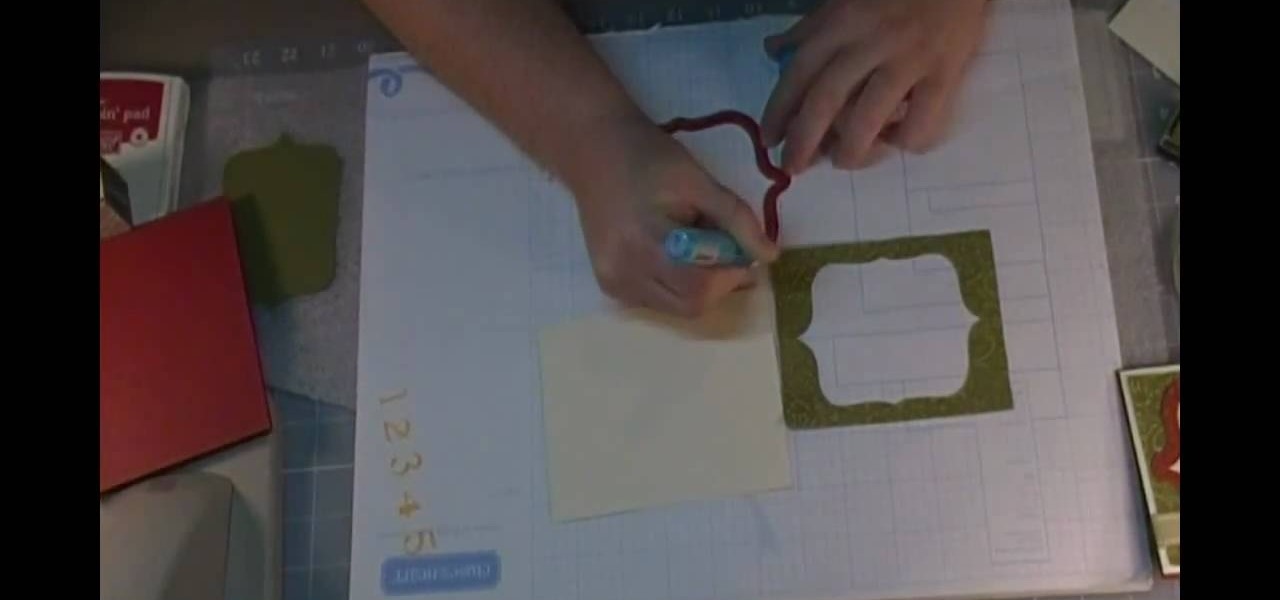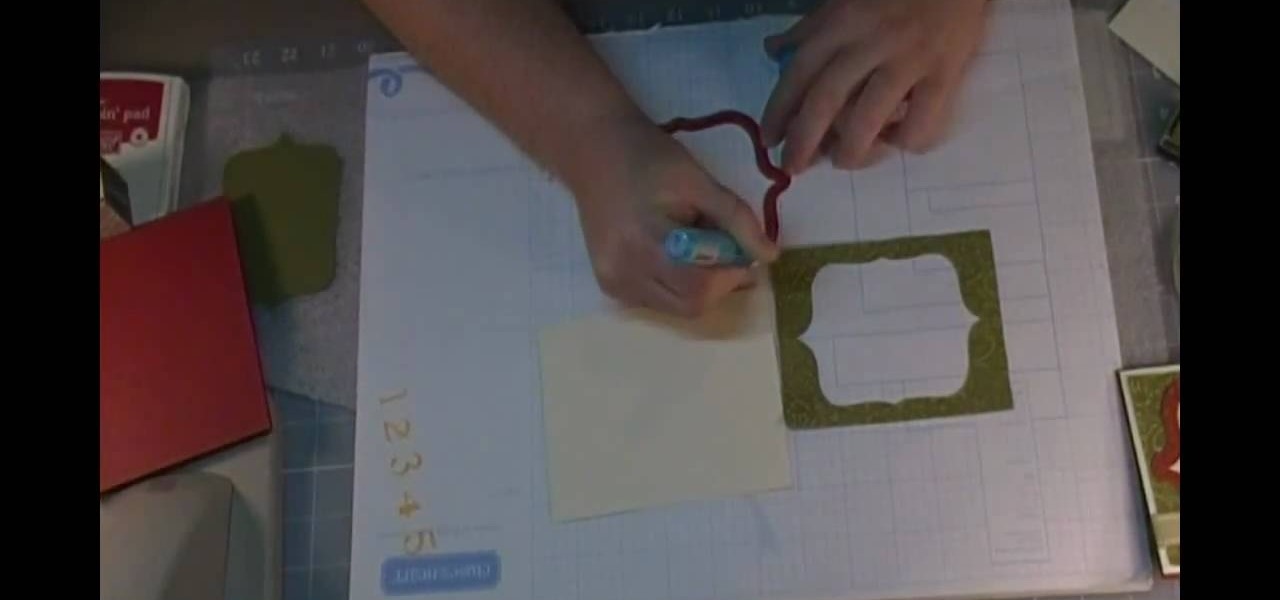
In this tutorial, we learn how to create a simple Christmas card using Cricut. First, you will need to take your card stock and fold it in half to create your basic card, pushing hard on the crease. After this, place a green holiday print on top of the front of the card and adhere it down. Next, cut out a bell shape outline, then cut out a piece of white paper in the same shape. Apply the white paper down first, then place the bell frame over the top of it. Push down a stamp sentiment on the ...

In this video, we learn how to make a Tyler Oakley inspired rag doll. You will need: an old t-shirt, a needle, felt, googly eyes, pen/pencil, paper, yarn, thread, and scissors. Start out by drawing the body of the doll out on the piece of paper, then cut it out. Now, trace the body shape onto the t-shirt and cut out two of these shapes. Now, take a needle and thread, and sew the two pieces of fabric together, leaving a small opening. Next, fill up the doll and then sew it back together. Now, ...

In order to chop an onion without crying, you will need the following: a spoon, a cutting board, and an extremely sharp knife.

In this video, Bill Dewey will show you the best way to shuck an oyster. You should have a knife and a glove so you will not cut yourself. Place the oyster on your glove hand. Keep the pointed side towards you. Take the knife and place it into the hinge. Twist the knife until you hear the hinge pop. Keep the knife against the top shell and scrape against the top towards the muscle. Now, open it up and cut the oyster from the bottom shell. Keep the liquor from moving off the shell. Now the oys...

To truss a chicken without using any strings, wires or skewers, hold the chicken up by the wings and let all the fluids drain out into a bowl or sink or any container. Next, use a knive or a sharp object and cut open a slit at the fat flaps just outside the bottom cavity. The slit should be about the size of a dime, and make a cut on the other flap as well. Push the leg through the slit on the opposite side, and then push the other leg to the other slit as well. The legs are now trussed. Tuck...

Wilton Cake Decorating demonstrates how to make and decorate a heart fireworks tiered cake. Roll out the pliable edible cake clay so that it is about 1/4 of an inch thick. Cut out heart shapes with cookie cutters. Let them dry for a few hours. Attach the hard hearts to wire with an icing adhesive. Create a bouquet out of the candy flowers by crooking the end of the wires and sealing the bases with floral tape. Create three-inch panels for the six-inch cake out of the cake clay. Cut out heart ...

This video illustrate us how to preform a simple interrupted suture in surgery. Here are the following steps:

This video shows you a mind-reading card trick. This particular trick requires 8 cards: 4 kings and 4 queens. First, the subject is asked to memorize one of the 8 cards as they are laid out before the subject, face-side up. The cards are picked up and sorted in various ways and the subject is asked a series of questions. The questions are always asking whether the card the subject memorized is in a certain group that the trick performer presents. The card in question always is in the group th...

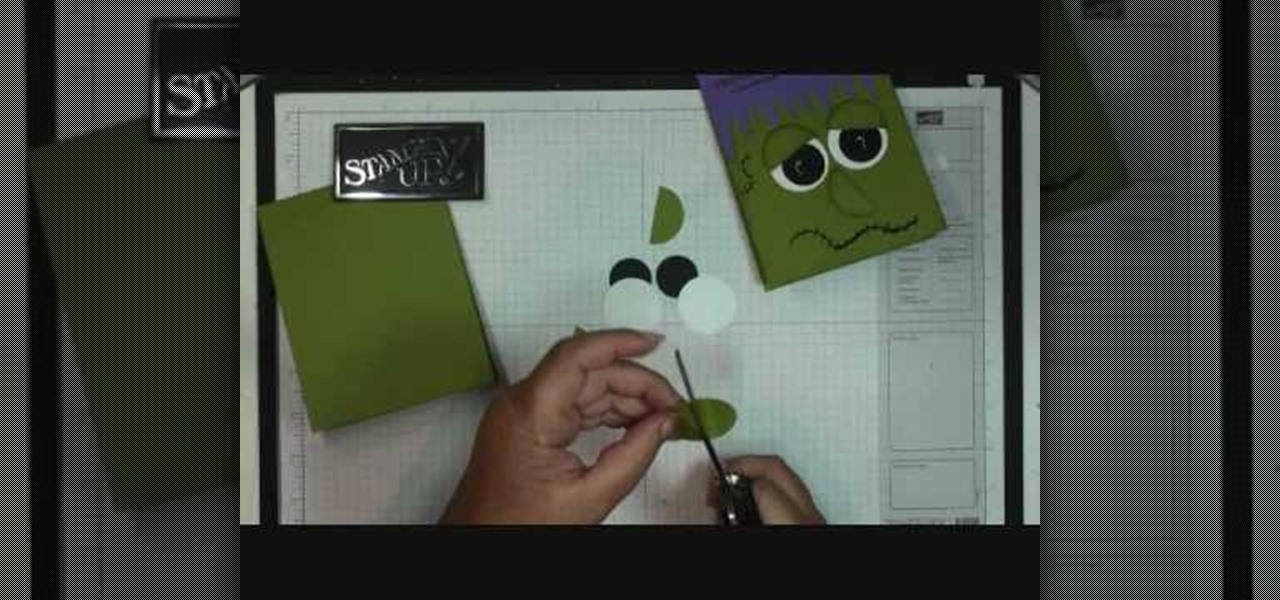
In this video tutorial, viewers will learn how to make a Frankie card. This video provides all the materials required to make the card. The materials required include: old olive card stock that is cut at 4 1/2" x 11", lovely lilac card stock that is cut at 2 1/2" x 5 1/2", stylus tool, Smarty Pants stamp set, 1" circle punch with 2 black card stocks, 1 3/8" circle punch on whisper white and old olive card stock, glue and a black market pen. This video will benefit those viewers who enjoy art,...

This video describes how to get a Kate Moss look with your bangs brought to you by stylist James Brown. Start with dry hair so that you can understand exactly where the bangs will be after cut as they can move up when they dry otherwise. Using a comb to pull the bangs down slightly and figuring where to put them just at the eyebrows you cut and move the hair back and forth along the brow to make sure it is staying in line with where you want it to end up. Continue until the hair is uniform ac...

Learn how to make your own homemade cleaning wipes and save money with this video tutorial. You will need a roll of paper, 2-3 cups of you favorite cleaner, and a storage container with a lid, a cutting board, and a knife. Cut the paper towel role in half using only one half now. Put the half paper towel roll in the container and soak with the cleaner. Remove the cardboard from the center of the roll and the cleaning wipes will be pulled out from the center of the roll.

You can scare the hell out of your friends with the neat trick, or you can use it in your next horror-filled independent movie, to scare the hell out of your viewers. Watch this prank video tutorial to learn how to embed floss into your neck.

Contrary to some screenwriting gurus, voice-over can be a handy narrative device. By speaking directly to the audience, rather than dramatizing, voice-over cuts through the running time. It can also cut down on resources. Just don't overdo it. Over-baked voice-overs sidestep drama, and leave little to interpretation. Imagine if everything were explained to you secondhand, rather than witnessing it yourself.

EternalBlue was a devastating exploit that targeted Microsoft's implementation of the SMB protocol. Metasploit contains a useful module that will automatically exploit a target, as long as it's vulnerable. But what if we wanted to exploit this vulnerability without Metasploit holding our hand? It can be done using a Python file to exploit EternalBlue manually.

After receiving many requests for the feature, Signal introduced read receipts last year to its mobile apps. However, some users don't like the idea other people knowing when they've read messages. Luckily, Signal lets you disable this feature and reclaim a little privacy.

Many guides on Null Byte require using the Secure Shell (SSH) to connect to a remote server. Unfortunately for beginners, learning to use SSH can become a confusing mix of third-party programs and native OS support. For Chrome OS users, using SSH is even more difficult. We'll fix this by using the Chrome Secure Shell to establish an SSH connection from any device that can run a Chrome browser.

The pictures we upload online are something we tend to think of as self-expression, but these very images can carry code to steal our passwords and data. Profile pictures, avatars, and image galleries are used all over the internet. While all images carry digital picture data — and many also carry metadata regarding camera or photo edits — it's far less expected that an image might actually be hiding malicious code.

Reddit user Mr. Squishy recreated the entire Game Boy Pokémon Red Version game in Vanilla Minecraft, i.e., a Minecraft server without gameplay modifications. Instead of using mods, he used 357,000 commands blocks—blocks that execute commands in the popular sandbox game. How long did it take him? Almost two years.

The Stagefright exploit, which allowed for malicious code to be embedded in files on your device, is now very real in the form of Metaphor. Developed by software research company NorthBit, Metaphor is their implementation of exploits to the Stagefright library, and when executed, can access and control data on your device.

Alright, this will be my first tutorial in C. Note that this guide is written for Linux.

Valentine's Day is right around the corner... which is the perfect excuse to ignite your inner cupid and bake a heart-shaped cake. If you have a heart-shaped cake or springform pan, you're all set. If not, don't worry—you don't need one! With a little ingenuity, you'll have a beautiful heart cake using the pans you already own.

Living on a budget often means compromising what you want for what you need—or at least, for what's affordable. But that doesn't necessarily mean you have to compromise on flavor, especially if you know the right tips and tricks to make something spectacular out of the ordinary.

Welcome back, my hacker novitiates! In the previous two posts in this series, we looked at the basics of buffer overflows. In this post, we will look at one technique for finding buffer overflows. We will try to send random, oversized, and invalid data at a variable to see whether we can make it crash or overflow. This process is known as fuzzing. It is often the first step to developing an exploit, as we need to find some variable that is susceptible to overflowing.

When browsing the web, you may not be quite as anonymous as you think, especially if you are using public WiFi. The easiest way to stay as anonymous and safe as you are going to get, is to use a VPN (there are a number of great free ones). In this tutorial, we will show you how to set up a VPN on Android, and how this protects you.

Knowing how to cut and slice raw meat is a skill all omnivorous cooks need in their arsenal. However, raw meat's limp and gelatinous character can be challenging to work with, especially when you're trying to slice it into symmetrical, attractive sections for a stir-fry or a stew.

Have you ever been called a "noob" or "eZ" after some person kills you? have you ever said "you hack" or "you suck" after getting your butt kicked by another player? this wont ever have to happen again. It is actually possible to be very good at PvP in Minecraft, and you can also be good at it. Now, it is your turn to win in every battle you fight in Minecraft PvP.

This time it's serious. Really. The largest web security vulnerability of all time went public on Monday, April 7th, 2014, resulting in widespread panic throughout the Internet as system administrators scrambled to secure their websites from the OpenSSL bug known as Heartbleed.

The new HTC One (M8) is a large phone, no doubt about it. Still, with those BoomSound speakers, 5-inch display, and 2600mAh battery, it's a wonder they managed to cram everything in that gorgeous, unibody metal shell. By that logic, it makes sense that the M8 makes the switch from a micro-SIM card to nano-SIM to save as much space as possible.

A lot of fruits start to turn colors once they've been cut due to an enzyme called polyphenol oxidase that turns the fruit colors when it's exposed to oxygen. You can prevent this reaction in apples with a honey-water bath, but what about avocados?

For a photo- and video-sharing app based around privacy, Snapchat sure has a lot of security holes floating around. At one time, you were able to take screenshots of Snapchats in iOS 7 without the sender knowing, which is something that you can still do on rooted Android devices.

This was my little cooking project for the holidays, I hope you like it! For this recipe you will need:

Bird's Feather Nail Art Tutorial For Beginners. Video: .

A lot of people hate chopping onions, and understandably so. Their shape and layers make them difficult to handle if you don't have much practice, and even if you know exactly what you're doing, it's a task that usually ends in tears.

Duct tape is the king of all household items. You can use duct tape for practically anything, like this sweet wallet. But duct tape isn't the only crafty tape out there; masking tape holds its own, too.

Everyone loves using their cell phones for everything except actually making phone calls. Whether it's watching streaming video, listening to music or playing video games, it would seem that calling people is almost an afterthought to cell manufacturers in this day and age.

File Transfer Protocol, or FTP, is a network protocol made for transferring files in a client and host fashion over a Transmission Control Protocol (TCP) network, such as the internet. FTP is integrated into most browsers, and you have probably used it before. It is a common way to host files and transfer them easily. To access an FTP, a login is required, unless the server is configured to use anonymous logins (like the Arch Linux mirrors).

Installing a T Mold Transition Between Laminate and Ceramic Tile There are several different types of laminate transitions that you may need when installing laminate flooring. Each one is used specifically for where the laminate flooring ends, such as where the laminate stops at ceramic tile. Other transitions are used where the laminate ends at carpet, vinyl flooring, a threshold or a step down such as a sunken living room or stairs.

In this tutorial, we learn how to cut crown molding perfectly for your home. First, you will need to determine what spring angle your crown molding is. It comes in 38 degrees, 45 degrees, and 52 degrees. If you buy the wrong kind, it will not match your crown molding and will look odd. Once you have figured out what you need, you will need to cut the molding on the side that is on the back side of the bottom. You will also need to drop your block next to it to get it cut at the right angle. W...

In this tutorial, we learn how to make paper rose with construction paper. First, take a piece of pink paper and cut a thin strip out of it. Next, take that strip and fold it in half twice. Now, cut the paper in half so you have several strips of paper. Now, fold in the strips to make them look like petals. Next, cut two thin strips out of a green piece of paper and craft them into the shape of a stem. Then, cut thin strips out of the green and shape them into leaves. After this, combine the ...

In this video, we learn how to carve a whole chicken. Start off by removing the wings from the chicken with a sharp knife. Go around the bones and let them guide you where to go. Next, remove the legs of the chicken, cutting again with a sharp knife. When finished, lay your chicken flat down and find where the breasts are. Cut around the breast bone to find the best spot to cut off the breasts. After this, cut the chicken breast into strips and set aside. Now that your chicken is finished, di...