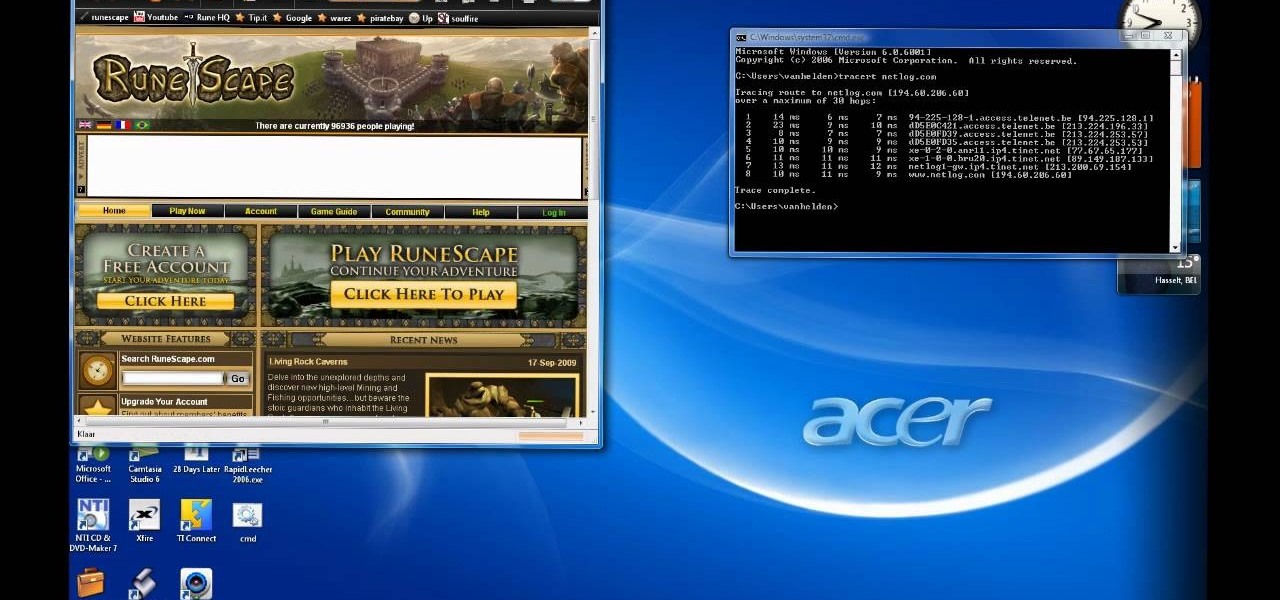
In this episode of Full Disclosure we are explaining the website attack known as Cross-Site Scripting (XSS). Cross-Site Scripting is a type of security vulnerability that affects web applications that do not sanitize user input properly. This kind of vulnerability allows an "attacker" to inject HTML or client side script like JavaScript into the website. Cross-Site Scripting is most commonly used to steal cookies. Cookies are used for authenticating, tracking, and maintaining specific informa...
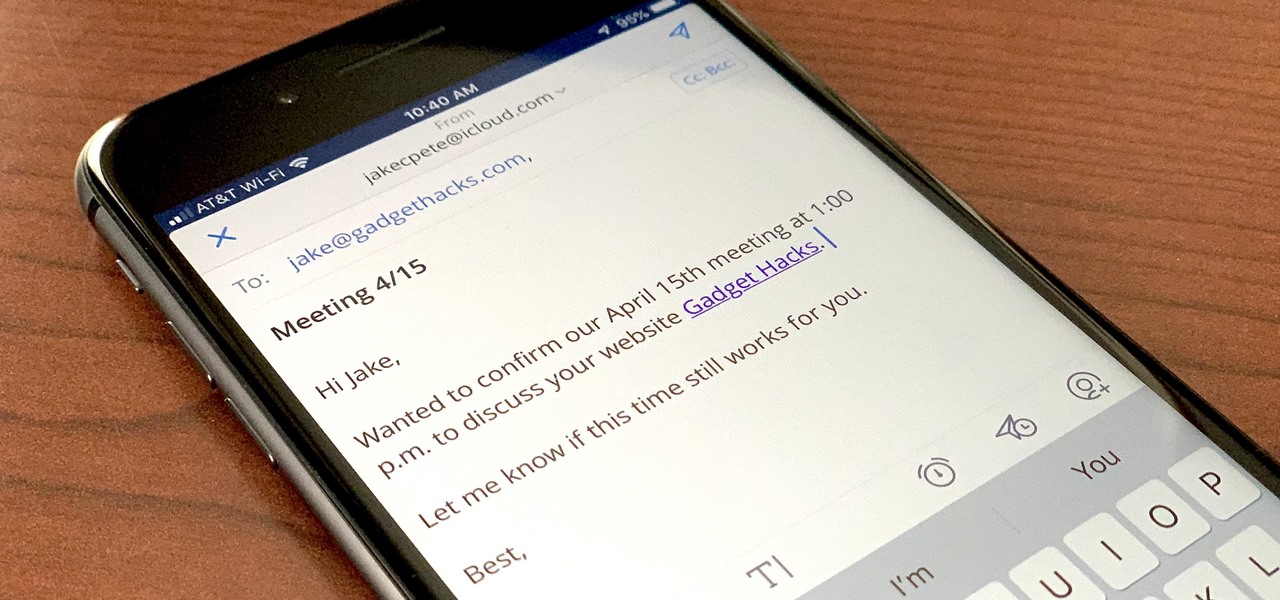
If you're a long-time Spark user, you'll know that one of the only drawbacks to the app used to be its lack of rich text-editing tools such as hyperlinking. If you needed to link out to a site in an email, your best bet was to grab a computer to get the job done. Well, close those laptops and shut down those PCs — Spark corrected this issue, implementing support for hyperlinking right into the app.

Last year, Razer kicked off a new trend by building a smartphone from the ground up with mobile gamers in mind. At the time, many thought the Razer Phone solved a problem that no one really had — but a year later, we're starting to see that gaming phones are perfect for more than just Fortnite players.

Nmap is more powerful than you know. With a few scripts, we can extend its functionality beyond a simple port scanner and start to identify details about target servers sysadmins don't want us to know.

It's been a long road, but the guys over at CoolStar have finally come up with a stable, semi-untethered jailbreak for 64-bit iPhones, iPads, and iPad touches running on iOS 11.2 up to 11.3.1, with the latest update extending coverage to 11.4 beta 3. So if you've held off on updating to the latest iOS 11.4.1, your patience has finally paid off.

Don't think because your MacBook is using FileVault disk encryption your device is secure or immune to hackers. Here's how to find out if that FileVault password is strong enough to withstand an attack from a motivated attacker.

The Drug Enforcement Agency (DEA) has been purchasing spyware from the Milan-based Hacking Team and its US subsidiary Cicom USA since 2012. Public records reveal invoices between Cicom USA and the DEA that have ranged between $22,000 to $575,000 from 2012 to 2015.

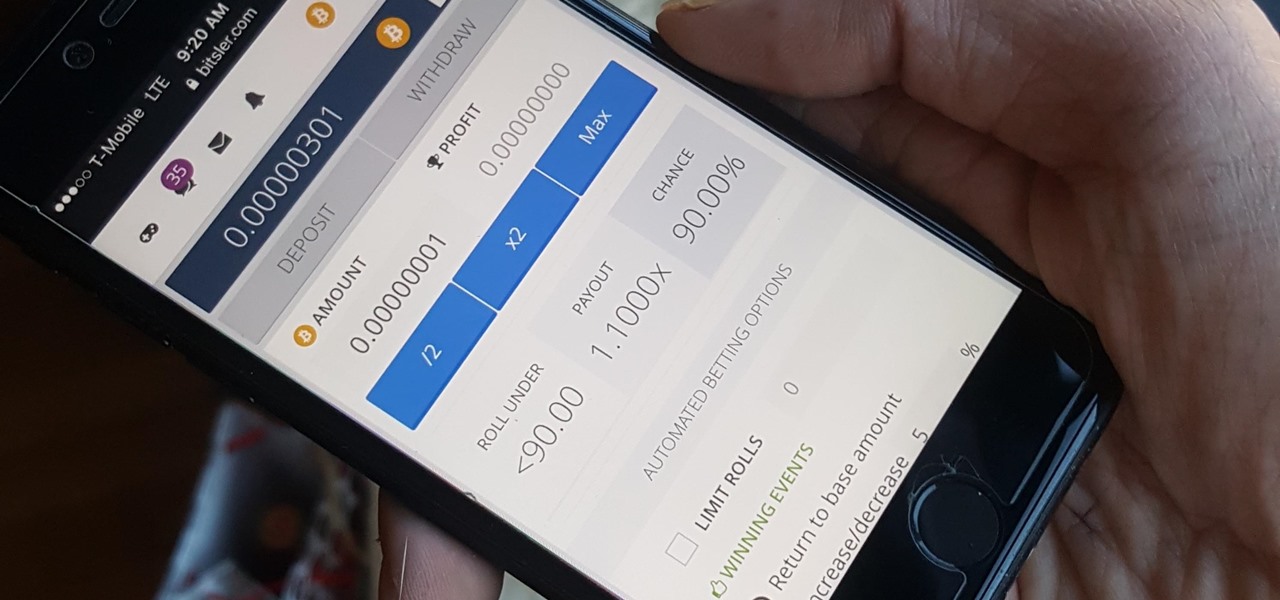
Bitcoin, the decentralized cryptocurrency notorious for its status as the currency of the dark web, seems to be shedding its shady past and is now enjoying soaring highs not seen since 2014. The highly volatile online commodity reached parity with an ounce of gold back in March amid speculation of a pending ETF approval from the Federal Trade Commission. Since then, Bitcoin has doubled in value and analysts predict a bitcoin could reach $100,000 in value in 10 years.

There are two types of Halloween lovers: Those who like culturally-relevant costumes and serving precious ghost cupcakes, and those who live to freak their friends the hell out in the most disgusting way possible.

Welcome back, my greenhorn hackers! The Holy Grail of any hacker is to develop a zero-day exploit—an exploit that has never been seen by antivirus (AV) and other software developers, as well as intrusion detection system (IDS) developers. In that way, you can exploit systems with your newly discovered vulnerability with impunity!

The end of a weekend can be depressing knowing just how bad Monday morning will be when you get back to work, but that feeling is tenfold when coming back from a lengthy vacation with zero work responsibilities.

Welcome back, my fledgling hackers! Over the years, we have examined multiple ways to own, exploit, or compromise a system. On the other hand, we have not spent a lot of time on denial-of-service (DoS) attacks.

Welcome back, my tenderfoot hackers! Recently, Microsoft released a new patch (September 8, 2015) to close another vulnerability in their Windows Vista, 7, 8, and 8.1 operating systems. The vulnerability in question (MS15-100) enabled an attacker to gain remote access to any of these systems using a well-crafted Media Center link (MCL) file.

Welcome back, my amateur hackers! Over the course of the next year, we will be developing our own zero-day exploits. In my first article in this series, I introduced you to buffer overflows, which are the source of some of the most lethal exploits, particularly the "remote code execution," so we are focusing our exploit development here on a buffer overflow.

Life hacks are tips and tricks to help make life easier. Shortcuts and clever workarounds for life's daily problems. Sometimes common sense isn't so obvious until you've actually seen it. In this video, I'll be sharing with you 10 life-changing hacks you can use right now, from finding your lost smartphone to sleeping better at night.

Welcome back, my tenderfoot hackers! Not too long ago, I showed how to find various online devices using Shodan. As you remember, Shodan is a different type of search engine. Instead of indexing the content of websites, it pulls the banner of web servers on all types of online devices and then indexes the content of those banners.

Welcome back, my neophyte hackers! Many newbie hackers seem to be confused regarding the process or methodology to employ a successful hack. Most want to simply go straight to the exploit without doing the due diligence to make certain that the hack will work and you won't get caught.

Welcome back, my novice hackers! We've done a number of tutorials using one of my favorite hacking tools, Metasploit. In each of them, we've used the msfconsole, which can be reached through either the menu system or through simply typing "msfconsole" from the terminal.

Welcome back, my tenderfoot hackers! So many readers in the Null Byte community have been asking me questions about evading detection and hacking undetected that I decided to start a new series on digital forensics.

Welcome back, my fledgling hackers! One of the first issues any hacker has to address is reconnaissance. Before we even begin to hack, we need to know quite a bit about the target systems. We should know their IP address, what ports are open, what services are running, and what operating system the target is using. Only after gathering this information can we begin to plan our attack. Most hackers spend far more time doing reconnaissance than exploiting.

Welcome back, my nascent Hackers! In my last blog, we looked at a passive way to gather information necessary for a hack. The advantage of using passive recon is that it's totally undetectable, meaning that the target never knows you're scouting them and you leave no tracks. The disadvantage, of course, is that it's limited to only some websites and not entirely reliable.

Make a cool confetti cannon that's great for concerts, parties and special events! Kipkay demonstrates how to hack together this high powered cannon. Confetti bombs are super fun, pay attention to learn how to make your own confetti cannon.

Cheat Engine will help you win on Fish World! A little hacking never killed anyone, but it has made them richer, so see how to hack Fishworld now with this awesome Facebook Fish World cheat.

Level up on Happy Aquarium by hacking it with Registry Helper. Huh? No Cheat Engine? See for yourself. This won't work for all computers, so test it out for yourself.

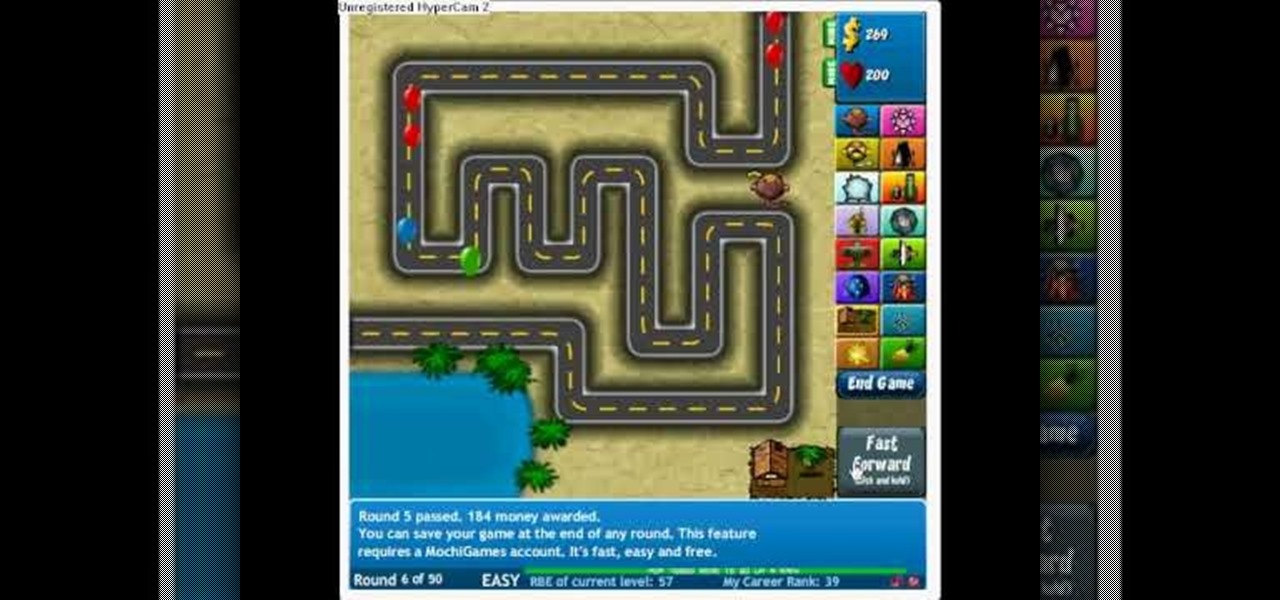
Bloons Tower Defense 4 cheats are here. And you guessed it… this one uses Cheat Engine. If you want to hack the game, you have to know how to do it, and Cheat Engine can be kind of a complicated process if you've never used before.

Create a miniature hover craft from the fan, polystrene or Styrofoam plate, batteries and double-sided scotch tape. It really works. Powered by two 9 volt batteries you can use paper plates for the body of the hovercraft if need be. This is a cool cat toy or just a household hack.

Interested in some good clean fun? With this hack from Japan, you'll learn to operate a Roomba vacuum cleaner remotely using a Nintendo Wii balance board with a Bluetooth serial adapter. Watch this tutorial and build your own Surfin'ba today!

Have you ever seen a steam candle? It's essentially a simple-as-pie steam engine that revolves on top of a water surface. They are relatively easy to make if you know how to do it. Take a look at this instructional video and learn how to "hack" together your own steam candle.

We've all seen the popcorn cell phone video. Now, we have the exclusive inside into how those videos were created. A microwave magnetron is strapped covertly to the bottom of the table. Then the prank is ready. Gather the phones and wait for the exciting reactions.

Check out this instructional video and learn how to hack a simple flashlight and transform it into a night vision flashlight! The items you'll need for the project cost less than ten dollars and you get a perfect night vision view. Watch this how-to video and learn how to build a night vision flashlight on the cheap.

This will show you how to hack an old two dollar alarm clock and transform it into a cool DVD clock! No, it doesn't play DVD's or CD's, but it still looks cool.

Make your very own hydrogen (and oxygen) generator with a 9V battery, copper wire, and baking soda (or salt). Why? Who knows. Make sure to check your connections. For more information on this hack, including detailed, step-by-step instructions on assembling your own HHO generator, watch this how-to video.

TOUCHPAD HACK - This video tutorial shows how to transform a touchpad into a useful mini graphics tablet with some simple, everyday items. You will need a 1.5V battery, a small ball bearing, and a Philips head screwdriver. Watch this video tutorial and learn how to transform a touch pad into a miniature graphics tablet.

Ah, the alluring glow of the LED light. Whether you're looking to create a bit of romantic (albeit extremely geeky) ambiance, or you just want to have some extra emergency lighting around the house, a set of mini LED candles is a great thing to have. They also happen to be quick, easy, and cheap to make yourself. In this video, executive editor Mike Haney demonstrates how to do it.

If you are a photographer and are handy with a screwdriver and electrical tape, this is a really cool project to do. Basically, you "Frankenstein" a camera, taking a camera apart and rebuilding it with different lenses and the like, which makes for really cool photo effects.

Learn how to get free electricity from your home telephone line just by watching this video. Save money on your power bill, and hack into the electricity coming out of the phone jack. The phone company doesn't monitor electricity usage, so you can probably get away with this con. Check out this video tutorial and learn how to tap into the electrical energy source in your phone line.

Trying to focus on studying for your Stats final in the library but getting a serious ADD spell? Then make use of your time - while having a little fun with whoever else is in the library - by hacking into your computer's command prompt.

This video is specifically for the C530 Slate cell phone from AT&T, though this procedure will probably work on similar models of phone. You can hack, or jailbreak, your phone to allow you to use third party apps or switch to a different service provider. You will need a non-AT&T sim card for this hack to work (T Mobile is shown in the video). Then turn it on, hit the unlock key and then enter in your unlock code. Make sure you get it right!

In this tutorial, we learn how to hack Google with addons for the Mozilla Firefox web browser. They're easy to install and use and this video presents a complete guide. For more information, including a full demonstration and detailed, step-by-step instructions, watch this helpful home-computing how-to.