What appears to be an ordinary MP4 may have been designed by an attacker to compromise your Linux Mint operating system. Opening the file will indeed play the intended video, but it will also silently create a connection to the attacker's system.

So, someone on your shopping list has an iPhone. Lucky for you, Apple's line of smartphones are practically made for accessories. From AirPods to adapters, there's something for every iPhone user in your life. Are you feeling overwhelmed by the options? You've come to the right place.

Apple's iOS 13 has been available for beta testing since June, and the stable release pushed out to everyone on Thursday, Sept. 19. To help you make the most out of iOS 13 for iPhone, we've rounded up everything you'll want to know, whether a colossal feature, small settings change, interface update, or hidden improvement.
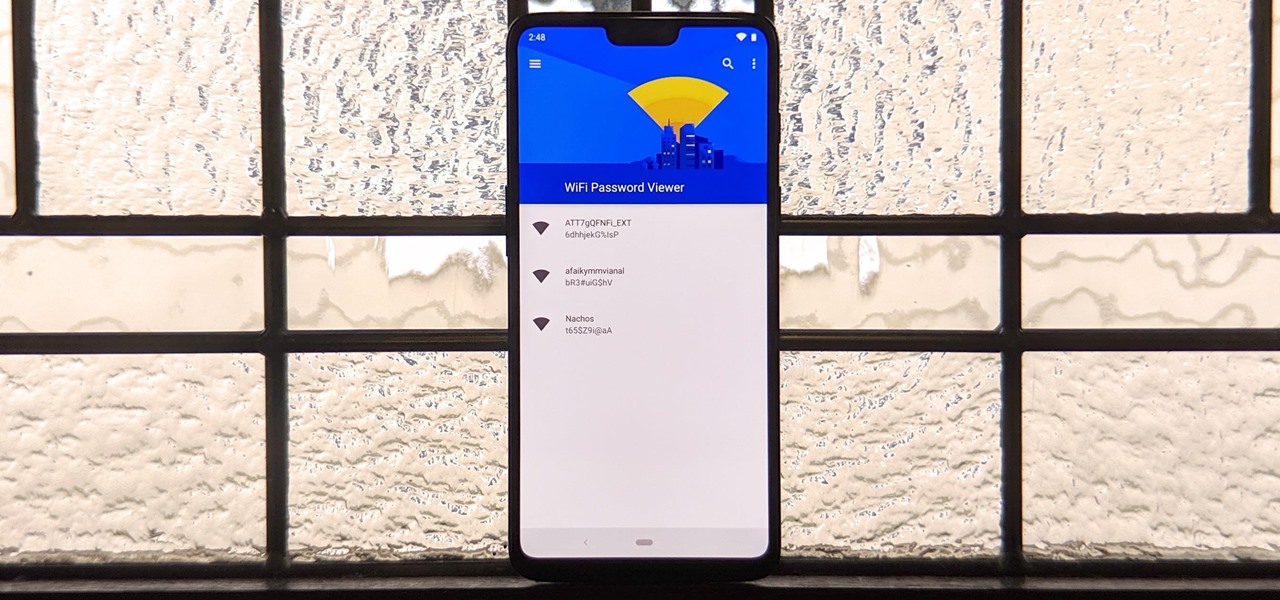
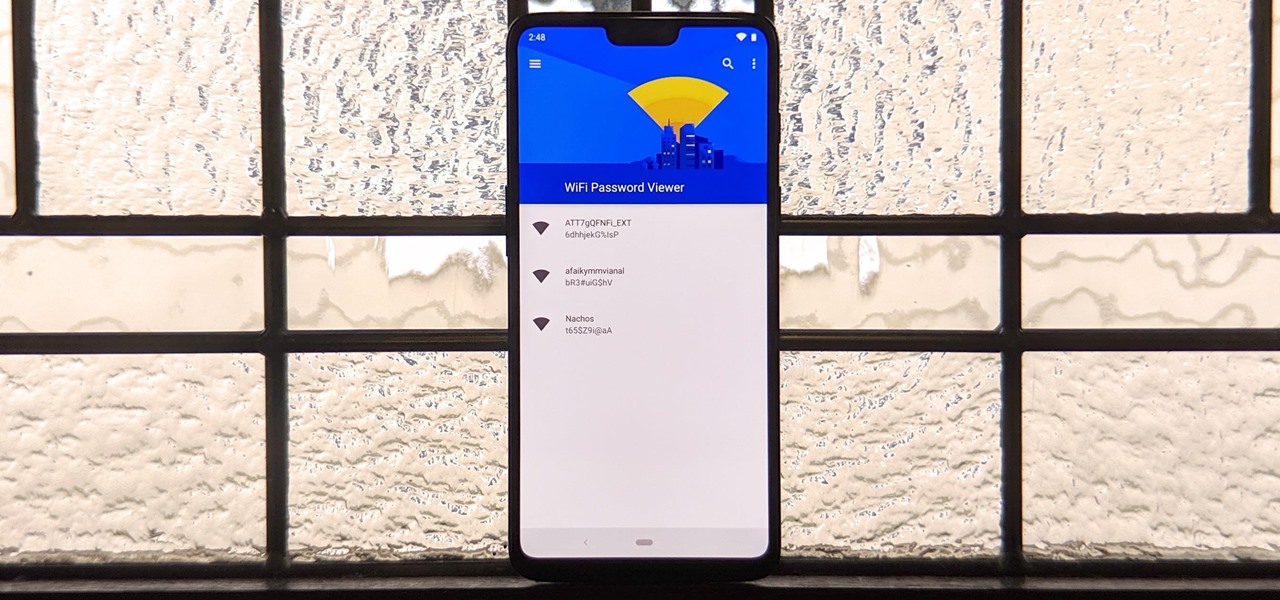
You've probably connected your Android device to dozens of Wi-Fi networks since you've had it, and your phone or tablet remembers each of them. Whether it's a hotspot at home, school, work, the gym, a coffee shop, a relative's apartment — or even from a friend's phone — each time you type in a Wi-Fi password, your Android device saves it for safekeeping and easy access later.

Trying to figure out which music streaming service to subscribe to can be a difficult task when the playing field is so crowded. Each has its benefits, as well as downsides, so finding the right one for your needs and wants can take a lot of overwhelming research. But we've done all the research for you to help you find the best music subscription your money can buy.

SSH is one of the most common protocols in use in modern IT infrastructures, and because of this, it can be a valuable attack vector for hackers. One of the most reliable ways to gain SSH access to servers is by brute-forcing credentials. There are a few methods of performing an SSH brute-force attack that will ultimately lead to the discovery of valid login credentials.

There's never been a better time for streaming videos on your phone. With so many options available (including a potential mobile-only Netflix tier) and so many new smartphones having large screens, there's a good chance you know someone who mainly use their phone for videos. And if you looking for a gift for them, there are some great options.

With smartphone cameras and software getting better and better every year, more and more users are getting passionate about photography. So when you're shopping for a gift to get someone, if they have a smartphone, chances are they'll more than appreciate some tools and accessories for taking better photos with their pocket friend — and we've got some gear ideas they'll love.

There's a lot more to your iPhone's dialer screen than just entering phone numbers and hitting the green call button. It's not very obvious, but there are secret codes that you can enter on the dialer to find out information about your device, help troubleshoot issues, and mask outgoing calls, to name just a few things.

To name just a few companies, VK, µTorrent, and ClixSense all suffered significant data breaches at some point in the past. The leaked password databases from those and other online sites can be used to understand better how human-passwords are created and increase a hacker's success when performing brute-force attacks.

UPDATE: Due to increased, uncontrollable spam, submitting anything other than comments on WonderHowTo and its affiliated network of sites is temporarily closed. Only current and past members who have previously submitted helpful news and guides may be able to submit forum posts.
I read in the Economist about a new study that reveals that our galaxy - not even the entire universe - should be colonized by now. This paper profoundly reaffirms the conundrum that is the Fermi Paradox, an observational problem that is sometimes referred to as the Great Silence.

LONDON: Bad at maths? Gorge on chocolates before you attempt your next examination. A new study has revealed that eating chocolate could improve the brain's ability to do maths as well as boost your energy level.

VANCOUVER: Contrary to common opinion, daydreaming is not slacking off because when the brain wanders it is working even harder to solve problems, new research has shown.

Amaze friends and family at your next dinner with this amazing magic trick. See the magic spoon melting trick revealed.

Incredibly artfully done, KlairedelysArt's SFX Terminator makeup look creates the illusion of peeled back skin to reveal the Terminator beneath. Amazing Halloween look for a chick.

Ever wonder how they got the coin to move through the bottle from your hand? Well here is the answer and it is as simple as making pb and j. Learn how to move a coin through a bottle and astonish all your friends. Make a signed coin go through a bottle revealed.

In order to write a revealing cover letter, you will need to freshen up your resume. Try re-writing it. Change your format. The most common form is chronological. Remove all the empty words and vague phrases. Remove all clichŽs. Highlight your achievements not just the duties you performed in past jobs. Try to quantify your achievements. Create a clear career summary. This will help the employer to see how you will be able to fit in and help prospective employers. Fill in all of the gaps. Don...

Now you see it, now you don't! Team up with the science sleuths of A-TV to make your own invisible ink.

An easy to learn trick with just one card! Kipkay performs and the reveals the secret behind the warped card magic trick. Simple but effective. Do the warped card magic trick.

Falling in line with tradition, Samsung is ever-so-subtly teasing their big Galaxy S5 reveal at an event dubbed Unpacked 5. Just like with previous releases, we've seen a steady stream of information leak about Samsung's next flagship, from possible UI elements to more detailed hardward and software information. Now, we've got a date to look forward to, on the first day of Mobile World Congress no less.

Xeni visits the offices of the Electronic Frontier Foundation and speaks with Jake Appelbaum and Bill Paul, two of the authors of a security research paper that shows how your computer's memory can be tricked into revealing data you thought was safely encrypted, and out of the reach of others. Hack into encrypted computer data.

Learn how to create hidden messages on paper that can only be revealed with fire. Create hidden messages.

The famous Houdini trick is revealed. Unlock handcuffs with a Bobby pin.

The NPD Group is a market research firm that issues the most trusted sales numbers for video games. They just released their second quarter 2011 report, and the trends it reveals confirm much of what we here have been speculating here at Indie Games Ichiban (and what we've been hoping for): downloadable games have risen, while full-box retail games have fallen—that is in the US, at least.

If you have a pocket door installed in your home, there are moments when it can become damaged and fails to work. If you're having problems with it and are finding a quick solution to replacing it or repairing it, this tutorial will be there to help. Check it out and enjoy! Repair and replace pocket doors in your home.
ATTENTION COLLISION REPAIR INDUSTRYHave you ever put your stud in your stud gun to repair a dent and the stud falls out before it reaches the panel? Sure it has, it has happened to all of us. However, the new Magna-Spot eliminates this problem with their exclusive (MPS), which secures the pins in the electrode. You can read the press release below to learn more of the benefits.ENTER AND WIN THE NEW MAGNA-SPOT STUD GUNDetails to this contest are going to be revealed in layers as follows:

this video is about doing a card. The first thing you do is show a card to a person but you don't see it. Then you place that card face down on the table. Then you go through the deck of cards and take out four small decks of cards and place them face down on the table. Then put there card aside in the middle of the deck of cards. Then you take a card from the top of the deck and place it face up on the table. Now place the four deck of cards together in your hand and spread them out on the t...

In this two part video tutorial, Eran Stern reveals the first text trick in his series and shows how to design an audio waves animation with the After Effects Text Tool.
The Department of Homeland Security has been forced to release a list of keywords and phrases it uses to monitor social networking sites and online media for signs of terrorist or other threats against the U.S.
The top-secret US National Security Agency is not required to reveal any deal it may have with Google to help protect against cyber attacks, an appeals court ruled Friday.
It is now official. The mainstream media is no longer covering Ron Paul’s presidential campaign. A few weeks ago Dylan Byers of Politico reported that NBC News was the only media organization that still had a reporter covering Ron Paul full-time.
THE Pentagon's top two officials have revealed that President Barack Obama had asked for preliminary military options to respond to the Syria conflict but the administration still believed diplomatic and economic pressure was the best way to protect Syrians from the Assad government's repression.

Exposure 3.2 | Aperture f/5.6 | Focal Length 70 mm | ISO Speed 200

Anne Hathaway appeared on The Daily Show with Jon Stewart to promote her new movie, One Day. But before that, she proclaimed herself a Scrabble fiend. She likes to play the board game with family and friends, as well as local play on the iPhone and solo play against her computer. And Jon reveals his son's strategy for using "Best Word" on EA's Scrabble version (something I'm not to keen on)...

Suda51's next game. Think of it as Buffy, but with chainsaws and zombies.

At a windows partner conference in Taipei, Microsoft unveiled their Windows 8 tablet. First impressions: WOW! Looks like they are actually innovating for once.

Who hasn't gotten completely lost in Minecraft? You can build a compass, but that's no replacement for a map.