
How To: Cook mussels with Floyd Cooks of the BBC
Chef Keith Floyd presents an easy to follow step by step guide to cooking with mussels. Classic moules mariniere recipe video from BBC cookery show 'Floyd on Fish'.


Chef Keith Floyd presents an easy to follow step by step guide to cooking with mussels. Classic moules mariniere recipe video from BBC cookery show 'Floyd on Fish'.

Keith Floyd cooks a family-sized Sunday lunch of walnut-stuffed apples, artichokes, and cider-soaked roast chicken. Meanwhile, his Brittany guests cook a langoustine entree inspired by North French ingredients. Great recipe idea from classic BBC cookery show 'Floyd on Food'.

Chef Ken Hom shows how to cook Buddhist Casserole. Great clip from BBC show Ken Hom's Cookery. Learn how to make Chinese buddhist casserole.

Chef Ken Hom shows how to cook Sesame Prawn Toast. Great clip from BBC show Ken Hom's Cookery. Learn how to make Chinese sesame prawn toast.

Learn how to make a delicious tandoori tikka marinade with this video from BBC cookery show 'Indian Food Made Easy'.

Learn how to make traditional Indian naan bread with chef and food writer Anjum Anand in this great video from BBC cookery show 'Indian Food Made Easy'.

Welcome to the fragrant world of Cornish Indian food. Chef and food writer Anjum Anand shows a local Cornish couple the best way to cook mussels in a traditional Indian style. Great video from BBC food programme 'Indian Food Made Easy'.

Check out this DIY video tutorial from Curbly, the best place to share pictures of your home, find design ideas, and get expert home-improvement advice.

Despite being bombarded with so many things to do each day, we still somehow find ourselves in a mid-afternoon lull where there's nothing better to do than stare at the adventures of a piece of lint darting across our computer screen.

The Animal Crossing series has been a big hit for Nintendo, so in a bid to enhance the experience even more for users, the game is getting the augmented reality treatment.

One of my favorite perks of this job is the opportunity to try out all the big flagship phones each year. Whether it's rating their suitability for a particular use-case or just entering their specs into our comparison tool, we have to get our hands on all major phones released in the US. We pride ourselves on being fair in our reviews and roundups, but that doesn't mean we don't have preferences.

Windows 10 passwords stored as NTLM hashes can be dumped and exfiltrated to an attacker's system in seconds. The hashes can be very easily brute-forced and cracked to reveal the passwords in plaintext using a combination of tools, including Mimikatz, ProcDump, John the Ripper, and Hashcat.

You may not have thought of dorks as powerful, but with the right dorks, you can hack devices just by Googling the password to log in. Because Google is fantastic at indexing everything connected to the internet, it's possible to find files that are exposed accidentally and contain critical information for anyone to see.

Imagine a scenario where you're nowhere near your iPhone, but it's on loud, and you really need to silence it. An alarm may be blaring, notifications could be spitting out sounds left and right, and calls may be ringing. Things can get annoying real quick for whoever's around it. Plus, all that attention makes it easy for someone to find and possibly steal your iPhone. Luckily, you can quiet it down.

Smartphone videos get better and better each year. Seven or eight years ago, who would have thought iPhone and Android phones could support 4K video recording. Some phones can even shoot slow-motion at 960 fps. But no matter the resolution or frame rate, a phone's rolling shutter can make quick movements in front of the camera appear wobbly, distorted, or with artifacts.

The year in augmented reality 2019 started with the kind of doom and gloom that usually signals the end of something. Driven in large part by the story we broke in January about the fall of Meta, along with similar flameouts by ODG and Blippar, the virtual shrapnel of AR ventures that took a wrong turn has already marred the landscape of 2019.

Your iPhone just went missing, and now you're panicking. You need it for work, to get around, to contact your friends and family, and pretty much everything else in your life. So, what are the chances you might get it back? The odds may be stacked against you unless it's just under a couch cushion, but you can improve your chances of recovering your iPhone by taking certain steps.

So, you're on the way back from a restaurant and realize you left your iPhone there, but you're late for a meeting and can't go back yet. You may as well kiss that iPhone goodbye, right? Not yet, as long as the right person gets their hands on it first. But that potential do-gooder won't know to contact you, and that's where Find My iPhone's "Lost Mode" comes in handy.

Cross-site scripting can be one of the easiest vulnerabilities to discover, but to be successful with this type of attack, it is essential to learn how to get past filters. In the previous guide, we explored some ways to do this, such as abusing attributes and event handlers and tricking the application into accepting unusual characters. Now, let's take a look at more techniques used to defeat filters.

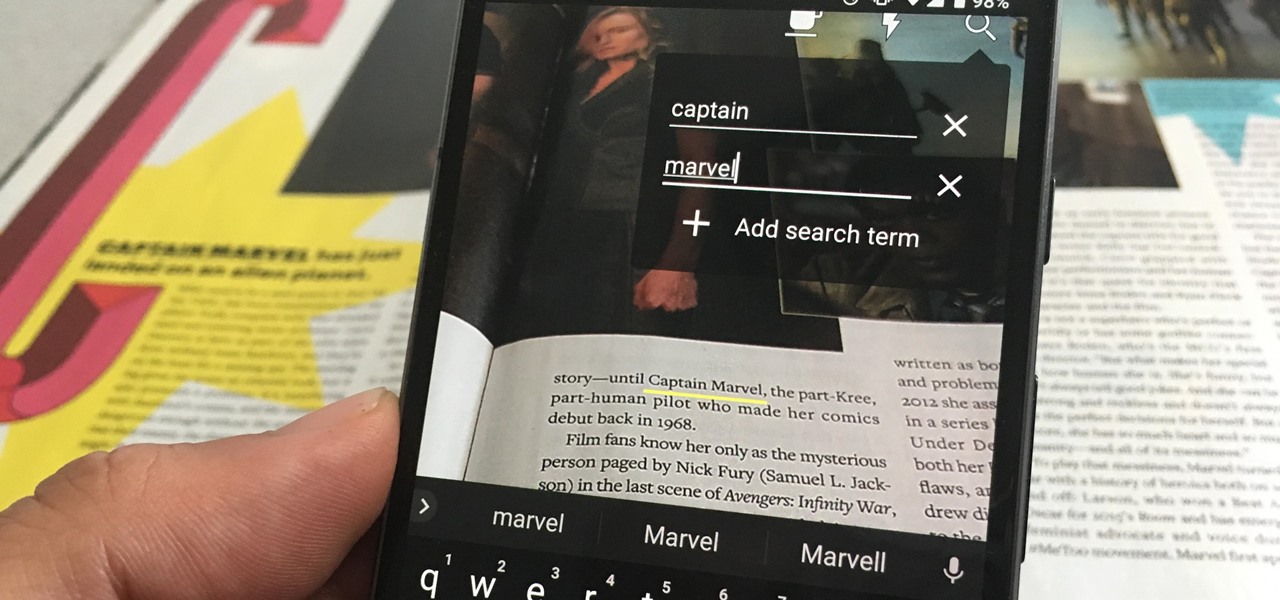
The idea of a perfect phone is a myth. There are lots of pros when it comes to OnePlus devices, but there are also a few things that could be better. And even if there were a phone without flaw, there are still things that you might want to customize for personal preference. That's why we set out to find the very best tweaks for OnePlus phones, and to make it easier for you to apply them.

Your iPhone comes packed with a long list of excellent text tones to choose from. Bamboo anyone? Of course, for some of us, stock sounds from 2013 don't cut it anymore. We want customizability, something that's found more on Android than iOS. However, you can add your very own text tones to your iPhone right now, so long as you have a sound file in mind and a computer running iTunes.
One of the neatest tricks available in Google Lens, an app that can identify and interpret real world information, is the ability to copy text from the app's camera view and paste it into a digital document.

Yesterday, I talked about what I think is the most immediately mainstream-friendly app on the Magic Leap One is (Screens), and now we'll touch upon the runner-up: Helio.

As Android bug bounty hunters and penetration testers, we need a properly configured environment to work in when testing exploits and looking for vulnerabilities. This could mean a virtual Android operating system or a dedicated network for capturing requests and performing man-in-the-middle attacks.

According to Google at their 2018 I/O conference, Google Assistant is now available on over 500 million devices. Now that the assistant is available on iPhones as well, Google has to give iOS users a reason to switch to its assistant over the built-in Siri. Today, Google has eight more reasons for users to do so.

If preorder delays are any indication, the iPhone X certainly has some buzz. But does the X have the quality to support that buzz in the long run? After all, a $1,000 (or more) iPhone feels more like an investment than a smartphone purchase. The question on any prospective buyer's mind should be, "Is this thing worth it?"

When it comes to finding lost things, the joke goes that it's always in the last place you look. With an assist from ARKit, Pixie can make your iPhone the first and last place you look for that missing item.

Going to music festivals is one of the best parts of the summer — Which is probably why thousands of people attend them. With numbers like that, trying to find and meet up with your friends can be difficult and intimidating. Thanks to Apple's ARKit, however, you'll soon be able to locate your friends in a crowd using an app.
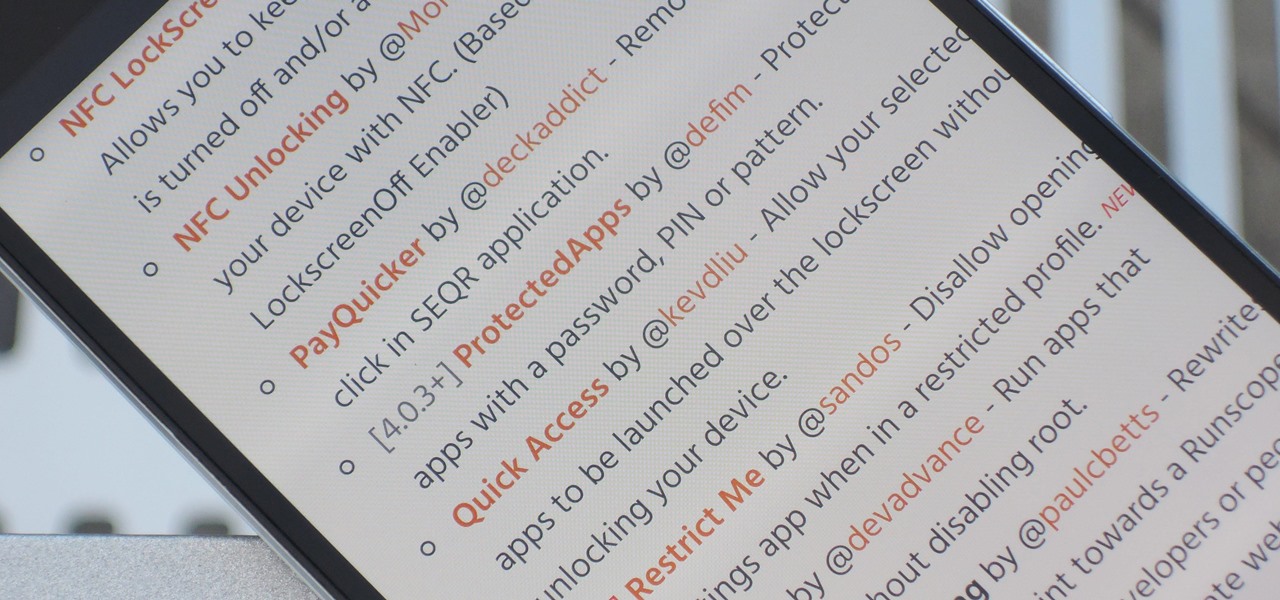
The Xposed Framework has an official repository for downloading modules which can be easily accessed by searching the Download section in your Xposed Installer app. But not every module is available on the Xposed repo — in fact, many unique and interesting modules are only hosted on third-party servers.
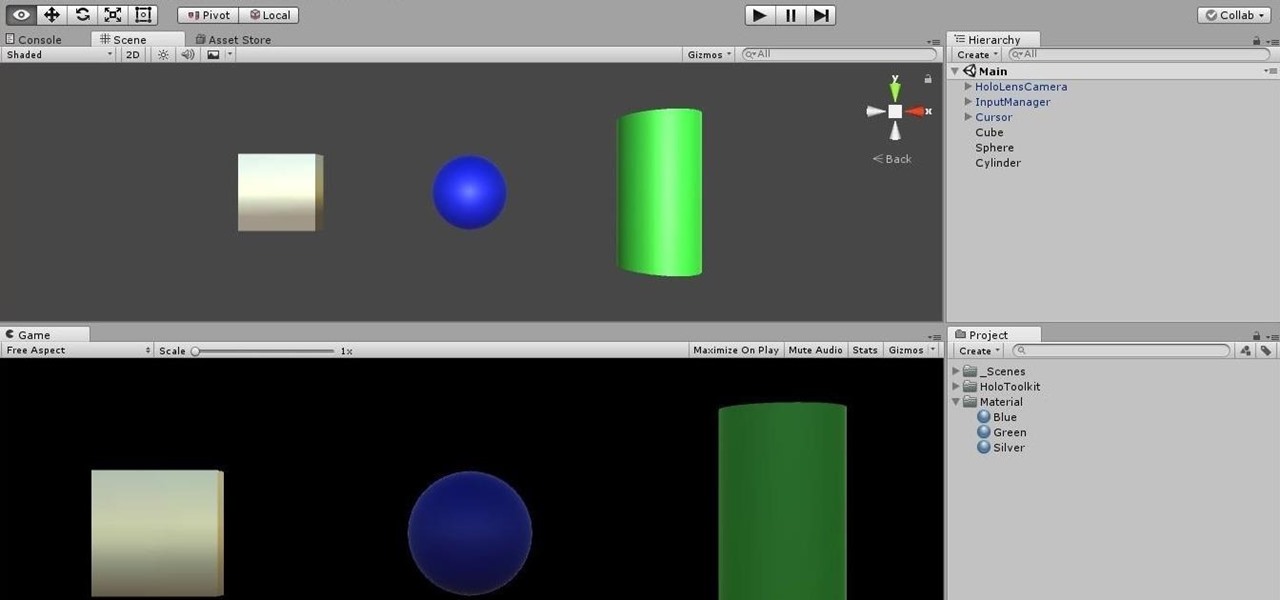
Being part of the wild frontier is amazing. It doesn't take much to blow minds of first time mixed reality users — merely placing a canned hologram in the room is enough. However, once that childlike wonder fades, we need to add more substance to create lasting impressions.
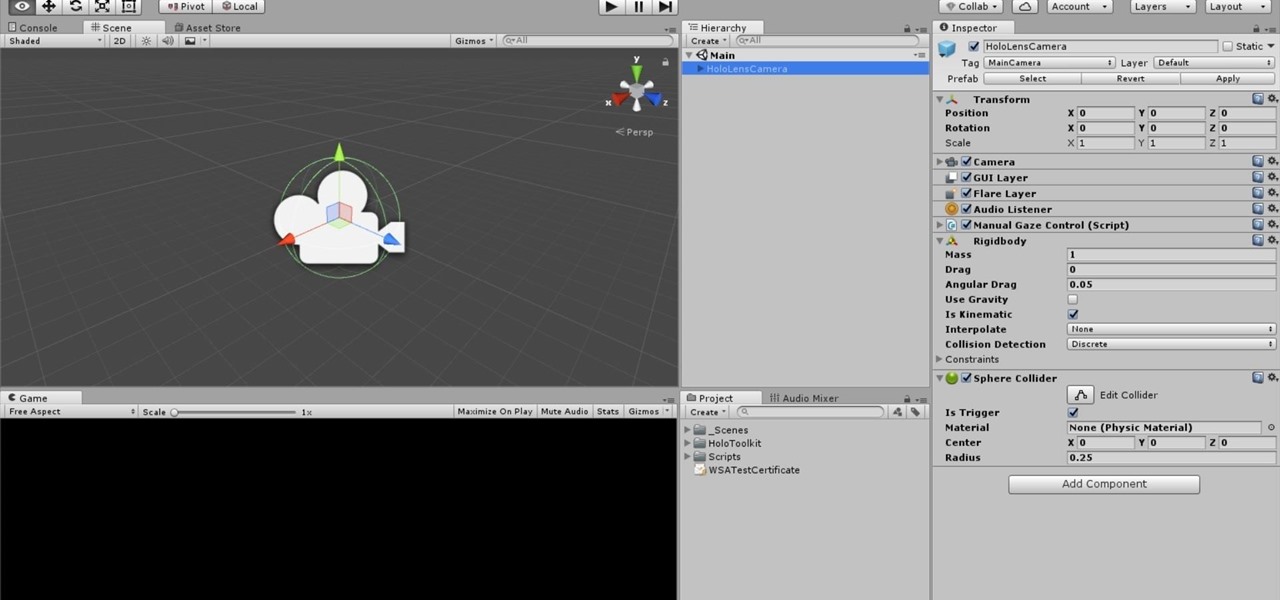
One of the truly beautiful things about the HoloLens is its completely untethered, the-world-is-your-oyster freedom. This, paired with the ability to view your real surroundings while wearing the device, allows for some incredibly interesting uses. One particular use is triggering events when a user enters a specific location in a physical space. Think of it as a futuristic automatic door.

It appears a privacy lawsuit that began five years ago is about to come to an end, and you might get some money out of it.

During our high school years, one of us (hint: her name starts with a B) worked at Cold Stone Creamery. She loved working there, and from this love emerged a fascination with adding creative ingredients to plain ol' vanilla ice cream.

If you want to make some money from catching bugs and are sick of pentesting Facebook, Google, and Microsoft's products, Uber may be your new favorite playground.
More often than not, when you find an app that offers a particular functionality, there are ten other apps on the Google Play Store that offer virtually the same features. But the reason we choose one app over the alternatives is mainly due to one thing—a preference for the user interface of the app we ultimately install.
Fugu - a simple virus in bash. I once told a friend of mine I'd written a virus in bash and he scoffed - "You can't write a virus in bash!" - he sniggered, like an ignorant idiot.
Step by step directions for finding the height of a trapezoid. Video: .

In the last iteration of how to train your python, we covered if/else and conditional statements. We're going to diverge a little today and cover lists. Lists are simply that, lists. It is a set of values located under one variable. Now that we know the definition of a list, let's learn about them! List Basics

Your brain holds a lot of precious information and is capable of great feats. However, there's one quality that doesn't lie among its strengths—memory security. Yes, that's right, your brain can be hacked, and it doesn't take a psychologist to do it. Anyone with the right know-how can change your memories for their own personal benefit, and you can do so to others, too.
A hemisphere is sphere that has been cut in half. When you cut the sphere in half you are left with the great circle, plus half of a sphere. This fact can be used to find the area, and the volume of a hemisphere. The video works several example problems in which the area and volume of a hemisphere is calculated.