
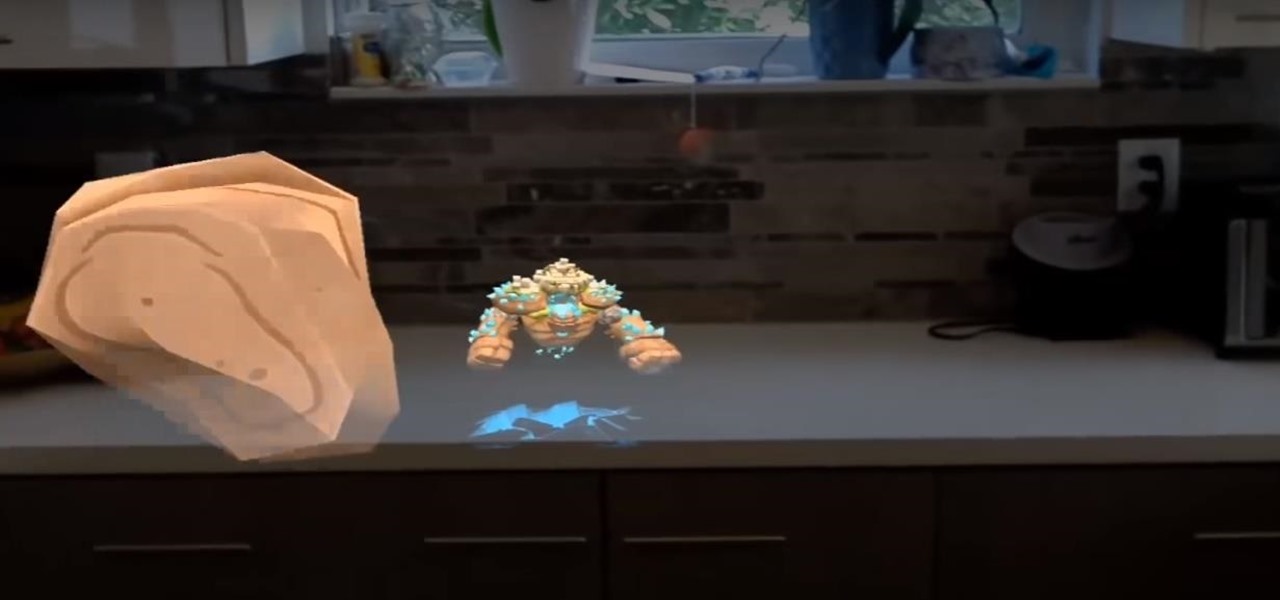
News: Microsoft Exec Confirms HoloLens 2 Set to Ship in September
Microsoft has unveiled practically every detail of the HoloLens 2 except for when eager developers and enterprise customers can expect to receive the device.


Microsoft has unveiled practically every detail of the HoloLens 2 except for when eager developers and enterprise customers can expect to receive the device.

Despite the rise of music streaming, the experience of immersing oneself in the artwork and lyrics of old school albums is alive again, as sales of vinyl records and CDs have outpaced digital downloads for the first time since 2011. Now, the latest album from Amsterdam-based Necessary Explosion evolves this experience through augmented reality.

Kali Linux is established as the go-to operating system for penetration testing, but in its default configuration, it's less than ideal for regular desktop use. While in many scenarios, a live boot or virtual environment can resolve these issues, in some situations, a full installation is better. A few simple changes can be made to a Kali Linux desktop to make it safer to use in this environment.
Apple announced upcoming changes today to prevent third-party tracking of users and prevent autoplay, on Safari. Safari will prevent the recording (by anyone other than Apple) of users' browsing behavior, and by doing so prevent advertisers from targeting ads based on individuals' history.

Google just announced that it will be bringing the Google Assistant—previously an exclusive feature on Pixel phones—to many more devices in the coming days. The only requirement they're giving is that the phone must be running either Android Marshmallow or Android Nougat, so according to the most recent Android distribution numbers, that's roughly 32% of all existing phones and tablets.
Serving as the primary tool of distribution for many websites, social media is how most of us catch up what's going on around the world. While there is a bunch of clickbait going around on Facebook and Twitter, there are plenty of genuinely interesting articles being shared.

With the release of the M8, HTC decided to begin publishing some of its exclusive apps to the Google Play Store. While most of these apps aren't available for download unless you own an HTC device, this practice made it possible for the Taiwanese smartphone manufacturer to issue updates to its users independently of carrier-modified firmware upgrades.

Get rid of your water-wasting sprinkler system— but not entirely! Keep your landscape and garden maintained by converting those sprinklers into eco- and pocket-friendly drip irrigation. In this how-to video, Paula Mohadjer from the Cascade Water Alliance explains how you can easily convert your sprinklers into a drip irrigation system.
Consider a normal and ideal height for a girl in 5feet 8inches in height. The book of Andrew Loomis is a good guide for drawing realistic human figures. It explains the body proportions, techniques, drawing the parts, human movements, and poses of the body.

In this article, we will build a parallel password cracker using the techniques explained in the previous part. As SHA-512 is the digest function that Kali (and most modern Linux distributions) use to store our passwords, we will make a SHA-512 password cracker.

Welcome back, my rookie hackers! In my ongoing attempts to familiarize aspiring hackers with Linux (nearly all hacking is done with Linux, and here's why every hacker should know and use it), I want to address a rather obscure, but powerful process. There is one super process that is called inetd or xinetd or rlinetd. I know, I know... that's confusing, but bear with me.

Welcome back, my aspiring hackers! Although this article may have been better placed first in this series, I doubt that anyone would have read it when just starting out studying Linux. Now, that you are well into your Linux studies and have some familiarity with how it operates, I'd like to take this moment to explain the philosophy around the Linux operating system.

Welcome back, my nascent hackers! Like anything in life, there are multiple ways of getting a hack done. In fact, good hackers usually have many tricks up their sleeve to hack into a system. If they didn't, they would not usually be successful. No hack works on every system and no hack works all of the time.

Probably SSH is not as clean and fast as other useful tools like netcat, but it has some features which are very useful, and when you'll need them, here's how to behave with that huge amount of computers all over your house.

Welcome back, my budding hackers! In my continuing effort to build your basic Linux skills for hacking, I want to show you how to build a secure "tunnel" to MySQL.

Welcome back, my aspiring hackers! One of those areas of Linux that Windows users invariably struggle with is the concept of "mounting" devices and drives. In the Windows world, drives and devices are automatically "mounted" without any user effort or knowledge. Well, maybe a bit of knowledge. Most Windows users know to unmount their flash drive before removing it, but they usually think of it as "ejecting" it.

Welcome back, my fellow hackerians! Today we'll be hacking Facebook profiles on your local network. You may think, "How is this useful, nobody but me is using my network." Well, you can use this on other Wi-Fi networks that are available for free (like at Starbucks) and crack their precious Facebook profile!

One of the best parts about cooking is feeling the cold, hard steel of your cooking knife in your hand. The sleek skillful edge doesn't stand a change against any delicacy, unless it's dull. A dull knife takes the fun out of cooking and is actually more dangerous than a sharp knife, so take a moment to sharpen and care for your tools.

In this tutorial series Mike Lively shows how to convert Wordpress into the Adobe Flex 3 application Flexpress.

For those about to rock, Live Nation salutes you, now with augmented reality. This week, at the Cannes Lions Advertising Festival of Creativity in France, the live entertainment giant unveiled a suite of AR experiences that music festivals and their sponsors will be able to deploy in their mobile apps to engage attendees.

After one of Britain's "Brothers Bling" bought Blippar out of bankruptcy, the mobile augmented reality company is getting back to business with the addition of web-based AR capabilities to its platform.

Kali Linux is probably the most well-known hacking distribution among penetration testers. However, there are alternative distros which offer versatility and advanced package management systems that are absolutely worth considering.

Google's ARCore team is staying busy, as evidenced by yet another update of its augmented reality toolkit.

The future of augmented reality isn't on your smartphone or face, it's in the everyday items all around us. At least that's the belief of Gordon Meyer, the vice president of marketing at New York-based startup Lampix.

Enterprise augmented reality software provider Upskill has raised $17.2 million in its latest round of funding, led by new investors Cisco and Accenture.

As augmented reality gains popularity, the demand for delivering related services and generating content increases. This is demonstrated by a pair of investments from the past week, one in the expansion of a technology lab and another in the form of seed funding for a content studio.

France's Groupe PSA (formerly known as PSA Peugeot Citroën) — one of the world's top-10 carmakers — aggressively seeks to take a lead in the rollout of the industry 's first driverless cars, as it becomes the first mainstream carmaker to announce it will launch a Level 3 self-drive vehicle launch by 2020.

DAQRI, a company mostly known for its odd but fun-looking industrial Smart Helmet, unveiled their new Smart Glasses product at CES 2017. Their smartglasses look like a strange attempt to answer the Microsoft HoloLens, and the price tag of $4,995 for the developer's edition reinforces that notion.
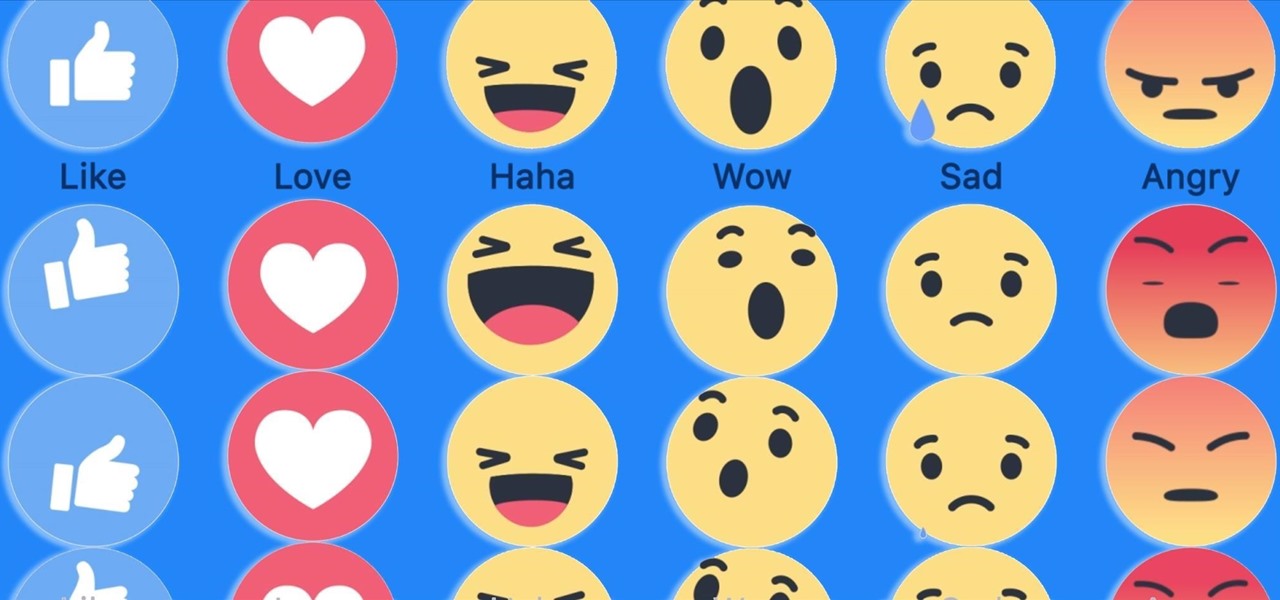
Have you ever run across a Facebook post that you don't necessarily want to "Like," but you're not really passionate enough about to bother stringing together a couple words for a comment? Well, you're in luck, as Facebook added five new "Reactions" that let you do more than just like a post, and they're now live for everyone.

In many programs on Linux, you'll come across programs which allow you to specify additional arguments instead of just simply running the program by itself. If you've used the Kali distribution, I'm more than certain you'll have come across these with the command line tools, else if you have been following these tutorials, we have already come across three tools which also use the same technique, i.e. gcc, gdb and wc. How do we do this with C? Let's find out.

Surely you're aware of the Sony hacking scandal by now (here's a quick primer if you're not), as well as the multi-billion dollar company initially bowing to threats by canceling the Christmas release of the The Interview, the film at the center of the whole debacle.

With over 2 million uploaded videos and over 28 million people who had talked about it online by the end of August, the ALS Ice Bucket Challenge was the most viral social media event of 2014. Its popularity provided the ALS Association with $115 million in donations to date, with everyone from students to veterans to celebrities contributing.

How, you ask? They did it without requiring a goofy-looking face-computer. I know what you're thinking, "Without headgear, how is it a Glass killer?" It's because it does what Glass was meant to do: keep you connected while on-the-go, without constantly staring at your phone.

In this video tutorial, viewers learn how to calculate the standard deviation of a data set. The standard deviation of a statistical population, a data set, or a probability distribution is the square root of its variance. To calculate the standard deviation, users will need to follow these steps. 1) Find the mean of the data. 2) Subtract the mean from each data point. 3) Square each of the values you got in step 2. 4) Then find the mean of the values you get from step 3. 5) Finally, square r...

When it comes to the athletic footwear retail game, it's just not enough to just sell shoes anymore.

While some widely praised immersive computing initiatives at Google are shutting down, over at Epic Games things are just ramping up, and it involves quite a bit of cash available to indie augmented reality developers and startups alike.
As it prepares to ship its first product by the end of the summer, Magic Leap has managed to impress yet another high-profile investor in telecommunications giant AT&T.

Upon Google's release of ARCore in February, the platform wasn't only playing catch-up with Apple and ARKit in terms of downloads, but it also lagged in capabilities, as Apple already had vertical surface recognition and image recognition on the way with ARKit 1.5 for a March release.

The internet is constantly under siege by bots searching for vulnerabilities to attack and exploit. While conventional wisdom is to prevent these attacks, there are ways to deliberately lure hackers into a trap in order to spy on them, study their behavior, and capture samples of malware. In this tutorial, we'll be creating a Cowrie honeypot, an alluring target to attract and trap hackers.
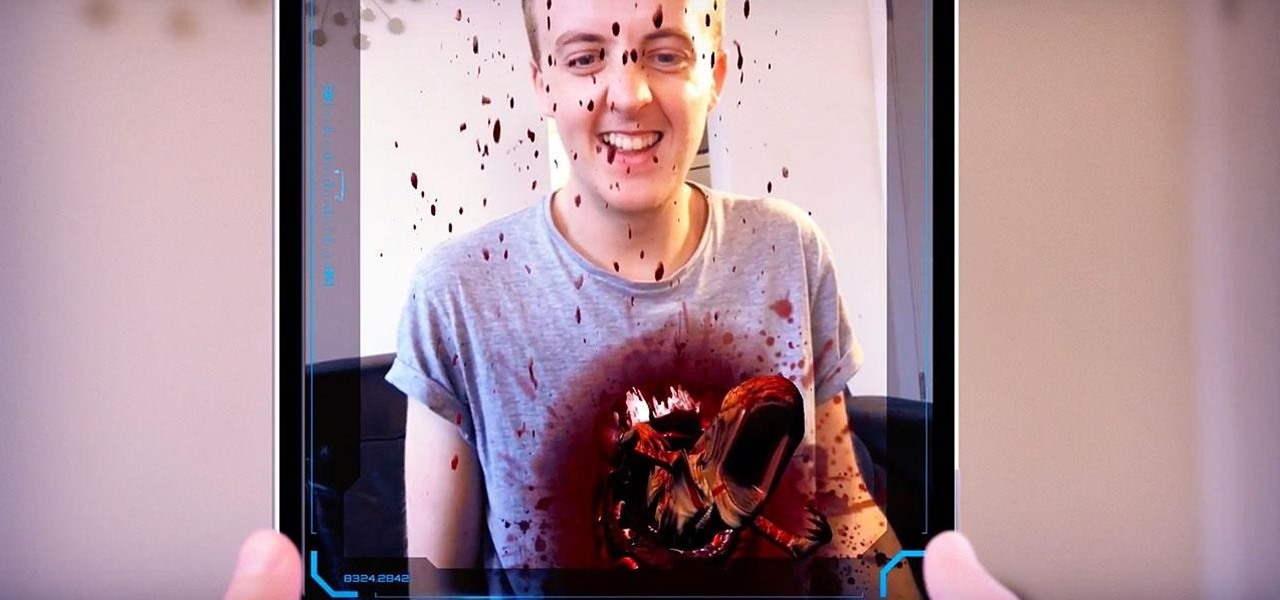
The latest installment in the Alien movie franchise, Alien: Covenant, came out many months ago, and the fan day dedicated to the franchise, Alien Day, April 26, is long past. But for many Alien fans, Alien Day is every day. For those loyal members of the xenomorph-worshipping tribe, a new augmented reality-powered book has arrived to serve their science fiction needs until the next film is released.