Normally, office supplies and food don't mix, but you can use a paper shredder to make fresh pasta in your very own home (...or office). In other words, you don't have to buy a bulky and expensive piece of equipment to make fresh pasta. If you already have a paper shredder, you can simply feed pasta dough through it for perfect tagliatelle noodle strips that will taste far better than anything you can buy at the store. Step 1: Clean Your Machine
Want to get even this Halloween? Want to scare somebody with nothing but a few lines of code? Here's how it can be done...
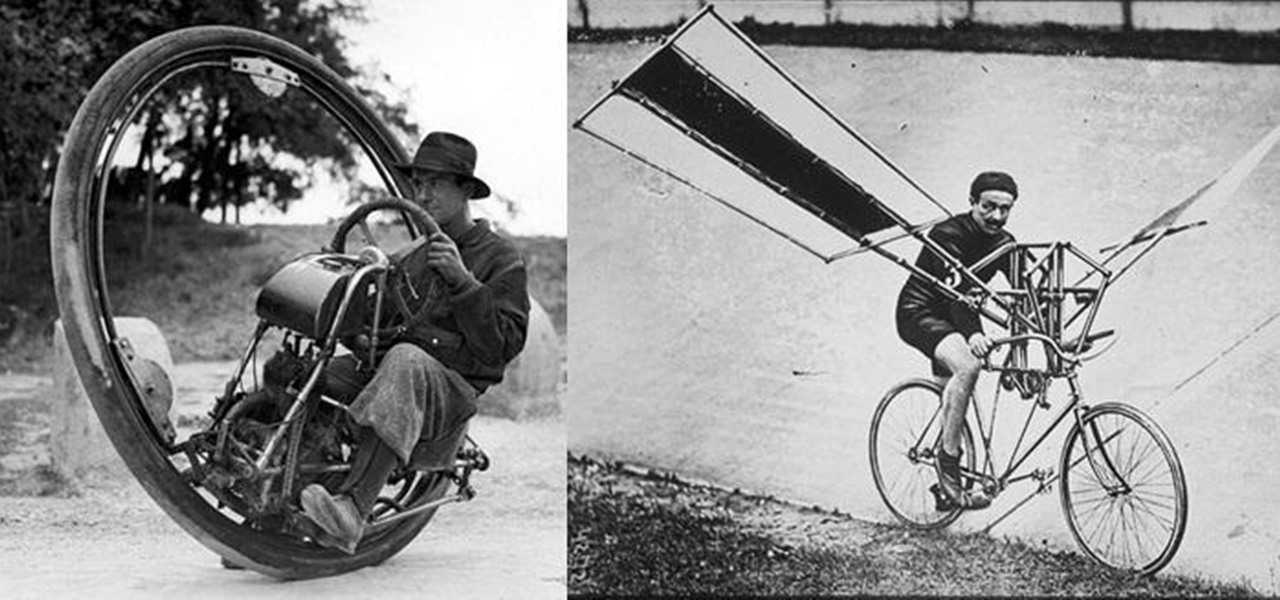
We don't spend much time thinking about bicycles today, do we? Sure, they're a "green" alternative to driving everywhere in cars, but the vast majority of America has dismissed them as simply being too much work, or more importantly—too slow. That wasn't always the case, though, I assure you!

First off, I would like to say two things. One, this is not for beginners; if you don't feel that you understand this how-to at all, do not try it. Second, never ever install random software or change settings if you do not trust the source.

In this tutorial, we learn how to make cotton candy with a cotton candy machine. First, you will want to take your choice of flavored sugar and pour it into the top of the cotton candy machine. Next, you will take your paper cone for cotton candy and place it in your hand. Turn on the machine on and when it's heated up and sprays out sugar strings, move your hand quickly around the machine and gather the cotton candy up with the cone! You can enjoy as soon as it's done and layer different fla...

Need a little help with your magic card skills? Check out this video tutorial to learn how to perform the "time machine" card trick.

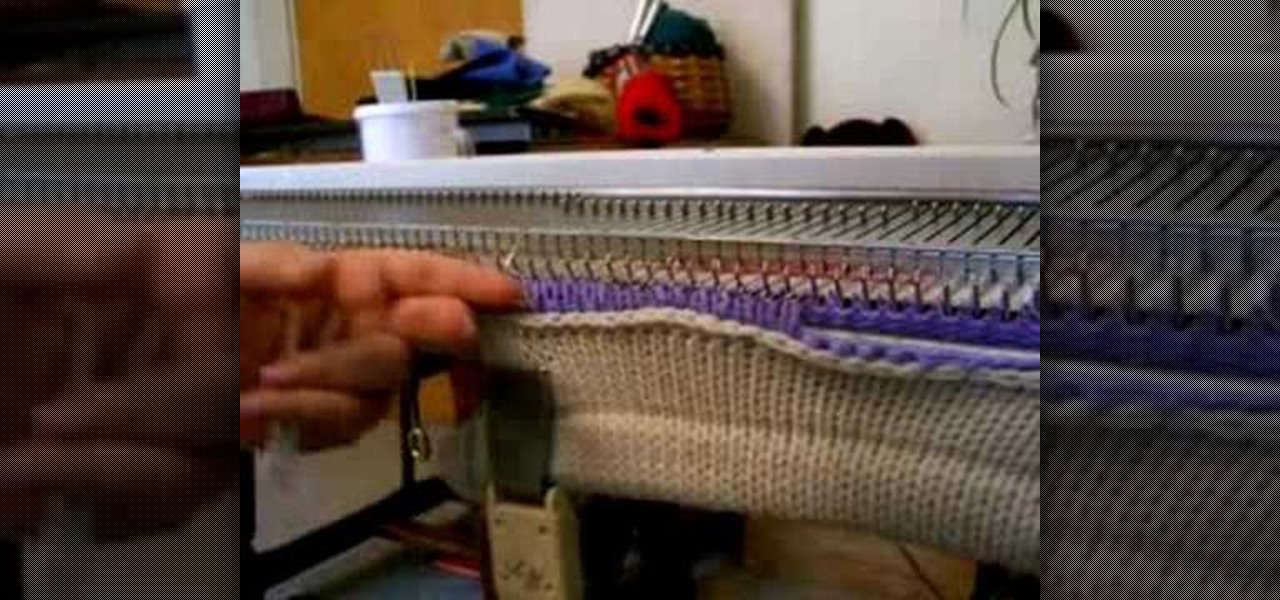
Watch this instructional knitting video to complete and open cast on with a knitting machine. Push your needles back into forward position and knit across one row. You will want to use clips and claw weights to keep your knit work straight. If you knit with a knitting machine, this is an essential trick for getting started with larger projects.

Watch this instructional knitting video to hang a rag hem on your knitting machine. Add weights to the inside of the knitted hem to keep your knit work straight. You will need a single pronged tool or a three pronged tool. If you knit with a knitting machine, this is an essential trick for getting started with larger projects.

If you knit with a knitting machine, a cone of yarn proves much more useful than a standard ball of yarn. This instructional knitting video demonstrates how an electric cone winder works. This little machine allows one to quickly wind a ball of yarn onto a cardboard cone.

There are a total of 242 stars in Super Mario Galaxy 2 on the Nintendo Wii — 120 normal stars, 120 green stars and 2 bonus stars. If you've already found all of the stars in Worlds 1, 2, 3 & 4, now it's time for World 5!

This instructional knitting video provides tips for making interesting patterns using a knitting machine. This is a demonstration of how to use a knitting machine to crochet cast on. This is one way to cleverly weave your yarn onto the knitting machine and begin the piece of knit work. You may want to reference written instructions in addition to watching this knitting video.

This instructional knitting video provides tips for making interesting patterns using a knitting machine. This is a demonstration of how to use a knitting machine to crochet a cast off. This is one way to cleverly remove your work from the knitting machine and complete the piece of knit work. You may want to reference written instructions in addition to watching this knitting video.

This instructional knitting video provides tips for making interesting patterns using a knitting machine. This is a demonstration of how to pick up and hang stitches. Use a three prong tool to attach one piece of knitting work to the knitting machine. Once you set the set the machine up, you can knit a wearable piece with an altering pattern.

This is a cool technique for machine knitters to use. It's a hand technique that converts quite easily to machine. Sew a phony seam when with a small knitting tool to alter pieces on a knitting machine.

Take a look at this instructional video and learn how to build your own miniature computer numerical control (CNC) machine. A CNC machine acts as a controller that reads G Code instructions for machine tools such as drills and printers. To perform this task, you'll need some geared motors you can find in old analog camcorders with optical zoom.

Using a sewing machine entails knowing how to thread it properly. This sewing how-to video demonstrates how to insert thread into a sewing machine. Follow the users instruction to properly insert the thread into your sewing machine.

Using a sewing machine entails knowing how to the tension knob properly. This sewing how-to video demonstrates how to properly adjust the tension knob on a vintage Kenmore sewing machine. The tension knob is located near the front of the sewing machine. It has a dial numbered from 1 to 9. The larger the number, the tighter the tension.

Using a sewing machine entails knowing how to insert a bobbin properly. This sewing how-to video demonstrates how to insert the bobbin into the feed dog of a vintage Kenmore sewing machine. The bobbin in the feed dog part of the sewing machine makes up the bottom of the thread needed for sewing.

In this video series, let our expert show you how to use the confusing hip abduction and hip adduction machines for thigh exercises. With Sheila Lindsey's help, you can start learning how to work your inner and outer thighs. She illustrates the various parts of the machines, and she gives you some tips for achieving the results that you are looking for. With her simple gym instruction, you can begin your thigh workout with just the right amount of expertise. So, watch and learn today!

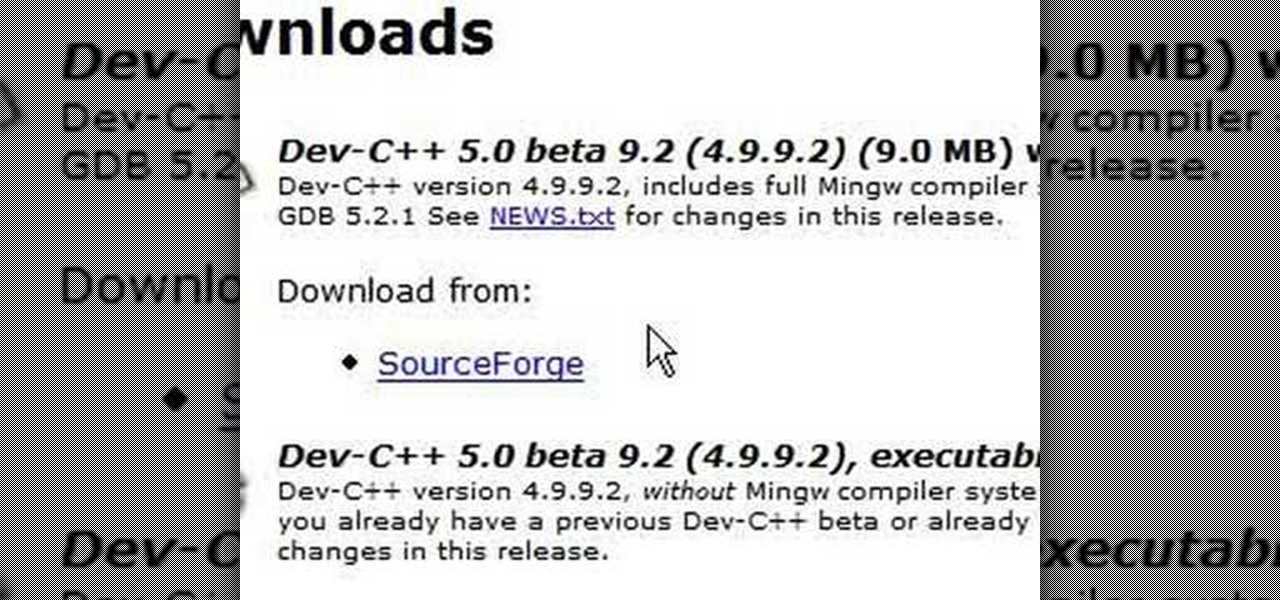
C++ is one the most powerful and fundamental languages commonly used to computer programming. If you've ever wanted to get started using, then please watch this video series. It's 29 parts will teach you everything you need to know about coding in this magnificent language, allowing you to create your own fairly full-featured computer programs. Honestly, if you have any questions about C++ at all, or want to learn it and don't think that you can because you've tried programming before and fai...

This is a video showing how to make a perfect latte at home. First the coffee is ground and then she pours some milk. The presenter says that 1/3 of the daily requirement of milk can be found in a latte. Once the coffee is ground it is brewed. She uses a lot of coffee so that it is richer. While the espresso is being made, the milk is steamed. The espresso should drip out like honey. The steamed milk is then poured over the coffee.

In my first installment in this series on professional hacking tools, we downloaded and installed Metasploit, the exploitation framework. Now, we will begin to explore the Metasploit Framework and initiate a tried and true hack.

Today's post is a small go-to guide for beginner programmers in Null Byte. With many of our community members picking up programming from our Community Bytes, it only makes sense to lay out a one-stop guide for your reference. Hopefully this guide will help you make an educated and thoughtful choice on what programming languages you want to learn, and how you want to learn said languages.

Paper or plastic is a thing of the past; both options are equally terrible for the environment. With this tutorial, learn how to turn your old bed sheets into funky grocery tote bags. You will be the envy of everyone at the store with these adorable, homemade bags.

Tech-savvy programmers and developers usually apply their unique talents exclusively to creating apps and websites — two high-paying and exciting pursuits that can open countless doors and opportunities in multiple fields.

Post-exploitation is often not quite as exciting as popping the initial shell, but it's a crucial phase for gathering data and further privilege escalation. Once a target is compromised, there's a lot of information to find and sift through. Luckily, there are tools available that can make the process easy. One such tool is Postenum.

Those of us who've taken the time to learn how to code are relatively well-suited for shakeups in the economy. Despite the recent and notable disruptions caused by the COVID-19 outbreak, demand for talented and trained programmers and developers is still high, and it will likely keep rising as companies in every industry adapt their business models to a more remote world.

Whether you're looking to add a substantial coding foundation to your hacking skill set or want to get a job in programming and development, knowing one or two programming languages just isn't going to cut it.

You've spent untold hours playing your favorite games. You know what you love. More importantly, you know what can be improved upon. The distance between vision and reality is not as far as you think. You just need a bit of training.

One of the greatest trends to emerge from this period of home isolation is the live concert broadcast from bedrooms and living rooms across the planet. Though public gatherings are on hold, you can still impact people with your music and mixes. In fact, it's helping many people get through this confusing time.

For anyone using open source information to conduct an investigation, a balance between powerful tools and privacy controls are a must. Buscador is a virtual machine packed full of useful OSINT tools and streamlined for online research. This program can easily be set up in VirtualBox, and once that's done, we'll walk you through some of the most useful tools included in it.

Smartglasses maker Epson remains the top gun in the drone market with its Moverio line of wearables, and the company is further elevating its offerings with its new Drone SoAR app for DJI drones.

Getting root is considered the Holy Grail in the world of Linux exploitation. Much like SYSTEM on Windows, the root account provides full administrative access to the operating system. Sometimes even a successful exploit will only give a low-level shell; In that case, a technique called privilege escalation can be used to gain access to more powerful accounts and completely own the system.

As Android bug bounty hunters and penetration testers, we need a properly configured environment to work in when testing exploits and looking for vulnerabilities. This could mean a virtual Android operating system or a dedicated network for capturing requests and performing man-in-the-middle attacks.

One of the most critical bugs to come out in the last five years was Shellshock, a vulnerability which allows attackers to execute arbitrary code via the Unix Bash shell remotely. This vulnerability has been around for a while now, but due to the ubiquity of Unix machines connected to the web, Shellshock is still a very real threat, especially for unpatched systems.

Command injection is a technique used by hackers to execute system commands on a server, usually via a web application or some kind of GUI. This can happen when an application provides some sort of functionality to the user involving the use of system commands. When the input is not properly sanitized, commands not originally intended to be run are allowed to be executed.

While mobile gaming, in the 10 years since the App Store launched, has matured to console-level quality, premium augmented reality games built with ARKit (or ARCore) have been scarce.

The easiest way around a security policy is to find users who don't follow it. The Have I Been Pwned database identifies accounts with information breached by major third parties like Yahoo and LinkedIn. With Maltego, hackers can locate breached accounts created using company email addresses, potentially giving attackers access to a company account if the employee reuses a compromised password.

Microsoft's Monday keynote introduced the fourth generation of the company's Kinect sensor during Build 2018 in Seattle.

With the heavily anticipated installment of the God of War game series arriving on April 20, PlayStation has taken the opportunity to make its first foray into mobile augmented reality with a companion app.