
News: Snap CFO Resigns After Just Seven Months on the Job
In the business world, it's sometimes said that "where there's smoke, there's fire." At Snapchat parent company Snap, Inc., it appears the equivalent of smoke is executive turnover.


In the business world, it's sometimes said that "where there's smoke, there's fire." At Snapchat parent company Snap, Inc., it appears the equivalent of smoke is executive turnover.
In the realm of internet security, it's becoming clear that augmented reality is not immune to the increasing wave data breaches plaguing users.

Compulsive gambling is a recognized addiction, just like alcoholism or chemical dependency. Follow these steps to see if you might fit the profile. Recognize the signs of compulsive gambling with this guide from Howcast.

Do you own a small business, but find yourself unable to understand the intricacies of your financial statements? You are not alone. This video features a small business coach explaining some of the intricacies of financial statements. The tips provided here should help you better understand your financial statements and use the information gleaned therein to improve the profitability of your business.

The Cloud Security Alliance (CSA), a leading IT trade association, has published its first report on risks and recommendations for connected-vehicle security, ahead of when driverless cars are about to see volume production in the near future.
In case of a natural disaster, computer networks are often disabled, rendering the record keeping at most institutions useless. It's important that you make a financial first aid kit to ensure that you are able to get by and keep track of your personal information after a hurricane or fire. This video will show you what you should put in your financial first aid kit, which you should go make right now.
When you decide its time to retire, you will most likely need to cash in your Social Security benefits. In this official two part tutorial, presented by the American Social Secuity Administration, learn exactly how to use their website and apply online. Applying online is very easy, and takes a lot less time than applying in person. By applying online for social security, you will bypass all of the long lines and waiting that usually happens in one of the offices. Plus, you won't ever have to...

Malware attacks on mobile phones are reaching an all-time high and it looks like companies like Samsung are doing all that they can to prevent any unwanted hackers from accessing its sensitive user data.

Although John Chen of BlackBerry still sees Qualcomm as a partner, the chip maker and telecommunications company has just been given a preliminary order to pay BlackBerry $814,868,350 in royalty overpayments.

Airport security lines are one of the biggest hassles involved in air travel. Navigating them quickly and successfully can be the difference between making your flight and not. This video offers some tips for how to get through security quickly, including buying airport-security-friendly luggage and packing said luggage in an easy-to-inspect way. Also, don't wrap any gift, as security may want to unwrap them!

Home security is as important as having a job. You have to protect your family and your valuables. If you can't afford a high tech security system, then maybe a fake security camera will do the trick. This security camera dud is also a cheap alternative for a film prop. Watch this video tutorial to learn how to build a fake cardboard security camera.

Airport security keeps getting stricter and more time-consuming. Shorten your time in the security line with these tips. Watch this video travel tutorial and learn how to get through airport security.

Money skills are critical for any adult, which means the best time to teach someone financial responsibility is during the teenage years. These parenting tips are meant to teach your child about income and costs. Use allowance as a tool to show your teenager how to manage their own money.

Two-factor authentication (2FA) is a great way to add another layer of security to sensitive third-party apps and websites like Venmo. However, before iOS 12, to log into a particular 2FA-secured app or site on your iPhone, you'd have to memorize or copy the SMS code from Messages, then jump back in a timely manner to log in. Apple's latest iOS version streamlines this process.

Welcome back, my hacker novitiates!
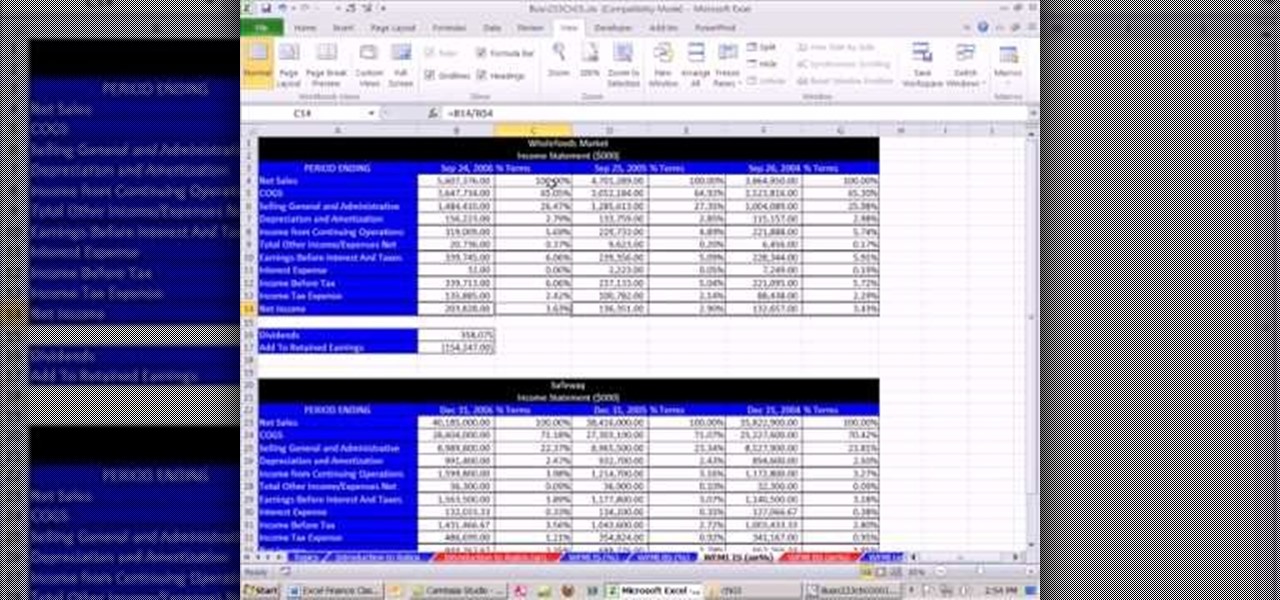
As you might guess, one of the domains in which Microsoft Excel really excels is finance math. Brush up on the stuff for your next or current job with this how-to. In this tutorial from everyone's favorite digital spreadsheet guru, YouTube's ExcelIsFun, the 15th installment in his "Excel Finance Class" series of free video lessons, you'll learn how to generate a common-sized financial statement within Microsoft Excel.

Windows Vista is jam-packed full of new security features, which could be a good thing, but they're just so obtrusive it's not really worth it. If you want to learn how to stop all of the annoying security alerts, this video will walk you through the process of disabling these security notifications in Windows Vista.

Installing security lights outside of your home can make for a great addition, but they also create new problems with regards to maintenance and cleaning. Having lights outside exposes them to all of the elements that mother nature can throw at them. This video will show not only how to install security lights, it will also show the proper measures to take so they will keep working with minimal maintenance and care.
This is a lock picking video which demonstrates how to pick a tumbler lock. Of course the only way to really open locks is to practice. But this is the basic info to picking locks. This lock picking tutorial also covers security pins and clear instructional animations to demonstrate. Learn how to pick a lock and use this video to understand lockpicking, security pins, skill tension, and bump keys. See all about how to pick a tumble lock & understand lock security pins.
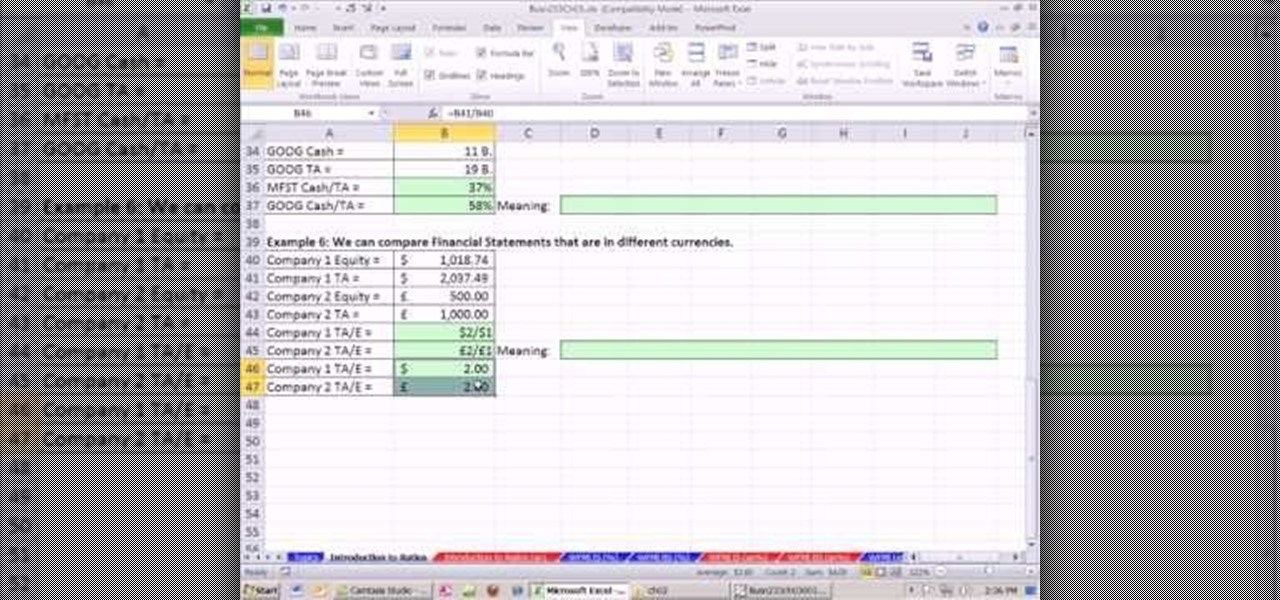
As you might guess, one of the domains in which Microsoft Excel really excels is finance math. Brush up on the stuff for your next or current job with this how-to. In this tutorial from everyone's favorite digital spreadsheet guru, YouTube's ExcelIsFun, the 17th installment in his "Excel Finance Class" series of free video lessons, you'll learn how to perform simple financial ratio analysis.

EDGAR is a massive database of financial documents and filings maintained by the SEC. If you want to use EDGAR to research financial institutions, it's pretty easy to do with an FTP client. Watch this video to learn how you can download and use FTP software to access EDGAR.

Lock picking can be difficult with some security features. This instructional video shows you what happens when you encounter them and what to do. Break into a lock when you've forgotten your keys, but please don't sneak in anywhere you don't belong. Watch this video lock-picking tutorial and learn how to detect security pins.

With the new screening protocols and their full body x-ray scanners, the TSA is taking constant criticism from unhappy travelers. Between the nude images the scanner produces and the awkward pat downs, air travel will never be the same. That's why it's important to make sure you're prepared for your flight and the TSA security checkpoints.

Flying under the radar during Magic Leap's big week at the Game Developers Conference, the company settled a potentially ugly lawsuit with a former employee.
This week in Market Reality, we see two companies capitalizing on technologies that contribute to augmented reality platforms. In addition, industry mainstays Vuzix and DAQRI have business news of their own to report.

In this clip, you'll learn how to quickly set a security pattern on an LG Droid Ally Google Android smartphone. For more information, including a complete demonstration and detailed, step-by-step instructions, and to get started setting up your own security secreen, watch this helpful video guide.
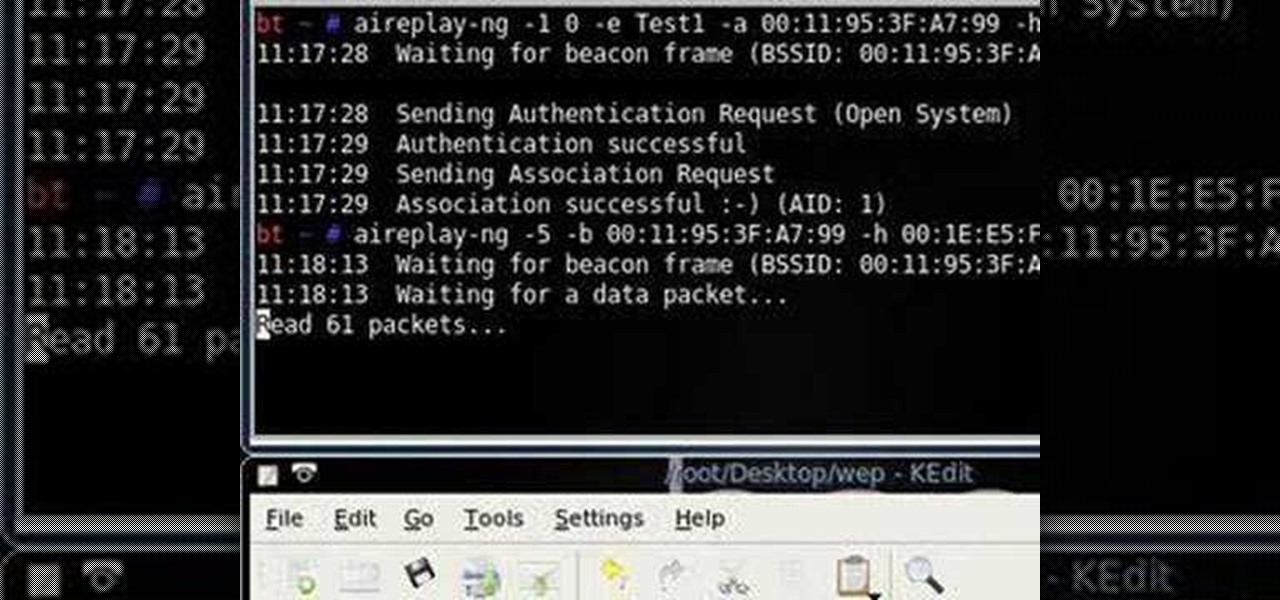
Want to test the security of your WEP WiFi wireless network? In this clip, you'll learn how to use the Backtrack Linux distro and the Aircrack-ng WiFi security app to crack a WEP key. The process is simple. For more information, including step-by-step instructions, and to get started testing the security of your own WiFi networks, watch this hacker's how-to.

Learn how to configure the features in F5's FirePass v7 SSL VPN Endpoint Security. Peter Silva shows some of the new Endpoint Security features in the recent FirePass v7 release. Watch how to create policies, enforce host checks and other protective measures for your Remote Access deployments. For more information, and to get started configuring your own installation of FirePass v7, take a look.

If you live in a hurricane prone area, it is a good idea to protect your windows with security film. This video will teach you how to install hurricane security window film on your own and protect your home and assets.

Not sure what to do when you get a security warning about a macro? What are macro security settings, the Trust Center, and Trusted Locations anyway? Watch this instructional video to learn how to enable macros and make informed security decisions that can help you keep your computer safer while you work in Microsoft Office Excel, Outlook, Word, Publisher, PowerPoint, and Visio 2007.

Ever wanted to learn how to pick a lock? Well, there's no better time than now to start learning the craft of so many locksmiths out there... lock picking. Just watch this video tutorial to see how to bypass security wafers when lock picking.

A basic tutorial from InfinityExists.com on using Backtrack - the Linux-based security software package. This tutorial covers: Where to get Backtrack 2, How to burn an .ISO file, How to boot Backtrack 2, How to login, and start the GUI interface. It also illustrates basic Linux commands, and how to set up your Network Interfaces.

It's easy to have your password stolen. Important people like executives, government workers, journalists, and activists face sophisticated phishing attacks to compromise their online accounts, often targeting Google account credentials. To reduce this risk, Google created the Advanced Protection Program, which uses U2F security keys to control account access and make stolen passwords worthless.
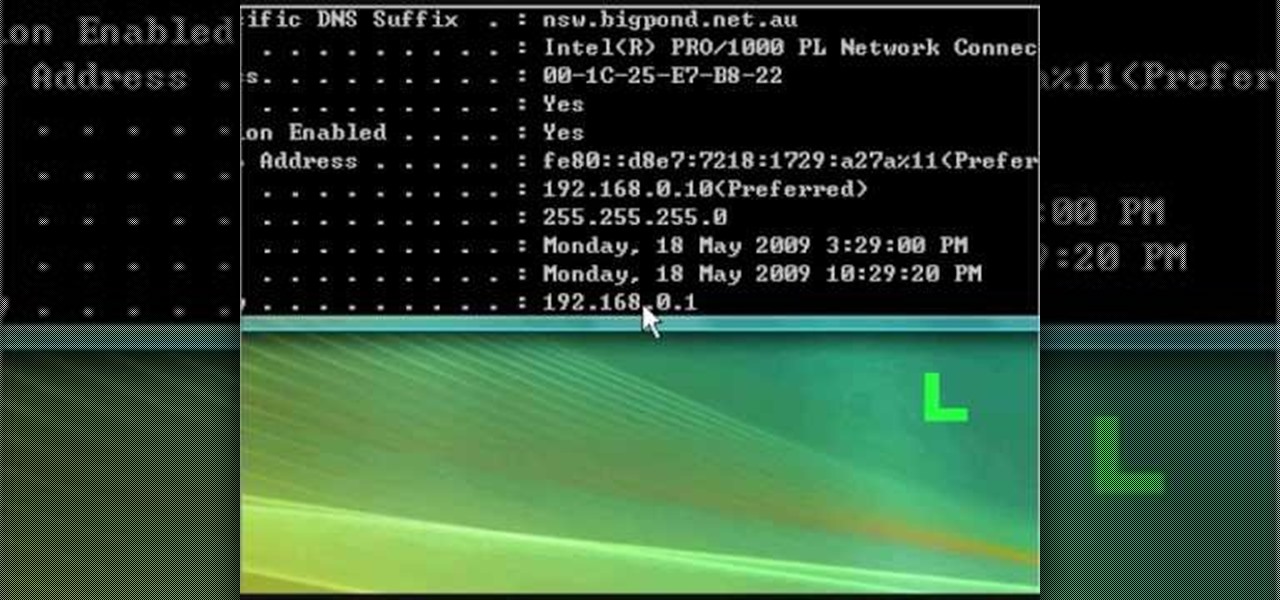
In this tutorial, we learn how to fix security mode for nds Wi-Fi. First, open the command prompt in Windows. Next, type in "ipconfig/all" in the black window that appears. After this, copy your default IP the screen just gave you, then type it into your address bar online. After this, you will be able to log into your security account and make default changes you prefer. Change different station accesses and any other security preferences you want to change. After this, you can change your p...

Having security setting on your web browser is a pretty important tool. It keeps you safe from potential hackers and makes sure you don't visit unsafe sites that could lead to a virus. But sometimes the security settings on a web browser can be a pain and the best choice would be to turn it off. So in this tutorial, you will learn how to easily change the security settings to INternet Explorer 8. So sit back and enjoy!

Cyber Security is a horrible computer virus. It mimics a virus protection program and invades your system, making it nearly impossible to remove. In this tutorial, learn how to remove this annoying trojan horse from your PC and save your computer.

Ever wanted to learn how to pick a lock? Well, there's no better time than now to start learning the craft of so many locksmiths out there... lock picking. Just watch this video tutorial to see how to pick a Brink's high security lock.

Have you ever been the victim of theft? It sucks. Why would these lazy scumbags rather steal from us than work hard like everybody else?

Video tutorial showing how to make your own solar-powered wireless security camera using an off-the-shelf solar panel and any wireless webcam. See creator site for more detailed graphics.
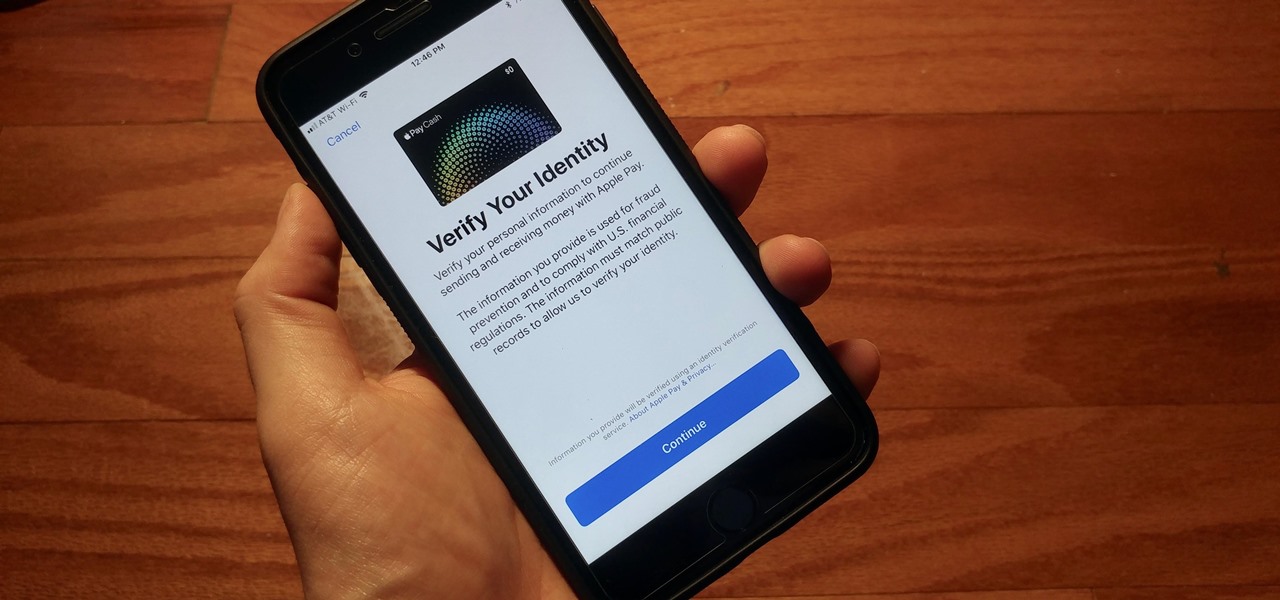
With iOS 11.2's introduction of Apple Pay Cash, you can send and receive money to others directly through iMessage, using the convenience and security Apple Pay is known for. However, if you want to make sure your efforts go uninterrupted, you'll want to make sure you verify your identity with Apple.