Video games and art have somewhat of a sticky relationship. Many video games have large teams of talented artists doing amazingly creative work, and yet the art community is only just beginning to utilize video games as art (sometimes). Perhaps if video games were shown not just as a medium of expression, but as a means of creating great art as well, the art community would be forced to consider it differently. The third part in the Hacked Kinect series will focus on the artistic possibilitie...

Since its inception in 2007, the Pwn2Own computer hacking contest has been challenging the vulnerability of mobile phones and web-related software. In 2010, the fruit of two full days of hacking came down to the exploitation of the following web browsers: Safari 4 on Mac OS X, Internet Explorer 8 on Windows 7, and Firefox 3.6 on Windows 7. The winners walked away with the successfully hacked computer, plus a cash prize, but they left one Godly browser intact: Google Chrome. Even the savviest ...

Geekosystem has generously assembled a handy list of 10 foods you can allegedly make in a coffee maker. Sounds kinda grimy to me, but my own mother passed this link along, so if mom thinks it's kosher, I'll give it a try.

Chris Marion's Guitar Hero hack is nothing short of genius. The pyro-gamer-maniac interfaced his guitar with a microcontroller hooked up to five flame shooters (translation: every time he presses a button, a giant flame is propelled into the sky). Click through for full instructions on building your own.

TSA agents are having a little too much fun, it's time for the rest of us to join in. More complicated (and more promising) than the see-thru video trick, Jeri Elsworth gives instructions for building your own hand-held TSA see-thru scanner with a $3 feed horn and some (admittedly hefty) technical know-how.

Two easy solutions for avoiding pesky drill dust. You will need: a Post-it and/or a disposable paper cup.

Apparently IKEA does not sell matches or lighters, so Helmut Smits was forced to improvise. Titled FLAMMA, this conceptual art piece is outdoor survivalism for the resourceful yuppie set.

Okay, here we go. Here is the deal. Bam, Knoxville, Dunn, Steve-O, Party Boy, Jeff Tremaine, and myself are dressed in old man faces, but wearing tshirts that say "Beer is Good" and wearing diapers. (Substitute speedos for diapers if you want). We are gathered around Jack Nicholson's Walk of Fame star. The "Nicholson" is covered up by a taped "Ass" to make his star to say "Jack Ass". Because it is his star, it is only fair Jack Nicholson is with us too, also sporting the "Beer is Good" tshirt...

"Skimboarding in a Storm" displays some ultra cool camerawork, employing the relatively cheap and user friendly GoPro camera (also used in the clever Kitchen Timer Panning Time Lapse Hack).

If you have a great idea for a TikTok, you probably need to take your time to execute it perfectly. But what if something crazy and unexpected is happening in front of you, perfect for an impromptu video? You don't want to miss the action, but getting all the way to TikTok's camera might take too long — that is, if you don't know this trick.

If you want to root, it's step one. If you're a tinkerer, it's vital. It's Android's hidden "Developer options" menu, and it's definitely worth taking 30 seconds to unlock.

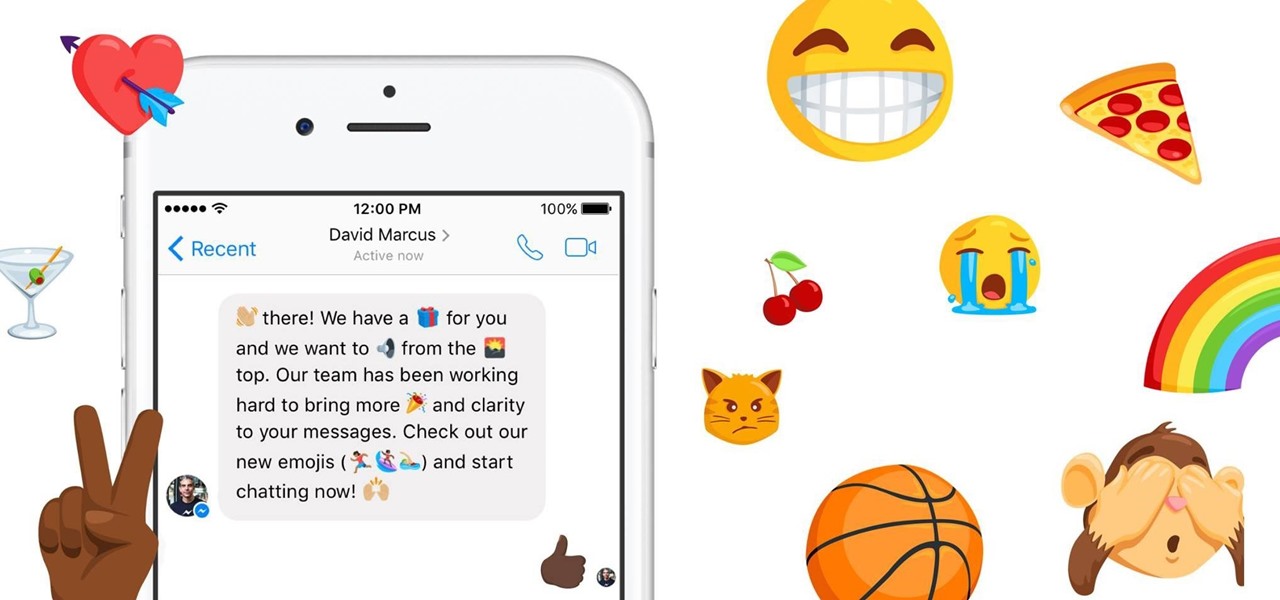
In an effort to be more inclusive, Facebook will release over 1,500 ethnic and gender diverse emojis for its Messenger app across all platforms on June 2nd, 2016. The update includes the usual emoji diversity inclusions, such as skin tone choice for faces and hand gestures, and widened gender roles such as female police officers, surfers, and runners, to name just a few, along with fancier "gender-agnostic" options. Beyond the diversity choices themselves, the update will allow you to set a c...
I just came across an article on Reddit about some iOS malware called XcodeGhost that has affected many apps in Apple's Chinese App Store. After reading more about it, I thought it was pretty incredible how the attackers had pulled this off. As the name might imply, the malware was not loaded onto iOS devices because the iOS devices were directly hacked, but rather it was the Xcode versions used by the developers of legitimate apps that were hacked! Basically, some devs were using hacked Xcod...

Hi! In case you missed it, on Reddit is pretty good article about attack on

FBI has taken down a notorious hacking forum called "darkode" where cyber criminals bought, sold and traded hacked databases, stolen bank accounts, and malicious software that steal information from other computer systems and helped each other to infiltrate other computers. The FBI called the site one of the most serious threats to data security in the world. criminal charges has been filed against 12 individuals who were associated with the forum and the investigation is still ongoing, more ...

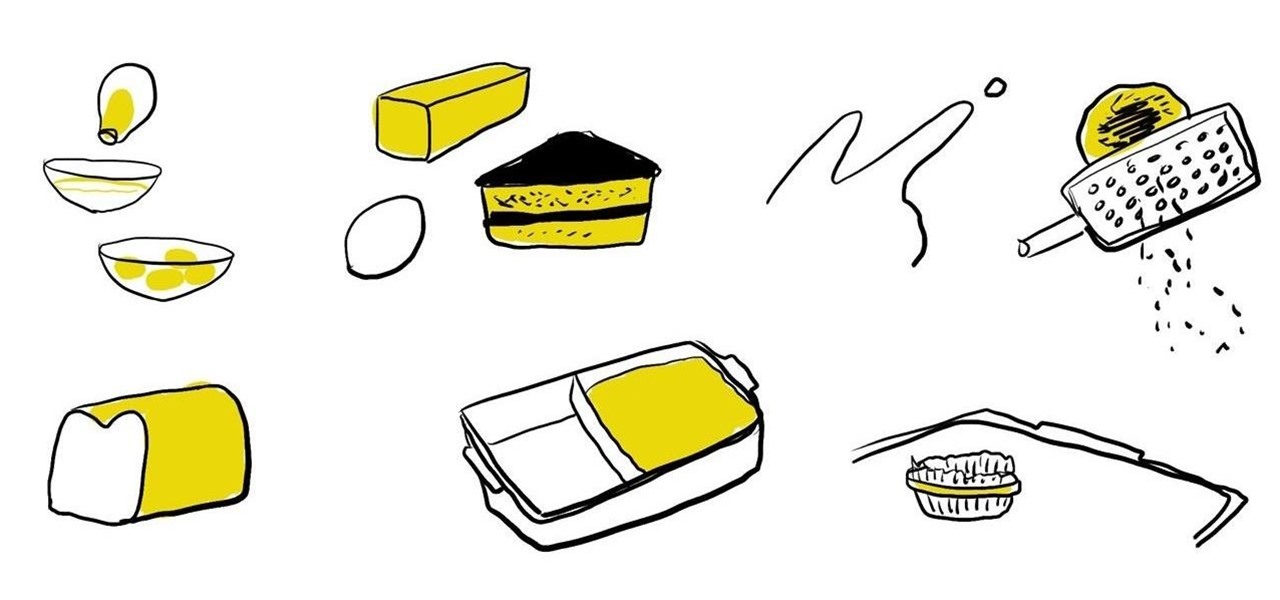
Did you accidentally burn the edges of your freshly-baked cookies or muffins? Rather than throwing them away, salvage the good parts by using a cheese grater to shave off the burnt ends before serving.

Pretty much all of your cleaning supplies can be found in your kitchen or medicine cabinet for dirt cheap. White vinegar can be used to clean shower head deposits and your dishwasher on an empty cycle. Ammonia can be used to clean the gunk off your stove burner grates. And citrus fruits can be used to clean bathtub rings and dull sink faucets.

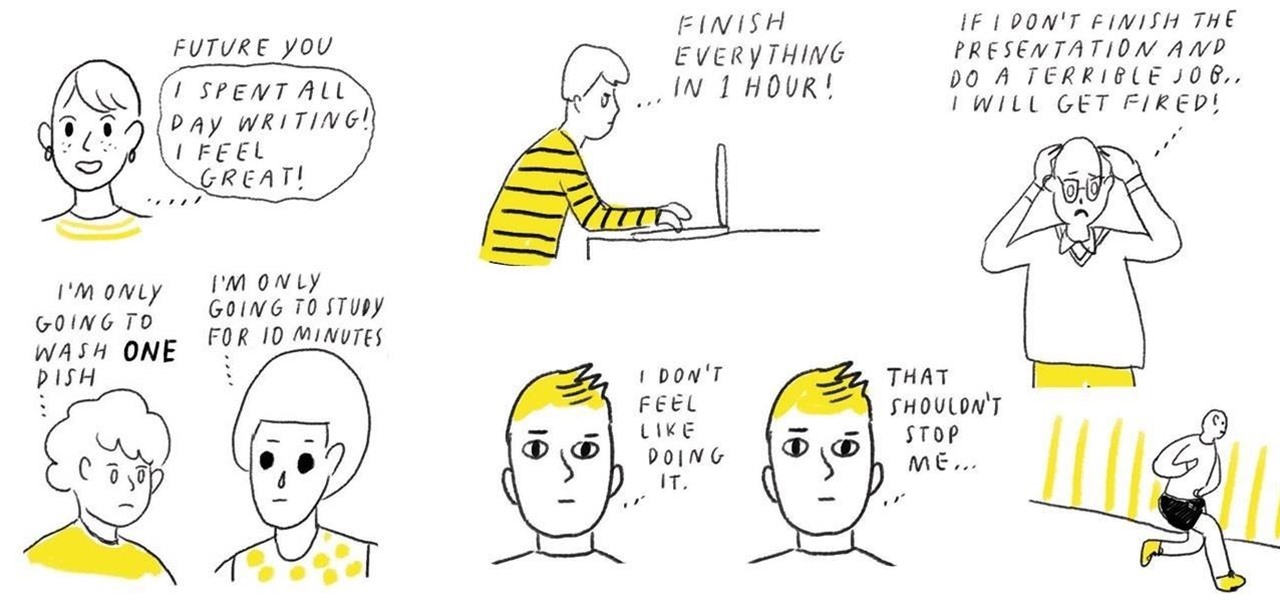
Are you dreading a big, tedious task on your to-do list? Commit to only doing 10 minutes of it or only the very first minimal step. By lowering the hurdle for getting the task started, it is very likely that once you start doing it, you won't feel so bad about getting the rest of the task completed.

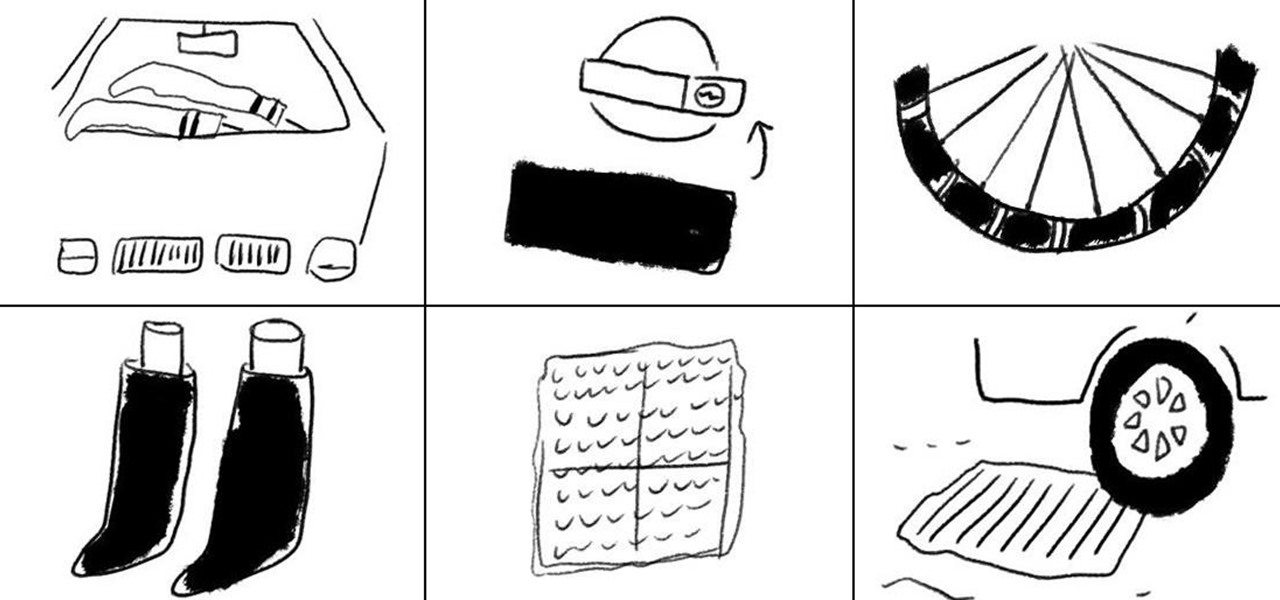
Need to bike around in cold weather to get to places? Winterize your bike by adding plastic zip ties around your tires to add more traction when you are biking through ice and snow.

Life hack your next outdoor picnic to cool your warmed drinks, keep flies away, and transport food efficiently from your home to your local park.

Each year, about 40% of all food produced in the United States goes uneaten and gets thrown away. Become a part of the solution and not the problem by practicing the following simple hacks to make your produce and perishables from the supermarket last for as long as possible.

When i went to class today, a good friend asked me a question. He wanted to know what the best hacking software was to basically do everything. What i told him was this: Well there isn't an "Ultimate" tool boot there are a number of tools which deserve a "Medal." So what i'm trying to say here... What are some of the best hacking tools available right now? For starters i created a list with some of the tools.

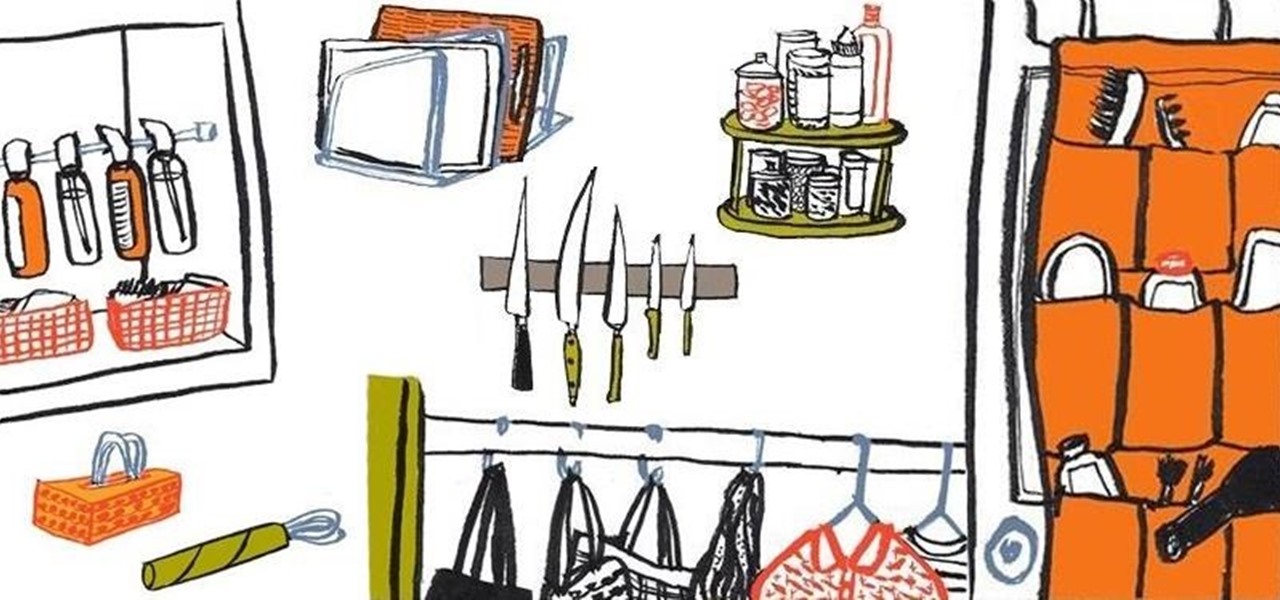
If you're like most people, you probably wish you had more space in your home. With a few clever organizing hacks, you can free up more space in your living space and feel more in control of where and how you store your possessions.

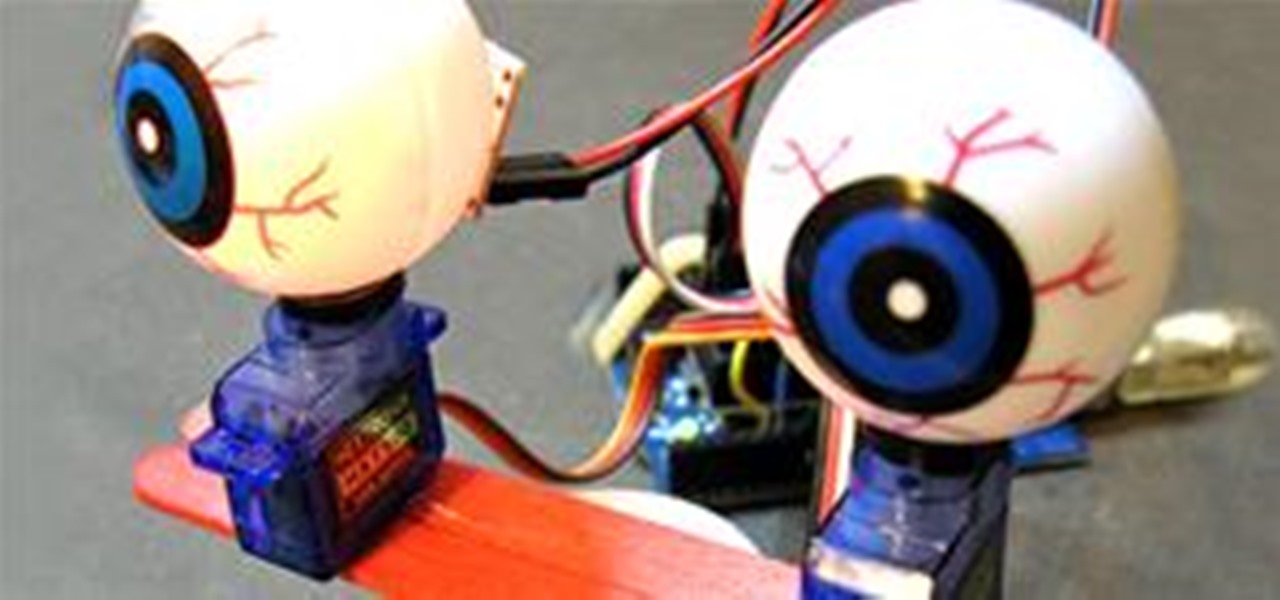
Todbot offers instructions for making your own Arduino shifty-googly Halloween eyeballs. Perfect to pop inside a pumpkin or skull.

UGC beauty How-To video is a true YouTube phenomenon. Considering the internet's tendency toward the male bias, the complete domination of beauty in YouTube's How To & Style section is noteworthy.

NK5 is a genuine wizard with an old monitor. He's hacked together everything from an electric kitty fence to a Halloween hologram using the guts of an old CRT.

This ultra clever mod of household junk makes for an ingenious variation on the carnival classic.

Looking for a cheap addition to your KGB-esque arsenal of spyware? Here's a hack using a webcam and a telephoto lens to record some far out sights. Build a $40 USB spy telescope.

SQL injection is a common web application attack that focuses on the database backend. WebGoat is a deliberately insecure J2EE web application maintained by OWASP designed to teach web application security lessons. I plan to use WebGoat for a few future videos. This first WebGoat video will show the basics of installing WebGoat and doing two of its SQL injection lessons. Hack websites with SQL injection and WebGoat.

This four chapter tutorial has proven popular among our staff.

This instructional video will show you how to get all of the change out of a vending machine! Who needs Coke or Pepsi when you can have coins? Then, you can get all of the soda you want out of that vending machine.

Tired of touch-tone hell? Get human with our cool phone hacks and cheats with the tips from this how-to video. Become a life hacker - we'll show you how to find phone numbers, cheat the computer and hack the call center system with our hacking tools. Watch this video tutorial and learn how to hack a call center telephone system. Hack a call center telephone system.

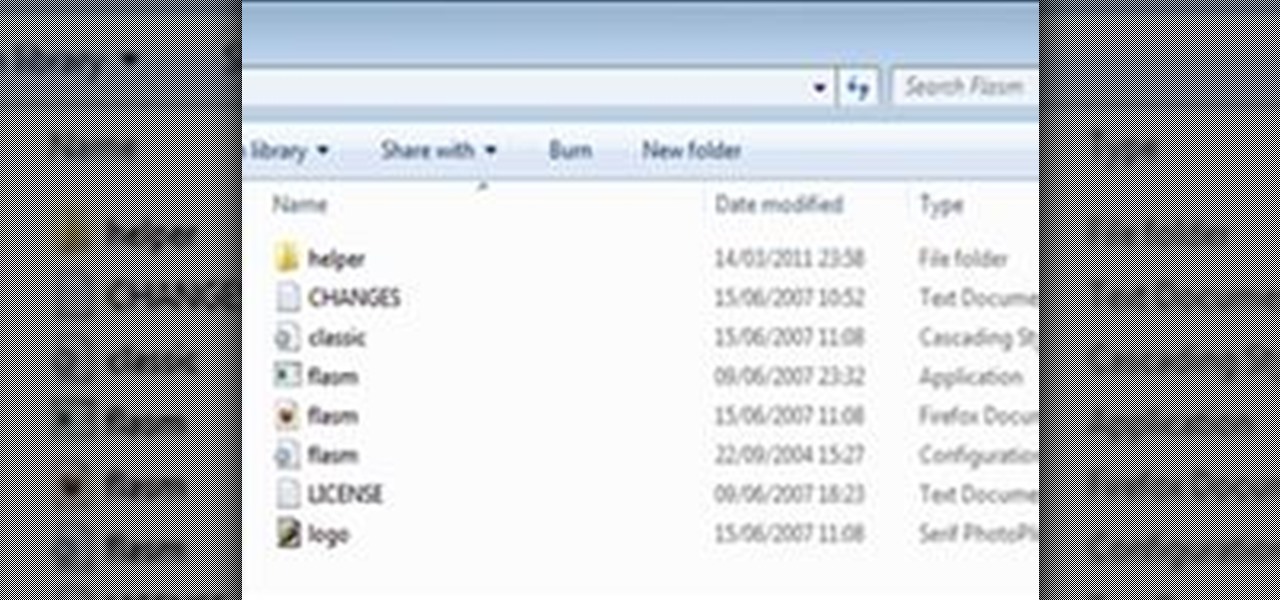
This is a tutorial showing you how to easily hack flash (.swf) games! You only need two things:

Build a 10-12 foot high half-pipe in the middle of the ice rink. Everything is normal about the ramp with the exception that the flat area is not wood, it's ice. So, essentially it is two quarter-pipes facing each other to make one full half-pipe. Get a bunch of skaters and BMXers to try it out. It's a little like the gauntlet . . . perhaps have hockey players fire pucks at them while they are skating.

Light up your keyboard with this illuminating tutorial from Make Magazine's Kipkay. To get started on this hack, which should take roughly a half an hour and cost no more than $5, you'll need the following: (1) a regular computer keyboard (most any model will do), (2) a screwdriver, (3) a drill, (4) telephone wire, (5) heat shrink tubing, and (6) two 5 mm high-brightness, white LEDs. For comprehensive, step-by-step instructions on building your own light-up keyboard, simply watch this hacker'...

Prank your friends by hacking some ordinary bubble gum to ooze fake blood when someone chews it. It can take 3-4 days for the "blood" to disappear. Use this as inspiration for one of your April Fools Day pranks! Make bloody prank bubblegum.

Grab your thinking caps and get your hack on. Null Byte is officially seeking contributors on a weekly basis who are willing to take the time to educate the Null Byte community on anything, from hardware hacks to life hacks. Contributors that write tutorials will be featured on the Null Byte blog, as well as the front page of WonderHowTo (providing it's up to par, of course).