Welcome back, my hacker apprentices! Although there is a multitude of different hacker types, the one target they all share is the database. I often refer to the database as the hacker's Holy Grail, or the ultimate prize for an effective hack.

Welcome back, my greenhorn hackers! Continuing with my Wi-Fi hacking series, this article will focus on creating an invisible rogue access point, which is an access point that's not authorized by the information technology staff and may be a significant security vulnerability for any particular firm.

Here's a list of the lifehacks shown in this video: Banana Foil

Welcome back, my hacker trainees! A number of you have written me regarding which operating system is best for hacking. I'll start by saying that nearly every professional and expert hacker uses Linux or Unix. Although some hacks can be done with Windows and Mac OS, nearly all of the hacking tools are developed specifically for Linux. There are some exceptions, though, including software like Cain and Abel, Havij, Zenmap, and Metasploit that are developed or ported for Windows.

Do you ever wonder how all these celebrities continue to have their private photos spread all over the internet? While celebrities' phones and computers are forever vulnerable to attacks, the common folk must also be wary. No matter how careful you think you were went you sent those "candid" photos to your ex, with a little effort and access to public information, your pictures can be snagged, too. Here's how.

Want to learn how to build a robot out of Snap Circuits? I'll show you how to combine Snap Circuits parts from three different sets (the Snap Circuits rover, Snap Circuits Micro, and the Snap Circuits motion detector) to make a simple programmable motion activated robot. For a complete step-by-step build of the robot, visit my project at Instructables: http://www.instructables.com/id/Hack-the-Snap-Circuits-Rover/

Welcome back, hacker novitiates! In the next few hacks, we will be breaking into Windows servers. In this installment, we will learn to add ourselves as a user to a Windows 2003 server. Of course, when we have added ourselves as a user, we can come back any time and simply log into our account without having to hack into the system and risk detection.

By overlapping your Farmtown crops, you can up the production output for your fields. There's a bit of a trick to being able to layer your crops in such a way that the game will allow. However, you can still manage to accomplish this without having to resort to cheat codes, mods or hacking the game. Just follow along with this tutorial - you can even keep your accessories like flowers and bird baths! Put your longest growing crop on the bottom.

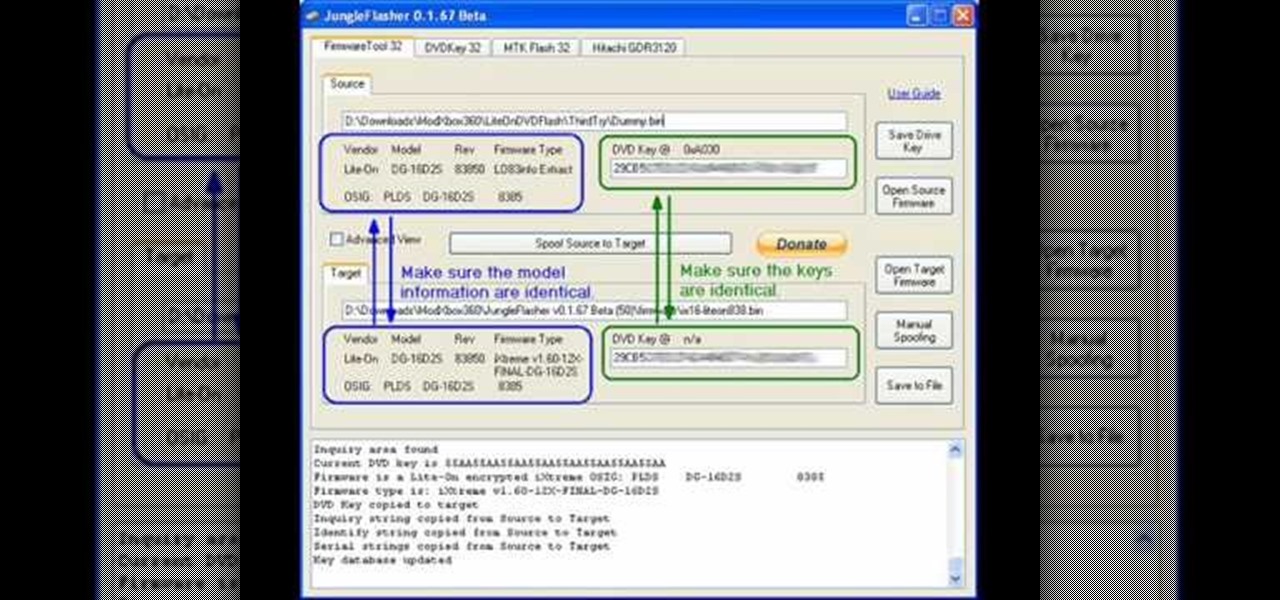
If you're tired of paying $60 for new XBox 360 games or waiting years for them to get cheaper, you should probably mod you system. This will allow you to play burned copies of games for free (no time to get into the moral implications here). The first step in that process is flashing your disc drive and installing custom firmware on it that will recognize your burned game discs. This video will show you how to flash the Lite-On drive used in many XBox 360's. If you don't have the Lite-On driv...

Are you smarter than the average bear? Show the world by using Yogi Bear as your Black Ops playercard emblem. This clip will teach you everything you'll need to know to draw a custom Homer Simpson emblem in the Call of Duty: Black Ops Emblem Editor.

Unlock the "Closer Analysis: Hidden Intel" trophy in Call of Duty: Black Ops! This achievement is won by finding the hidden intelligence documents in Missions 1, 2 & 4.

Want to earn the "Sally Likes Blood" achievement on the Regular difficulty setting in the single-player campaign of Call of Duty: Black Ops? Here's how you do it.

Want to learn how to do quick scoping in BO? It's easy: use the variable scope and zoom in to the second or third level of magnification. Voilà. No more two-second delay when shooting. For a complete walkthrough of how to quick scope, watch this gamer's guide.

So, how do you get your family together in FrontierVille on Facebook? One way is with the Dinner Triangle. If you family gets lost out in the forest or behind a tree or building, then all you have to do is ring the Dinner Triangle and they'll come running. See how to use it!

Interested in hacking the power button on your Windows PC to put your computer to sleep instead of shutting it down? This Windows 7 tutorial will show you how it's done! It's easy! So easy, in fact, that this home-computing how-to can present a complete overview of the process in just over a minute's time. For more information, including detailed, step-by-step instructions, watch this Win 7 user's guide.

In this Electronics video tutorial you will learn how to use Bluetooth connectivity to share cell phone files. You are not hacking in to other people's phones as you need their permission to access their phones. You can change ringtones and pictures or share them with your friends. For this both people have to have Bluetooth on. Go to options > Bluetooth > visibility > shown to all. Now go back to Bluetooth and make sure it's ON. Now select 'paired devices'. The same steps have also to be fol...

The Evo 4G does a lot of fancy things. Unfortunately, a lot of those fancy things are power-intensive. Interested in getting the most out of the HTC Evo 4G's battery? Whether you're the owner of an HTC Evo 4G Android smartphone or just covet one, you're sure to enjoy this Evo owner's guide from HTC Evo Hacks, which presents a complete, step-by-step walkthrough of how to improve your Evo's battery life. For complete details, take a look!

In this tutorial, we learn how to use salty hashes to keep passwords secure. A hash is stored in a database that is hashed with an algorithm, so not everyone can see exactly what your password is. When you type your password into a website, it doesn't actually register as words, it registers as a hash. This keeps your passwords secure so not everyone can see them. Salting is when you use random pits and attaching them to your regular hashes so not every password is the same. The salt is what ...

Hacking the PSP is a complicated process, and there has been some demand for a software tool that would make the process easier. This video has that solution. It explains how to use a program called PSPtool to create the magic memory stick and Pandora's battery much more easily than you could otherwise. Follow these instructions and play those homebrews!

In this clip, learn how to make a fast, cheap and super easy mount for your your bicycle to display safety lights. Wearing bike lights at night will help you stay safe in the dark and if you want to avoid the cost of getting lights custom fitted, this hack is perfect for you. All you will need is some PVC pipe and some grip tape (like the kind used for tennis rackets). Follow along and get started. This mount is flexible and fits most standard lights or flashlights.

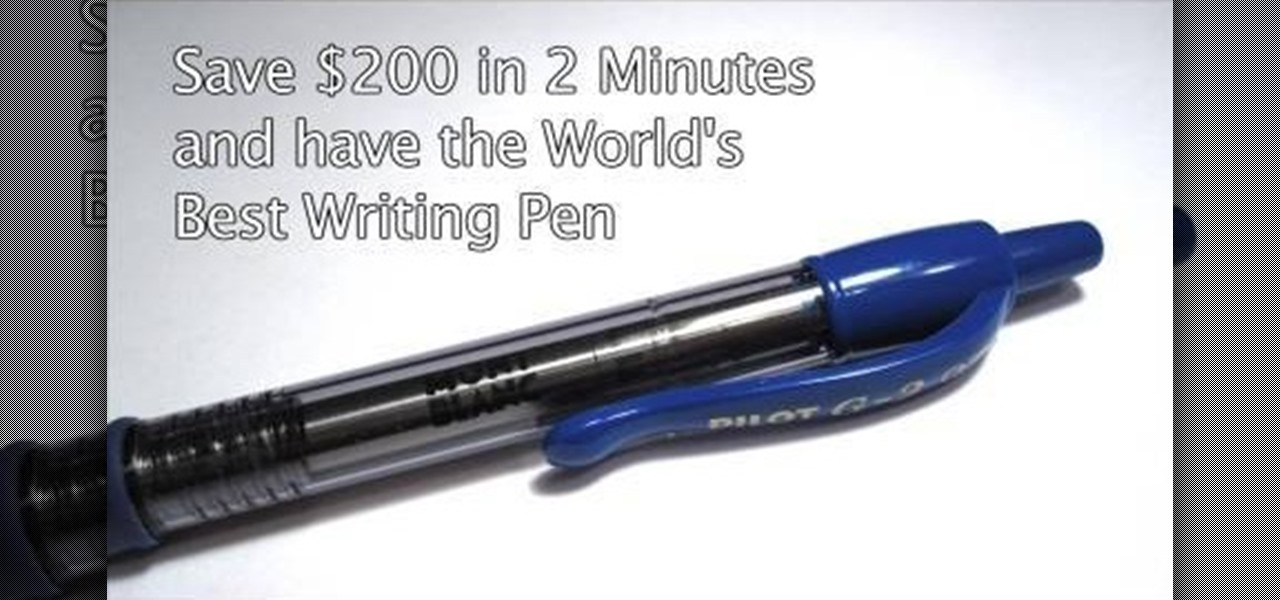
In this tutorial, you will learn how to hack an ordinary pen and turn it into a Mont Blanc worth $200. Mont Blanc is known for its smooth writing style and enviable design and with this clip you can get all the perks of this luxury brand for about 15 bucks.

If you move around a lot, you may notice that you can't play the same DVDs from country to country. The world is separated into different regions, and not all movies will play in all places. There are ways around this security measure, however, if you follow this tutorial.

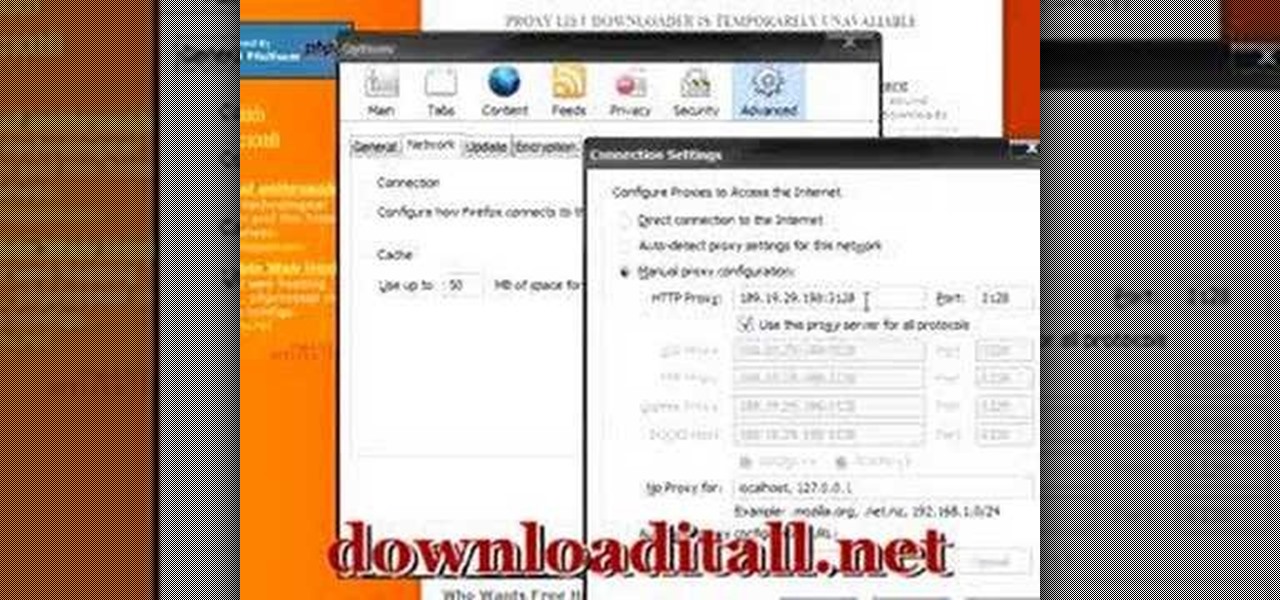
If you are stuck using a computer in a place with safety filters, you can use this tutorial to bypass those controls and get to your YouTube account. So, whether you are in a school, library or your parents have parental controls activated, just follow along and you will be able to get past them every time. There are two methods described in this tutorial, one is easy for beginners and the other more advanced. They both work like a charm, however, and you will be watching your favorite videos...

Windows 7 has hit the streets. If you've got Windows Vista or XP, and you are preparing to do the switchover to WIndows 7, check out this video!

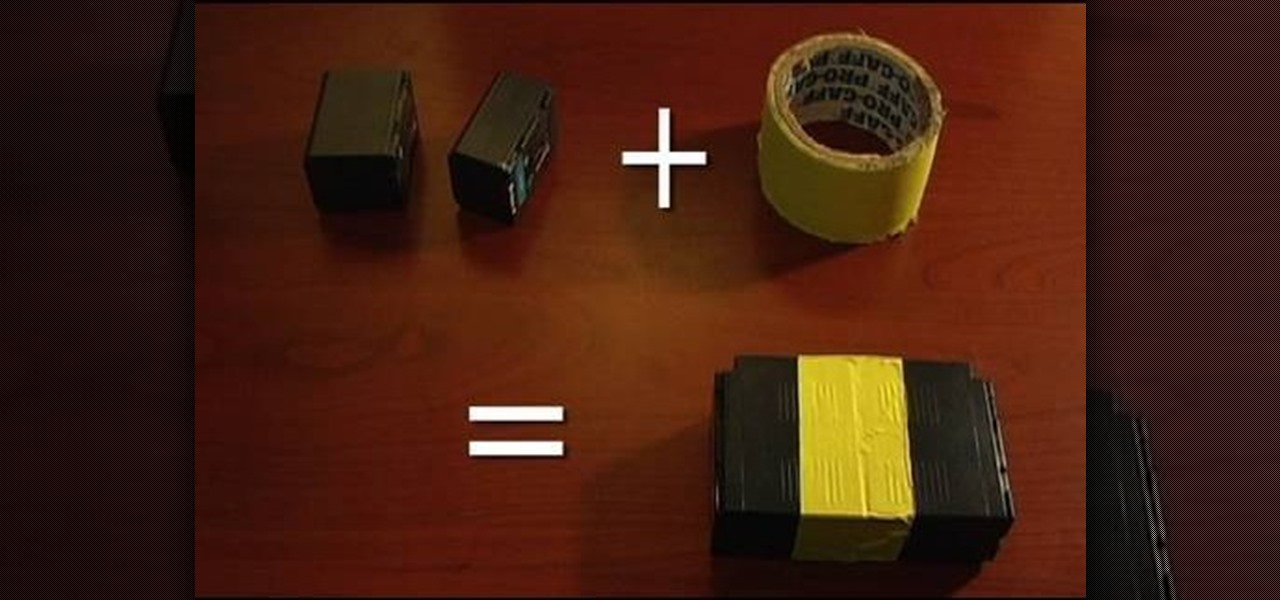
See how to make a guerilla battery pack for your camera! For this quick battery hack from ChappyShowcase, all you need is some gaffing tape and two batteries from your camcorder. Simply tape the two batteries together so that the contact terminals are facing away from each other. By combining two batteries into one, you'll have a guerilla battery brick setup. Now you're prepped for the most efficient battery swapping capabilities possible! This is a good trick for any assistant cameraman.

Learn everything you could possibly want to know about the internet, multiplayer game Evony with tutorials from EvonyTutorials. Watch this video tutorial to learn how to play Evony - military domination. See exactly what the game Evony is!

Get your dose of the coolest Adobe Lightroom tutorials, tips, time-saving shortcuts, photographic inspiration, and undocumented tricks with Matt Kloskowski from Photoshop User TV. Photoshop Lightroom is the leading photo management software solution. See what leading photographers use to manage their photos, and how.

Learn how to turn a t-shirt into a sexy one piece swimsuit. This swimwear project is cheap and easy. The sexy GiannyL demonstrates this DIY closet hack that's simple and cheap. All you need is a t-shirt, pins and a sewing machine. Cut along the pattern Gianny L has demonstrated and sew. Voila! You have a dead sexy one piece swim suit.

Ever wanted to learn how to pick a lock? Well, there's no better time than now to start learning the craft of so many locksmiths out there... lock picking. Just watch this video tutorial to see how to pick single-pin locks.

Ever wanted to learn how to pick a lock? Well, there's no better time than now to start learning the craft of so many locksmiths out there... lock picking. Just watch this video tutorial to see how to pick a Brink's high security lock.

Want to see whether your PC is being accessed by hackers? Netstat (network statistics) is a command-line tool that displays network connections (both incoming and outgoing), routing tables, and a number of network interface statistics. It is available on Unix, Unix-like, and Windows NT-based operating systems. This video tutorial presents a basic introduction to working with the netstat tool. Determine whether you've been hacked with this how-to.

Check out this step-by-step video tutorial on how to take the back off and take apart the new iPhone 3G (2nd generation). The directions here also include how to replace the LCD, touchscreen, battery, and motherboard in Apple's iPhone 3G. It also includes any information that might be needed to hack the internal workings of the iPhone.

Old T-shirts are usually relegated to our closets or heaped in piles to be donated to Goodwill, but even the frumpiest of T-shirts need not be discarded when you can repurpose it!

Hey iPhone jailbreakers! Did you jailbreak your 2G/3G iPhone and then update to firmware 4.1? Yeaah. Now you've got a shiny little brick, don't you. Well, this video will help you get free (again) from the clutches of those clever guys in Cupertino. Apple doesn't like people messing with "their" phones, but come one, didn't YOU buy it? So hack it, crack it, load it up with 3rd party apps and when you get 'no service' check out this how to and bring your phone back to life.

Epic Duel can be an epic game, but you can get to the top quicker with an age old secret: cheating! If you follow this video and grab Cheat Engine 5.6, you'll be able to give yourself more credits, more quickly than actually earning them. Come on, life is short, why work hard, isn't cheating the way most successful people have made it? If you're looking to get yourself Cheat Engine 5.6, you can find it here. Go forth, and cheat.

If you have an iPhone or an iPod Touch then you probably think that the only places you can listen to your MP3 files are on your laptop, your i-gadget of choice, and your car. But in reality anything that you can groove to on your iPhone or iPod Touch can be listened to - and transferred to - your PlayStation 3.

In this tutorial, we learn how to use the notepad to get by school internet blocks. First, open up Notepad on your computer, then type in "<html>" "<body>", "iframe src=http://www.youtube.com", then "height=100%", then "width =100%". To finishe, type in "<iframe>>/body><html>". Save this as hack.html as all files. After this, open up your browser, then you should be able to go to the website that you wanted to go to! This is a great way to get around the security settings that your school has...

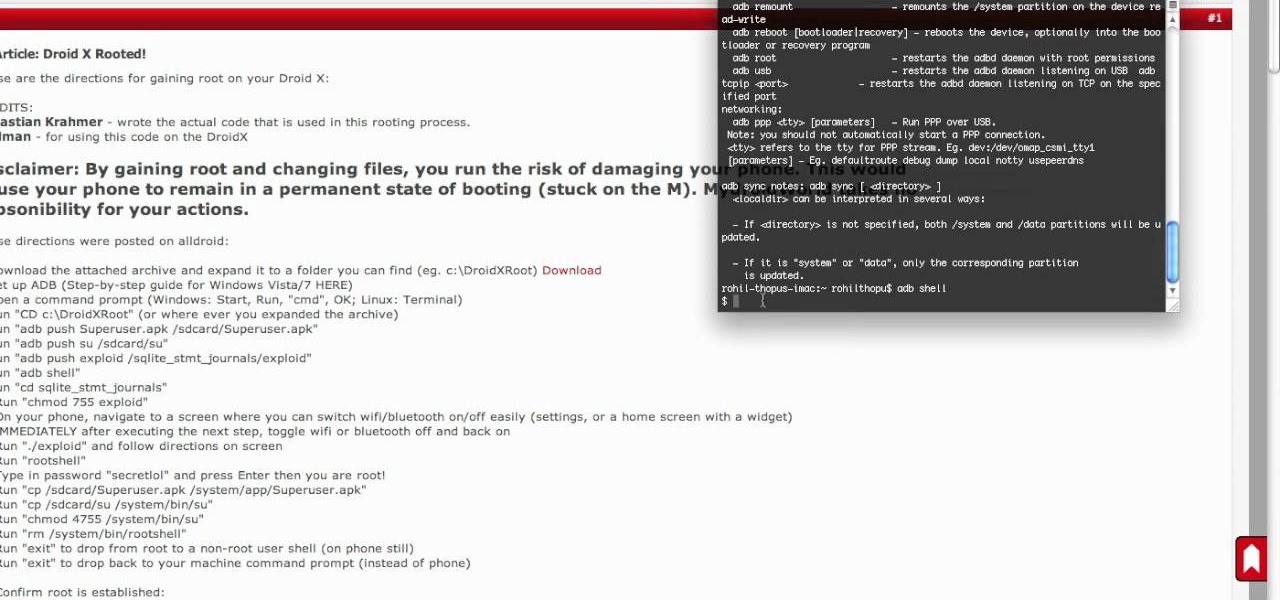
It seemed like an impossible task. No one could figure it out. Only God himself knew the answer. But the impossible has become possibly after only a week of trying. The Droid X has been rooted.

Imagine your own time-lapsed footage in a 360 degree pan. You don't need an expensive Hollywood-style pan mount to get this effect. You can easily do this rotating pan mount on the cheap, with something you would never suspect— a kitchen timer.

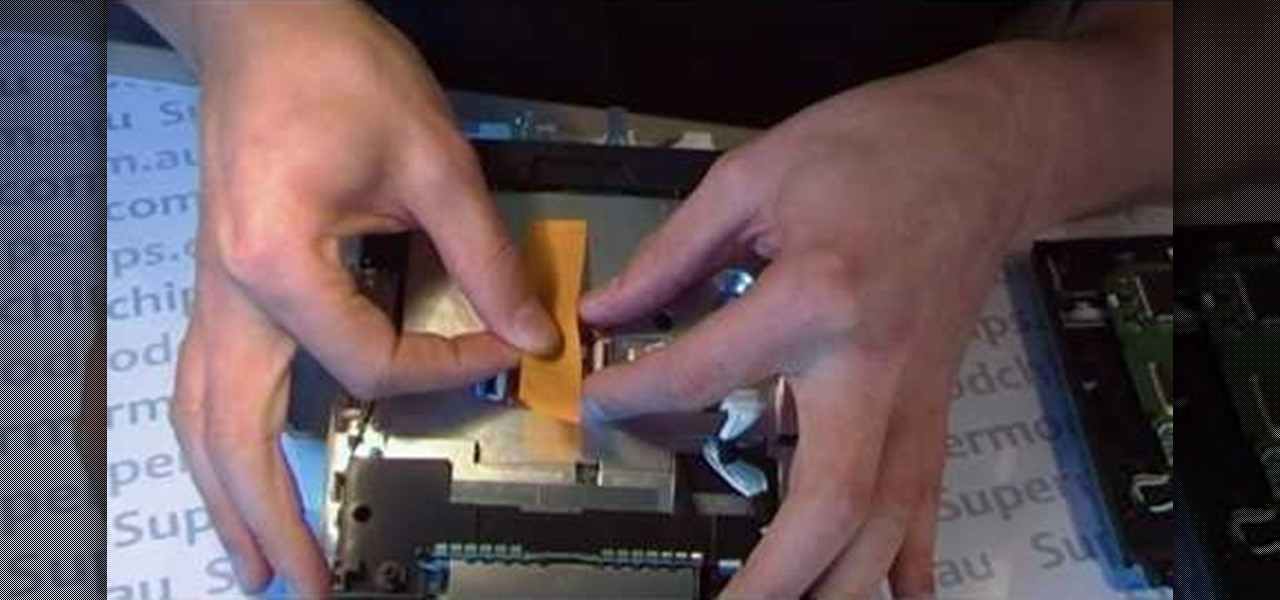
If you're looking to do a bit of hacking for your Nintendo Wii, this video is what you need. In this tutorial, you'll find out how to install the drivekey modchip for the Nintendo Wii easily. This is easy to put in and will help with your gaming experience. But do remember once you've opened up your Nintendo Wii, the warranty might expire, so do so wisely.