It's been a while since I wrote up an article for this series but I did say that I'd be covering some WinAPI. So if you're interested in programming for the Windows platform, hop aboard and follow along.

Welcome back, my hacker novitiates! Every so often, a MAJOR vulnerability appears that makes millions of systems vulnerable to attack. The most recent, named Shellshock, basically leaves every Mac OS X, Linux, and UNIX system on the planet vulnerable. As nearly two-thirds of all web servers on planet Earth run one of these operating systems (primarily Linux), that's a whole lot of systems out there waiting to be harvested.

Ever since the FBI took down the Silk Road and Dread Pirate Roberts last month, many questions have been raised about whether Tor still provides anonymity or not, and if it's now broken. I'll try to address that question here today succinctly from multiple angles, keeping it as simple and plain-language as possible. The Closing of Silk Road

Watch this video and learn how to make a wonderful magical snow globe perfect for Christmas or any other holiday. You just need a jar with a lid, some pure glycerin, glittery snowflakes, and a Christmas figurine of your choice (e.g., Santa, reindeer, elves, etc.).

When words aren't enough, emojis are there to help. Your iPhone has almost two thousand of them for you to communicate in a more lively manner or to express indifference, excitement, joy, and other emotional states. However, the more emojis that come out, the more difficult it is to find the one you want — unless you know your way around your keyboard.
There are countless ways in which you can turn your love of tech and coding into a full-fledged career — from developing apps and websites as a freelancer to working in the IT departments of small startups or major tech companies. But one of the best ways that you can put your programming skills to good use is to join the increasingly important world of cybersecurity.

As long as you have the meeting ID, you can join and interrupt virtually any video call on Zoom. And that's how we get terms such as "Zoom-bombing," where someone jumps into a chat to say or visually show vulgar and inappropriate things to the other participants. However, hosts can put an end to it.

The deadly Wuhan coronavirus outbreak has not only has claimed lives in China but also has caused disruption around the globe, particularly in the tech industry. To date, the virus has claimed more than 1,000 lives in China, according to the country's officials.

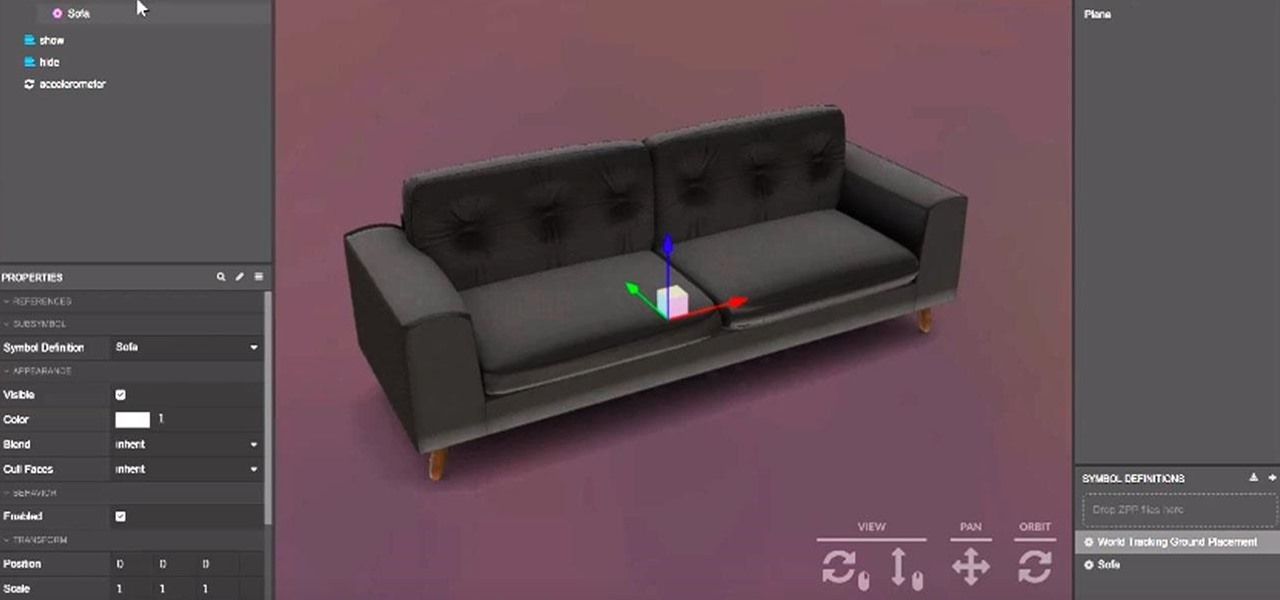
In recent years, Google's Arts & Culture project has been leading the way in terms of innovating the practice of using technology to preserve landmarks and great works of art via digital 3D copies. Increasingly, these efforts are also giving history buffs the chance to experience classic works and spaces with unparalleled intimacy through the wonders of augmented reality.

The augmented reality cloud will probably be one of the most important pieces of digital real estate in the next few years, and China has no intention of being left out of the virtual land grab.

One of the first steps in attacking a web application is enumerating hidden directories and files. Doing so can often yield valuable information that makes it easier to execute a precise attack, leaving less room for errors and wasted time. There are many tools available to do this, but not all of them are created equally. Gobuster, a directory scanner written in Go, is definitely worth exploring.

Filmic Pro has a superb suite of professional settings — bit rate, frame rate, and mic choice, to name a few — which can enable you to capture the best footage possible. But different shots require different setups, and it can be frustrating to change settings on the fly. Filmic Pro lets you skip that whole process by saving your favorite settings as presets for quick and easy access.

Augmented reality platform maker Zappar and its marker-based augmented reality technology have been around well before Apple and Google brought markerless AR to mobile apps.

As Magic Leap continues to spread its influence in the US with the help of wireless carrier AT&T, the augmented reality startup is also working its way into East Asia.

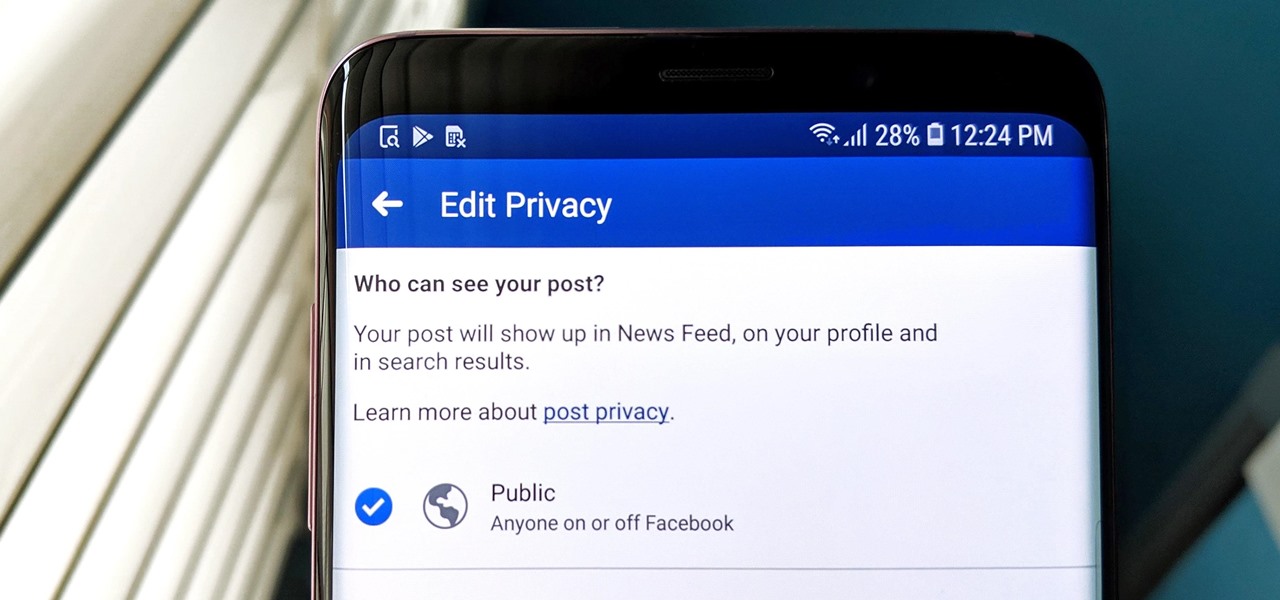
Facebook has grown into one of the central hubs of the internet where ideas are shared with others. But with the rise of brand development, individuals and companies need to get their messages out beyond their group of Facebook friends so it can be seen by more of the world.

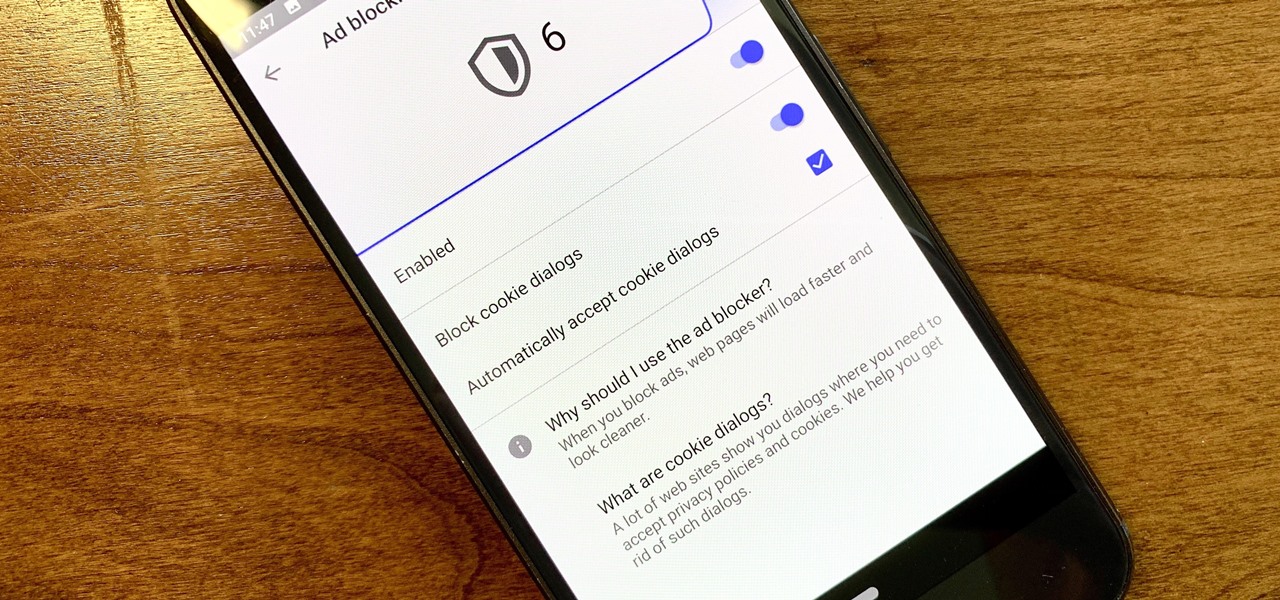
Ever since the GDPR was implemented, it seems every website on the internet needs to inform you of how its privacy policies have changed. If your web browsing experience has been marred by a constant barrage of these cookie pop-ups and privacy dialogs, you should know there's an easy way to block these web annoyances so you never have to tap another checkbox or accept button again.

When first released, Snap Map made a lot of users uneasy. Beaming their location to the world at all times isn't necessarily the definition of privacy, but Snapchat's map is nonetheless intriguing, offering users a view into the lives of people across the globe. Now, you don't even need to have an account to access Snap Map — you can view it right from your web browser.

While the numbers may not always seem to agree, the message remains the same: augmented reality is a growth segment. This week's edition of Market Reality starts with two new reports outlining the expected good fortunes for the industry and concludes with an example of a company capitalizing on their own growth.

Sophisticated hackers have been exploiting vulnerabilities in Chrome and Firefox to trick even the most careful internet users into logging into fake domains for sites like Apple, Google, and Amazon.

The company that pioneered music scanning for mobile devices is moving into the augmented reality advertising arena. Included in an update of their iOS and Android apps last week, Shazam can now scan special codes to immerse users in 3D animations, 360-degree videos, mini-games, and other AR content.

The modern age of techno-dating has made an interesting landscape for social interactions when there is some modicum of romance (or lust). For those of us born before the internet evolved into the prolific monster it has become, we first met our love interests face to face. Today, however, apps like Tinder have changed the introductory stage, for better or worse.

A scary piece of malware just got a lot more terrifying this week. Security firm Comodo reports that "Tordow," a banking Trojan first uncovered in September 2016, received a massive update this December.
Hello everyone! This is my first attempt at a tutorial here. There are a couple great assembly tutorials here, and I wanted to toss my coin in the fountain.

Managing hard drives in Linux is crucial to understanding your system and its operation as well as understanding the system you are exploiting or conducting a forensic analysis on. Linux has numerous commands that can provide us with information, control, and management of hard drives, and in this tutorial, we will examine a number of the most important ones.

Welcome back to another tutorial on functions. Last time, we looked inside memory to see what functions looked like in the flesh and all that Assembly was pretty nasty. At least you have some exposure to it. This time, we will be examining how functions work with the stack.

In this article, we will build a parallel password cracker using the techniques explained in the previous part. As SHA-512 is the digest function that Kali (and most modern Linux distributions) use to store our passwords, we will make a SHA-512 password cracker.

Hackers are claiming money for a security flaw in Apple's new update. Quick Summary:

First of all, I hope the title makes sense. :D Well, this is basically creating a program that can help with dictionary attacks. Generate possible passwords. It pretty much lies in you knowing the person you want to hack.

In 2014, Snapchat introduced a special type of Filter called Geofilters. Geofilters only appear when you're in a specific location. For example, a Disney Land Geofilter will only appear if you're actually there. Rather, your phone needs to think that you're at Disney Land. By spoofing your GPS location, you can effectively travel all across the globe — at least in the eyes of Snapchat.

Hi everyone! In the previous part of this series we introduced remote code arbitrary execution via buffer overflows using all of our past experiences.

Mother Nature is one creative entity, especially when it comes to fruit. Let's face it: most major supermarkets stock only the most common fruits like apples, pears, and grapes, but they're so basic. Why not explore other options, from the stinky-yet delicious durian to the captivating citrus caviar that is finger limes?

Welcome back, my nascent hackers! In previous tutorials for my Wi-Fi Hacking series, I have shown you how to crack WEP and WPA2 passwords, break a WPS PIN, and create Evil Twin and Rogue access points. In this continuation of the series, let's look at slightly different approach to attacking wireless.

Finding the right mix of custom ROM, kernel, and tweaks for my OnePlus One has left me flashing every new release I come across. This has led to many hours going through thread after thread trying to find the latest and best software out there for my phone. While I do enjoy the hunt, I would rather have a centralized location that covers all my bases, so that's why I have started using OnePlus One, an app by Alex Inthiaano.

I've known eaters who will fearlessly bite into the hottest peppers, but even they have quailed before durian, the fruit that hails from Southeast Asia and whose smell has been compared to garbage, rotting flesh, and the bathroom post-use. However, this hefty globe with its spiny, prickly outer covering isn't called "the king of fruits" for nothing. According to its many fans, its stench does not correlate to its taste, which has been described in extremely flattering terms. Monica Tan of The...

Third-party keyboards have become a game changer for iPhone owners since their integration in iOS 8. And while the major players from the Android realm—Fleksy, SwiftKey, Swype—already have their keyboards on the iOS App Store, their products are relatively standard fare.

Welcome back, my tenderfoot hackers! Not too long ago, I showed how to find various online devices using Shodan. As you remember, Shodan is a different type of search engine. Instead of indexing the content of websites, it pulls the banner of web servers on all types of online devices and then indexes the content of those banners.

Just like the HTC One Google Play Edition, the recently released Samsung Galaxy S4 Google Play Edition ditches the manufacturer's UI in favor of a pure Google experience, i.e. AOSP, but is also optimized specifically for the device's hardware.

There are a ton of streaming services available at your disposal in the Google Play Store—Spotify, Pandora, TuneIn Radio, Last.fm, and the list goes on and on. These apps help satisfy my day-to-day cravings for good beats, but I tend to do a little too much hopping around from music app to music app (and music widget to music widget) in the process.

In this video series, our expert John Carstarphen will show you how to create three dimensional text in Cinema 4D. You will learn how to set text spline and keyframes, adjust sweep parameters and circle radius and interpolate the precise parameters you need to get exactly the effects you are trying to achieve.

Designing and manufacturing waveguides for smartglasses is a complex process, but DigiLens wants us to know that they have a software solution that partially solves that problem.