How To: SQL Injection Finding Vulnerable Websites..
Welcome Back !! TheGeeks. SQL Injection (SQLI) Part-1

Welcome Back !! TheGeeks. SQL Injection (SQLI) Part-1

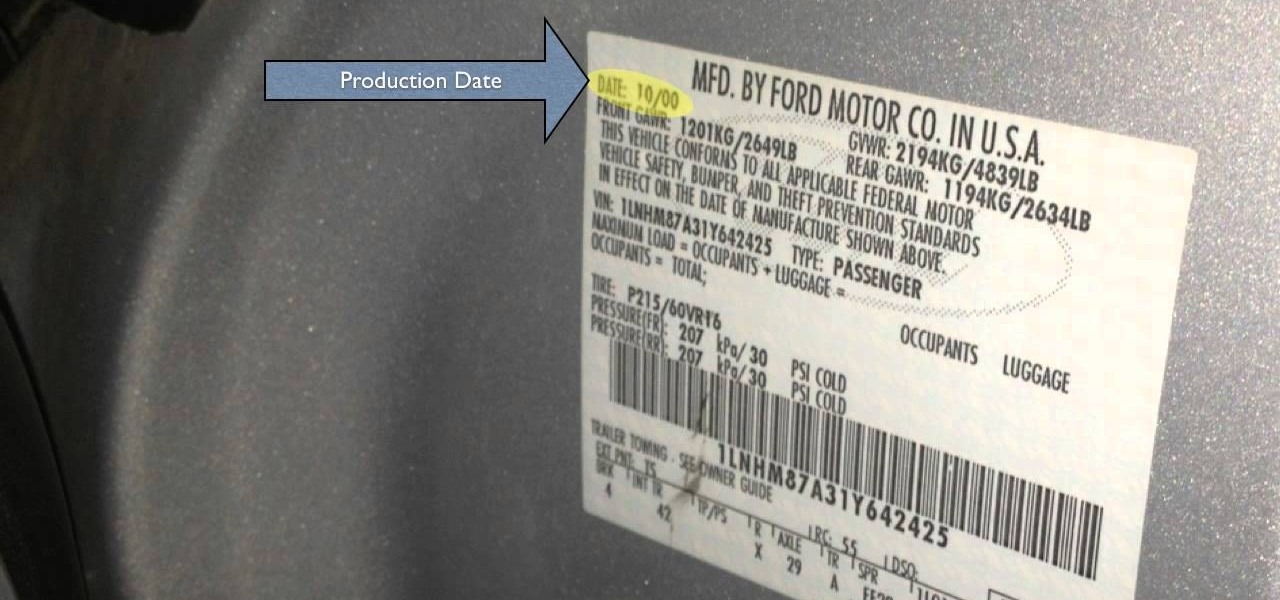
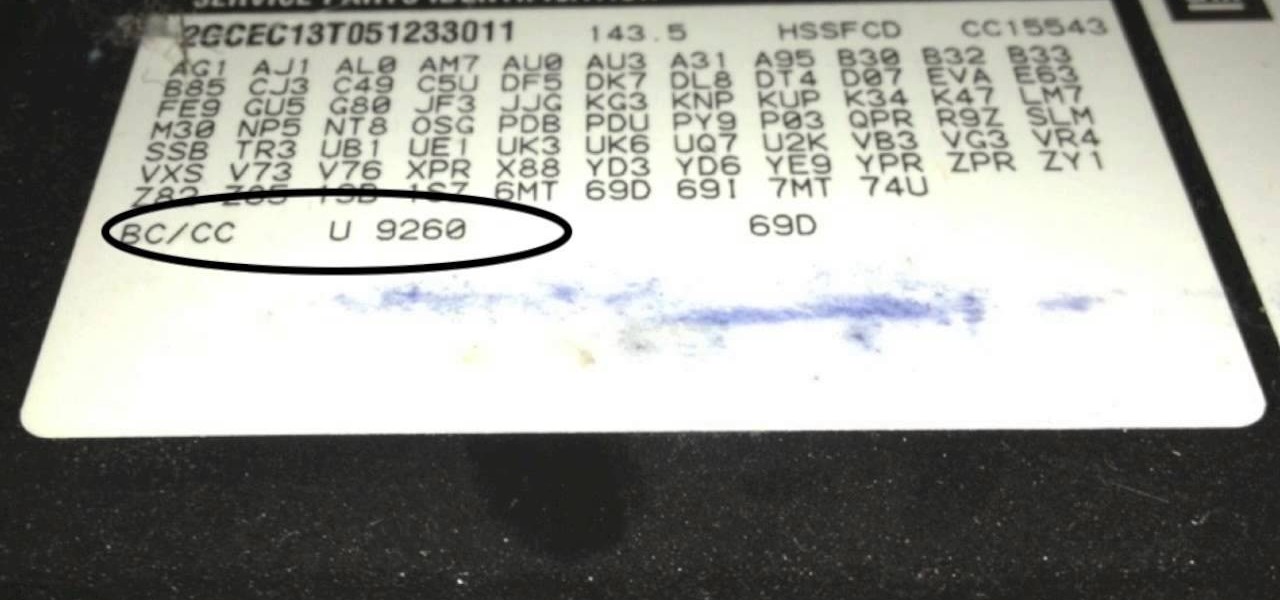
So i ran into a problem few days ago and it seemed to be very annoying one. I got hands on ASUS X55A with broken HDD. So i changed HDD and woo enter bios password. I hit enter and got into bios where uder security tab was shining ADMINISTRATOR PASSWORD INSTALLED. There was no user password but administrator password was set and it led to that i wasnt able to boot anything. At all.
Welcome learners, lets us proceed further with the information we already have. In this post we will explore more about finding hacked accounts online. We will look into how to find juicy info in pastes which are deleted on Pastebin.

This is second post in my series of posts for finding hacked accounts online. Please do read the part 1 of the post at http://null-byte.wonderhowto.com/how-to/find-hacked-accounts-online-part-1-0164611/

Welcome back, my fledgling hackers! In this series, I am trying to develop your knowledge of digital forensics, which is valuable whether you're choosing a career in it or just want to know how your hacker activity can be traced. Few professional digital forensic investigators have a hacking background, but the best ones do.

I found a stray kitten outside. I fostered him and then found him a home!
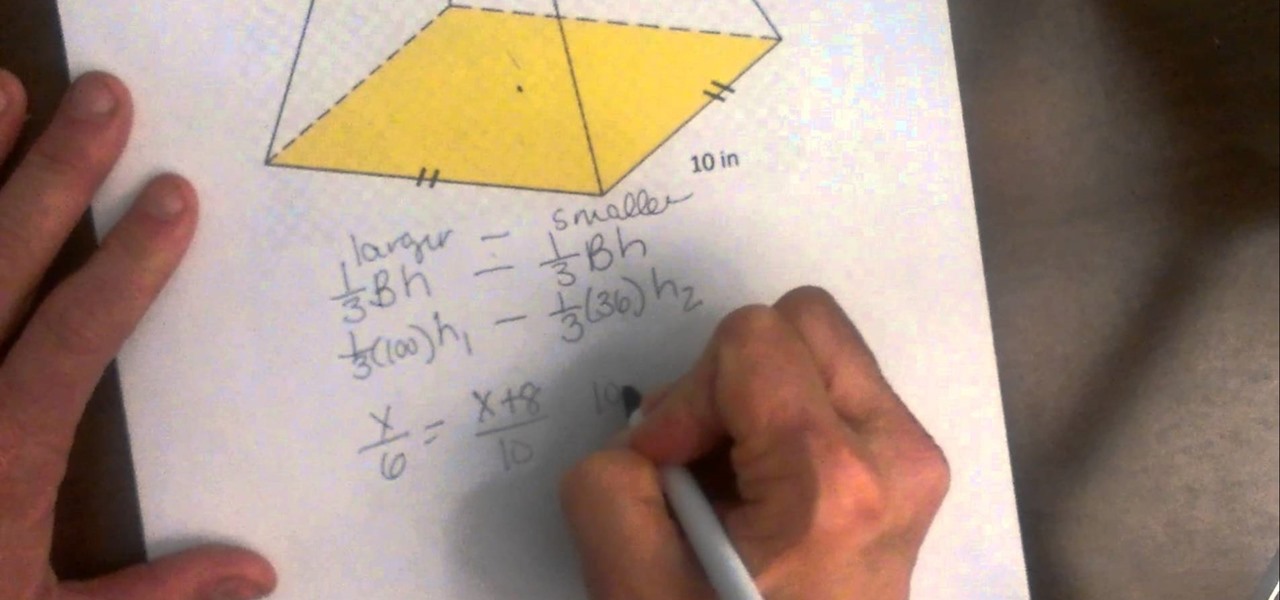
A truncated pyramid (frustum) is a pyramid with the top cut off. This video reviews how to find the volume.

This is a collection of various guides and tools available on the internet. Instead of searching for 1 you can easily find whaht your looking for here.
The sector area is a section of the circle. You can think of it as finding the area of a pizza slice instead of the entire pizza.
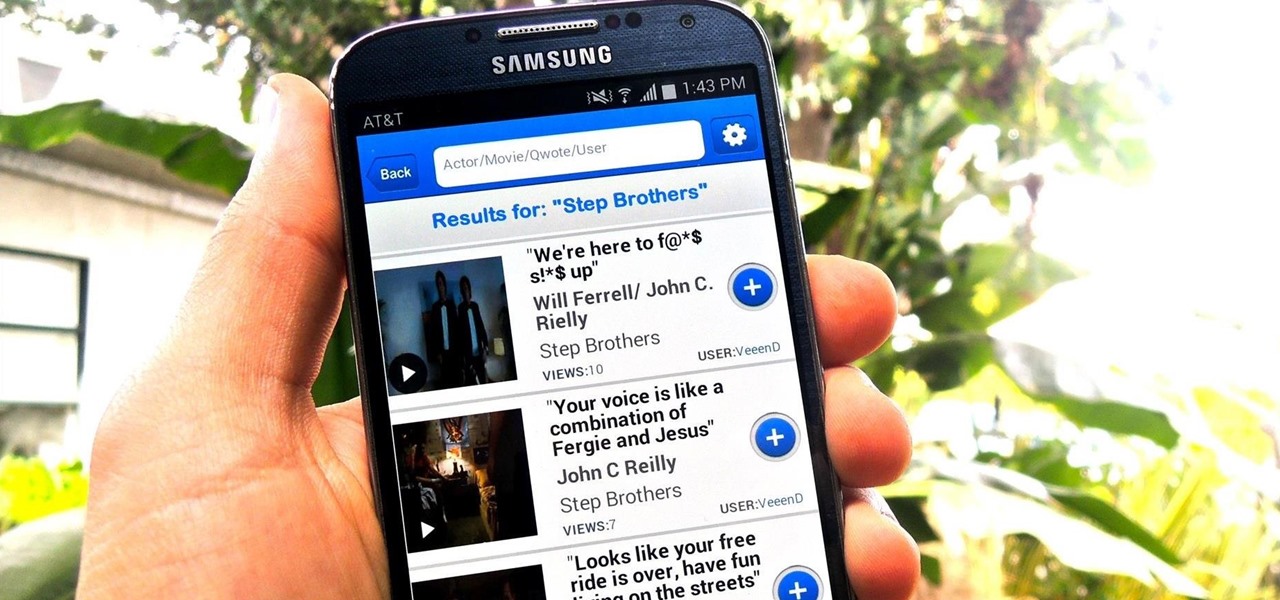
The Oscars are just around the corner, so it's the perfect time to remind people of your favorite movie moments, even if they're not exactly Oscar-worthy. But don't just settle on sending GIFs that don't include any of the fun audio, or resort to scouring YouTube for that one specific movie clip. Instead, take a look at Qwotes, a new mobile app from developer StudyUp.

Welcome back my fellow hackers. Today I'm going to teach you how to preform an Idle Scan. You may be asking what is an Idle Scan. Its a very stealthy scan because you don't use your own ip you use a zombie (in computer terms).

When you've gotta go, you've gotta go. No matter how hard you try and hold your pee (or the dreaded number two), it's going to find a way to leave your body one way or another. That's why it's always good to know where all of the nearest bathrooms are at all times, no matter where you are.
Could possibly be the most evil prank you can pull off. Use the noise maker found in a party popper to set up this evil prank that will just about scare the living $#?# out of anyone that puts it on.
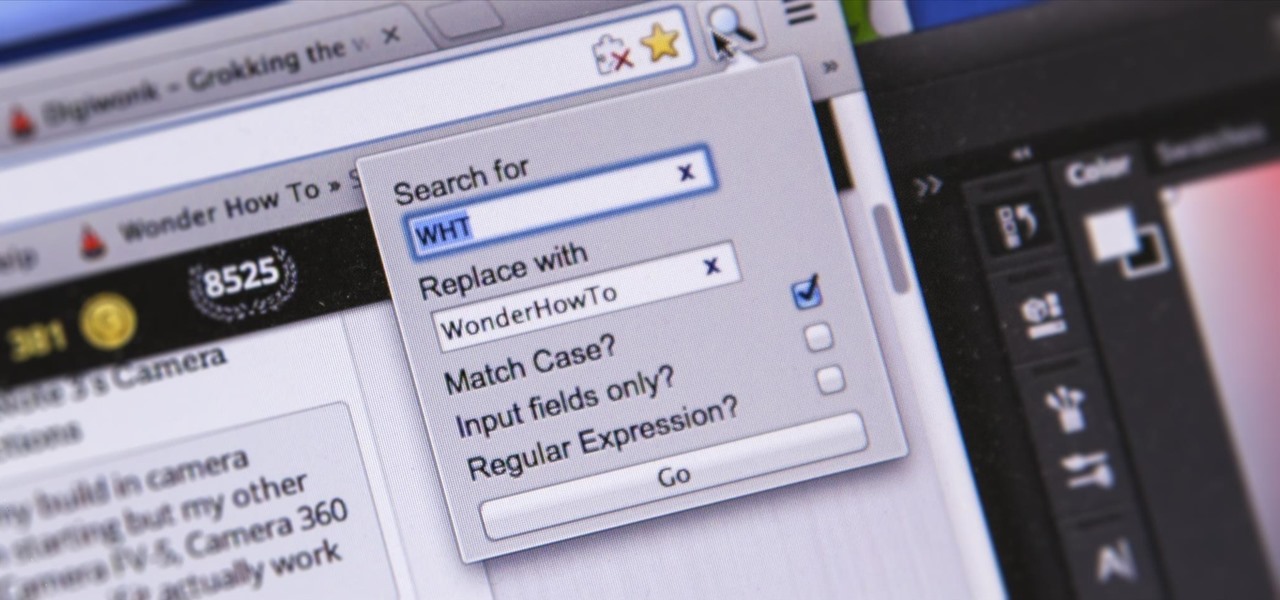
I'm sure you've been there—halfway through typing something out, you realize that one word you've been using more than any other has been misspelled. Perhaps it's a single word, acronym, or line of code that you find yourself typing quite often at work, but this one requires complicated hand gymnastics that you'd simply rather not perform over and over again.

The world of spices can be bewildering. They promise to make your food more flavorful if you know how to make the most of them. Unless you know a couple of essential tricks, however, it just seems like you're adding bits of colored powder to your food.
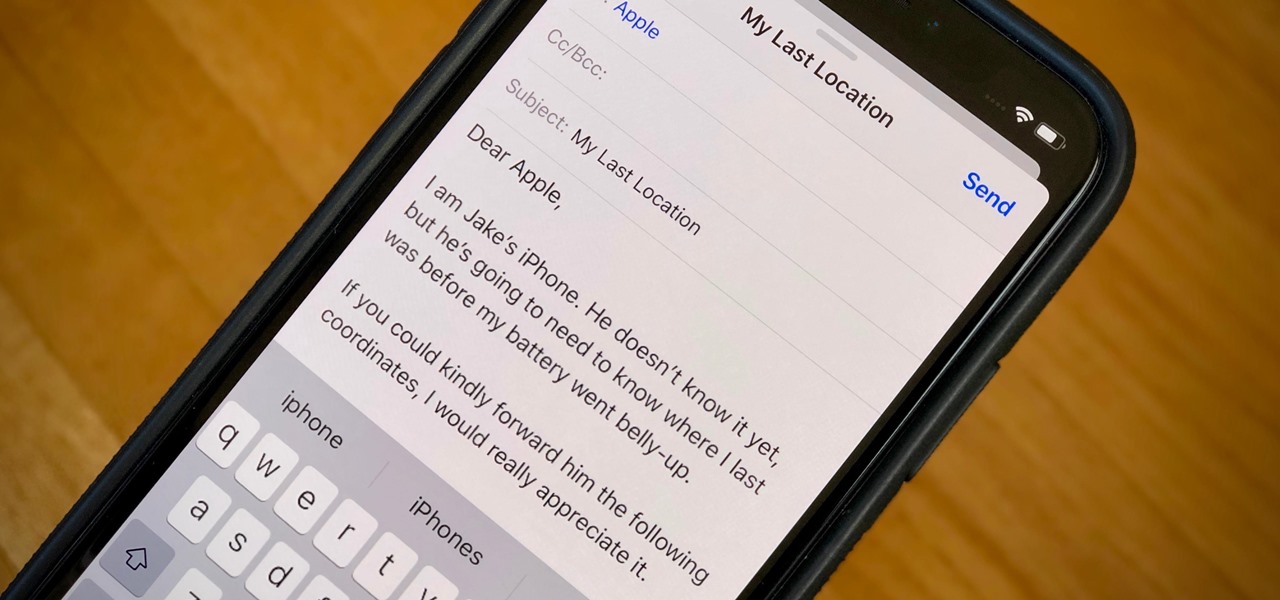
When your iPhone can't be found, Find My iPhone is a true lifesaver. When you use the feature, you can ping your iPhone and even see its current location on a real-time map. But what happens when your iPhone runs out of battery? Find My iPhone can't locate a dead iPhone, can it? You might be surprised to know it can, to a certain degree.

Staying healthy is a progressive challenge we all face throughout our lives, and figuring out just how to do that can be a challenge when it's not your job. For doctors, however, it is. Here's how they keep themselves healthy day to day.

Welcome back, my hacker novitiates! When we are trying to find vulnerabilities in a website to attack, we need a solid web server vulnerability scanner. Internet-facing web apps can open enormous opportunities for us as they are often riven with vulnerabilities and can often offer an entire point to the internal network and resources.

This tutorial video will show you how to find first tweet of any user in Twitter. You have to type first-tweets.com in address bar of your browser. The site will be redirected to discover.twitter.com/first-tweet page. Just type any user name and twitter will show the first twit of that user. Watch the video and try it yourself.

Welcome back, my greenhorn hackers! Sometimes, we don't have a specific target in mind, but rather we are simply looking for vulnerable and easy-to-hack targets anywhere on the planet. Wouldn't be great if we had a search engine like Google that could help us find these targets? Well, we do, and it's called Shodan!

Marinades are among my all-time favorite tricks as a cook for several reasons. They're easy like Sunday morning, they let time do what it's supposed to, which is work for you, and you get a huge return for relatively little effort on your part.

Just in time for Hanukkah! my easy vegan latke recipe (potato pancakes). You can find the full printable recipe here or you can watch me make them on YouTube in the video below. You'll find the ingredient list below the video.

This one's vegan! Yes, Himalayan rock salt (sorry caramel, this one's only with chocolate) makes this recipe amazing. You'll also find no butter, no milk and no other dairy products (yes these cake pops are 100% dairy free)in this recipe, so it's perfect for the vegan you love! :)

Welcome back, my fledgling hackers! The database is the hacker's "pot-of-gold," as it contains information that is very valuable to both the business and the hacker. In this, the second of my series on hacking databases, we're on the "hunt" for Microsoft's SQL Server. Although far from the most commonly used database (Oracle hold's that title), Microsoft's SQL Server is very often found in small-to-medium sized businesses. Even a few big businesses use it.

I want my Halloween costume to take as little effort as possible and be cheap—extremely cheap. That means I don't want to pay 50 bucks for some costume online or spend all day playing with liquid latex, and I most definitely do not want to visit a super crowded costume store in Hollywood.

Welcome back, my nascent hackers! Earlier, I wrote a guide on finding operating system and application vulnerabilities in Microsoft's own security bulletins/vulnerability database. In this tutorial, I will demonstrate another invaluable resource for finding vulnerabilities and exploits by using the SecurityFocus database.
In this Video Tutorial I show you five fundamental Steps to find a Job on an Online Job-Platform like LinkedIn.com. If you really follow and create this steps you will land an awesome Job.
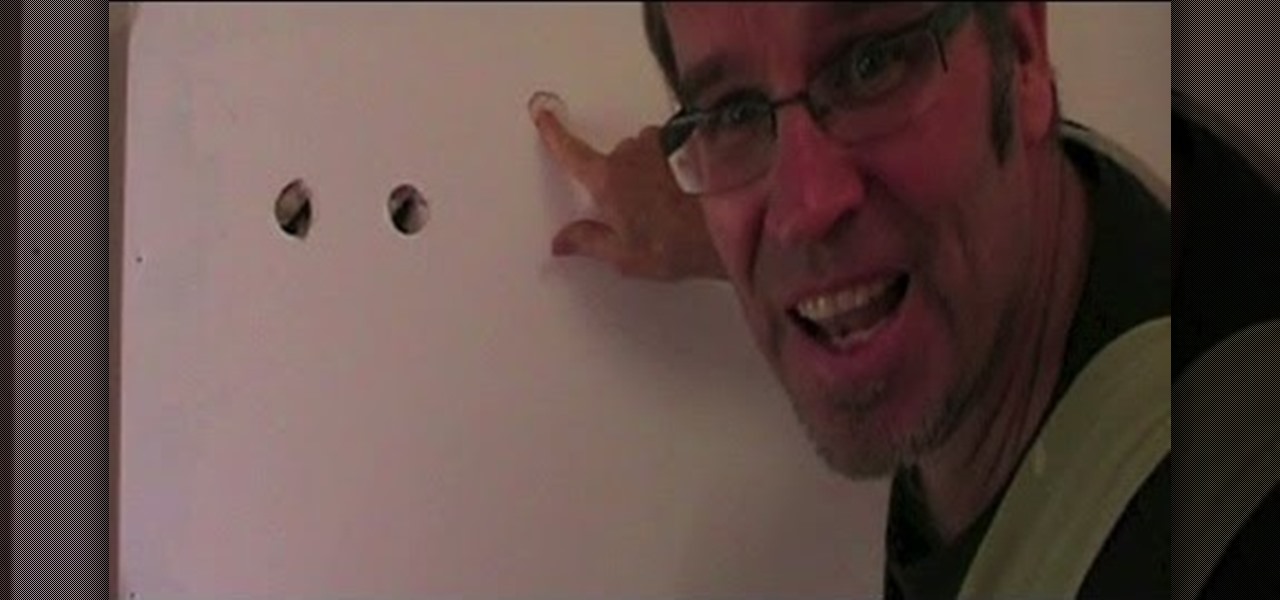
How to find a stud in the wall. How would you like to be able to find a stud in a plaster wall / drywall wall, easily and every time without an expensive stud finder? Let's look at how to find a wall stud using three conventional methods then l'll explain my foolproof method of how to find a stud in the wall without a stud finder.

If you've played any of the BioShock games, you already know about the powers that you can wield from you hands. It's kind of like being a wizard or Dragon Ball Z character. In previous BioShock games they were plasmids, but in BioShock: Infinite, it's a slightly new twist, and they're called vigors.
The only thing worse than not having any plans is not even knowing where to begin making them. Sure, you can check Yelp or one of countless other review sites to find a great spot, but there's no way of knowing what the vibe is like before you get there. Is it crowded? Are people having fun, or does it look pretty lame?

Living in Los Angeles has taught me one thing—parking is a luxury. If you are lucky enough to find street parking anywhere near your desired location, do not pass it up thinking you will get an even closer one. It does not exist. Looking for free parking? Get real. You can't even park at a busted meter in Los Angeles, despite state law saying otherwise. Now, finding a good parking spot is not just relevant for Los Angeles, but for other large cities and any other crowded areas, be it a shoppi...

Like in the original Black Ops, there are a bunch of funny and cool Easter eggs built into Call of Duty: Black Ops 2. Most have been discovered, like the Atari arcade invincibility on Nuketown 2025, but perhaps you didn't know about Thor's hammer?

Once you have the skills to bring your ideas to life, the hardest part is coming up with ideas. What do you do when you can't think of something to make? What happens when your well of inspiration runs dry?

Haven't found all of the hidden Easter eggs in Call of Duty: Blacks Op 2 yet? Then the one you're probably missing is this one in Zombie mode, which is a pretty cool shout to Skrillex, whose music seems to fit in quite well with all of those zombies running around.

Every year, Black Friday gets a little more insane. People get up at ungodly hours, wait in lines forever, and get into some of the most ridiculous fights you've ever seen. All in the name of saving some cash. Everyone loves saving money, but without a game plan, you could end up missing all the good deals and going home with nothing. Luckily, the Internet is here to take some of the stress out of holiday shopping. With these sites and apps, you can find out about all the best deals before yo...
As a technology writer, phone screenshots can pile up on your computer in no time. Testing out different apps, showing buggy software, and doing step-by-steps can lead to a plethora of mobile screenshots piling up on your computer's desktop. The problem with my screenshots is that they save as photo.png or photo.jpeg, as do many of my other photos. If I haven't finished a project or article, I tend to move them to different folders to save them for later. After a while, the screenshots begin ...