Do you need proxy access, but cannot have it for some reason? The most common perpetrator behind the issue is the network you're trying to access the pages from. Some networks will block websites, then go as far as filtering out all of the web queries for terms like "proxy" because it can get around their filter. Quick web proxies can be used for tons of other things, though.

Last Friday's mission was to accomplish solving HackThisSite, realistic 3. The third mission in a series of realistic simulation missions was designed to be exactly like situations you may encounter in the real world, requesting we help a friend restore a defaced website about posting peaceful poetry.

We're aiming for this to be one of the last HTS mission announcements, at least for now. As soon as Null Byte finds a server to play with, we are going to start doing root the box competitions, which is like king of the hill, except you have to hack a server and maintain access. Each server will have numerous known security holes. But, for now, back to the normal flow of things...

We're officially seeking Null Byters on a weekly basis who are willing to take the time to educate the community. Contributors will write tutorials, which will be featured on the Null Byte blog, as well as the front page of WonderHowTo (IF up to par, of course). There is no need to be intimidated if you fear you lack the writing skills. I will edit your drafts if necessary and get them looking top-notch! You can write tutorials on any skill level, and about anything you feel like sharing that...

The community tore up the first realistic mission last week. You've applied the techniques learned in the basic missions to a real scenario, so I'm pretty content. The realistic missions are where the learning gets intense and where we can apply real knowledge to extremely realistic situations. We will also be continuing the normal Python coding and hacking sessions. These sessions are created to bring our community together, to learn from each other, and grow together. Everyone is welcome, f...
We're officially seeking Null Byters on a weekly basis who are willing to take the time to educate the community. Contributors will write tutorials, which will be featured on the Null Byte blog, as well as the front page of WonderHowTo (IF up to par, of course). There is no need to be intimidated if you fear you lack the writing skills. I will edit your drafts if necessary and get them looking top-notch! You can write tutorials of any skill level, about anything you feel like sharing that is ...

Community byters, it's time to get serious. We are finally moving on to the realistic missions in HackThisSite. This is where the learning gets intense and where we can apply real knowledge to extremely realistic situations. We will also be continuing the normal Python coding and hacking sessions. These sessions are created to bring our community together, to learn from each other, and grow together. Everyone is welcome, from novice programmers to aspiring hackers.

Null Byte is looking for forum moderators! Last Friday's mission was to accomplish solving HackThisSite, basic mission 9. This mission delves a little further into Unix commands and remote directory traversal (which is just a fancy term for going through folders blindly).

Lots of people are going to be getting the latest iOS devices this holiday season. But what good is a portable device if you don't hack it? Jailbreaking on the latest stock iOS, version 4.3.5, is a bit of a trivial endeavor. Not many people know how to downgrade from this firmware to a firmware that can be jailbroken (pre-iOS 5). If you want the added functionality and the complete control over your device that comes with jailbreaking, then read on.

Gamers like myself who have switched back and forth between Skyrim on PC and Xbox lack the ability to share game saves. This really sucks. I love playing Skyrim on a console. It's a very comfortable, easy and relaxed gaming experience. You don't have to worry about your frame rate being optimized, or wrist pains from using a keyboard. However, gaming on the PC can allow you to use texture enhancing mods and get an overall smoother experience due to a lack in glitches and bugs that plague the ...

Welcome to another Community Byte announcement from Null Byte! The goal of the Community Bytes is to teach people in a co-operative, hands-on manner. Learning from experience and immersing yourself in a subject is the best way to learn something foreign to you, so that is exactly what we do! In our sessions, we have started to both code and complete HTS missions. This means that there is something for everyone here, so make sure you join us.

Welcome to another Community Byte announcement! For the past few Community Bytes, we coded an IRC bot, and hacked it. Then, we created a web-based login bruteforcer! This week we are going to start something a bit different. We are going to start going through the missions at HackThisSite one-by-one each week, starting with the basic missions.

Welcome to the second Goonight Byte! Our second coding session was kindly hosted by th3m, so props to him for letting this happen.

Giveaway Tuesdays has officially ended! But don't sweat it, WonderHowTo has another World that's taken its place. Every Tuesday, Phone Snap! invites you to show off your cell phone photography skills.

Linux can have the most beautiful interface in the world, because it is simply what you make of it. You can change every little detail with relative ease because that's what Linux is all about: Freedom and OpenSource.

This Null Byte is a doozey.

Sturdier than sewing thread and far less cumbersome than metal wire, dental floss has an amazing multitude of practical uses that can be used for baking, cooking, interior decorating, and more.

Firesheep caused quite a stir when it was released last October, giving both hackers and non-hackers instant access to people's account information when on a public Wi-Fi connection. When logged into an insecure website on the same network as someone with Firesheep, you're giving them access to the cookies that keep you logged in. This is called session hijacking, and grants them easy access to your accounts, like Facebook, Flickr and Twitter. Now, there's an even easier way to do this—a mobi...

Giveaway Tuesdays has officially ended! But don't sweat it, WonderHowTo has another World that's taken its place. Every Tuesday, Phone Snap! invites you to show off your cell phone photography skills.

Giveaway Tuesdays has officially ended! But don't sweat it, WonderHowTo has another World that's taken its place. Every Tuesday, Phone Snap! invites you to show off your cell phone photography skills.

Nintendo's Wii Remote came close, but never has a video game peripheral garnered such adoration from the hacker community than the Kinect.

It seems the French have carefully observed the hacking achievements of one super clever Carnegie Mellon grad, turning his hack into a modern iPad application-to-be.

Hacking can't be that hard, can it? At least, that's what it seems like thanks to movies like Hackers, The Net and that last Die Hard flick. Even the Jurassic Park girl's got some game. They all look like they're typing 20wpm, yet can generate a screen full of code in the blink of an eye. Amazing. As long as they're some isolated computer nerd who's glued to their PC all day long (which is pretty much all of us these days, thanks Internet), they're a bona fide hacker.

In 2007, Nintendo introduced the world to motion control video games with the Wii. Microsoft and Sony built on Nintendo's phenomenal success and released their own motion control products for the XBox 360 and Playstation 3 late in 2010: the Kinect and the Move. The Move is basically an improved Wiimote that looks like a sci-fi Harry Potter wand, but the Kinect just might be the most important video game peripheral of all time.

By now, many of you may have heard about iPhone tracking and recording your location data, but is there anything else being extracted from cell phones without our knowledge? If you're a Michigan state resident, the answer is an alarming "maybe".

When the iPad 2 was released earlier this month, as to be expected there was a whole lotta buzz. And for good reason—while the the newest version shares the same price tag as the old, it boasts some significant new features. In case you missed it, here's a quick overview:

It's gigantic! It can handle over 100 simultaneous touch points! It has a curvature of 135 degrees! And best of all, it is not the newest, insanely expensive gadget to hit the market. Instead, this touchscreen was hacked together with a bunch of PCs, video cameras, projectors and cheap infrared illuminators at the University of Groningen, in the Netherlands. It works like this: "The cameras, illuminators and projectors are all placed behind a large, cylindrical screen (formally used as a 3D t...

Meet Newstweek, a hidden device engineered to hack news items being read at public WiFi hotspots (cafes, libraries, airports, etc.). Both nefarious and tech-saavy, the ingenious mechanism wasn't fathered by a group of web hackers, but rather a pair of Berlin artists, Julian Oliver and Danja Vasiliev. The duo are interested in exploiting the "trustworthiness" of big media outlets in order to demonstrate the vulnerability of relying on just a few dominant networks.

Aram Bartholl over at F.A.T. is pretty pissed because MoMA is discriminating against internet artists. As most New York-based working artists know, MoMA offers annual membership for only $35 (compared to the standard rate of $75) to artists who can provide "credentials" that prove legitimacy. Though the offer isn't publicized on the MoMA site, word on the street is "credentials" equates to "a letter from the gallery or an announcement for one of the artist's shows within the past two years" (...

This past Sunday, a group called Gnosis launched a massive hacker attack on Gawker media, one of the web's most popular blog networks (Lifehacker, Gizmodo, Jezebel, io9, Jalopnik, Kotaku, Deadspin and Fleshbot). 1.3 million registered users' passwords were compromised, and 188,279 of them were decoded and made public. The biggest takeaway? Many Gawker denizens use downright dumb passwords. (Guess they didn't see their own Lifehacker's story on avoiding such a thing.)

PopSci's Gray Matter explains how to "hack light", a simple project that calls for glow sticks, diagonal cutters and Drano. Here's the science behind it:

Every day of the week, WonderHowTo curators are hard at work, scouring the web for the greatest and most inspiring how-to videos. Every Friday, we'll highlight our favorite finds.

Have a lock on your bike or shed but you have lost the key? Watch this hacking how-to video and learn the art of picking a lock using a common kitchen utensil. Yes all you need to crack open a lock is a fork for your kitchen drawer. Follow along and see how easy it is to pick any lock with a fork. Open a lock using a fork.

Apple's iOS doesn't have the best reputation when it comes to customization, but with every new iOS version we get, there are more options to personalize. Your iPhone comes packed with plenty of tweaks and hacks to make the device feel truly yours, and one of those is a fun yet useful mod that adds on and off icons for toggle switches on your iPhone.

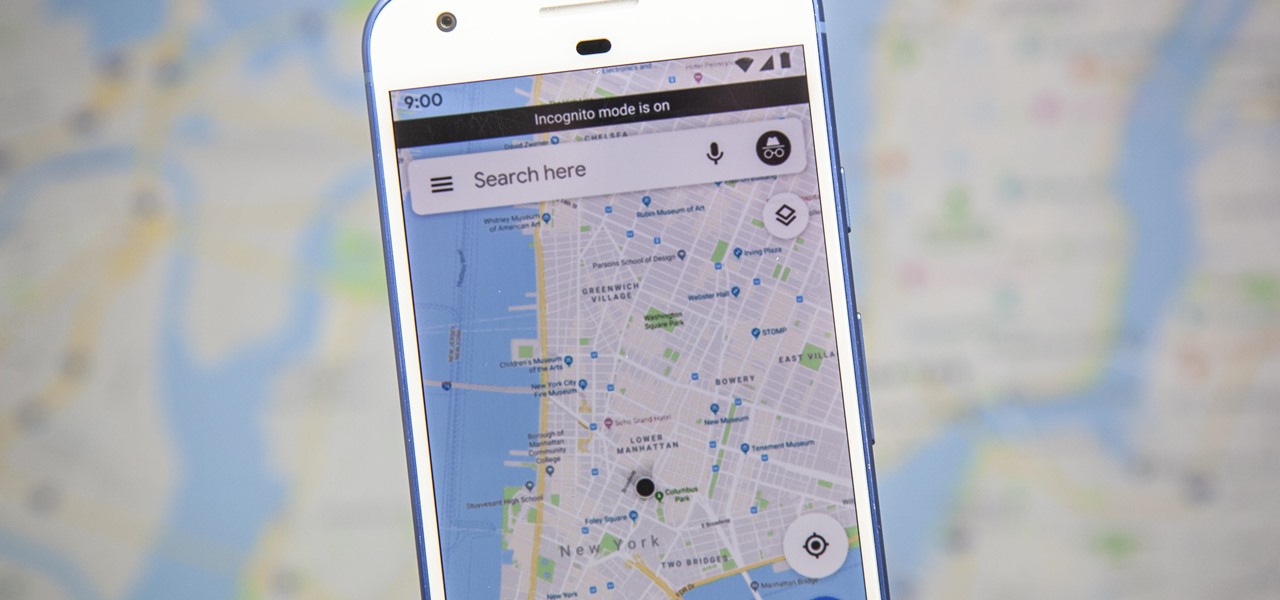
Google just recently added an incognito mode feature to Google Maps for iPhone and Android. With that, you can now use Maps in private at any time, which means you can browse and search with peace of mind.

Apple announced iOS 12 during WWDC 2018. While it will be some months before the official version releases to the public, you can still enjoy some of the new additions now. For example, you can get the new wallpaper introduced with the update, whether you're using an older iPhone or an Android device.

If you're someone who shares your Hulu account with friends and family, let me be first to acknowledge you as a hero. That being said, heroes have messy profiles — your account quickly reflects the viewing habits of your shared users, making it difficult to keep your watch history yours. That changes now, with new tools from Hulu.

Fans of Fortnite Battle Royale were understandably ecstatic when the smash hit arrived on mobile. While at first the game was restricted to invite-only, Fornite is now available to all on iOS. If you're just starting out, you're going to want to check out these expert tips to gain an advantage over the other new players.

Most phones adjust the ringtone and notification volume by default when you press the physical volume buttons. If media is playing, then the volume rocker will adjust media volume — but only after the first few seconds played at the previous volume level. This has been a point of frustration for many years, but thankfully, the Galaxy S9 lets you change the default volume control.

On most web browsers, opening a tab requires two or three taps. Not with Samsung Internet. While the app offers a few different ways of getting it done, there's a trick that lets you open a tab with virtually no effort at all. It's one of the reasons Samsung Internet is one of the best browsers on Android.