The pictures we upload online are something we tend to think of as self-expression, but these very images can carry code to steal our passwords and data. Profile pictures, avatars, and image galleries are used all over the internet. While all images carry digital picture data — and many also carry metadata regarding camera or photo edits — it's far less expected that an image might actually be hiding malicious code.
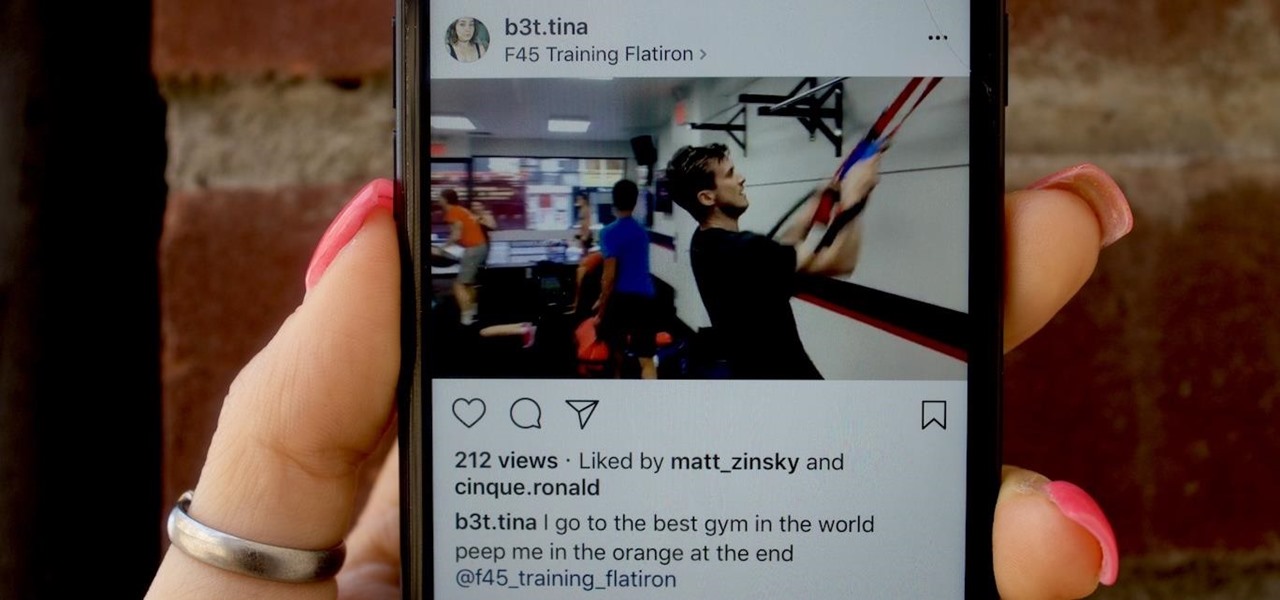
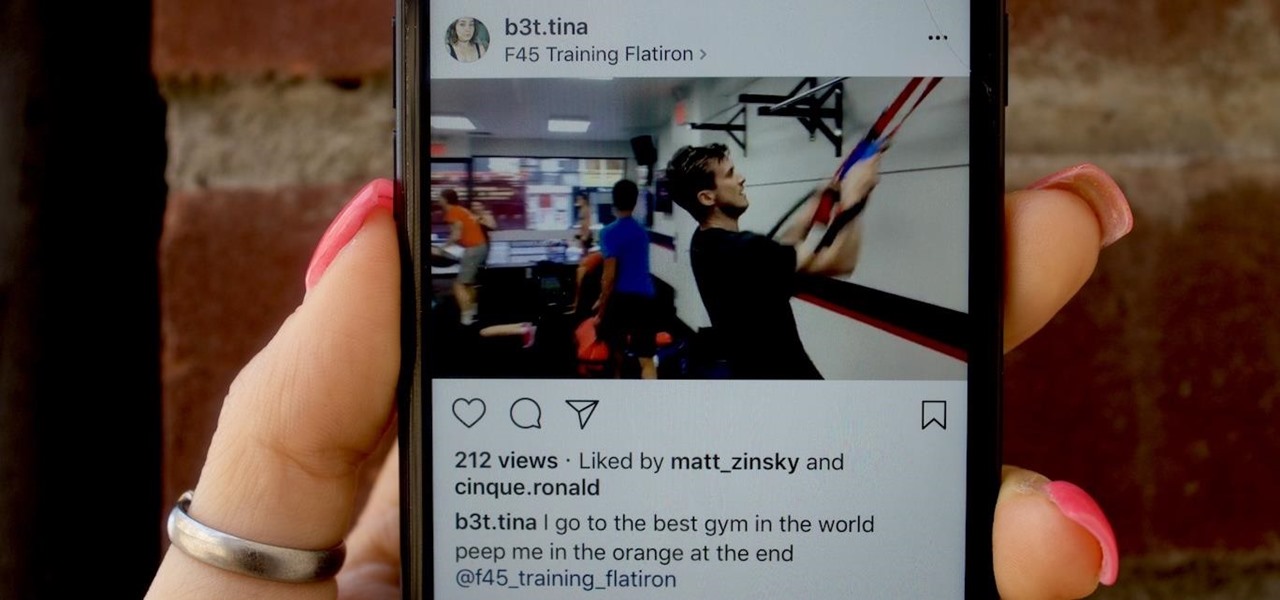
As you all journey along with me on my challenge to become some sort of Instagram expert, let me share with you one hack that is currently helping me out a lot. If you've ever wanted to put a line break in your posts, then keep on reading.

You were the chosen one, Snapchat! The new download numbers for the social media app show just how hard it will be to bring them back to the light after the rise of the Instagram empire.
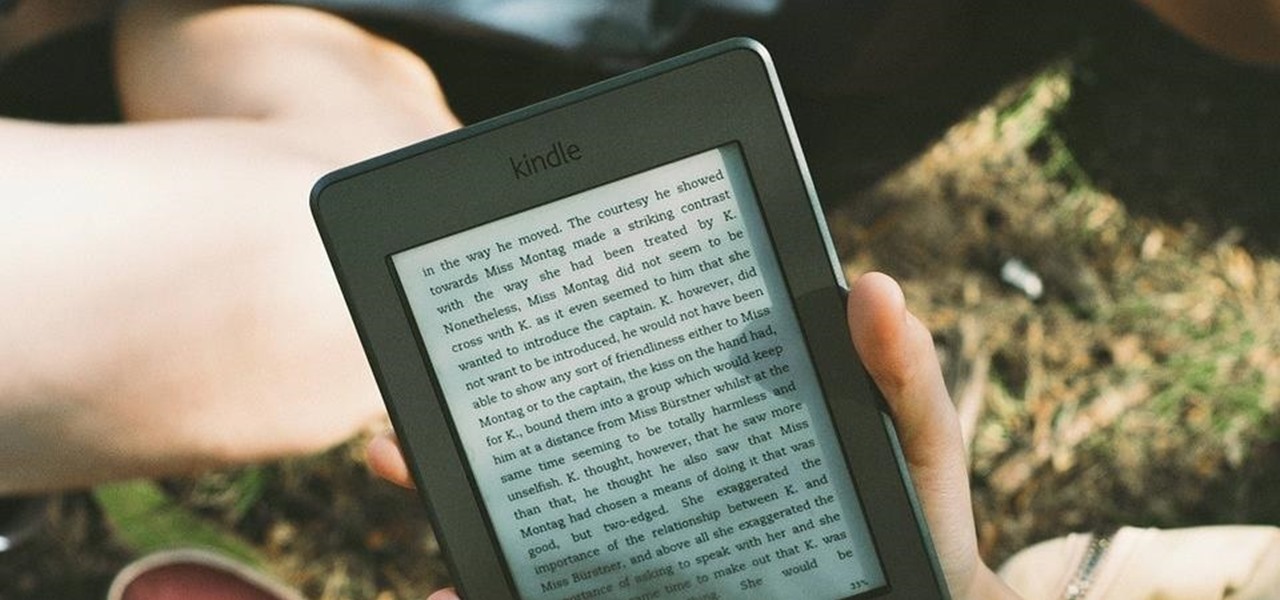
When I crack open a new book, I always make sure I have a pen and a highlighter nearby so I can mark away! Anything particularly witty, inspiring, or engaging gets highlighted, underlined, or circled. When I use the Amazon Kindle app on my phone, I do the same thing by writing notes and highlighting, but I often find it difficult to keep track of my markings.

UPDATE: It was previously reported that the OnePlus 3T 128 GB in Gunmetal would be discontinued. GSM Arena received an official rebuttal from the company which noted that the phone is not discontinued, but rather, out of stock. Though, it seems like the company has more of a problem keeping track with what its reps report, rather than its phone supply.

The Nokia 6 has been out since January, releasing in China before having a slow trickle of releases throughout the year. Despite announcing a global release, the United States never received a street date for the smartphone, and for all this time, Nokia has left us out to dry. Now, it seems, their phone could be on its way as the 6 has received its FCC certification.

Google's Gboard is by far the most popular keyboard available right now. Gboard lets you search almost anything—from regular Google searches, to emojis, and even GIFs—just by using your keyboard. The app even lets you share search results, saving you a great deal of time, which would've otherwise been spent juggling between apps and programs.

In my days as a hardware tech, I often came across motivated do-it-yourselfers who watched a video or two on how to repair a phone and thought that they'd give it a go. More often than not, they failed miserably and damaged their phones (and wallets) even more in the process.

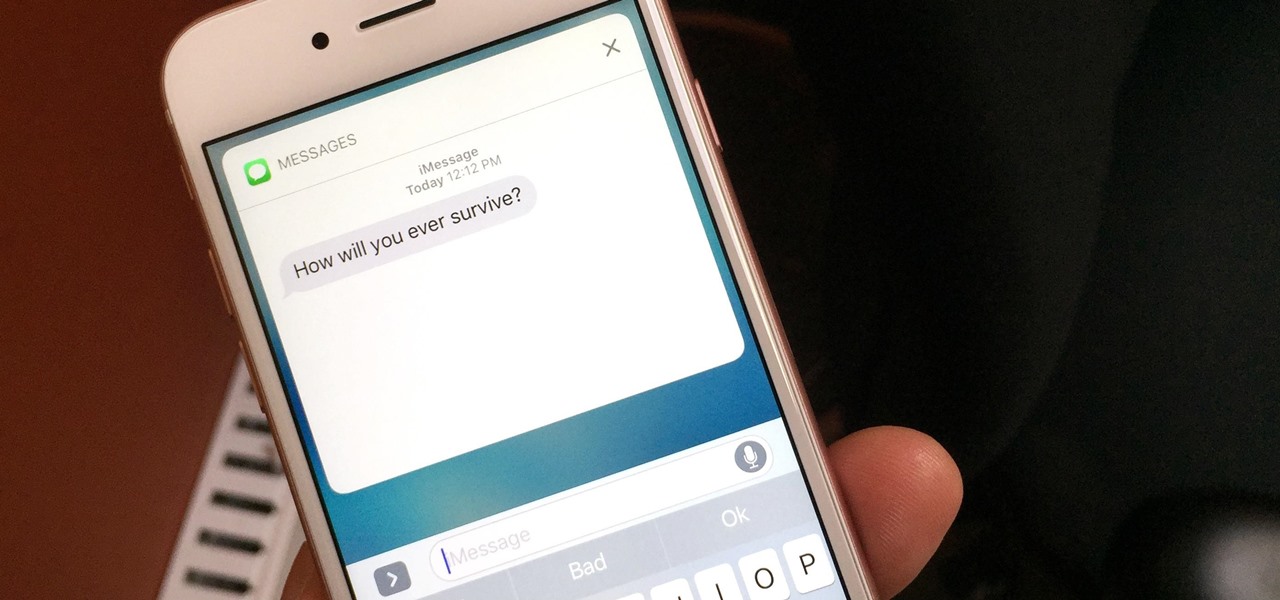
If you have an iPhone with 3D Touch or Haptic Touch, some lock screen notifications will let you respond to a message without even unlocking the screen. This is definitely a handy feature, and it should save a lot of time in some cases, but there are some obvious security concerns.

A human rights activist from the United Arab Emirates recently stumbled upon three gaping security loopholes in iOS that work by enticing you to tap a link sent to your iPhone. Ahmed Mansoor received a text message from an unknown number roughly two weeks ago, but instead of following the link it included, he sent the message over to a security researcher at Citizen Lab.

Samy Kamkar, security researcher and friend of WonderHowTo, just had one of his devices featured in Mr. Robot.

Google switched things up this year by releasing a developer version of Android N far ahead of I/O, but that's not the only convention they've done away with this year. For the first time, Google will accept name suggestions from the public.

One of the more annoying parts about cooking or baking at home is dealing with sticky ingredients. You scrape the peanut butter out of the jar and into a measuring cup to make sure you have the right amount for your recipe, then scrape the correct amount into the bowl you're cooking with.

Even the most seasoned cook is always looking for ways to make cooking easier and cleaning up after meal prep a breeze. There are a million and one tricks and tips out there to simplify your kitchen routines, but some of them are more valuable than others.

Learn how to paint nails perfectly - with nail hacks every girl should know, with my SuperWowStyle Nail Art Videos!

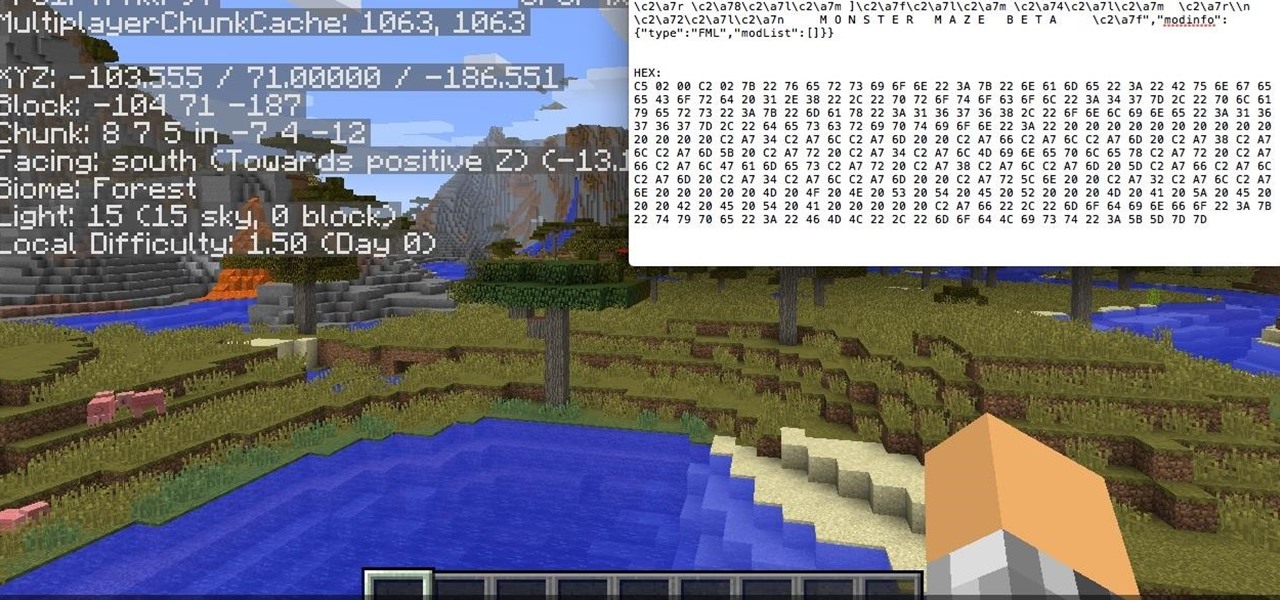
Hello, fellow hackers. I'm sure we've all seen it somewhere: the undying question of "How do I hack the game so-and-so?" And the answer usually is, "Come back when you actually know how to hack!" But how does one even go about "hacking" a game? What could that even mean?

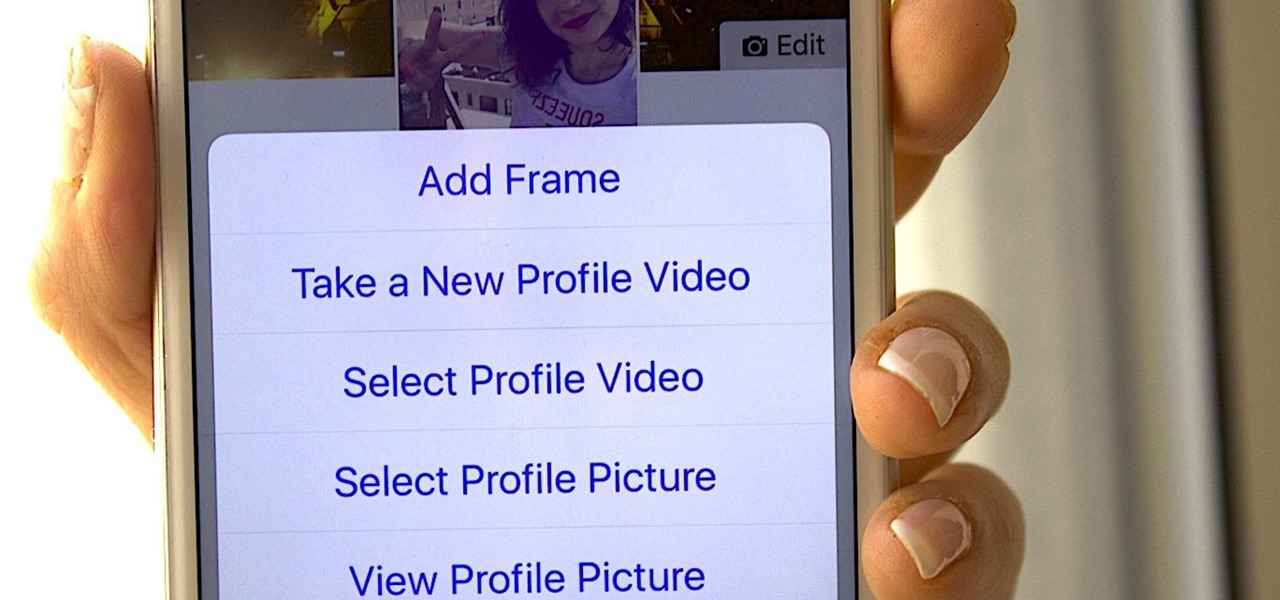
Instead of the still image we've been accustomed to since the inception of Facebook, you also have the option to apply a seven-second video as your profile image, which definitely mixes things up a bit with GIF-like animations. Best of all, this can be done straight from your iPhone or Android device.

Many home chefs are deterred from whisk-intensive recipes such as mayonnaise because they seem to require more than two hands—which is obviously the maximum number we possess. One hand is required to stabilize the bowl, another must be whisking constantly... and a third hand is needed to pour a steady stream of oil.

Bored of your old casual tees? Try these hacks to make them snazzy in a jiffy!

Bad news first: It's not out yet, but it's coming really soon. The premise for the game is this:

Check out this video from CouponCodesHero on hacking a vending machine in no time. All you need is a little packing tape and some paper money, then fool the machine to either get free stuff, or use the "change" to get free money!

Welcome back, my novice hackers! As most of you know by now, a notorious commercial, legal hacking group named "Hacking Team" was recently hacked. As part of the hack, thousands of emails and other material on their servers was divulged. Among the material released were three zero-day exploits. In this tutorial, we will walk through the steps to load one of them, which has become known as the CVE-2015-5119 exploit.

With each day that dawns, there is a new, major hack that makes the news headlines. If you are paying attention, there are usually numerous hacks each day and far more that never make the news or are kept private by the victims. Every so often, a hack is so important that I feel compelled to comment on it here to help us learn something about the nature of hacking and IT security. This is one of those cases. Last week, the U.S. Office of Personnel Management (OPM) revealed that they had been ...

This video has 7 fraction hacks that can save you time when working with fractions. The hacks are: Adding fractions without a LCM

Super Bowl Sunday is just around the corner. With 111.5 million viewers tuning in last year (112.6 if you count streaming), which broke another record that it previously set for the most-watched television event in U.S. history, it's safe to say that most of us will be watching Super Bowl XLIX on February 1st, 2015, whether via TV, web, or mobile.

Welcome back, my amateur hackers! Many of you here are new to hacking. If so, I strongly recommend that each of you set up a "laboratory" to practice your hacks. Just like any discipline, you need to practice, practice, and practice some more before you take it out to the real world.

Welcome back, my hacker apprentices! Metasploit framework is an incredible hacking and pentesting tool that every hacker worth their salt should be conversant and capable on.

10 Life Hacks: 1.Wifi Booster

Welcome back, my greenhorn hackers! Now that we're familiar with the technologies, terminology, and the aircrack-ng suite, we can finally start hacking Wi-Fi. Our first task will be to creating an evil twin access point. Many new hackers are anxious to crack Wi-Fi passwords to gain some free bandwidth (don't worry, we'll get to that), but there are so many other Wi-Fi hacks that are far more powerful and put so much more at risk than a bit of bandwidth.

Welcome back, my fledgling hackers! In the first part of my series on Wi-Fi hacking, we discussed the basic terms and technologies associated with Wi-Fi. Now that you have a firm grip on what Wi-Fi is exactly and how it works, we can start diving into more advance topics on how to hack Wi-Fi.

The big fireworks day is almost here, but most of you are limited in what you can do when it comes to celebrating the Fourth of July with a bang. Unless you live in a dry area prone to wildfires, one type of fireworks you can probably still legally buy are sparklers.

How to hack an Oreo, i.e. dunk an Oreo in milk perfectly.

In a 10 button Nesquik vending machine or other 10 button vending machines, you can hack to get credited for free drinks.

Skype is a great way to stay in contact with friends and family over the internet, and people tend to share a lot in their chats, so why not try and find a way to hack it! Once a Skype account is hacked, you can view all conversations within the last three months, see how long each video call was, and even access files that were shared through chat.

Wouldn't it be awesome if your glasses could detect when it's bright outside and automatically darken? Well, the technology has been around for a while, but it'll set you back a few hundred bucks.

For the vast majority of people, coffee is a must-have in the morning. It provides a stimulating effect that not only wakes you up, but sets your mood and attitude for the rest of the day. Personally, I wouldn't get anything done without coffee.

Back in 2010, iOS developer Daniel Amitay developed a camera security app for iPhones that used an unlock screen almost identical to that of the iPhone.

Get more money and experience in Fish World with this simple Facebook Fish World cheat using Cheat Engine 5.5. Easy to perform.

The Lesser Evils side quest is accessible immediately after completing the factory hostage mission at the start of Deus Ex: Human Revolution. This Giant Bomb tutorial will take you through the mission, which involves breaking into an apartment building complex and hacking into a computer to uncover the location of a video.

If you want to enter the police station armory in Detroit while playing Deus Ex: Human Revolution, you either need to have enough credits to afford it, or you need a high hacking skill. This video from Game Front will allow you to skip both of those requirements by giving you the password to the armory so you can take all the weapons you want.