
How To: Beef Up Your Recipes with Beef Salt
Beef: it's what for dinner. And if you really like the taste of it, it can be what you season the rest of your dinner with, too.


Beef: it's what for dinner. And if you really like the taste of it, it can be what you season the rest of your dinner with, too.

With the first wave of Apple Watches being received today, you're probably busy setting yours up and playing with all its features.

Whether it's to flaunt your new digital face on Instagram or to show off a unique app to your friends, you'll ultimately need to know how to take a quick screenshot with your shiny new Apple Watch. Turns out, it's not that much different than taking one on your iPhone.

Welcome back, my neophyte hackers! In previous tutorials, we learned how to steal system tokens that we could use to access resources, how to use hashdump to pull password hashes from a local system, and how to grab password hashes from a local system and crack them.

With the Galaxy S6 Edge, the curved display is mainly an aesthetic feature. Unlike the Galaxy Note Edge, Samsung didn't include many software features to take advantage of its unique design, outside of the scrolling tickers and night clock. For instance, with the Note Edge, you can launch apps from the curved portion of the screen—but this isn't true for the S6 Edge.

Google Play Music is an awesome app—even if you don't subscribe to their $9.99/month All Access service, you can still use it to store and stream up to 50,000 of your own songs for free. Add to that the fact that it's a pre-installed app on most Android devices, and there aren't many reasons not to be using Play Music.
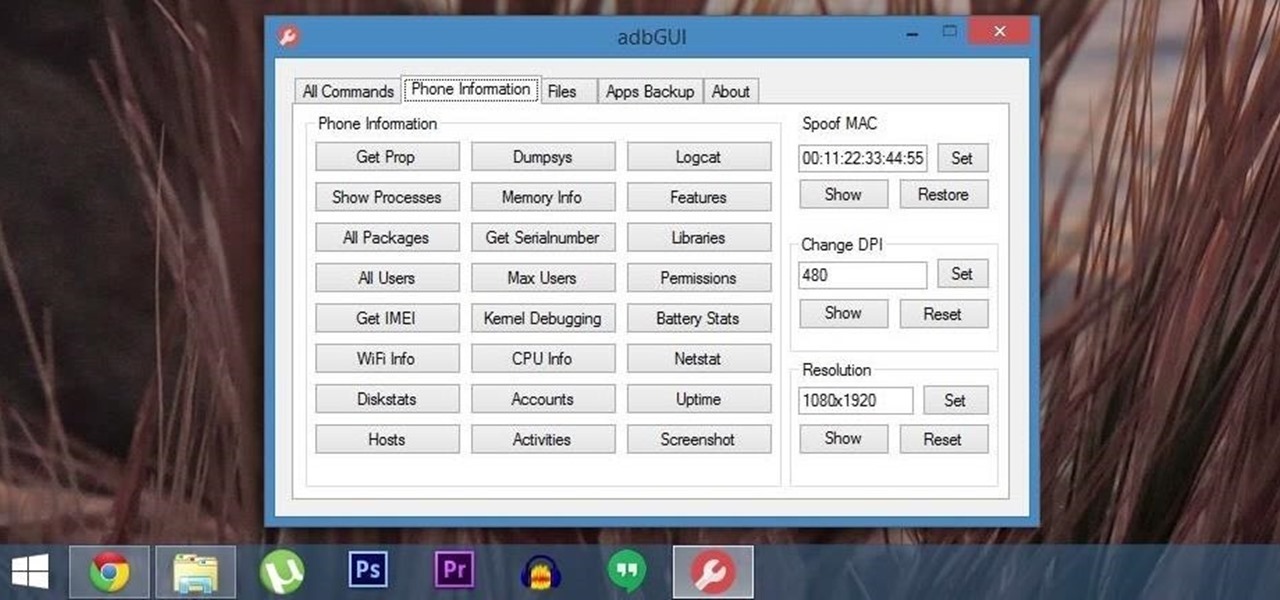
Android Debug Bridge (or ADB for short) serves as a remote terminal interface for executing shell commands on any Android device. Put simply, ADB lets you send commands from your computer to your phone or tablet, some of which would require root access if they were performed on the Android side of the connection.
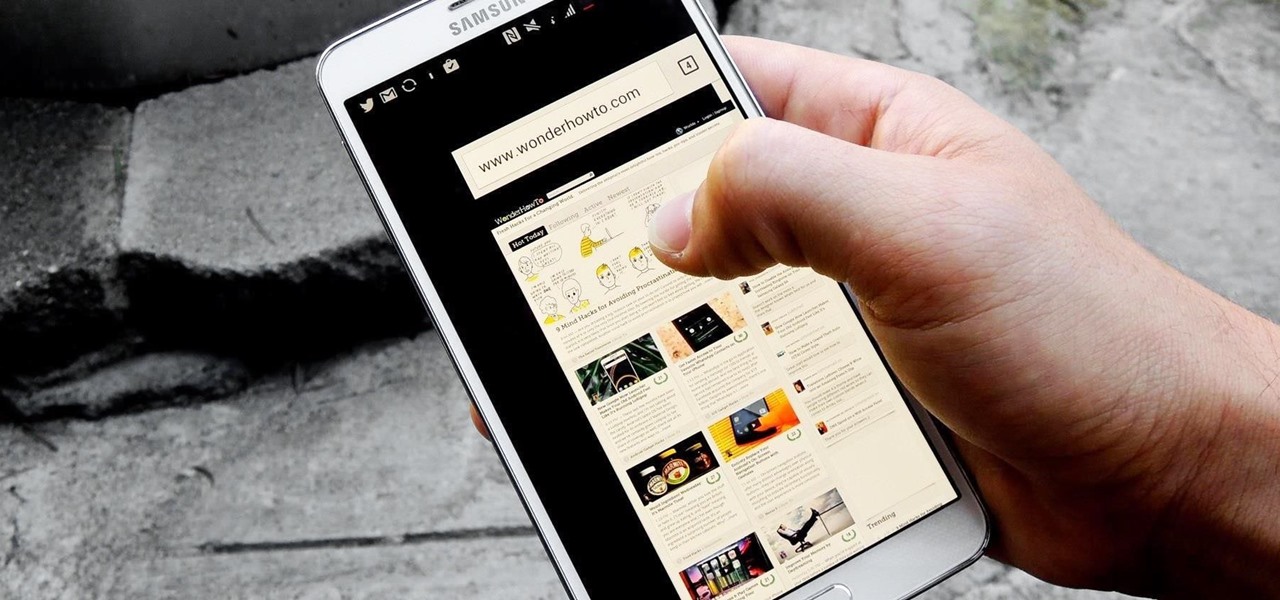
Our hands aren't necessarily getting any bigger, but smartphones still seem to be getting larger and larger. With average cell phone display sizes nearly doubling since 2007 (leading to new terminology like "phablet"), reaching all corners of a screen can become nearly impossible with one hand. Granted, most larger devices like the Samsung Galaxy Note 3 and Galaxy Note 4 come with a one-handed option to make navigating easier, but other popular devices like the Nexus 6 don't. While it may see...

Samsung included an "SOS" feature for its phones since the Galaxy S6 that could literally be a lifesaver should you ever find yourself in an emergency situation. It's one of those things that we hope to never have to use but will be very thankful for if a need ever arises.

As your Galaxy S6 lies on your desk while you're hard at work, it's difficult to resist from periodically pressing the wake/lock button to check the weather or glance over any notifications you may have on your lock screen. While pressing the hard key is easy enough, there's an even easier method where you simply hover your hand over the device to wake the screen.

Ever feel like you're receiving notifications way too late on your Android device? Many Android apps use Google's Cloud Messaging service to send and receive notifications, including Hangouts, Gmail, Pushbullet, Facebook, and even WhatsApp to an extent.
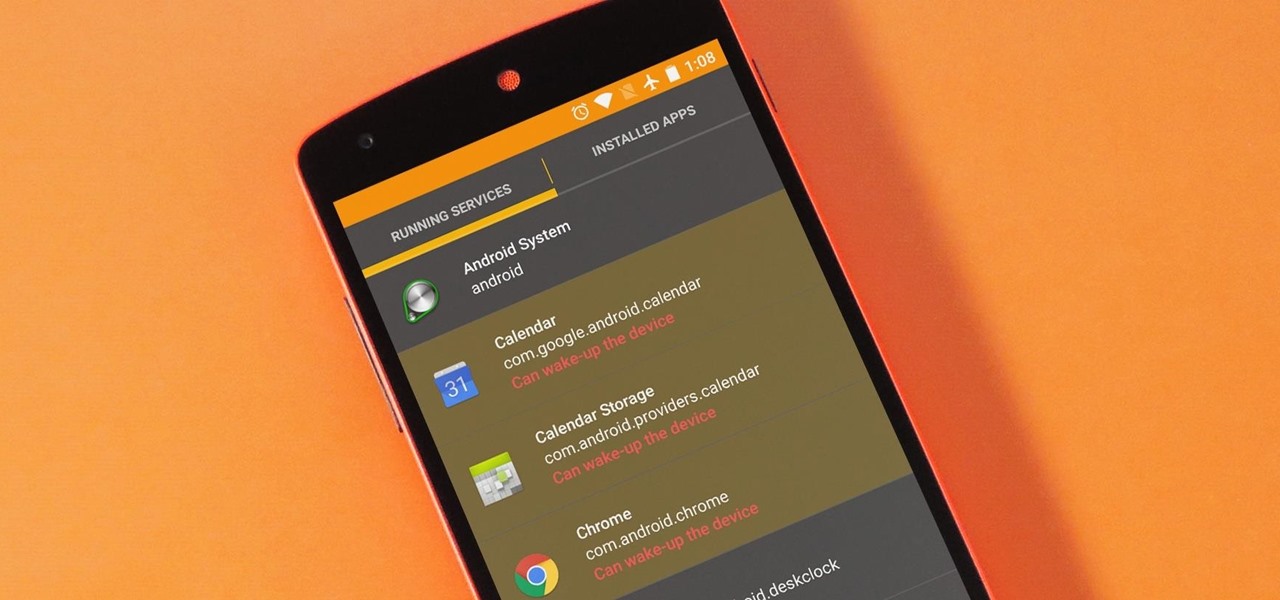
The vast majority of Android apps use background services to sync data, check for location updates, and perform various silent tasks. These background services can start up whenever they'd like, and they continue to run in the background even when you're not actively using the app that they originated from.

In addition to the fingerprint scanner, the Samsung Galaxy S6 has all of the basic lock screen options that other Android phones have: swipe, pattern, PIN, and password. There also just happens to be a secret sixth option called "Direction lock" that protects the device with a series of customizable directional swipes—only it's hidden in an unsuspecting settings menu.
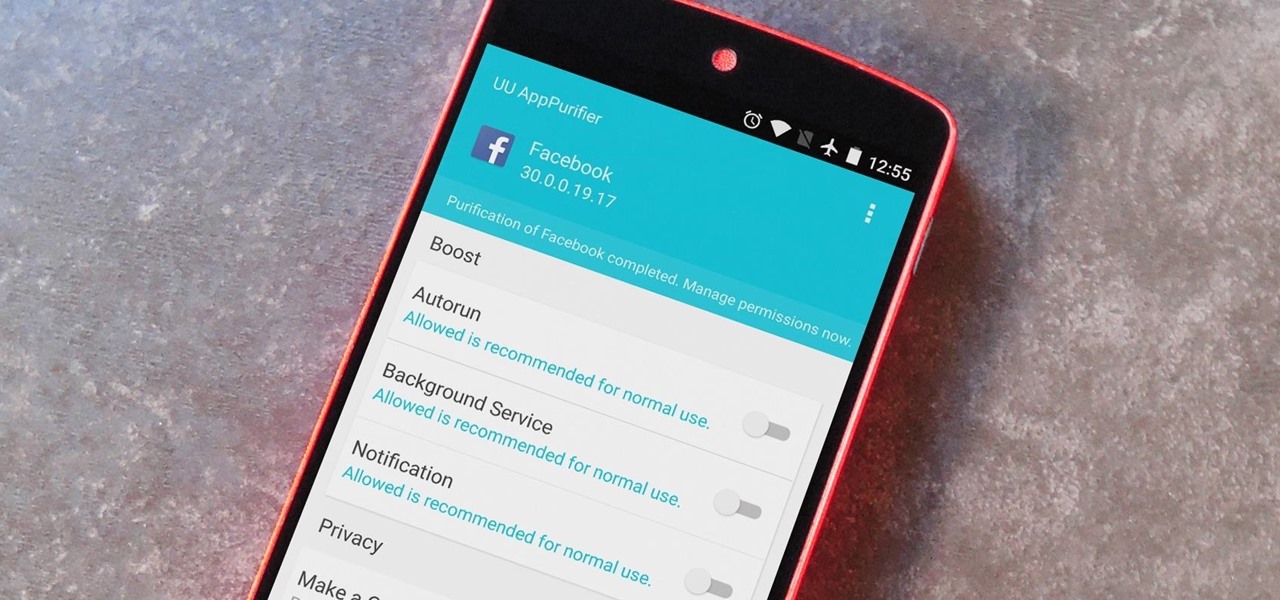
When it comes to app permissions, Android takes an "all or nothing" approach. You have no granular control over what data apps can access, so the only way to prevent an app from seeing your location or starting up on boot, for instance, is to not install the app in the first place.

Upon getting the new Samsung Galaxy S6 Edge here at the office, there are countless things we wanted to do before actually diving in and using the device. One of those things is removing all of the unnecessary pre-installed applications we never asked for.

With 16 megapixels and optical image stabilization technology, it's safe to say that the Samsung Galaxy S6 is well-equipped to take badass pictures. Packed with additional camera modes, like Panorama, Selective focus, and Virtual shot, there's always a way to capture an image as intended.
Whether it's for handling your business's social media account or just for personal reasons, like trolling an ex-girlfriend's page (not that I've ever done that) or posting on behalf of your pup, there are instances where having two different Facebook accounts on one device is simply easier than switching back and forth.

With the sheer number of pictures stored on my iPhone, using the tap gesture on the status bar is extremely convenient and time-saving when I want to reach the beginning of my Camera Roll album in the Photos app.

If you're jonesing to play some Super Mario Run on your Android phone, you might not be able to get your fix for some time—at least, until Nintendo figures out the best way to keep piracy down and security high. But if you can't wait for the first official appearance of Mario on Android, we've got the next best thing...
Cleaning the clutter off of your desktop every so often is a great idea. Unfortunately, that doesn't mean that you're actually going to do it. Whatever the reason, you may not have time to get everything organized, but luckily there is a way to temporarily "clean" your desktop in a hurry.
If you're a Trekkie, you might be surprised to find that Spock's popular Vulcan salute can actually be used as an emoji on your iPhone. With the public release of iOS 8.3, you'll now have updated unicode for more diverse emojis.

Get some tinfoil hats and make a time machine because we are about to go back to the 90s and learn about some phreaking.

HTC's fitness-tracking application, Fun Fit, has made its way to the Google Play Store for all to enjoy. And while fitness apps are a dime a dozen, Fun Fit offers what its name implies—fun. Like plenty of other fitness apps, Fun Fit is able to track calories burned, steps, distance, active time, walking time, and running time. Where the app differs is in its presentation.
Your iPhone's home screen is a tricky thing. You can sort your collection of apps in any order you'd like, but where you place those apps is a totally different story. App and folder placement follows a strict grid on iOS from left to right, top to bottom. No exceptions, and that's how Apple wants it. So you might think without a jailbreak you're stuck with this layout — but you're wrong.

With wearable tech becoming the latest trend in electronics, it's a shame that most smartwatches are locked down to one ecosystem. If you purchase a smartwatch, you can expect that it will not work with devices from competing manufacturers. That will be the case for the Apple Watch when the product finally hits shelves, and it has been the case for Android Wear devices like the Moto 360 for quite some time now.

Yes, they're called volume keys, but they can do much more than adjust your volume. With minimal effort, you can do some amazing things with these physical buttons, like secretly record videos, toggle on your flashlight, scroll through pages, control your music, and much more. And while using them to wake your screen is useful, let's take it a step further and show you how to use them to completely unlock your device, even if the screen is off.
Step 1: Introduction: Hello! Hackers

Welcome back my fellow hackers. Today I'm going to teach you how to preform an Idle Scan. You may be asking what is an Idle Scan. Its a very stealthy scan because you don't use your own ip you use a zombie (in computer terms).

Icebox cakes are some of the most satisfying, easy desserts to put together. This version made out of ice cream sandwiches takes the cake, literally, because the layers are almost pre-made for you. Simple and pretty when cut and served, it will be love at your first creamy bite. Depending on whether you want a layer of chocolate crunchies in your ice cream sandwich cake or not, this could be either a two-ingredient ice cream cake or a four-ingredient one. If you don't need the crunchy layer, ...

Welcome back, my amateur hackers! Over the course of the next year, we will be developing our own zero-day exploits. In my first article in this series, I introduced you to buffer overflows, which are the source of some of the most lethal exploits, particularly the "remote code execution," so we are focusing our exploit development here on a buffer overflow.
A group ironically called the "Guardians of Peace" hacked into Sony Pictures' computer systems and released a mountain of internal information such as medical records, leaked scripts, work complaints, and even celebrity aliases.

One of the golden rules to cooking a Thanksgiving turkey is to place it on a roasting rack before it goes into the oven. Missing this step and cooking it directly on the pan will burn the bottom of the bird, resulting in overcooked, dry meat.

Who says you have to cook on Thanksgiving? If you need a break, have surprise guests in town, or simply don't want to be in the kitchen cooking all day long, never fear: you have options.

You wouldn't send your GPS coordinates to a completely random stranger just because he or she asked you for it, right? So why are you constantly sharing your location (and other data) to apps on a daily basis?

Welcome back, my nascent hackers! We have spent a lot of time in previous tutorials focused on hacking the ubiquitous Windows systems, but the vast majority of "heavy iron" around the world are Linux or Unix systems. Linux and Unix dominate the world of Internet web servers with over 60% of the market. In addition, Linux and Unix servers are the operating system of choice for major international corporations (including almost all the major banks) throughout the world.

Welcome back, my budding hackers!

In my opinion, the greatest food hacks are the ones that help you cut way, way down on dishwashing. That's especially true when it comes to baked goods, which usually involves dirtying up a couple of mixing bowls, measuring cups and spoons, some kind of stirring implement, and the baking pan itself.

There comes a time in relationships when two people decide to move in together, and when this happens, you learn two things:

To prevent melted ice cream from leaking out of the pointy bottom of a cone, plug the hole up with a marshmallow before adding any ice cream on top. This will also give you a nice treat when you're almost finished, as the marshmallow will absorb some of the ice cream.

Welcome back, my budding hackers! When we are looking for ways to hack a system, we need a specific exploit to take advantage of a certain vulnerability in the operating system, service, or application. Although I have shown you multiple ways to exploit systems here in Null Byte, there are still many more exploits available that I have not yet shown you.