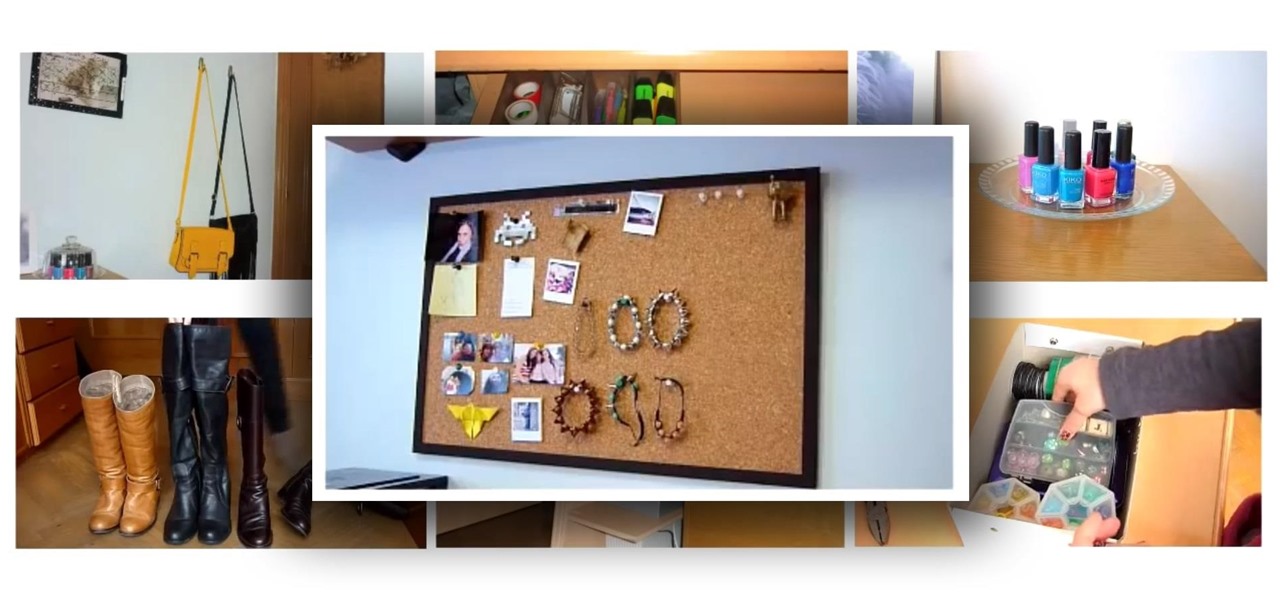
News: 7 Tips for Organizing Your Room
Today I'm going to show you 7 easy ways to organize your room. They are really simple and cheap so I hope you find them useful!

Today I'm going to show you 7 easy ways to organize your room. They are really simple and cheap so I hope you find them useful!
Sometimes I actually search Google Images for things other than GIFs and pictures of athletes' extremely hot wives. Google Images has helped me with school projects, work, and proving my friends wrong on numerous occasions. Unless you're strictly using it for the latter, you're going to have to be aware of copyrights.
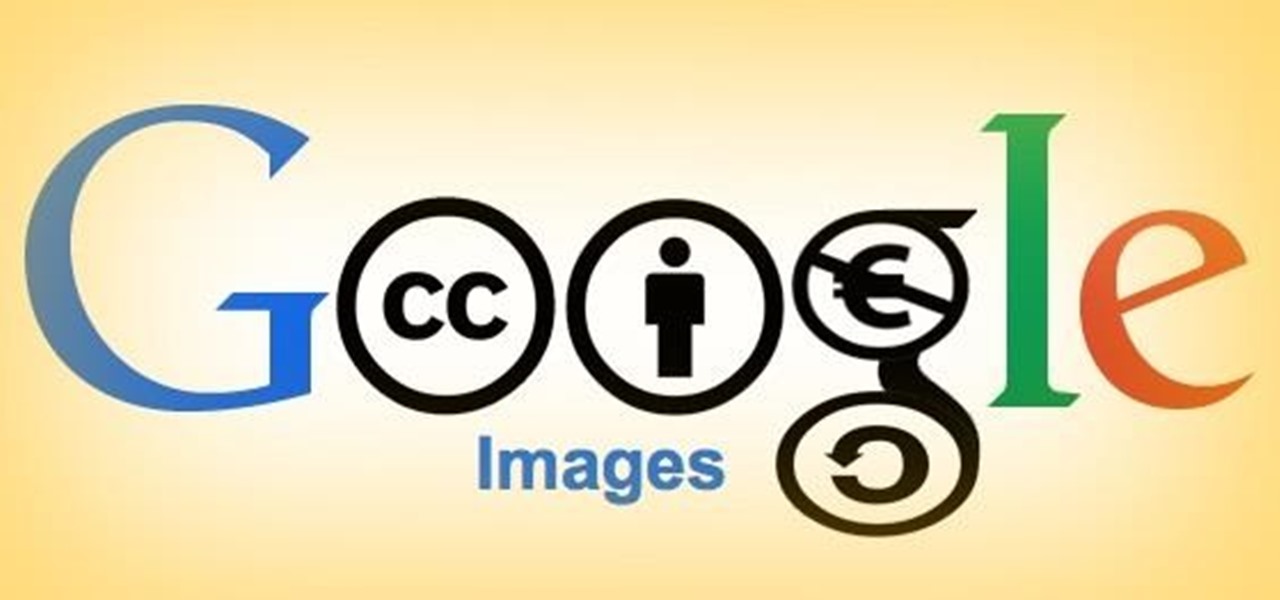
NSA aside, Apple makes it difficult for users to extract and download text messages from their iPhones onto a computer. For whatever reason (legal, devious, neurotic, etc), we've all found a time where we'd like to save backups of certain meaningful, important, or perhaps incriminating conversations (including all MMS or iMessage pictures and videos). While there are a handful of third-party applications that can help with this process, the majority of them cost money and implement certain te...
For a photo- and video-sharing app based around privacy, Snapchat sure has a lot of security holes floating around. At one time, you were able to take screenshots of Snapchats in iOS 7 without the sender knowing, which is something that you can still do on rooted Android devices.

While the Play Store has a plethora of apps available for finding lost Android phones, Google came out with its own web-based application, Google Device Manager, earlier this year to help you keep track of all your Android devices and remote lock, erase, ring, and track if need be.
In old-school Konami fashion, there's an Easter egg lurking inside your Samsung Galaxy S3, and I'm not talking about gingerbread men, robots, or jelly beans. In fact, it's actually an achievement, like those you would unlock in Black Ops on your Xbox 360, and it's pretty easy to find.
A wave of shock and anger swept across the country after Edward Snowden released private documents recounting the U.S. government's secretive mass surveillance programs. Although some of the fear was unwarranted (they don't read your emails or listen to your calls), many scrambled to find privacy of new heights for protection from the all-watchful eye. While the government may not be tracking you down, there are a myriad of other candidates that fill that Big Brother role—and I'm not talking ...

This slime is toxic-free and can be used as either a kid toy or to make a great prank. This slime can be made in just a few minutes and doesn't require much for materials. Our video explains in detail how to accomplish this project with step-by-step instructions.

Welcome back, my rookie hackers! Several of you have written me asking about where they can find the latest hacks, exploits, and vulnerabilities. In response, I offer you this first in a series of tutorials on finding hacks, exploits, and vulnerabilities. First up: Microsoft Security Bulletins.
What Is Pythagorean Theorem? Pythagorean Theorem is an equation discovered by a man named Pythagoras. It can be used to determine whether or not a triangle is a right triangle and find missing lengths of a triangle. The equation is: Parts of a Triangle

This is a illuminated pen holder that I made out of a couple recycled hard drives. The LEDs receive power from the standard USB cable connected to a computer. The stand for the penholder is taken from a clip light, and the penholder itself is made from 3 hard disk drive platters. Also, I hid a small 4GB flash drive inside the base hard drive for some hidden storage.

This step-by-step tutorial will show you how to install Mac OS on Windows 7 on Virtual Box. Video: .

Tire pressure is often overlooked, but can decrease your fuel mileage if you tires are not properly inflated. Have you ever peddled a bike with low tires. If you have, then you know it was much harder than when the tires are aired up. A car is no different. Low tires requires the engine to work much harder as well.

Is there anything better than finding a couple dollars sitting in your coat pocket that you forgot about? Well, after checking my trophy list for BioShock: Infinite, I realized that unlocking 1999 mode is actually an achievement. Hooray me. The achievement trophy is called "Should Auld Acquaintance", and instead of beating the game in easy, normal, or hard difficulty, you can just use the Konami code (found here) to skip right to 1999 mode and get that trophy.

This week, another guest returns to our Steampunk R&D show for the second time, Thomas Willeford. In our very first podcast, Thomas talked to us about creating his empire; this time we most notably talk about his recent appearance on the Science Channel's program Odd Folks Home, in an episode entitled "Blow Off Some Steampunk". Thomas Willeford is the owner and operator of Brute Force Studios, and has been responsible for some of Steampunk's most recognizable props and accessories, such as th...
Being lost sucks. There really is nothing worse than going to a huge event with a bunch of friends or family and then getting separated. Instead of partying with the bros, you get stuck next to this lame couple who keeps seriously making out every ten seconds. SMH.
Playlists are a great way to organize and share groups of videos on YouTube. Playlists can consist of your videos, someone else's videos, or a combination of the two.

Like a computer, your brain can store and process large amounts of information. It can remember names, solve math problems, and save tips that you might need at a later time.

MAC addresses (not to be confused with Macs) are unique identifiers assigned to network devices in order to access the internet. Hotels use these Mac addresses in order to check if a registered patron has agreed to their terms and conditions, how much bandwidth is being consumed, and of course, whether they've paid or not.

Have any Star Wars fanatics in your family? Well, here's a great Christmas gift idea for those Star Wars fans who think they have everything... a freaking LEVITATING DEATH STAR!

The Jetsons may not have gotten everything right about the future, but even though we may not have flying cars or live in the sky (yet), one thing they imagined correctly was our electronics eventually being able to understand us.

People use search engines for a wide variety of subjects (just look at some of the results that pop up in autofill). The results you get with each different search engine are usually different, but almost all of them display the same number of results per page by default—ten. If you find what you're looking for at the top of the first page, great. But if you have to do a lot of digging, it can be a pain to load so many different pages to find it, especially if your connection is slow.

Windows 8 and its new Windows Store have simplified the process for uninstalling and cleanly deleting applications from your computer. Removing applications in older versions of Windows required a few more steps: My Computer -> Control Panel -> Add or Remove Programs -> Find the Program -> Click Uninstall.
The Dark Knight Rises. The Amazing Spider-Man. The Avengers. Halloween is a few weeks away and all we're going to see are these same ol' superhero costumes. It's like that every year, due to the immense popularity of comic book films by DC and Marvel.

There are certain files on your Mac that do not warrant encryption, but still need to be hidden. Whether it be snoopy parents trying to find pictures, or friends stumbling upon one of your love letters, there are times when you need to hide a file and have it kept secret. Obscure Your Files with Obscurity

It seems like every other day there's a new security threat or data leak in the news. Whether it's your credit card PIN or your smartphone's apps leaking your email address, no one wants their personal information out there, especially passwords. And if you use the same email address and/or password for more than one site, the effects of someone getting hold of your credentials can be catastrophic.

For this project, I decided to rip apart a microwave I found in my neighbor's garbage can to see what was inside. With permission, of course! True story!

Yesterday, the entire Internet was talking about how the new Kindle Fire HD was supposed to be incredibly difficult to hack. Turns out, the folks over at XDA Developers are smarter than they thought—one day later, the mystery has already been solved. The exploit is the same one found by sparkym3 in Ice Cream Sandwich, but Amazon must have forgotten to patch it. As with any root, you can cause some serious damage, or brick your device completely if it's not done properly, so proceed at your ow...

It's no secret that there's a lot of surveillance going on these days. It's easier than ever to end up in a database, and even former government agents are speaking out about the atrocious amount of spying being done against our own citizens. They've targeted our laptops, cars, IP addresses, and now they're coming for our iPhones. AntiSec hackers managed to get their hands on a list of over 12 million Apple UDIDs (Universal Device IDs) from an FBI computer, and they published 1,000,001 of the...
There have been plenty of headlines recently about fake followers in both politics and entertainment. Everyone gets hit by a spam account here and there, but when a large percentage of someone's followers are fake, it can look pretty bad, especially with influential people being accused of buying their followers to look more popular.

Let's say you forgot the code to your Master Lock combination padlock. What can you do besides buy another one? Well, there's a surprising abundance of ways to open a combination lock other than with just the combination, some of which will even let you reset the code. Of course, these hacks aren't limited to folks just looking to open their own locks, but let's just assume that's what you're here for.

Even though we all know it's a bad idea, a lot of people still use their browser's store password function to keep up with all their accounts. While convenient, this shortcut also makes their passwords very easy to find if you have access to the computer they're stored on.
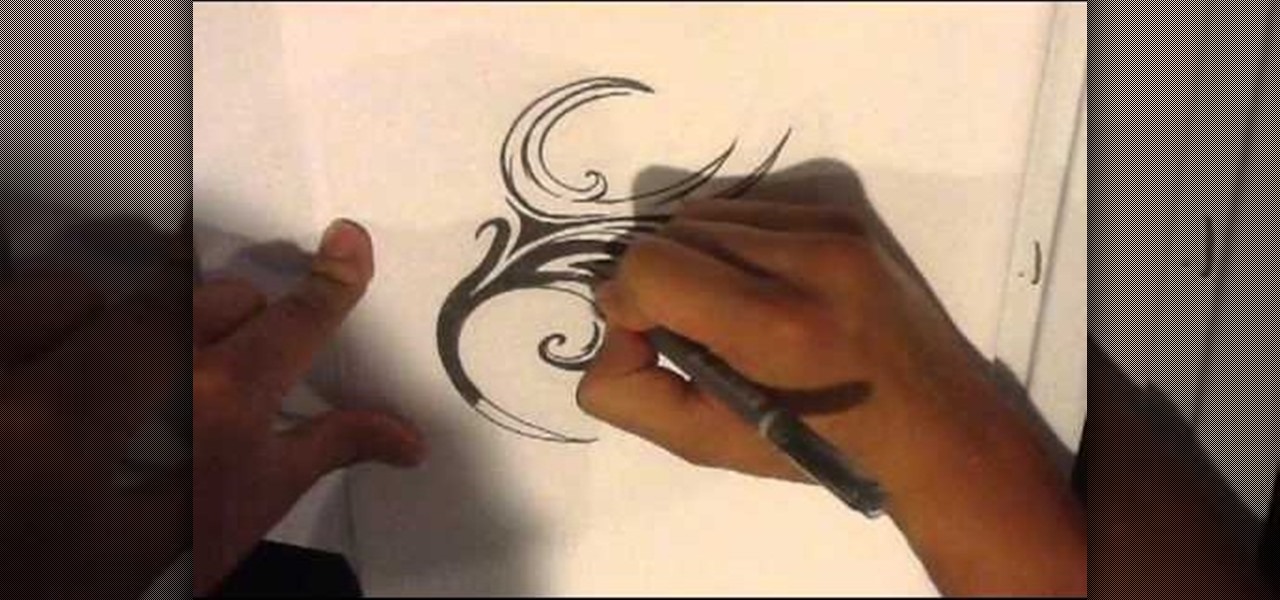
How to draw a tattoo. I go over how to draw your own tribal tattoo design. i sketch out a random assortment of extremely light lines. This is meant to help find distinct interesting shapes. Once you find something elaborate on that shape. Whether you want t be a tattoo creator, learn to tattoo. Or just want to do drawings of skulls. I try to go over a small part of it here. Source: http://howtodrawatattoo.blogspot.com/
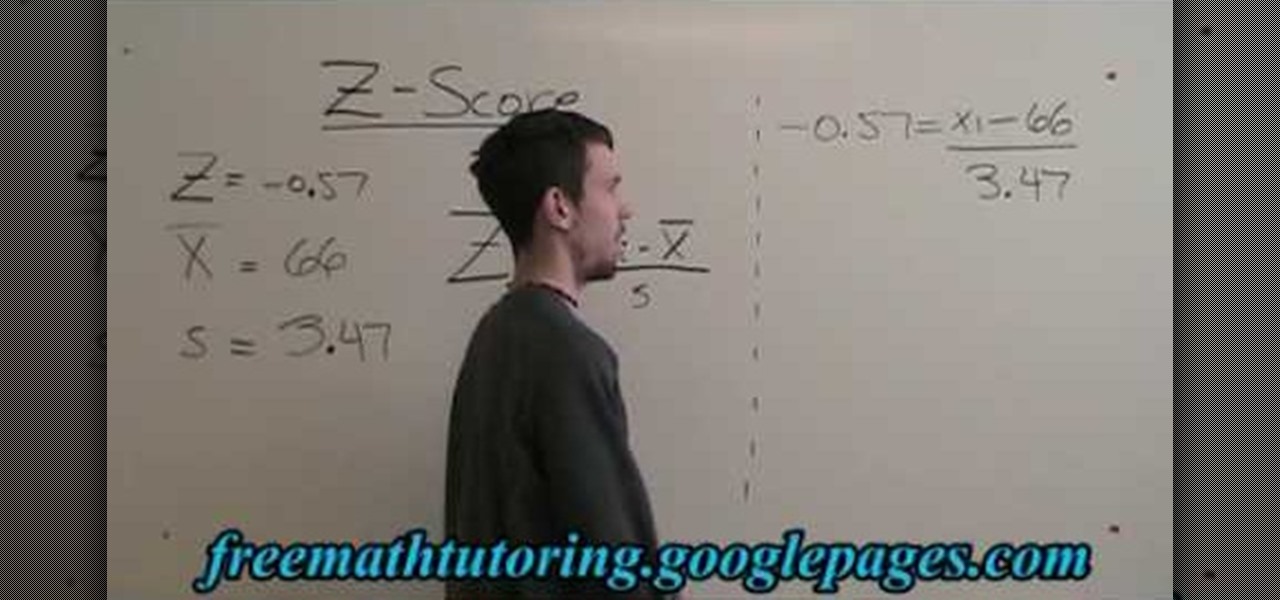
In this free video math tutorial, we learn how to use the Z-Score formula to find a data point (Xi) in statistics. With mathematics, as with anything else, not everyone progresses at the same rate. Stats is no exception. Happily, in the age of Internet video tutorials, this isn't a problem. Those who progress quickly can go beyond what's being taught them and those who are struggling likewise have all the time in the world to catch up. Whether you need help finishing your homework or studying...

In this tutorial, we learn how to delete an old friend from Facebook. First, you need to log onto your Facebook account. After this, you will need to go to where it says 'friends' on the top of the screen. After you click on this, you will go to the left hand side of the page and find the list of your friends. This will come up on your screen and then you will see the list of all your friends. Next, you will find the friend that you want to delete and click the 'x' on the right side by their ...

If you had the chance to pick up the Collectors edition of Fallout: New Vegas, you received a beautiful hardcover graphic novel of some of the events leading up to your eventual stroke of bad luck. If you read it, it follows the Great Khans as they travel with Benny to your location, and talks about Chance, the blonde haired, Conan-Like, Great Khan, killed by- hey wait, no spoilers! Anyway, if you'd like to find his grave and his equipment, check out this video! In it you will get the locatio...
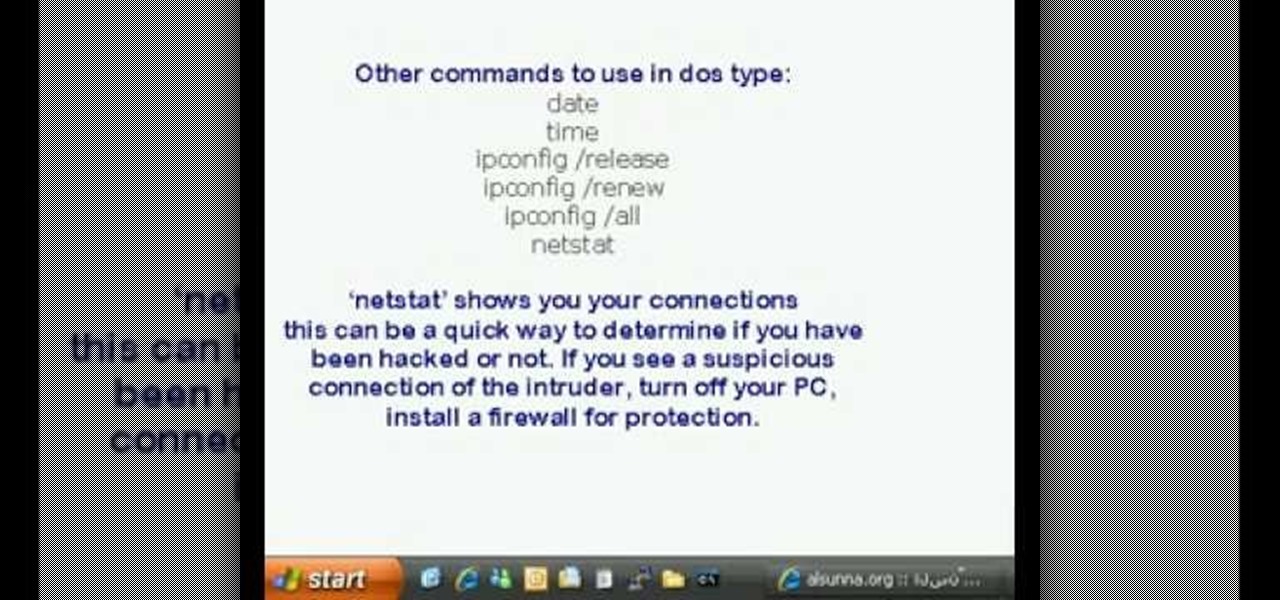
This is a video tutorial in the Computers & Programming category where you are going to learn how to find and ping your IP address. Go to start > run and type in "cmd" to get the DOS window. Here type in "ipconfig" and hit enter. If you are online, your IP address will be displayed. If you are offline, go online and try again. Then in DOS type in "ping yahoo.com". This is to see if you can connect to Yahoo. If you are online, the site will reply 4 times. If you type in "netstat", it shows yo...

This video tutorial is in the Education category which will show you how to subtract basic fractions in simple mathematics. You can do basic subtraction of fractions if the denominators are the same. If they are not, then find the lowest common multiple of the denominators and convert the denominators to their lowest common multiple. For example, to subtract 1/2 from 3/4 find the common multiple of 2 and 4, which is 4. So, the problem 3/4 - 1/2 can now be written as 3/4 - 2/4. Since, the deno...

In this video, we learn how to upload pictures and set a profile picture onto Facebook. First, you will need to locate the pictures you want to use on your computer. After this, log into your Facebook account and click on your profile, then the tab that says photos. Now you will be on a new screen where you can browse your computer to find the photos you want to upload. After you click on all these, click the "upload" link and then wait for the photos to load. After this, you will be able to ...

If you didn't find the solution to your misfire problem in this video, then the 1999 Mercury Villager 3.3L might have a code P0305 (Cylinder #5 Misfire). This is great troubleshooting advice from a professional mechanic to help you diagnose the problem. The vehicle is a '99 Mercury Village, 3.3L, with 150,000 miles on it. The chief complaint is the CEL (check engine light) comes on and it runs like it has a misfire. It feels like a steady consistent misfire, which is code P0305. Watch the vid...