Apple released the first developer beta for iOS 14.3 on Thursday, Nov. 12, only to pull the update back, push it back out, and finally release it for real. An afternoon marred by Apple server issues spanning macOS Big Sur downloads to iMessage and Apple Pay could have been part of the issue. The new update for iPhone adds ProRAW support for iPhone 12 Pro and iPhone 12 Pro Max.

Who here binges TV on a regular basis? I know I do. Never before have we had so many options for watching our favorite shows, especially when you consider how easy it is to stream from anywhere on a mobile device. But sometimes, all that choice gets a little overwhelming. What services are really worth the money? Where should you be investing your Friday-night binges?

It's always a big deal when the company that makes Android releases a new phone. Google's Pixel series has made a name for itself in three short years behind its camera prowess, but now it's time to start competing with the major players. That said, Google should like how their Pixel 4 and 4 XL stack up against the iPhones and Galaxies of the world.

With a cheap computer, smaller than the Raspberry Pi, an attacker can create a remote hacking device. The device can be attached to a target router without anyone's knowledge and enable the hacker to perform a variety of network-based attacks from anywhere in the world.

Silence spreads over these mountains like nothing I've ever felt. If I didn't have Moby blasting in my earphones, there'd probably be no other sounds around. Well, except for someone, Phil probably, murmuring in a nearby tent just low enough to make his words indiscernible.

Your social security number, credit card information, and medical history can fall into the wrong hands if you're not careful about how and where you share your data online. If you really care about your data, there are tools and techniques you can utilize to protect yourself from cyberstalkers, advertisers, and hackers in a time when digital lives are a high commodity.

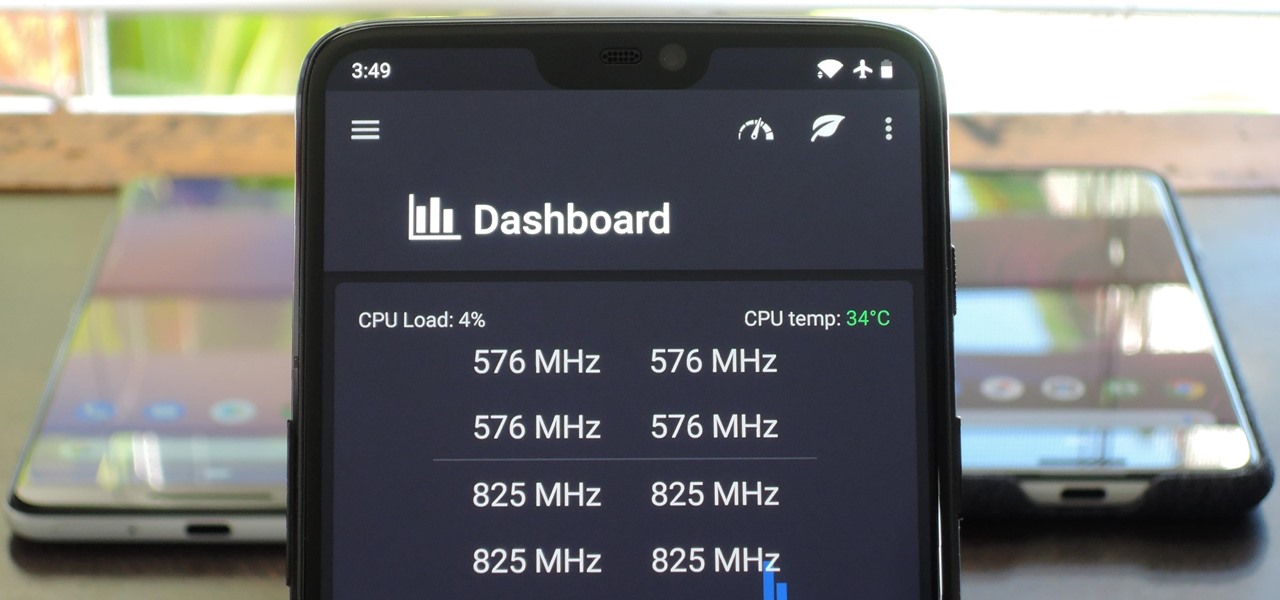
You can mod every aspect of your phone's software with root, but if you want to make changes at the hardware level, you'll need a custom kernel. If you've looked into custom kernels before, one name undoubtedly kept coming up: ElementalX. It's easily the best custom kernel out there, and the reason for that is its awesome developer, flar2, aka Aaron Segaert.

Smartphones and laptops are constantly sending Wi-Fi radio signals, and many of these signals can be used to track us. In this guide, we'll program a cheap IoT device in Arduino to create hundreds of fake networks with common names; This will cause nearby devices to reveal their real trackable MAC address, and it can even let an attacker take over the phone's data connection with no warning.

Windows 10 and macOS have poor reputations when it comes to customer privacy and user policies. Our hacking Windows 10 and hacking macOS articles might make it seem like a reasonably secure operating system doesn't exist. But I'm here to tell you that there is a viable alternative that could provide some sense of security and trust.

With an ordinary birthday card, we can introduce a physical device which contains malicious files into someone's home and deceive them into inserting the device into a computer.

OpenBSD implements security in its development in a way that no other operating system on the planet does. Learning to use the Unix-like operating system can help a hacker understand secure development, create better servers, and improve their understanding of the BSD operating system. Using VirtualBox, the OS can be installed within a host to create a full-featured test environment.

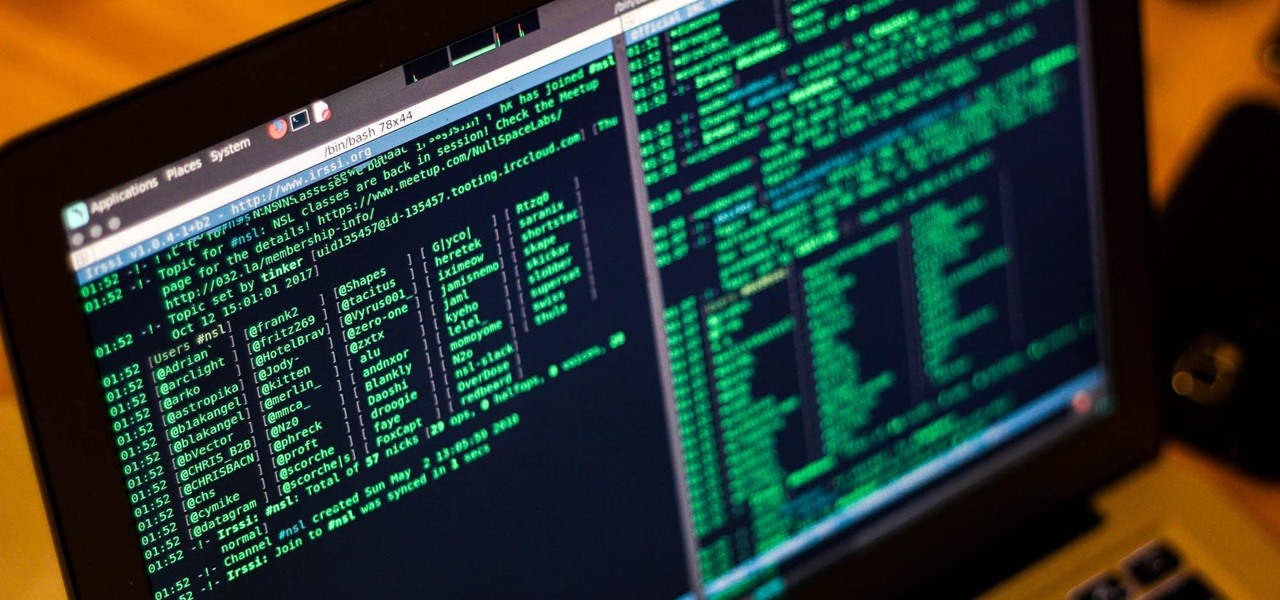
Internet Relay Chat, or IRC, is one of the most popular chat protocols on the internet. The technology can be connected to the Tor network to create an anonymous and secure chatroom — without the use of public IP addresses.

On July 20, 1969, humans set foot on the moon for the first time. But some say our microbes beat us there. With the Space Age came new questions about microscopic invaders from outer space and concern about where we are leaving our microbial footprints. The questions are even more relevant today.

Hi, everyone! Recently, I've been working on a pretty interesting and foolish project I had in mind, and here I'm bringing to all of you my findings. This guide's main aim is to document the process of building an Android kernel, specifically a CyanogenMod kernel and ROM, and modifying the kernel configuration to add special features, in this case, wireless adapter Alfa AWUS036H support, one of the most famous among Null Byters.

One of the best things about Christopher Nolan's Batman trilogy is how realistic he makes the caped crusader feel. Unlike the Joel Schumacher or even the Tim Burton versions, Nolan's world seems grounded in some level of scientific fact. But just how close is science to actually being able to replicate some of the Dark Knight's gadgetry?

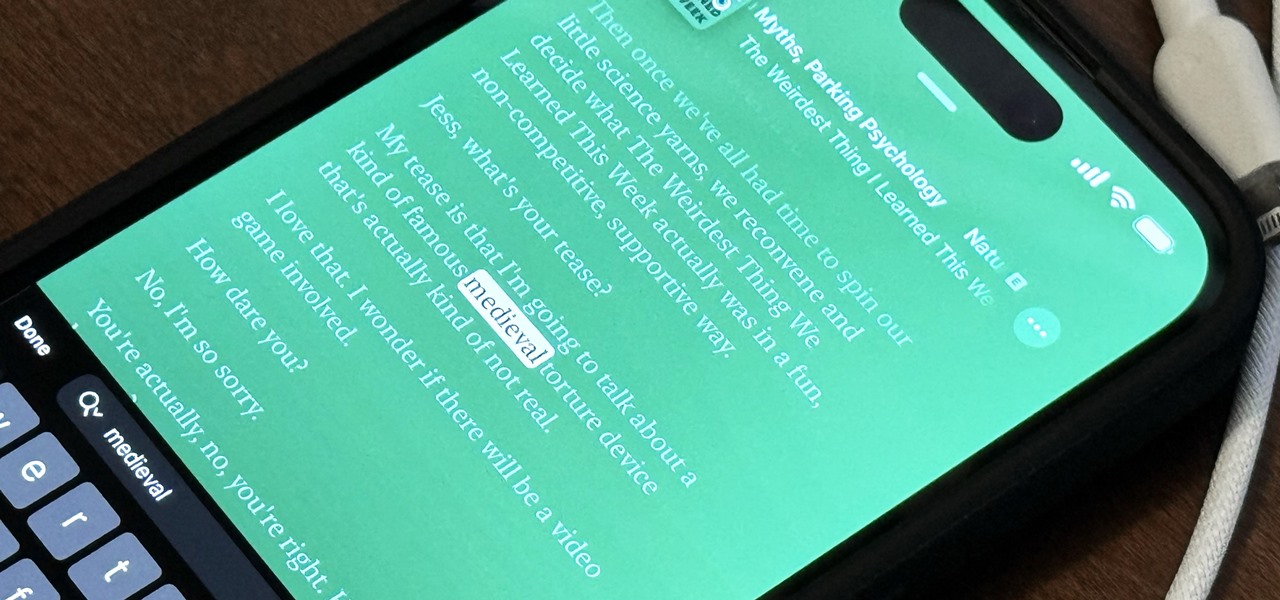
The last iOS software update was a modest one, but iOS 17.4 has a lot more for your iPhone, including changes to emoji, Podcasts, security, Safari, widgets, Apple Cash, CarPlay, and more.

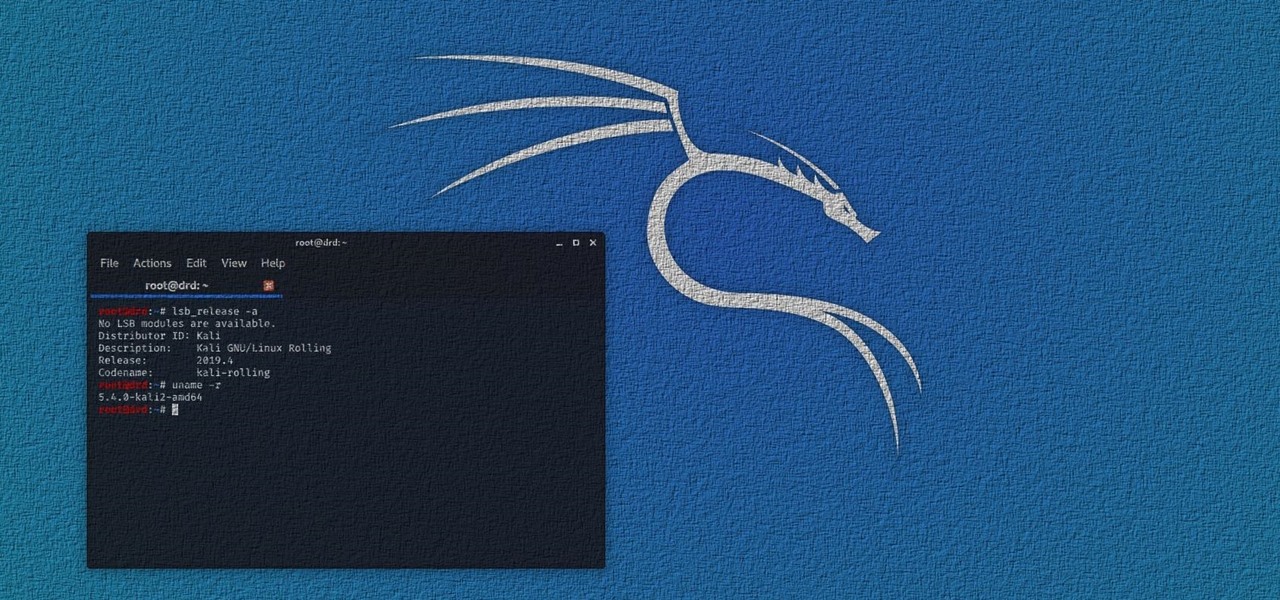
Kali Linux is the go-to Linux distribution for penetration testing and ethical hacking. Still, it's not recommended for day-to-day use, such as responding to emails, playing games, or checking Facebook. That's why it's better to run your Kali Linux system from a bootable USB drive.

The year 2020 was a pivotal span of time during which the word "virtual" took on a brand new meaning. Instead of referring to VR or augmented reality, the term was hijacked to describe meeting across long distances through a variety of software tools, most often through video.

Kali Linux has come a long way since its BackTrack days, and it's still widely considered the ultimate Linux distribution for penetration testing. The system has undergone quite the transformation since its old days and includes an updated look, improved performance, and some significant changes to how it's used.

If we were to assign a theme for the 2019 edition of the Next Reality 30 (NR30), it might be something along the lines of, "What have you done for me lately?"

Rooting. As an Android user, I'm sure you've heard the word once or twice. According to Kaspersky, 7.6% of all Android users root — but for the 92.4% who don't, we wanted to talk to you.

The PatchDeform modifier in 3ds Max deforms an object based on the contours of a patch object. This modifier works similarly to the PathDeform modifier, but uses a quad-based patch object instead of a spline shape or NURBS curve path. Patch Deform is a great tool for mapping geometry on a surface or the distribution of component on a surface in 3ds Max. The only catch is that the distribution geometry has to come from a surface originally made as a Patch. The surface cannot come from a set of...

That is right. I was just named President of Film Division at Ubroadcast Entertainment to launch a new distribution and production arm for the publically traded corporation.

When creating video for broadcast or distribution it is important to make sure that the color values meet requirements. Learn how to use the Color Limiter Effect to insure that your color limits fall within the required range. Use the Safe Color Limiter Effect in Avid.

SQL Server Reporting Services allows you to design and deploy nicely formatted and interactive reports representative of your data. Suitable for print or online distribution, these reports and it allows you to get professional results very quickly. This video demonstrates how to set up Reporting Services and the Business Intelligence Development Studio to build reports using the wizards and design. Use SQL Server Reporting Services.

James Stentiford talks you through the basics of riding a snowboard on deep snow in this how-to video. No need to change postures or weight distribution in powder, because you'll lose power and direction. Watch this video snowboarding tutorial and learn how to ride powder snow. Ride powder on a snowboard.

Learn how to download and install a Java distribution and the Java runtime environment using EasyEclipse. Install Java and Eclipse with Easy Eclipse.

Create and customize players using single title and multi-title template options. This tutorial also covers the basics of player distribution. Create players on Brightcove.

Set Lighting Technician's Handbook, Third Edition: Film Lighting Equipment, Practice, and Electrical Distribution by Harry Box

The title says it all. The worlds best skater, Tony Hawk, teaching you how to do the most basic and important skating trick: the ollie. The most important tricks you are going to learn in skating are ollies. The ollie is the act of jumping up using only your feet and the bringing the board up with you without grabbing it. The key elements of the ollie are timing, timing, timing, timing, timing… and your weight distribution and foot placement. Kris Markovich also helps out Tony in this video H...

Indie developers and their games have enjoyed massive success distributing through Steam, notably Zeboyd Games and Carpe Fulgar. While that bodes well for the future of indies on the platform, Steam has to devote a lot of front-page real estate to AAA games and thus can't promote small indies as well as a dedicated indie game distribution service could. IndieCity out of the UK seems like it could be that, but today a consortium of three German game companies launched their attempt at beating ...
Recently, I decided to install Kali 2016 as dual boot on my laptop. Everything install perfectly up until the installer gave me the option to set up the package distribution mirror. No matter what setting I provided, no mirror would set up correctly. I was forced to continue the install without setting up the mirror. If you do not know what this means, I will explain it. Basically, you will not be able to update or install any tools onto your Kali distribution.

Devil2005 has created a video on compiling and configuring dhcp daemon, or dhcpd, from source. He's using the Fedora 9 distribution of Linux for the video, but the lessons learned should be applicable to other distros. For that matter, even if you are not interested in installing dhcp in this way it's still a good lesson on how to download and compile various applications from source. Compile and configure dhcpd from source in Fedora 9.

Digital distribution games are already firmly established on the PC, and they've infiltrated every present and next-gen console to some degree. Whether you like to play DOS, AAA, PC or indie games, there's a way to purchase most of them without leaving the comfort and warmth of your couch or desk.

http://www.volusion.com/search-engine... - In this episode, Matt Winn discusses some great tips to boost your SEO using new content. If you have keywords you are interested on ranking for but have no content; creating landing pages specifically for these target keywords and optimizing them in a very natural way, will help you increase your SEO visibility. Create content that is useful for your viewers so that they can help you in the distribution and promotion of your pages. Don't forget to c...

Welcome, everyone! While Linux distributions are almost always used for exploits, security, pentesting and other stuff covered in Null Byte, knowing the Windows Command Line (or Command Prompt) is a useful skill that can help you in various ways, such as using exploit programs made for Windows or using the command line on someone else's Windows computer.

We have long admired the imaginative energy of IndyMogul. A new generation of filmmakers empowered by affordable filmmaking technology and free distribution.

As many of you Null Byters may know, I was planning on writing this article a week or two ago. Better late than never! So, let's get right to it then—choosing the right Linux distro for your needs.

We love you. Yes, you, esteemed reader. Your attention is what keeps Indie Games Ichiban World going, and we'd like to thank you for that, every single week. How? With $10!