Dropbox continues to make headlines with their recent programming blunder which left the accounts of its 25 million customers wide open during a four-hour time span. During the duration, anyone in the world could access any Dropbox profile by typing in any password. And seeing as this wasn't the first security failure, everyone, including the most loyal users are considering dropping the Dropbox.

No more Internet Explorer 9 Beta. Not today. Now you can explore the web with Microsoft's new Internet Explorer 9 Release Candidate (RC). It wasn't supposed to be released until tomorrow, February 10th, but it's been leaked a little early, WinRumors reports.
The Department of Homeland Security has been forced to release a list of keywords and phrases it uses to monitor social networking sites and online media for signs of terrorist or other threats against the U.S.
The top-secret US National Security Agency is not required to reveal any deal it may have with Google to help protect against cyber attacks, an appeals court ruled Friday.

To decipher my password, you need to know my mother's maiden name, where I was born, and what I had for breakfast on August 12th, 1996 (trick question, I was in a food coma).
Stanford is soon supposed to offer free classes in Cryptology, Computer Security and a slew of other intriguing topics! Check out the site to sign up and learn more!

Cool world. Check it out and post your ideas to the forum.

Here is the Trailer for a new insane movie called 22nd of May 22nd of May Koen Mortier, Belgium World Premiere

Using Embird embroidery software, Rosanne shows us how to use the Basting Stitches control properly, for a perfect design. Rosanne will also show you the bast in a hoop technique for more security. Insert basting stitches in Embird.

Middle-aged man instructs how to mount a rack bolt onto a door to strengthen the security of the door. Great video using subtitles and clear demonstration of how to use a drill when mounting the rack bolt kit. Fit a rack bolt onto a door.
Fascinating, although admittedly highbrow, discussion on the history of cryptography from the BBC. If you are outside of the UK and don't know how to access BBC content you need to spend a bit more time browsing the Null-Byte forums ;-) http://www.bbc.co.uk/programmes/b06mtms8

Startup promises to catch 100% of network attacks - Techworld.com.

A vast number of studies ranging across time, continents, cultures, political systems, and religions show that when evaluating potential mates, women place significantly greater emphasis than men on material wealth, and that men tend to both display and exaggerate their financial status and prospects when around women.

A former decorated undercover FBI agent, Mike German, explains how the national security state, in league with local law enforcement, is secretly targeting Americans for political views and activities perceived as a threat to the political establishment. » Former FBI Agent: Surveillance State Trashing Constitutional Protections Alex Jones' Infowars: There's a war on for your mind!.

(CNSNews.com) – There have been 2,527 Department of Homeland Security (DHS) employees and co-conspirators convicted of corruption and other criminal misconduct since 2004, according to a federal auditor Federal Auditor: 2,527 DHS Employees and Co-Conspirators Convicted of Crimes | CNSNews.com.

While US Defense Secretary Leon Panetta attempted to convince top Israeli politicians and security officials not to launch a strike on Iran's nuclear facilities during his visit to Israel last week, his predecessor Donald Rumsfeld, seems more prepared for a possible attack. Rumsfeld: Israel needn't notify US about strike - Israel News, Ynetnews.

In preparing to use surveillance drones for protests and “public safety,” the Department of Homeland Security is following Russia’s lead, where Vladimir Putin has approved a massive expansion of the technology specifically for the purpose of monitoring demonstrators. » U.S. Follows Russia In Using Drones To Spy On Protesters.

The Department of Homeland Security has put out an urgent solicitation for hundreds of items of “riot gear,” in preparation for expected unrest at the upcoming Republican National Convention, Democratic National Convention and next year’s presidential inauguration. » DHS Puts Out Urgent Order For Riot Gear.

In a rare admission that has gone almost completely unreported, the Director of National Intelligence has admitted that the National Security Agency violated the US constitution and abused its power by spying on American citizens and monitoring their communications. » Feds Admit NSA Spying Violated 4th Amendment.

The National Security Agency is storing all electronic communications and analyzing them in real time, according to former NSA employee turned whistleblower William Binney, who warns that the federal agency has a Google-style capability to search all conversations for keywords. » Whistleblower: NSA Analyzing Conversations In Real Time.

The Obama administration has given the Department of Homeland Security powers to prioritize government communications over privately owned telephone and Internet systems in emergencies. DHS emergency power extended, including control of private telecom systems - Washington Times.

Now, that's some whittling. Awesome school-desk-art by Ben Turnbull. See how wood carver Bob Seguin makes a mini navy colt revolver out of basswood here.

This is Part II in the Lockdown: The InfoSecurity Guide To Securing Your Computer series. Before beginning, check out Part I. This article will cover using alternate software to increase your security and will provide you with some information about websites and programs that test a computer's security. It will also guide you to software you can install or follow so you know what programs need to be updated on the computer. Lastly, I will talk about some features that should be disabled when ...

In this video tutorial, viewers learn how to set and encrypt their Wi-Fi password using WPA in Apple Airport. Begin by opening the Airport Admin Utility application from the CD. Then locate your the name of your network and double-click it or press the Configure button at the bottom right of the screen. Now enter your password and click OK. The network should be opened now. Then click on the Airport tab and click on Wireless Security. In the pull-down menu, select WPA2 Personal. Then click on...
California grad student on no-fly list gets home after stranding An American student who discovered he was included on the government’s no-fly list and was barred from a U.S.-bound flight from Costa Rica was reunited with family and friends after he flew to Mexico and then walked across the U.S.-Mexico border Thursday evening.

Another week has passed on the online battlefield as the CISPA legislation continues to grind away at our freedom. Here at Null Byte, we try to keep our community informed and knowledgeable at the same time—and that means creating content for them to learn from.

Here's another delicious Byte. Ucha Gobejishvili, a Georgian Security Researcher under the handle of longrifle0x, discovered two cross site scripting (XSS) vulnerabilities on the official website of Forbes. He discovered the hole in two different locations on the site, and has already informed the website of the vulnerability.

Whether you really need to pinch pennies for a long road trip or are really at the end of your rope with your financial and living situation, desperate times call for desperate measures--and sometimes that involves living in your car for an extended period of time. It is certainly not easy, but with the right equipment and know-how, making your car your abode is certainly possible if you make the continuous effort to keep things clean, be smart about where you park your car and avoid arousing...

Minecraftian is a beautiful and lengthy machinima made using Minecraft; dubbed the 'first full feature Minecraft Film'. The movie has everything a great movie needs: strong editing, beautiful music, and Minecraft itself.

In Linux, all password hashes are normally stored using the MD5 hashing algorithm in the /etc/shadow file, but MD5 is algorithmically weak due to collision vulnerabilities. The new recommended standard are the higher level SHA-2 hashing algorithms, SHA256 or SHA512. As a friend pointed out to me, Ubuntu is currently the only distro implementing SHA-2 as the default. With SHA-2, your passwords take an unreasonably larger amount of time to calculate. This will greatly decrease how many password...

Hideo Kojima is one of the biggest names in Japanese game design. He's the man behind every Metal Gear game, each of which has been beautiful but divisive. He's an auteur, a rarity in AAA game design, managing business, design, and programming for Kojima Productions. Last week he made a rare public appearance at the USC School of Cinematic Arts, which contains the school's video game programs, and gave a 90-minute talk about his career, influences, and the specifics of his new Fox game design...

Social Profile Change the privacy settings on your social profile (Facebook, MySpace, Friendster, Twitter, etc.) so that the following information can't be found by a random person who you didn't accept you as a friend:

Dress up Johnny Knoxville as his old man counterpart. He then needs to strip down to his underwear at a MLB or soccer game and streak across the field. If possible he should really bring a walker and hold it out while he is scrambling from security. Most people wont know who he is, but it will be a huge hit with all of us fans who will recognize him immediately and be thrilled with the opportunity to see a prank in action without being able to interfere with the filming.

Half-hitches are great knots, but only when use in combination with other knots. By itself, a half-hitch is unsafe and unreliable, but when joined with other knots, can be quite the opposite. Tying two half hitch knots together is great for attaching a rope or line to any object. The half hitch and double half hitch are used throughout specialities, most notably as a boating knot, outdoor knot, and paddling knot.

Lifehacker posts an article on the art of cracking weak passwords, courtesy of Internet standards expert, CEO of web company iFusion Labs, and blogger John Pozadzides. Pozadzides certainly knows a thing or two about password logic. (Note: this information is not intended to hack into accounts, but rather to protect you from using weak passwords).

Are Twitter and Facebook in trouble with the advent of Google's brand new social networking tool, Google Buzz?

Check out our video walk-through of part one of the final boss encounter in Resident Evil 5! This includes lots of game spoilers.

The figure eight follow through boating knot is one of the strongest knots. (also can be used for paddling). It is generally rated at 70% - 75% of rope strength. Due to it's strength and the fact that it is easy to visually inspect, it is commonly used by climbers as their "tie-in knot" - the knot that connects the climber to the rope. It forms a secure non-slip loop at the end of a rope. For even greater security, finish the tag end with a backup knot such as one side of the double fisherman...

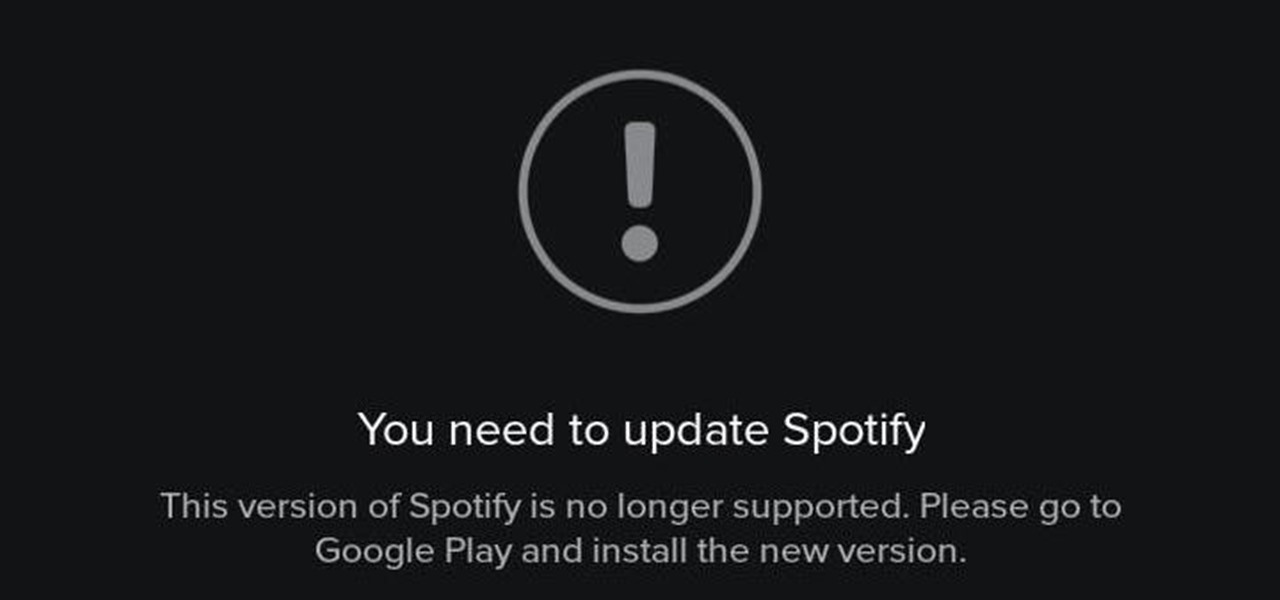
Adobe, eBay, and iCloud have been hacked...now add Spotify to that list. The company has stated that on May 27th, they became aware of "some unauthorized access to [their] systems and internal company data" but that "only one Spotify user's data has been accessed and this did not include any password, financial or payment information."