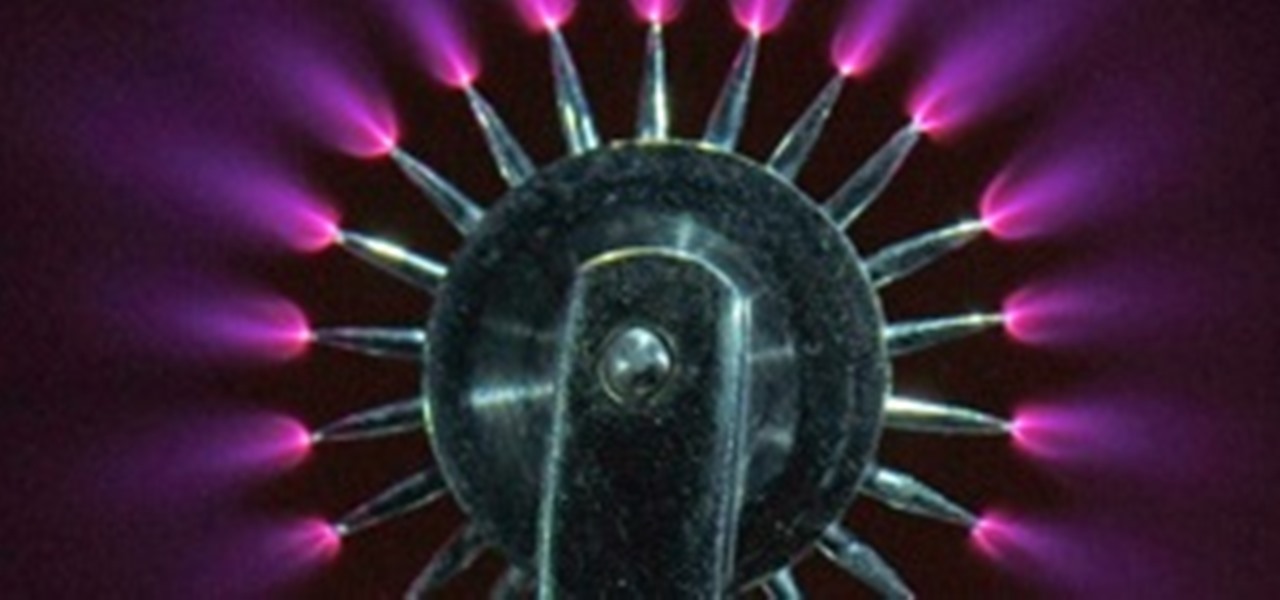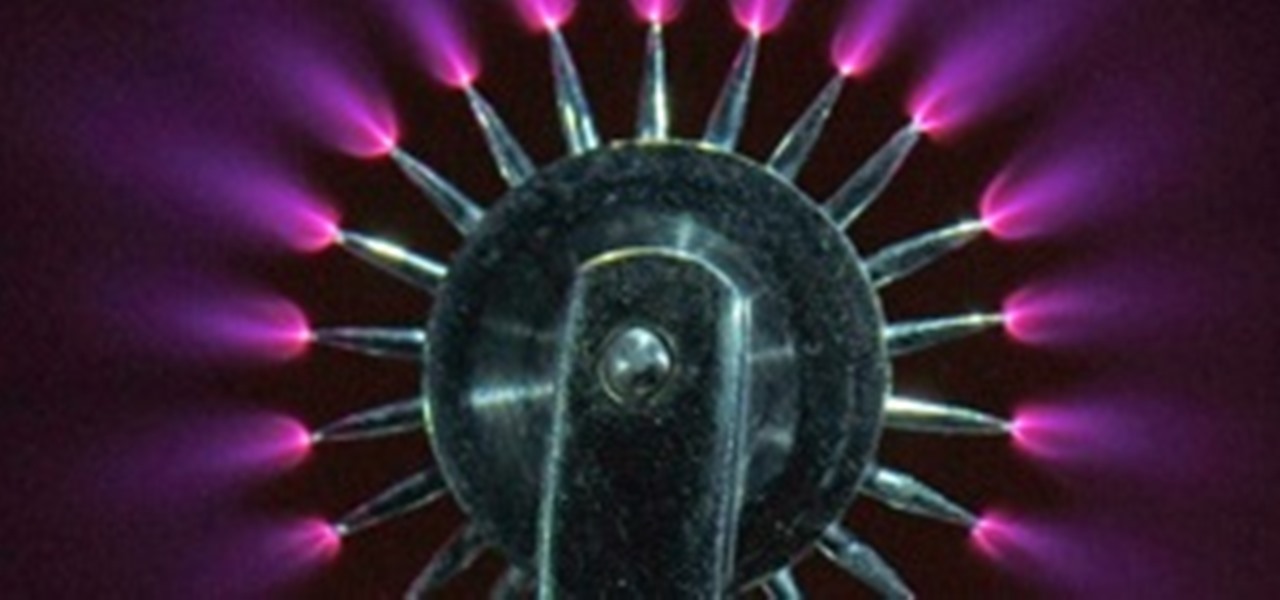
In this article, I'll show you how to build a simplistic circuit to generate negative ions. Negative ions have been known to contribute to fresher air, happier mood, and general health benefits. However, they also look amazing in the dark (check out the photos below, purple plasma is amazing!). And if all else fails, they make a cool nightlight. If you've ever been around a Tesla coil, cathode ray tube TV or sometimes even on a trampoline, you've probably noticed that smell; the smell of "sta...

How to use Asci Generator software to turn pictures into images made of Ascii text. Turn pictures into text with ASCI Generator.

In this series, I'll be exploring electromagnetic weapons, how to build them, their function and application to the future, and the amazing possibilities electromagnetism has to offer. First, the electromagnetic pulse generator, or EMP. You've probably heard of these before, and their devastating effects on electronics. A simple EMP consists of a capacitor, transformer, trigger, and coil of copper wire. This, when triggered, would produce an intense magnetic field for a brief period, similar ...

Spam is everywhere and Facebook is no exception. In fact, spammers are constantly stepping up their game by tricking unsuspecting Facebook users to participate in quizzes, games, apps, or "new features" that are actually dangerous computer viruses, spyware, or other trojan horses in disguise. Their attempts even trick people into unknowingly becoming spammers themselves.

Both on and off the set, the Gaffer or Chief Lighting Technician is one of the most important positions around. Though the average movie goer most likely has no idea the job even exists, they probably don't know what 99% of the other crew is/does either.
In terms of internet, faster = better. We all want faster internet, but how exactly do you get a fast wireless connection? Believe it or not, the answer is quite simple.

In my Wireshark article, we talked a little bit about packet sniffing, but we focused more on the underlying protocols and models. Now, I'd like to dive right back into Wireshark and start stealing packets.

In this article, I'll show you how to make a simple touch-triggered switch. This is very useful for various electronic projects, from a simple bedside light to a flat panel touch keyboard. The circuit can vary in switching power depending on the transistors you use. For example, if you're looking into creating a 120V light that turns on when touched, you'd need two powerful transistors and an isolation relay. However, a simple flashlight that turns on when touched would only take a couple of ...

How to Crack Passwords Faster by Putting Your GPU to Work with HashcatSecurity on the internet is always changing. Not too long ago, having a 10 character password meant that you were safe from all forms of hash cracking. Hash cracking is when you take a string of characters that have been passed through a cryptographic hash and try to reverse them. The normal processors that are housed inside of our computer cases are general purpose. The processors are not meant for handling complex math an...

Password strength and encryption are important things when it comes to computers. A password is the entire security of your computer, and OS passwords are not hard to break. Most users believe that if you have a password on your computer via the OS, that you are safe. This is not true at all, sadly.

Earlier last month, I wrote on how to subscribe to Google+ users using PlusFeed. I used it, and then I realized that I wasn't getting my own feed anymore. I discovered that the free service had been disabled due to cost issues, as detailed by the creator +Russell Beattie. The code is open source, and you can roll your own service, if you have the know-how and the time. If you don't, but still want to create RSS feeds for your own public posts, or just to track your favorite Google+ users, the...

First of all, we need to start giving names to things. Most ties (probably yours, too) are tapered. We will refer to the two ends of the tie as the wide blade and the narrow blade.

Nothing on the web is ever private. If you thought you can control your privacy, you were wrong. Websites may give you security options to better hide your information from the world, but ultimately your privacy resides in the hands of the website itself. We've seen how websites let ad companies track our private usage. We've seen how Facebook mucked up their privacy controls. We even saw how websites like Gawker are prone to hackers stealing user information. And now, Etsy has made what was ...

Back in the eighties, I used to hate television commercials, but I eventually got used to them. Had to, in order to enjoy my favorite shows. Then, the increasing number of billboard ads annoyed me in the nineties. They followed me everywhere I went—no escape—persuading me to buy the newest whatever. It seemed like Big Brotherism—like They Live. But, I got used to it. When I finally entered the digital age and became a web addict, I was peeved at the constant sight of online ads everywhere I v...

Mac owners— life just got a little easier. No longer do you have to wait in line for the newest version of iLife. No more searching Amazon or eBay for the best price on Aperture. And no more Angry Birds on your mobile device's small touchscreen!

Cheers to another completed Community Byte project! Things went well regarding timeliness and being friendly to the other coders and students. If you've got ideas for our next mission, or an idea for a tutorial, submit them to me. Friday, our mission was to take out HackThisSite, basic mission 5. This mission focused on JavaScript, again. This time there is a little bit more security in place.

Welcome to the Goodnight Byte for HackThisSite, Basic Mission 4. In Friday's session, we tackled some coding in Gobby. Nothing special, just a few modifications to the NullBot script we made a few session ago, and some education on regular expressions. Apart from coding, we did our scheduled HackThisSite mission. We had to take on some JavaScript, which was a new thing for Null Byte. This mission taught us about client-side HTML manipulation through JavaScript injections. This just means that...

Behavioral ad targeting companies are diving deeper into the realms of your subconscious with a new approach to serving adverts to you online—and they're using your television.

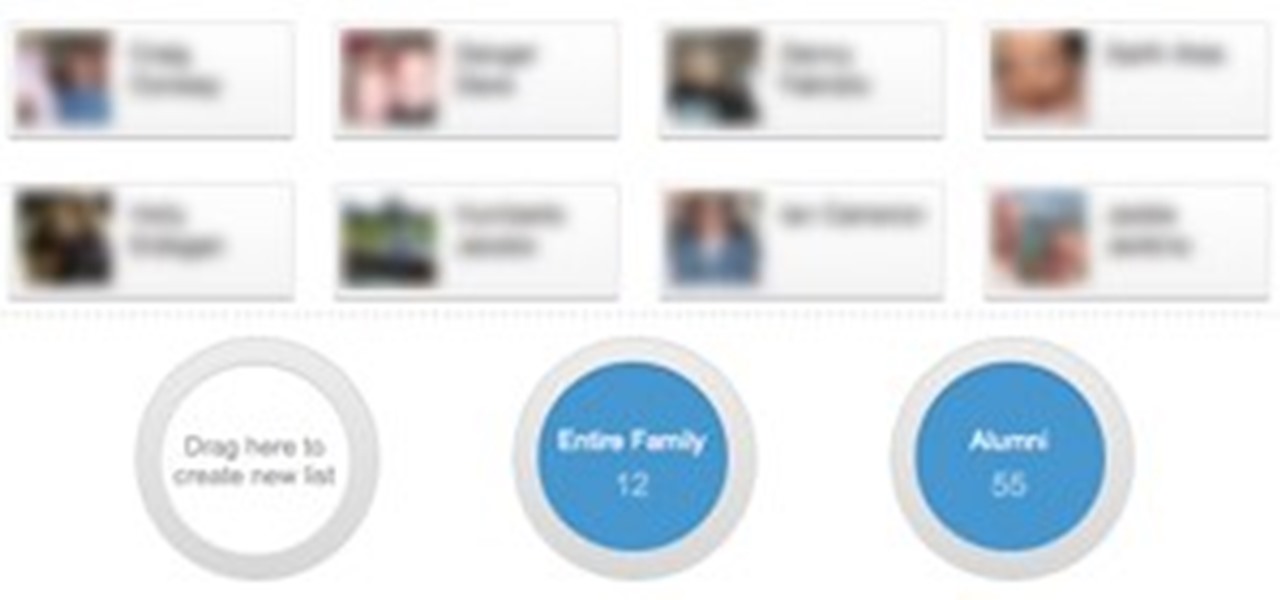
There's a lot of talk going around about Google's new social network and how it's heavily influenced by Facebook, but truth be told, how could they build Google+ without taking a note

Google recently unveiled the start of their new social network Google+, which is set to compete with Facebook and fix the awkward, broken aspects on online sharing they claim exist. It's currently only open to a limited number of Googlers during its "field trial," and if you weren't one of the lucky ones given an invitation, you can still sign up to be notified when Google+ is available in your area. You can also stay up to date on its Twitter page, GooglePlus.

Team Fortress 2 (TF2) is one of the best multiplayer games of all time. It took nine years to make, and the developers have supported it with more post-release free updates than any other game ever. Four years after its release in 2007, it is still immensely popular, and although its price has gone down, Valve has managed to continue making a massive profit by introducing the first successful microtransaction model in a mainstream American shooter. That model has been so successful that it lo...

DYVOUR n pl. -S one who is bankrupt Nigel Richards played this word in his very first game in the 2010 National SCRABBLE Championship (NSC) held in Texas, which ended today. Richards won that first game against Lucas Freeman with a 462 to 392 score, but "DYVOUR" was no forewarning for Richards — not at all.

Introduction I will not go into some time-waster of a story about how I came to build this app. It was a prerequisite in a bigger project I am still tinkering with from time to time.

Technology: The Less You Know the Better?

If you've ever had teeth removed/minor surgery, you most likely received some laughing gas, or nitrous oxide. This gas creates a happy, lightened feeling, and causes instant laughter. In this article, I'll show you how to make some. BUT BE CAREFUL!!! DO NOT proceed in this experiment unless you have EXTENSIVE knowledge of chemistry!!! Misuse of this procedure could result in the production of LETHAL GASSES! However, the set-up is quite simple, if done correctly should not lead to any issues. ...

WonderHowTo is made up of niche communities called Worlds. If you've yet to join one (or create your own), get a taste below of what's going on in the community. Check in every Wednesday for a roundup of new activities and projects.

Another week has passed on the online battlefield as the CISPA legislation continues to grind away at our freedom. Here at Null Byte, we try to keep our community informed and knowledgeable at the same time—and that means creating content for them to learn from.

In this article, I'll show you how to make a portable prank stun-baton. Powered by static electricity, simply charge up the baton, and discharge it for a static surprise. The concept behind this device ties in with Leyden jars, and their tendencies to retain static electricity.

Here's a nasty little Null Byte. An open redirect vulnerability was found in both Facebook and Google that could allow hackers to steal user credentials via phishing. This also potentially allows redirects to malicious sites that exploit other vulnerabilities in your OS or browser. This could even get your computer flooded with spam, and these holes have been known about for over a month.

What is Google Dorking? Well, simply put, "Google Dorking" is just an efficient way to utilise keywords in order to perform very specific searches on a given subject. In this case, one would look for websites/servers that are vulnerable to attacks or are configured improperly by using specific search criteria that should yeild results, should it find matches to known mistakes/errors in a website or webserver.

If you've ever wondered how software pirates can take software and crack it time and time again, even with security in place, this small series is for you. Even with today's most advanced methods of defeating piracy in place, it is still relatively easy to crack almost any program in the world. This is mainly due to computer processes' ability to be completely manipulated by an assembly debugger. Using this, you can completely bypass the registration process by making it skip the application'...

You may have asked yourself, "How do hackers take my password, if the website owner can't?" The answer is simple. When a website stores your login password for the site, it is run through a cryptographic hash function before it enters the database (if the website isn't Sony).

Today's segment of Making Art on Your iOS Device takes us into the third dimension. The below apps are suitable for beginners looking to venture into the world of 3d modeling, as well as pros who simply want the basics of Maya in their pocket.

L4D2: Chapter two - The Underground "Ok explain something to me, how is an under-the-river tour scenic?" - Nick

QI and ZA. QI n pl. -S the vital force that in Chinese thought is inherent in all things

On its quest for online domination, Amazon.com continues to expand past its basic web marketplace to fulfill the needs of everyone and anyone with a little cash to spend.

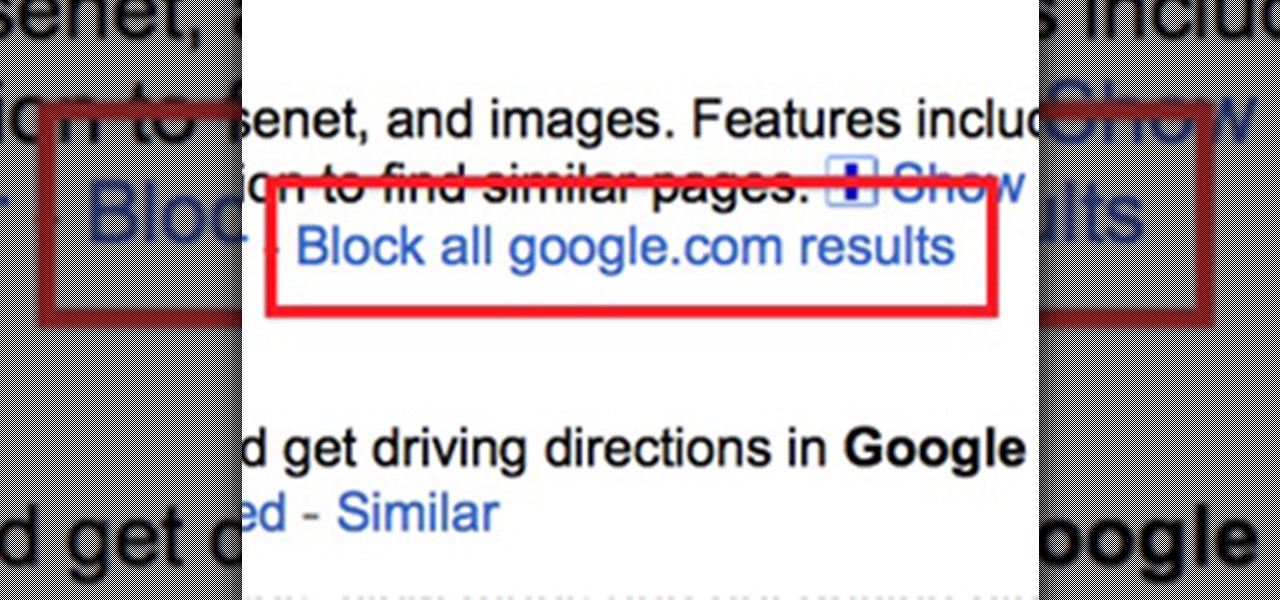
Google recently rewrote their search algorithm to make "low-quality sites" disappear from your front page results, putting the emphasis on better, more relevant answers with original content and in-depth information. And now Google has added a new feature to their search system that gives you some of the control of what you see in your results.

It's mid-January and some of you happy tax-paying citizens have already started receiving your W-4s and 1099s in the mail. But before you start filling out your 2010 Federal Tax Return, make sure you're hip to all the tax tricks in 2011. You could end up saving some money!

Pull up outside any construction site and you'll see tools scattered about—hammers, jigsaws, nail guns, hydraulic pipe benders—these are the tools of the trade. You would be hard-pressed to build a home or office building with just your hands! On that same page, security professionals also have their own go-to tools that they use on the job site, only their job site is your server.