Microsoft Excel is one of the most powerful programs for modern businesses. By allowing you to manage, sort, and analyze large collections of data, Excel provides an essential service for any company interested in using the power of data science to its advantage.

Augmented reality gaming pioneer and Pokémon GO mastermind Niantic is putting the pieces on the gameboard to prepare developers and gamers for the launch of its AR cloud platform.

With $100 million in grant funding already available to developers via its MegaGrants program, Epic Games is sweetening the pot with some gear for Magic Leap developers.

The North remembers...that smartglasses are the future! Game of Thrones jokes aside, the smartglasses startup opened its doors, and we visited its Brooklyn store to get our hands the consumer-focused Focals smartglasses.

Format strings are a handy way for programmers to whip up a string from several variables. They are designed to save the programmer time and allow their code to look much cleaner. Unbeknownst to some programmers, format strings can also be used by an attacker to compromise their entire program. In this guide, we are going to look at just how we can use a format string to exploit a running program.

Being able to write your own hacking tools is what separates the script kiddies from the legendary hackers. While this can take many forms, one of the most coveted skills in hacking is the ability to dig through the binary files of a program and identify vulnerabilities at the lowest level. This is referred to as binary exploitation, and today we're going to check out a tool known as Protostar.

As demand for AR and VR developers continues to increase, particularly with the advent of Apple's ARKit platform, Unity has partnered with online learning company Udacity to help developers sharpen their skills for these jobs.

The status of Uber's driverless program remains a big unknown amid the company's recent woes, but a reported multibillion-dollar shot in the arm by Japanese tech giant Softbank could change all that.

For companies wary of the temperature, PTC just made it easier for them to dip their toes in the waters of augmented reality.

If you want to make some money from catching bugs and are sick of pentesting Facebook, Google, and Microsoft's products, Uber may be your new favorite playground.

Researchers have discovered a "severe vulnerability" that allows attackers to use eBay to distribute malware, and the online auction company has no plans to fix the problem.

How's it goin'? In this tutorial, we will learn about the security issues of the popen and system functions. I've seen a few people attempting to run command line utilities or whatever it is they require with calls to these two functions but may not know the security implications which come along with it. I will show you using an example from the wargame IO Smash The Stack.

In many programs on Linux, you'll come across programs which allow you to specify additional arguments instead of just simply running the program by itself. If you've used the Kali distribution, I'm more than certain you'll have come across these with the command line tools, else if you have been following these tutorials, we have already come across three tools which also use the same technique, i.e. gcc, gdb and wc. How do we do this with C? Let's find out.

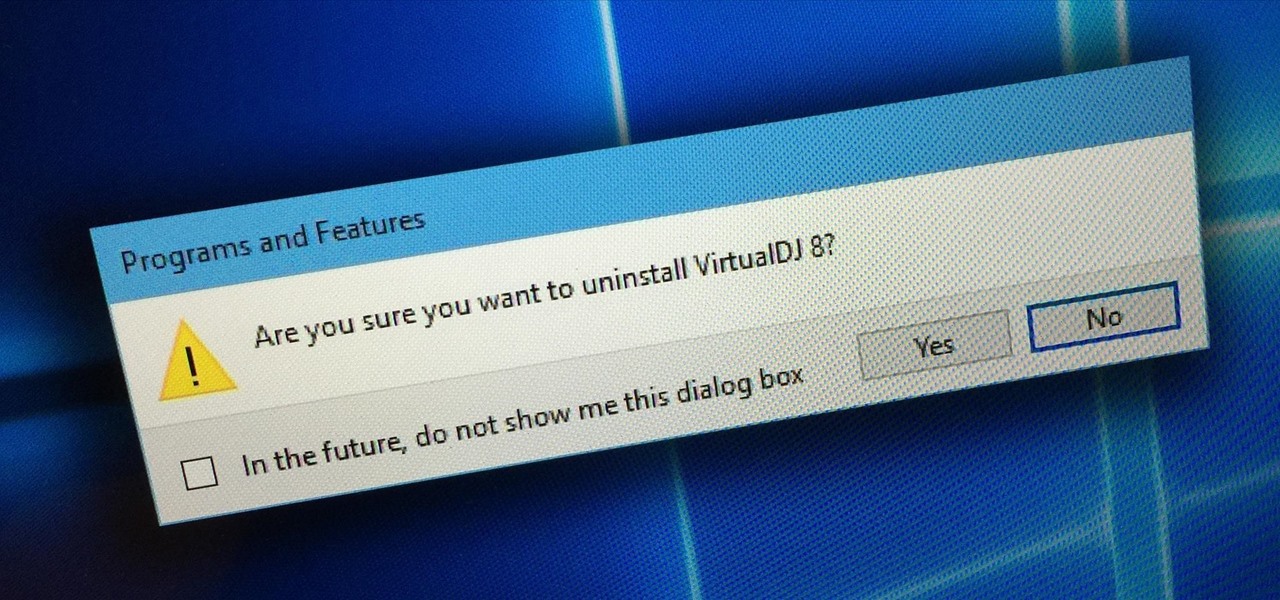
Uninstalling programs in Windows is not the nicest procedure. Some programs bundle a nice uninstaller with them which helps to ease the process. Other programs, mainly those that utilize the Windows Installer technology, begin the uninstall process right away. This can potentially be problematic for users who are trigger-happy with the mouse.

bObsweep robotic vacuums automatically clean whenever instructed to do so by an owner or because of a pre-programmed schedule.

In this simple tutorial you will be shown step-by-step how to write local shellcode for use on 64-Bit Linux systems. Shellcode is simple code, usually written in assembly that is used as payload in exploits such as buffer overflow attacks. Payloads are the arrow head of an exploit: though the rest of the arrow is important for the delivery of the attack, the arrow head deals the killing blow. In reality, payloads are slightly less exciting yet far more interesting and intelligent than medieva...

T-Mobile continues to make waves in the U.S. wireless market behind CEO John Legere's UnCarrier program. At the latest installment in a series of industry-challenging announcements, Uncarrier 5.0 unveiled Test Drive. The new program is set to allow would-be customers to try out the "latest generation" iPhone for seven days on T-Mobile's network without any financial commitments.

I have shown here to install Java development kit. It also contains the settings of path and classpath to prepare for java programming.

How much privacy are you getting as an AT&T customer? With the recent leaks confirming the National Security Agency's surveillance on AT&T users, and the ongoing trial of Jewel v. NSA, it seems not much at all.

When it comes to text documents and spreadsheets, Microsoft Office is the be-all and end-all office suite—but it's not cheap. Paying anywhere from $140 to $400 puts a big dent in your bank account, especially if you're a broke college student eating ramen for breakfast, lunch, and dinner. Something that I wish I would've known about during college is Microsoft's HUP (Home Use Program). With HUP, any employee or student of an organization that has a Microsoft volume license is eligible to purc...

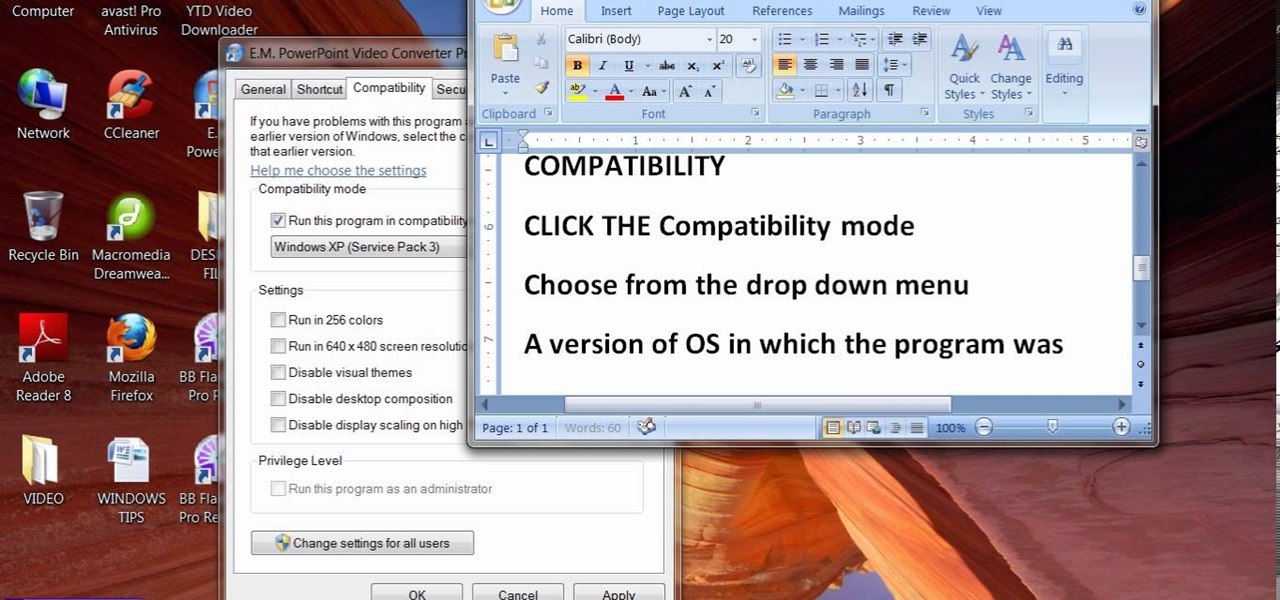
When people upgrade their windows few software don't run on new OS. How to fix the problem? Setting program compatibility solves the issue. Watch the video we made and submitted earlier in You tube.

In this video, we learn how to use Raw Therapee with Gimp. First, you need to go online to Raw Therapee, then download and install Raw Therapee. Once you have this, open it up and familiarize yourself with the layout of the software and where the different tools are at. Next, change your preferences and pick your settings throughout the different folders. Next, find GIMP through the program folders as your installation directory. Now, it will export your images to GIMP automatically. This way...

In this video tutorial, viewers learn how to play DVD movies on the computer for free. Usually, users will need to purchase expensive codes or plug-ins for a media player in order to play a DVD movie. This video introduces the VLC Media Player. This media player is able to play any DVD movie and is a free program. To download it, open your the Google website. Then search for the media player and select the first result. Then click on Download and install the program. This video will benefit h...

Check out this tutorial for a detailed tutorial for how to draw a rockstar type cartoon character using the program, Toon Boom Animate. These days, all animation is drawn on a computer and with this video, you can get started and join the digital revolution. This clip is well over an hour in length, so you will get everything you need to know here, for sure.

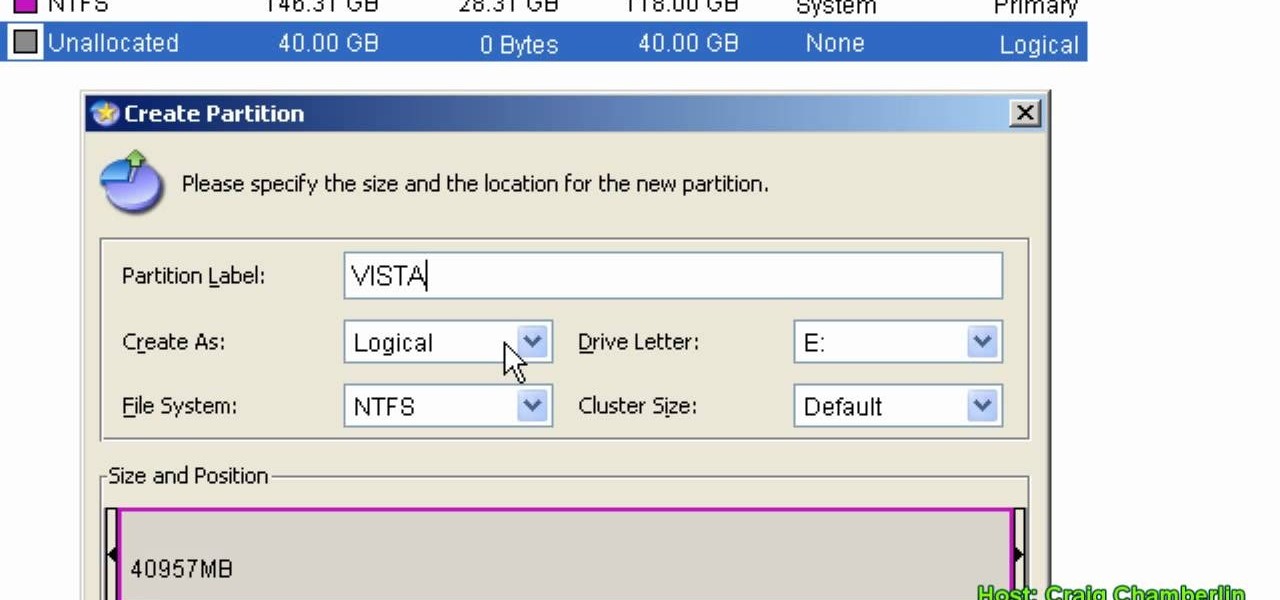
In this Computers & Programming video tutorial you will learn how to format a hard drive to boot a second operating system. First, do a Google search for EASEUS partition master, download and install it. Launch the program. Right click on the unallocated space on your hard drive and then click ‘create’. Now create a new partition for the new OS. Name it Vista, select ‘primary’ in the ‘create as’ window, choose ‘NTFS’ in the ‘file system’ window, select drive letter as ‘V...

Having downloadable files on your website is often an essential. It is an easy and fast way to share programs via the web and allow your visitors to experience software and files that you enjoy. In this tutorial, you will learn how to make a file downloadable for you website, so your visitors can easily download any file. This process is surprisingly straight forward and easy. You can follow this same process whether it is a text file, image, movie or music file. You will also learn how to tu...

This video shows us a tool that can be used to split and merge pdf files without having to buy any software.

In this video tutorial, viewers learn how to break up large files to easily send through email. Go to the website: and search "winrar". Download the program. Then double-click the file and follow the instructions to install it. Now right-click the file and select Add to Archive. Users will have an option to split the files into volume bytes. Then press OK wait for the program to compress the file into several parts. This video will benefit those viewers who...

In this how to video, you will learn how to make an RSS feed as an alarm clock. To do this, you can use the Microsoft speech program. Open the alarm batch file. Modify the Perl script so that it downloads the RSS feed from the Digg website. It will strip all the tags and html so only the text is left. From here, you run a script that converts the text to a wave file. From here, the alarm m3u will start. You can then run the command prompt to schedule the alarm time. Go to schedule tasks to ac...

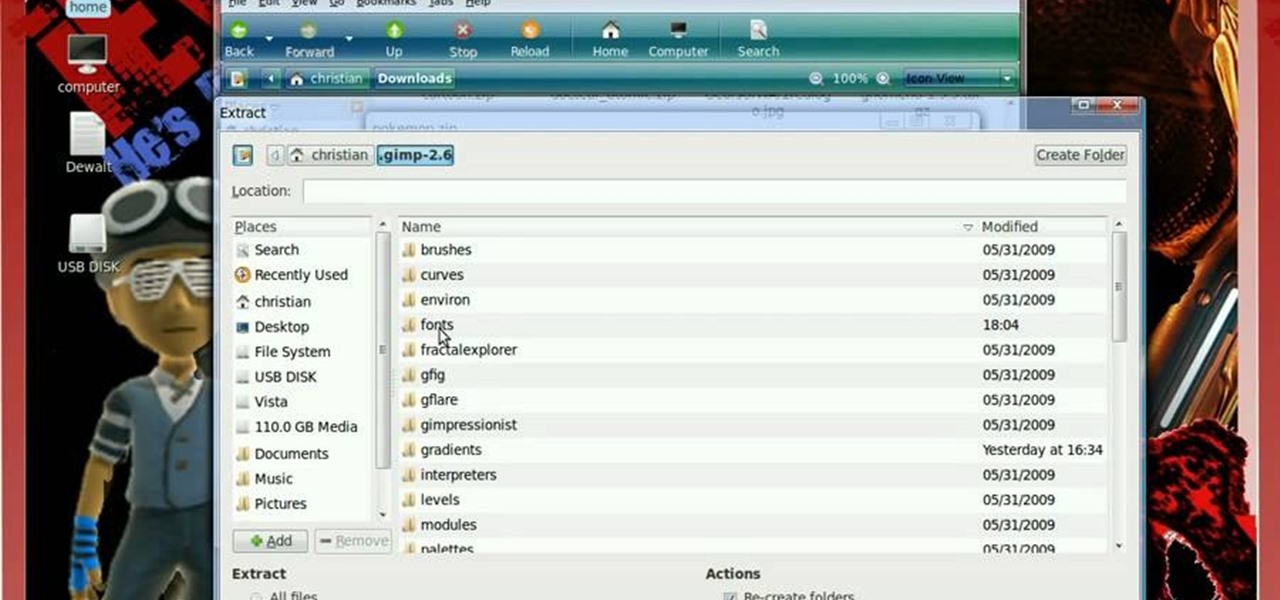
Linux is a fully functioning free operating system that you can download online. Just because you are using Linux Ubuntu doesn't mean your projects have to suffer or look less professional that those made on traditional operating systems like Windows or Mac OS X. In this tutorial, learn how to download and add fonts to the GIMP photo program on a Linux Ubuntu system.

This how to video shows you how to change the voice in the VoiceOver Utility program on a Mac. This will be useful if you want a voice that is more realistic or more understandable. First, open the program and choose the speech pane. On voices, click the drop down menu to choose which of the voices you want to use. At the side of this, you can change the rate, pitch, volume, and intonation. To change the voice settings with just the keyboard, press control option and command together. Use the...

This video tutorial shows you how to program your ESC for your RC vehicle. This is an important tutorial since this will help make your "remote control" vehicle be controlled by a remote. So sit back and enjoy!

Scanning is an awesome, fast way to transport a document into your computer. But, what if you want to edit it once you've scanned it? Most scanner programs will import your document as a read-only PDF or image file. With this tutorial, learn how to use the program ClaroRead on a Mac to scan your document directly into Microsoft Word for editing. This will save you a lot of time and a lot of annoying formatting and copy and pastes!

In this how-to video, you will learn how to change the font size with Microsoft Word 2007. First, open the program and type in a sentence or two. Now, move your cursor to where the font name is. To the right of this should be a drop down menu with numbers. These are the sizes of the font. Highlight the text. Now, click and change the number to change the size of the text. The larger the number, the bigger the font will become. This video shows you just how easy it is to change the font with t...

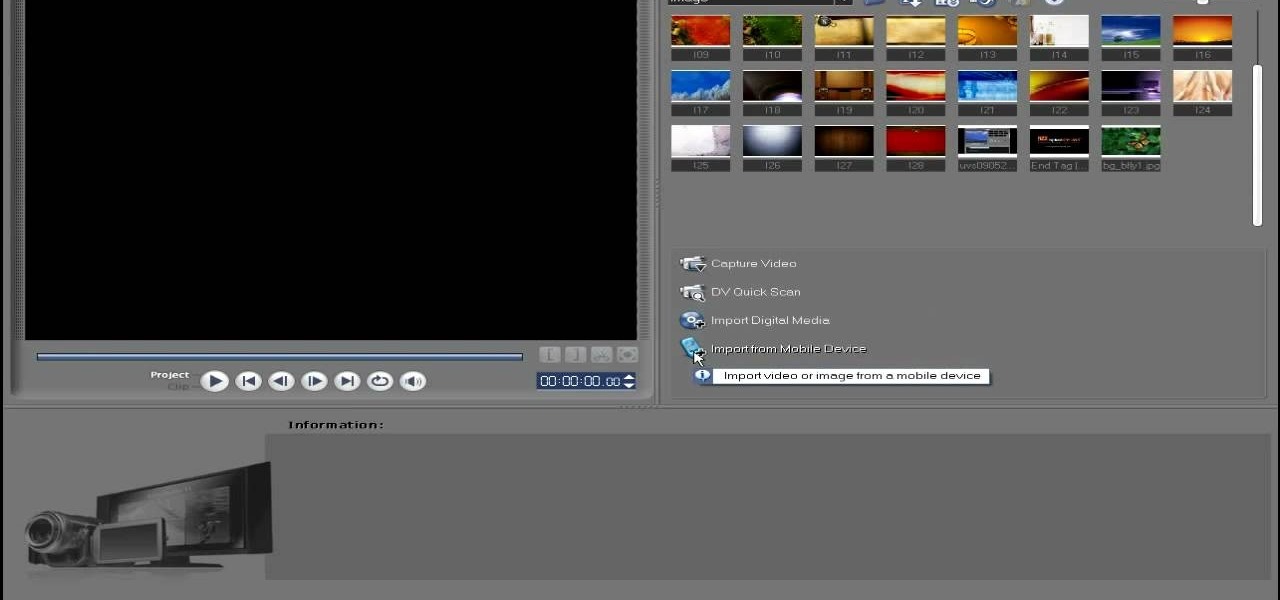
In this video tutorial, viewers learn how to import media from devices in Corel Video Studio. Begin by connecting your mobile device to the computer. It can be any device with a memory card or hard drive. Open the program and click on the Capture tab. Click on the option, Import from Mobile Device and select the device that you want. Select the file(s) that you wish to import and click OK. The program will then import the media to your selection window. This video will benefit those viewers w...

In this video tutorial, viewers learn how to uninstall the program on an Android phone. Begin by clicking on Settings and select Applications. Click on Manage applications. Now users will be revealed a list of all the applications that are installed on the phone. Simply scroll through the applications and select the unwanted application(s). Users will now see the information about the application, click on Uninstall. Now click OK and click OK again when the application is finished uninstallin...

Astrum Antivirus Pro is a rogue anti-spyware application and a clone of VirusTrigger and Antivirus Trigger. Astrum Antivirus Pro is often downloaded and installed by a Trojan or through browser security holes. Astrum Antivirus Pro may generate large numbers of popup adverts. Astrum Antivirus Pro will also display notifications of imaginary security risks in its attempts to get the user to purchase the full version. Astrum Antivirus Pro may run a fake system scanner and then display fake syste...

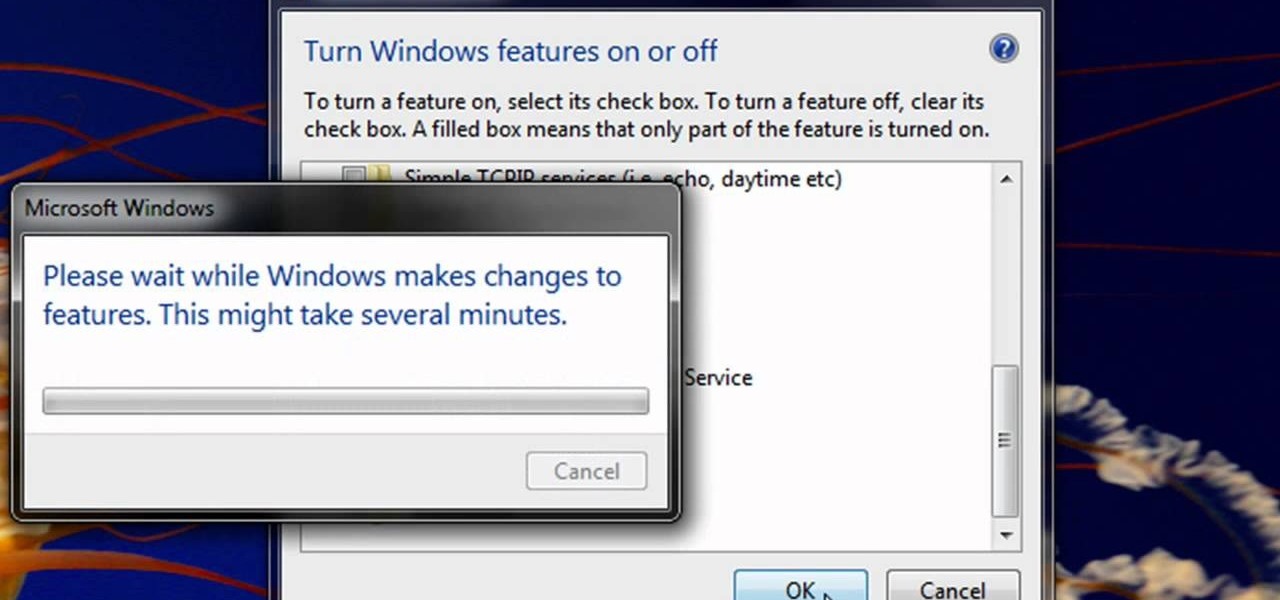
Enabling Telnet in Windows Vista is a little bit more difficult than its predecessors but it still can be done. This video will demonstrate exactly how to enable Telnet in Windows 7 and Vista.

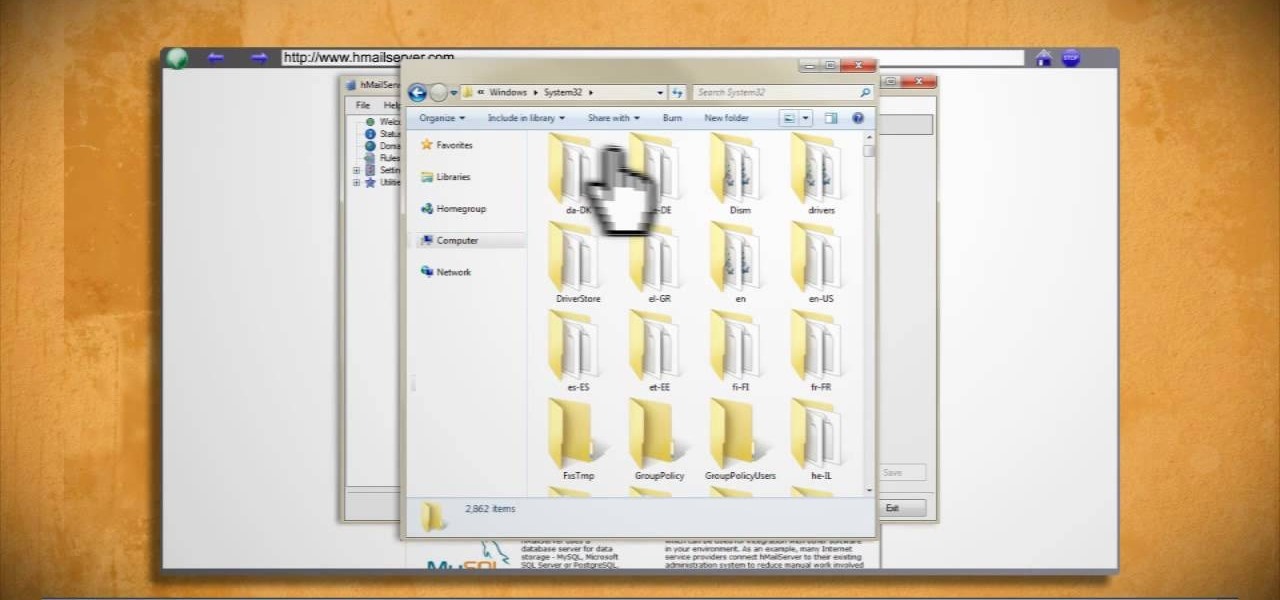
Learn how to make an e-mail server on your home computer to host your own web page and webmail service by following the steps outlined in this video tutorial. You will need a web server, an e-mail server, and a webmail interface. For the server, the most common program is WampServer, which you will need to download. Run through the installation process and grant the program access to your fire. Click on the new icon on your desktop and click Put Online and then Start All Services. This will g...

In this video from modernmom we learn exercises to reduce your breast size. You can't lose weight in your breast the personal trainer says. But when you want to lose weight, and you get into an exercise program that is consistent, you will begin to lose weight, and our bodies shed pounds all over, and because there is lots of fat in the breast tissue, you will notice they will get smaller. There's no one specific exercise though. But doing a walking program and watching calories will make you...