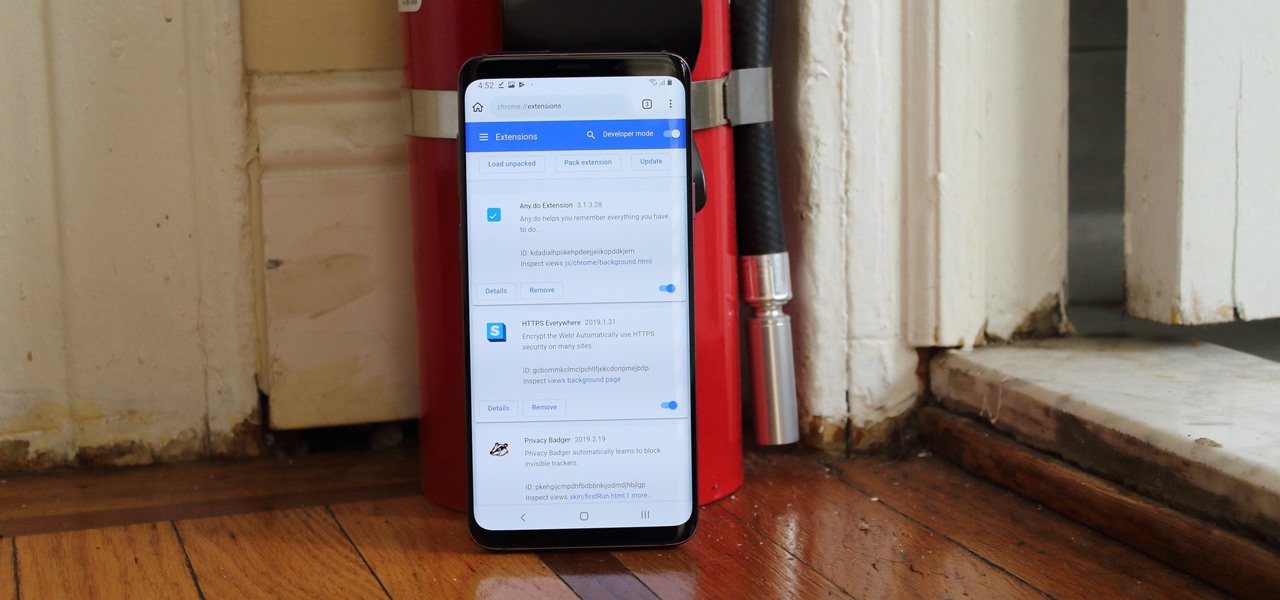
For years, there has been a disconnect between the Chrome app on your smartphone and the Chrome browser on your computer. The latter was a powerfully fast browser which could be enhanced with extensions to add new features and functionality, while the former was just a fast browser. Well, that all changes now.

Spring is here across the US, but, through the lens of Snapchat and augmented reality, winter is coming to New York.

Many of our online accounts now come with an added two-factor authentication (2FA) functionality to help keep our data safe. This essentially means no one would be able to access the account until a specific set of requirements were met. It could be a combination of a password with a security key or even a passcode with some form of biometrics, like a fingerprint or face scan.

The great thing about augmented reality is that so much is possible using the emerging tools and software, your only real limit is your imagination — that includes making real versions of imagined products.

While a release date for Harry Potter: Wizards Unite has not yet materialized, co-developers Niantic and WB Games have finally released gameplay footage and an in-depth game description to whet the appetites of eager Harry Potter fans.