
How To: Hang shelves
Watch this step-by-step essential guide to hanging shelves.


Watch this step-by-step essential guide to hanging shelves.

Learn how to create a to-do list using the iCal application that comes standard on all Macs.

Gary Rosenzweig looks at various methods for printing lists of files in folders in Mac OS Leopard: downloadable applications, using the Terminal, and simple copy and paste methods.

This is a guide on how to fix the Dreamcast Random Restart Problem

This is a tutorial on how to access characters command list in Mugen - the custom PC game engine - to see how to perform special attacks and basic moves.

Pyrit is one of the most powerful WPA/WPA2 cracking tools in a hacker's arsenal, with the ability to benchmark a computer's CPU speeds, analyze capture files for crackable handshakes, and even tap into GPU password-cracking power. To demonstrate how quickly it can hack a WPA/WPA2 password, we'll use it to play a Wi-Fi hacking CTF game anyone can practice for less than $10.

Hashes are commonly used to store sensitive information like credentials to avoid storing them in plaintext. With tools like Hashcat, it's possible to crack these hashes, but only if we know the algorithm used to generate the hash. Using a tool called hash-identifier, we can easily fingerprint any hashes to discover the right Hashcat mode to use to retrieve a password.

Google is an incredibly useful database of indexed websites, but querying Google doesn't search for what you type literally. The algorithms behind Google's searches can lead to a lot of irrelevant results. Still, with the right operators, we can be more exact while searching for information that's time-sensitive or difficult to find.

With the imminent arrival of the HoloLens 2 expected any day now, Microsoft is preparing new users to take advantage of its software from day one.

I already know what you're thinking: this guide is blasphemy. I am showing you how to turn a Galaxy Note 10 or 10+ into an iPhone 11 Pro Max. And while I'd usually agree with you, hear me out. How can you know you don't like something until you try it? So here is your way of trying out an iPhone using your Galaxy Note 10.

Out of the box, Apple's digital assistant could be a godsend or a nuisance, depending on your daily interactions it. No matter which camp you fall into, Siri can always be better suited to your personal needs with a little customization. You can make Siri a powerhouse not to be reckoned with, or you can minimize its presence if you only need Siri help sometimes — all without any jailbreaking.

Apple's macOS operating system is just as vulnerable to attacks as any Windows 10 computer or Android smartphone. Hacker's can embed backdoors, evade antivirus with simple commands, and utilize USB flash drives to completely compromise a MacBook. In this always-updated guide, we'll outline dozens of macOS-specific attacks penetration testers should know about.
Smartphones and laptops are constantly sending Wi-Fi radio signals, and many of these signals can be used to track us. In this guide, we'll program a cheap IoT device in Arduino to create hundreds of fake networks with common names; This will cause nearby devices to reveal their real trackable MAC address, and it can even let an attacker take over the phone's data connection with no warning.

Instagram is a great platform to share photos and videos with the world, but sharing with smaller groups is near impossible. You can directly message pictures, stories, or post links to friends, but that only works for one person at a time or in group chats you create. To share your content with a small group of people you care about the most, you'll want to use the "Close Friends" list.
Google's new Pixel and Pixel XL flagships are some very powerful smartphones, but as with any high-tech gadget, they're only as capable as the user allows them to be. So if you're a proud new Pixel owner, it's time to bone up on a few new features to help get the most out of your device.

Welcome to the final tutorial of the series on standard C. This article will cover the linked list abstract data type (ADT). There will be a lot of abstraction to try to deliver the understanding in the most basic way for easiest interpretation of what they are and how they work, then we will get into the guts of it and learn the technical code underneath. For those who have yet to grasp the concept of pointers, it's advisable that you do that first before approaching this. Having learned thi...

Welcome back! In our last training session, we covered some advanced list topics. We'll be going deeper into the advanced list rabbit hole today with lambda and lambda operators! (And I'm not talking about Gordan Freeman)

The day has finally come, and after quite a bit of hype and buildup, Windows 10 is now officially available. The update itself is on a staged rollout, which means it will be slowly becoming available to users over the coming weeks and months, so don't panic if you haven't already received an update notification. Besides, you have until July 29th, 2016 to download your free copy of Windows 10 if you're eligible, so there's plenty of time to get your ducks in a row.

When opening a link or sharing a photo, your Android device will bring up a list of possible applications that you can complete the action with. However, some of the apps included you never use or didn't even know existed, and this leads to unnecessary clutter. Fortunately, if you're rooted, there's an easy way to remove apps from the "Open with" and "Share via" lists.

Welcome back, my budding hackers. So many of you are interested in hacking Wi-Fi that I have decided to revisit my Wi-Fi Hacking series with some updated and more in-depth material. I strongly suggest that you look at some of my earlier posts, such as "Getting Started with Terms and Technologies" and "Getting Started with the Aircrack-ng Suite of Wi-Fi Hacking Tools," before continuing here. If you're ready, you can also check out our updated 2017 buying guide here.
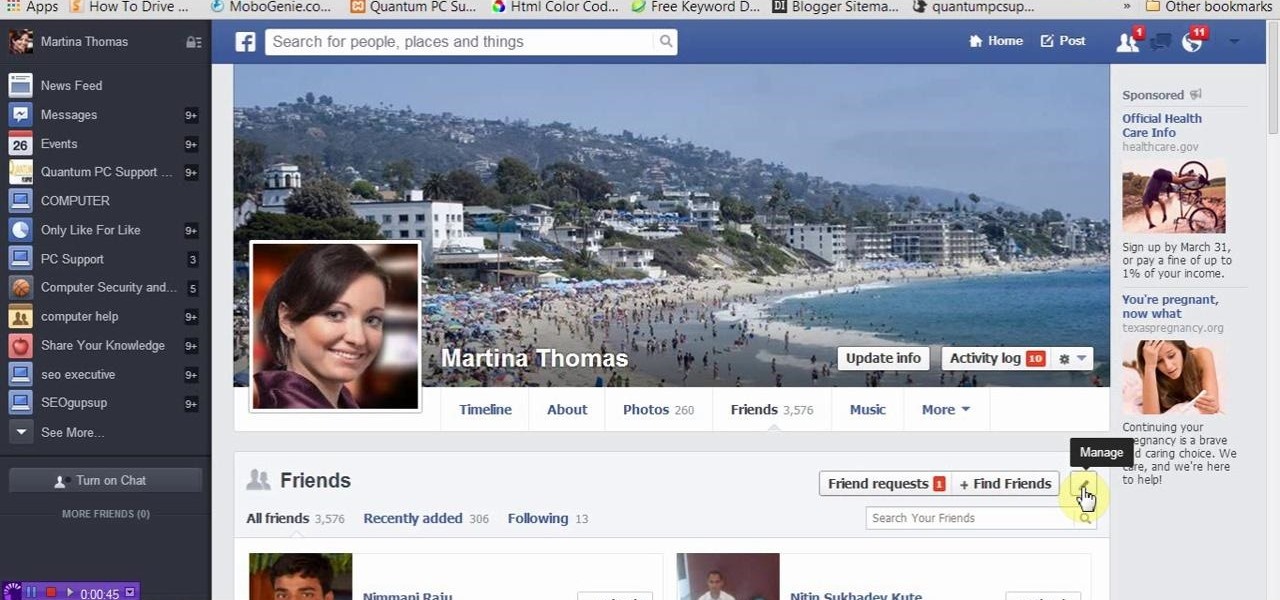
This tutorial video will show you how to hide Facebook friends list from public. With the help of this video you should restrict others from watching your Facebook friends list. Watch the video and employ the technique in your Facebook account.
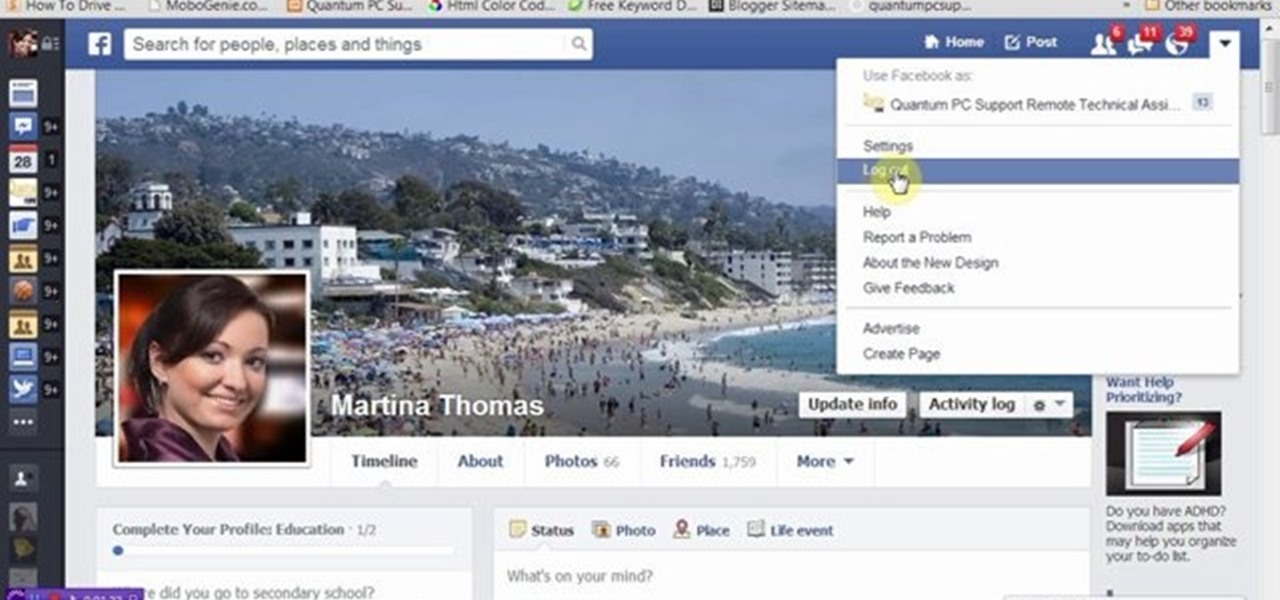
This video will provide an idea how you could hide your friend related information on Facebook and list from the public or your friends also. Especially the list is hidden from those who are not your friends in Facebook.

How to make eggshell planters. Great fun to do with the Kids this Easter Step 1: Watch This Video Guide

How to make a variety of different pancakes. Simple guide showing you pancake making tips and tricks.
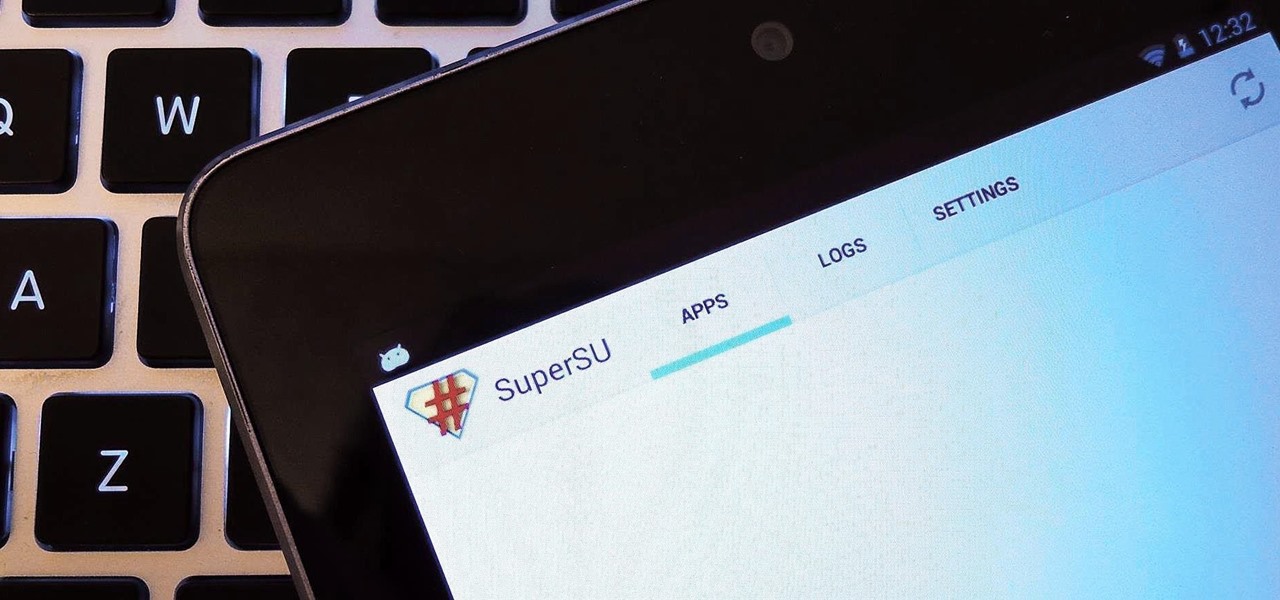
The new Jelly Bean is out in the wild, but if you've installed Android 4.3 from stock, you'll notice rooting is now not possible. If you miss the ad-blocking capabilities of AdBlock Plus, how Seeder made apps snappier, or the convenience of backing up with Titanium Backup, you'll need to get rooted.
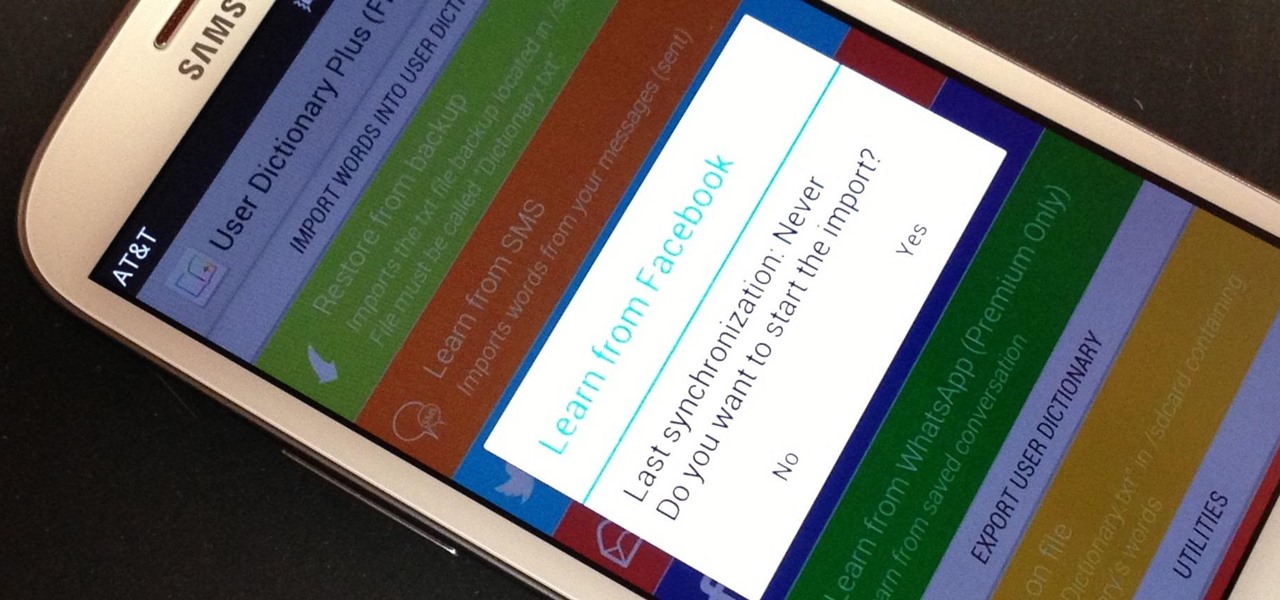
My standard text greeting to friends is something along the lines of "Wazzup biznitch?"—but apparently the auto-correct function on my Samsung Galaxy S3 has a problem with that. Time after time I have to retype it or just add all my made-up words to the word list—and I use a lot of made-up words, because that's what bosses do. But texting isn't the only way I communicate. I also use email, chat, and social media on a daily basis—and I don't always use my phone. So, wouldn't it be awesome if m...

In my first tutorial on Linux basics, I discussed the importance of hackers using Linux and the structure of the directory system. We also looked briefly at the cd command. In this second Linux guide, I'll spend a bit more time with changing directories, listing directories, creating files and directories, and finally, getting help. Let's open up BackTrack and getting started learning more Linux for the aspiring hacker.

If the ice does not funnel into the glass, you will have to replace the ice dispenser guide. You can follow the steps in this video to help you do this easy repair.
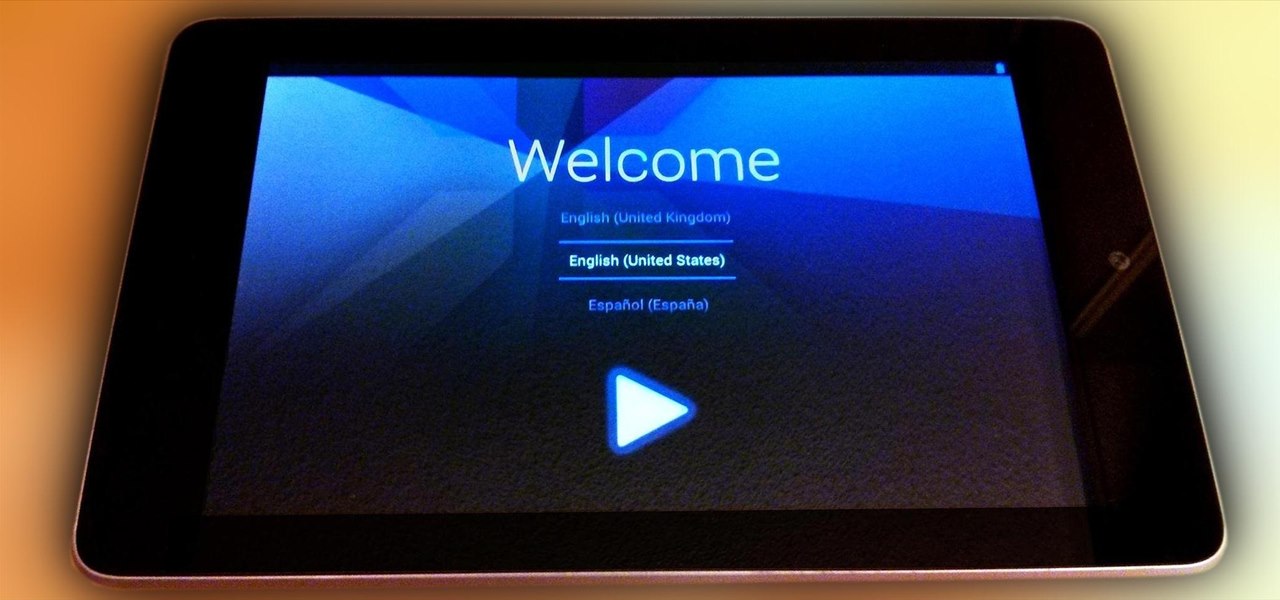
Something went wrong and your Nexus 7 is freaking out on you. Maybe you flashed a bad ROM or ZIP file, or maybe it's just bugging, and it's time to restore your tablet back to a working condition. Thankfully, you've already made a backup of your Nexus 7!

It's no secret that there's a lot of surveillance going on these days. It's easier than ever to end up in a database, and even former government agents are speaking out about the atrocious amount of spying being done against our own citizens. They've targeted our laptops, cars, IP addresses, and now they're coming for our iPhones. AntiSec hackers managed to get their hands on a list of over 12 million Apple UDIDs (Universal Device IDs) from an FBI computer, and they published 1,000,001 of the...

The Motorola Droid is getting a little long in the tooth, but it is still a remarkably capable phone with full keyboard, which makes it almost unique among it's Android-based competition. If you've rooted your phone (good for you!) and for some reason want to go back to the stock configuration that your phone was in when you took it out of the box, this video will show you how to do it. One good reason is if you want to update your phone's firmware, which will not work if you phone is rooted ...

This is a step by step tutorial on stencil painting your walls, brought to you by The Home Depot. Beginning with a brief description of the art of stenciling, you are then shown the materials you will need to proceed. Next, you are shown how to prepare your room and surfaces. The goal will be to use a single stencil in multiple positions. The stipple method of application is stressed to achieve a multi-dimensional application. Two colors are used to give the added dimension of shadow to the i...

Are you playing through Dark Souls and having flash backs to all those times you died in Demon Souls? IGN is here to help you with several tips and tricks on surviving. This guide shows you good spots to grind, what gift to pick for your character, and where to get the Sorcerer's Catalyst item that will allow you to cast magic in the game, even if you aren't a magic user.

Undeadburg is the first level of Dark Souls and is probably the best place to start off. This guide from Giant Bomb will take you through the safest path to get through the level and help you take out the undead enemies you find.

This League of Legends guide from CLG showcases how to use zone control against your opponent by forcing them to stay out of range of minions and preventing them from damaging you. This will allow you to win your lane so that you can move into the late game.

If you're interested in finding out how to get Unchained Alistar for free take a look at this guide from Riot Games. By subscribing to the League of Legends YouTube page, you'll be eligible to get Alistar for free, in addition to his Unchained Alistar skin!

The front camera on the Droid Bionic from Motorola is a perfect match for the Google Talk application provided with the Android smartphone. Using the Verizon Wireless 4G connection, you can stream video and voice to friends and family members on the go. This guide by Motorola demonstrates how to video chat on the Bionic.
The Eagles may very well be the most played team in the Madden NFL 12, and for good reason--they're the strongest team in the game. Don't worry about forfeiting games when you see them on the other side, with this guide from EA Sports you'll learn how to slow down Michael Vick, use a Sugar Blitz for a strong defensive play, and take advantage of their weak lineback and safety.

If you want to put the finishing touches on your new BioShock cosplay outfit, of if you just think it would be awesome to charge at your friends with the favorite weapon of Big Daddys across Rapture, this is a guide for you.

Make sure your vehicle passes inspection. If you feel any play in the steering wheel of your car, jack up the vehicle and try jostling the tire from side to side. If there is play, it may be time to replace a bad ball joint.