USB devices are ubiquitous and cheap nowadays, which means they make great raw materials for hacking and electronics projects. This video will show you how you use a USB host shield to hack USB devices and use them with MIDI controllers, game controllers, and other devices.
The increasingly important world of white hat or "ethical" hacking is getting competitive. Thanks to growing salaries and opportunities for talented and trained coding pros who can infiltrate servers and safeguard networks against digital threats, demand for intrepid cyber warriors is through the roof, and it shows no signs of slowing down any time soon.

The camera system on the iPhone has never been better. Apple's iPhone 11, 11 Pro, and 11 Pro Max sport some of the best shooters on the market. But no level of quality makes up for the fact that shady apps can access your cameras for nefarious reasons. You can take control of the situation, however, and block any app you want from using your rear and front-facing cameras.

Web applications are a prime target for hackers, but sometimes it's not just the web apps themselves that are vulnerable. Web management interfaces should be scrutinized just as hard as the apps they manage, especially when they contain some sort of upload functionality. By exploiting a vulnerability in Apache Tomcat, a hacker can upload a backdoor and get a shell.
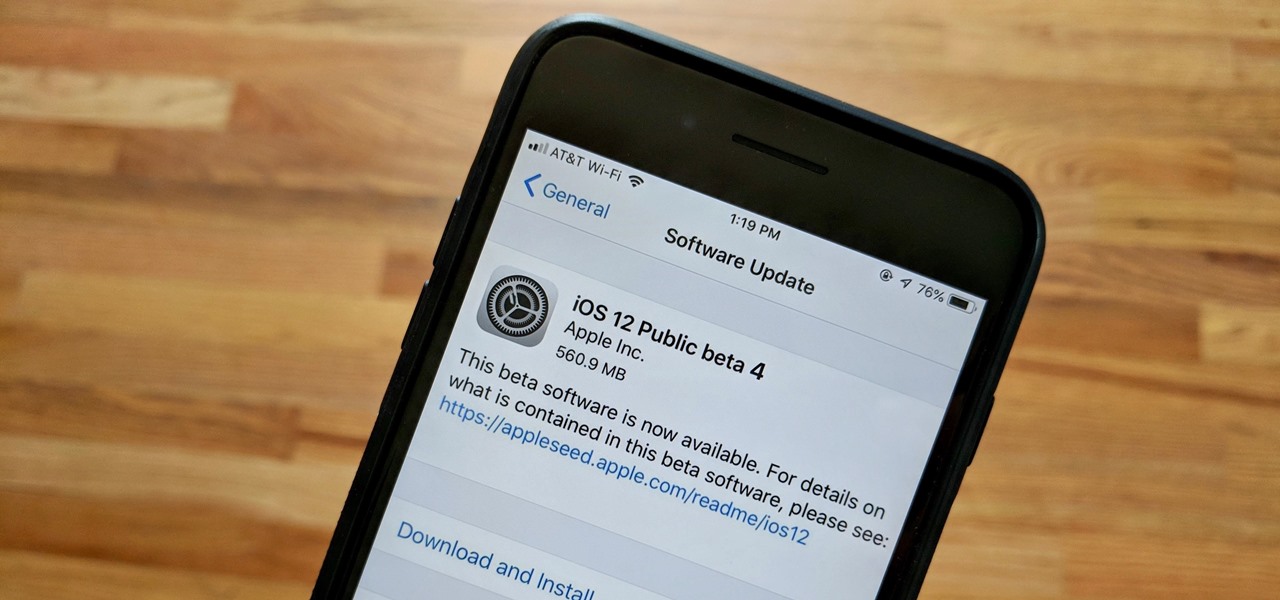
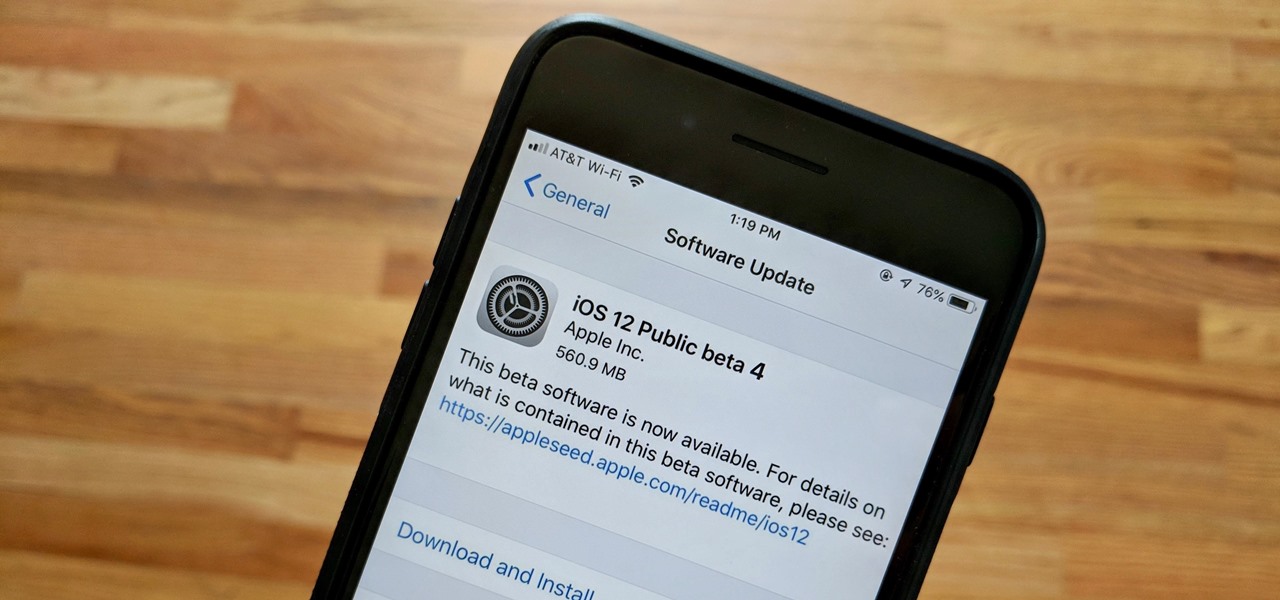
Apple released the fourth public beta for iOS 12 to public beta testers on Tuesday, July 31, just one day after the company seeded the fifth developer beta to eligible users. Both releases are surprising, as Apple had appeared to stick to a two-week release schedule for the iOS 12 beta season, and these updates both came one day earlier than expected.

Apple's latest iPhone operating system is notorious for its frequent bugs and glitches. The latest iteration, iOS 11.3, is no exception, as users are experiencing not only 3D Touch issues but missing screenshot previews as well.

We are slowly approaching Huawei's "See Mooore" event where the P20, P20 Pro, and P20 Lite will officially be revealed to the world. With the event being held in Paris, France, attending won't be an option for most of us. Fortunately, there are ways to enjoy the event online.

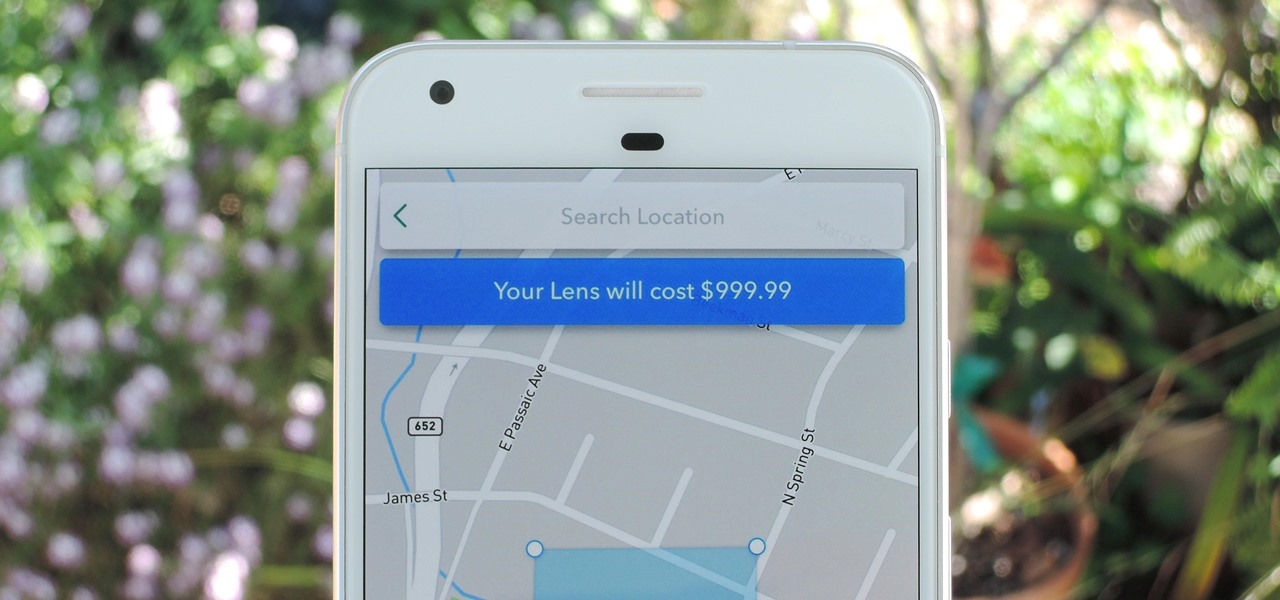
Snapchat just rolled out a feature that lets you create custom Filters and Lenses. While the average Geofilter won't run you more than a few bucks, it's not that hard to exponentially jack up the price. Amazingly enough, Snapchat's latest attempt to monetize their platform can ultimately cost you as much as $999.99. Ignore the penny, let's call that a cool grand.

Apple released iOS 11.2 beta 3 on Monday to developers, with only a handful of changes over Beta 2. Still, it's always recommended you upgrade to the newest version of iOS, so if you are running any of the previous 11.2 betas, make sure to update.

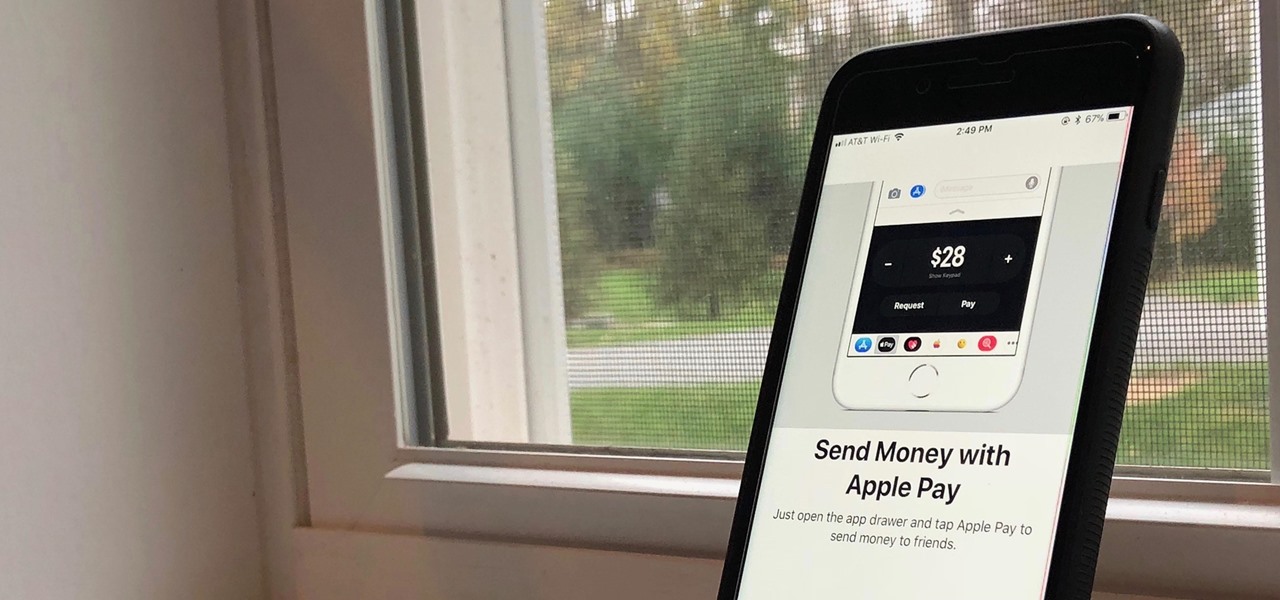
First showcased back in June at WWDC, Apple Pay Cash is Apple's answer to Venmo. Although iOS 11 has been out in the wild since September, this new iMessage feature has been mysteriously absent. That's finally changed with the second beta of iOS 11.2 — Apple Pay Cash is here.

The displays on all of our devices are getting better and better. TVs, smartphones (Infinity Display, anyone?) — any modern device you use, the screen looks great. So we should expect our content to live up to these fantastic displays. Netflix is attempting to do that, by implementing HDR video for LG G6 users.

It's happened to all iOS users: You're talking to a friend or watching TV, and all of a sudden, you hear "I'm not quite sure what you've said." Apparently, your phone heard something that resembled "Hey, Siri," and activated the assistant. But now, thanks to a new patent from Apple, the days of unexpected Siri may be numbered.

Don't ignore the update sitting in your Settings app; you'd be leaving your iPhone's security vulnerable.

According to the American Osteopathic Association, "1 in 5 teens has some form of hearing loss," and some experts believe it's because of an increase in headphones use. While I understand that music, movies, and video games help keep children preoccupied, there's no reason why they can't be entertained at a healthy hearing level.

Many websites are crowded with ads, pictures, and other irrelevant content that make it harder than necessary to read a simple article on your iPhone. In many cases, you have to zoom in just to get a better view of the text you're attempting to read—unless the webpage blocks zooming.

You would think that with each major iOS update, there'd be fewer ways to bypass the lock screen. Unfortunately, Apple's developers have consistently failed every year since 2013 in this department, leaving open lock screen exploits for iOS 7, iOS 8, and now the latest iOS version, iOS 9, with each exploit being discovered within days of the OS release.

In an attempt to get more people to subscribe to Apple Music, the Music app was completely revamped in the iOS 8.4 update for iPad and iPhone to include new tabs for New, For You, and Connect.

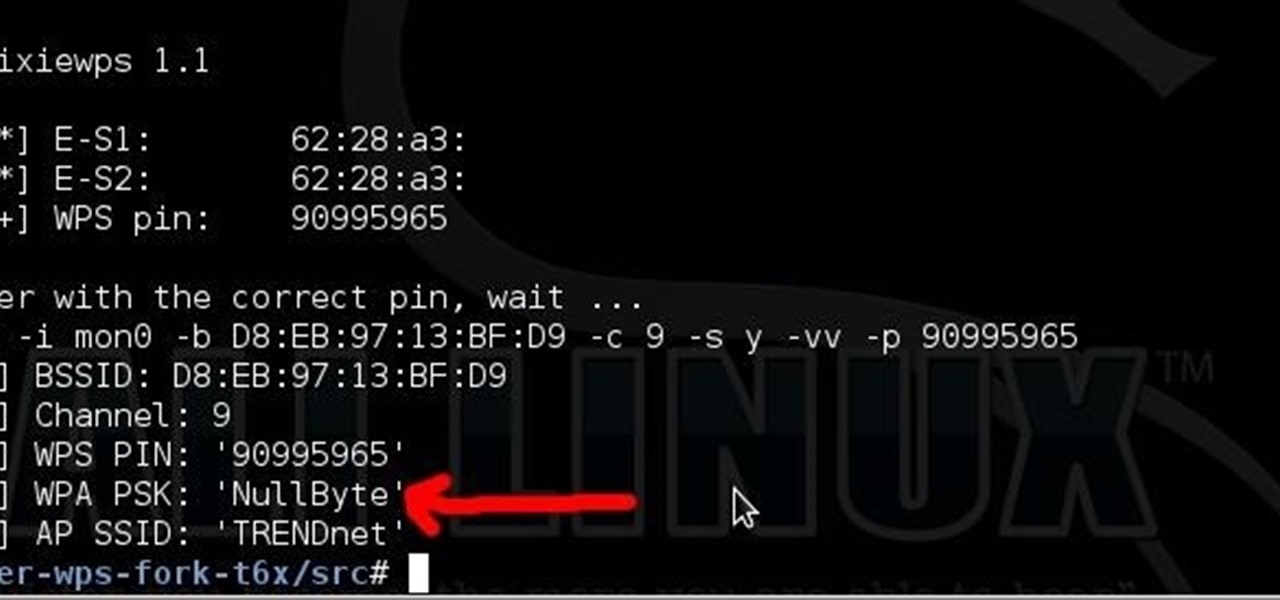
Long time reader, first time 'How To' poster. This tutorial has been highly requested. Here are the steps to perform a Pixie Dust attack to crack a WiFi password that has WPS enabled.

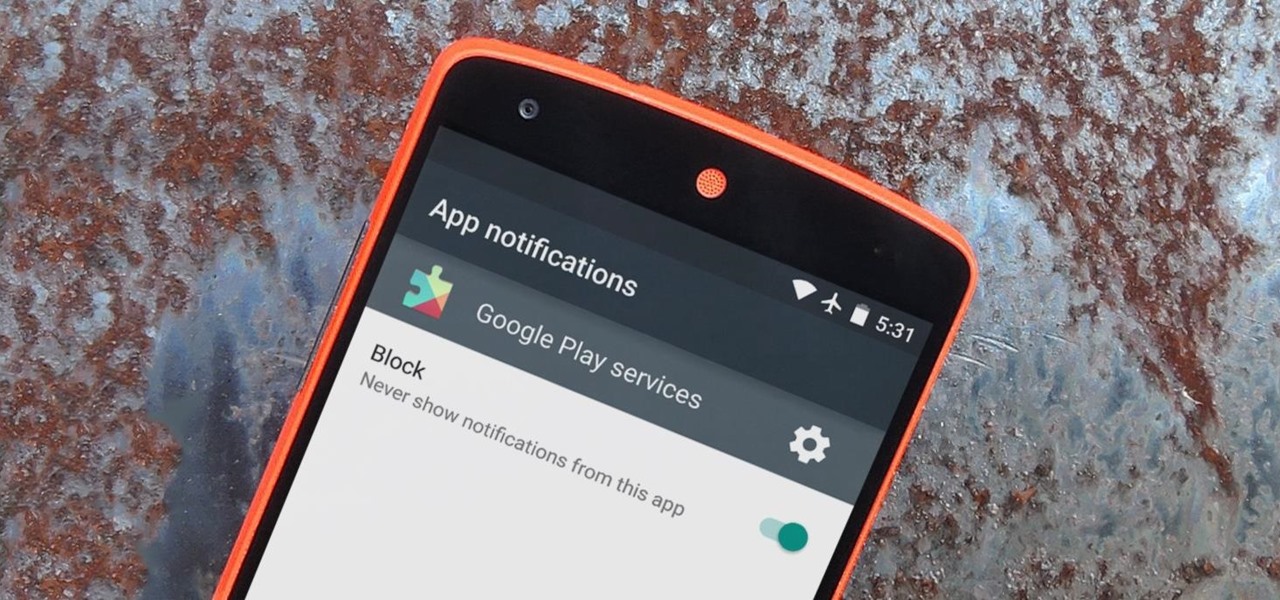
Have you ever had one of your Android games post a notification in a lame attempt to remind you to play? This is becoming a common practice these days, and to me, it's about as annoying as a Best Buy blue shirt when I'm just trying to check out the latest TVs.

Dolby may have made a lot of Android users angry by only offering their Atmos surround sound equalizer to Lenovo and Amazon, but we all know that exclusivity is only temporary in the Android world. Thanks to worstenbrood, we now have a ported version that can be installed on any device running Android 4.3 and above.

Believe it or not, not every Apple lover is willing to make the commitment and fork over $350+ for the Apple Watch. Like many others, I'm not willing to put that much faith into Apple's first attempt at wearable tech.

The display on the Apple Watch is way too small to even attempt typing on it, which is why the Messages app only allows for responses using default replies or by speaking a message. But you won't always be able to speak a message, and often the default replies will be too generic to want to use.

Continuity, introduced back when iOS 8 and Mac OS X 10.10 were released, lets users seamlessly connect all of their Apple devices together. With it came a feature known as Handoff that "hands off" an app or task from one Apple device to another, like starting an email on your iPhone and completing it on your Mac.

If you have an Apple Watch, it's easier than ever to ask Siri for directions, send a quick text, or locate the nearest Chipotle—because you don't need to pull out your iPhone anymore. Luckily, Apple made it fairly painless to get Siri up and running on the Watch, so let's go over the two quick activation methods.

Yes, they're called volume keys, but they can do much more than adjust your volume. With minimal effort, you can do some amazing things with these physical buttons, like secretly record videos, toggle on your flashlight, scroll through pages, control your music, and much more. And while using them to wake your screen is useful, let's take it a step further and show you how to use them to completely unlock your device, even if the screen is off.

Welcome back, my neophyte hackers! I have already done a few tutorials on password cracking, including ones for Linux and Windows, WEP and WPA2, and even online passwords using THC Hydra. Now, I thought it might be worthwhile to begin a series on password cracking in general. Password cracking is both an art and a science, and I hope to show you the many ways and subtleties involved.

Red Bull Stratos sent the first skydiver to space in a weather balloon this past weekend. Free-fall jumper Felix Baumgartner reached 24 miles in altitude in the Earth's upper stratosphere before he leaped from the capsule. Felix reached a maximum speed of 833mph, breaking the sound barrier, before slowing down at the atmosphere, where he finished with a 4:20 minute freefall.

When I left off on our last hack, we had hacked into the ubiquitous Windows Server 2003 server by adding ourselves as a user to that system so that we can return undetected at any time. The problem with this approach is that a sysadmin who is on their toes will note that a new user has been added and will begin to take preventative action.

Kip "Kipkay" Kedersha is known for his intriguing and clever how-to and prank videos, even when he teams up with MAKE Magazine. He will show you how to tweak, hack, mod, and bend any technology to your hacking needs. No electronic device, gadget, or household item can stand the test of Kipkay's hacks and mods.

Want AAA batteries for cheap? Learn how to hack a 9-volt battery with this money-saving video tutorial from Make Magazine's Kip Kay. All you'll need to replicate this hack at home is a pair of needle-nosed pliers and one or more Energizer 9-volt batteries. For instructions on how to extract quadruple A batteries from an Energizer 9-volt, watch this how-to video.

Michael-David BenDor demonstrates how an optical scanner voting machine can be hacked in under five minutes using everyday tools. So, if you want to rig the next election in Michigan, this is the video tutorial for you. Don't agree with the next popular president or governor? Then see how to hack and get around the presidential seal in the voting machine.

There are many ways to recycle a satellite dish and this is one of them. In this video tutorial, you'll learn how to hack an old satellite dish into a biquad WiFi antenna. For detailed, step-by-step instructions on building your own audio signal booster, take a look!

Find out how to use a six volt lantern battery to really save you money. This is no con, or prank, or joke that involves 32 AA batteries; this is the real deal. Just watch this money saving video tutorial to see how to hack a six volt battery. You can easily replace a few of this cells, which are equal to 3 D batteries, which can be used inside of your Maglite flashlight. Don't let that 6 volt battery go to waste after buying it for the other false hack, use them in any way you can, like this...

Wondering how to most effectively combine ice cubes and a simple USB-powered computer fan into a fully functioning air conditioning system? In this video tutorial, you'll learn how to hack a coffee can and USB-powered fan into a simple, but effective, air conditioning unit. For detailed instructions on hacking together your own tin-can AC unit, watch this über-short how-to.

Interested in getting 1.5-volt button cell batteries for pennies on the dollar? Kip Kay, of Make Magazine, is here to show you how. The trick is to buy Energizer A23s, each of which contains 8 1.5-volt button cells. For detailed instructions on this straightforward money-saving hack, take a look!

Make a bionic hearing spy device by hacking a megaphone! Kipkay brings you this hack video on how to use a megaphone to spy on people. You can pull in conversations up to 100 feet away! Check out Kipkay hiding in a tree, spying on people. It also works through walls. That's how to make a bionic hearing spy device!

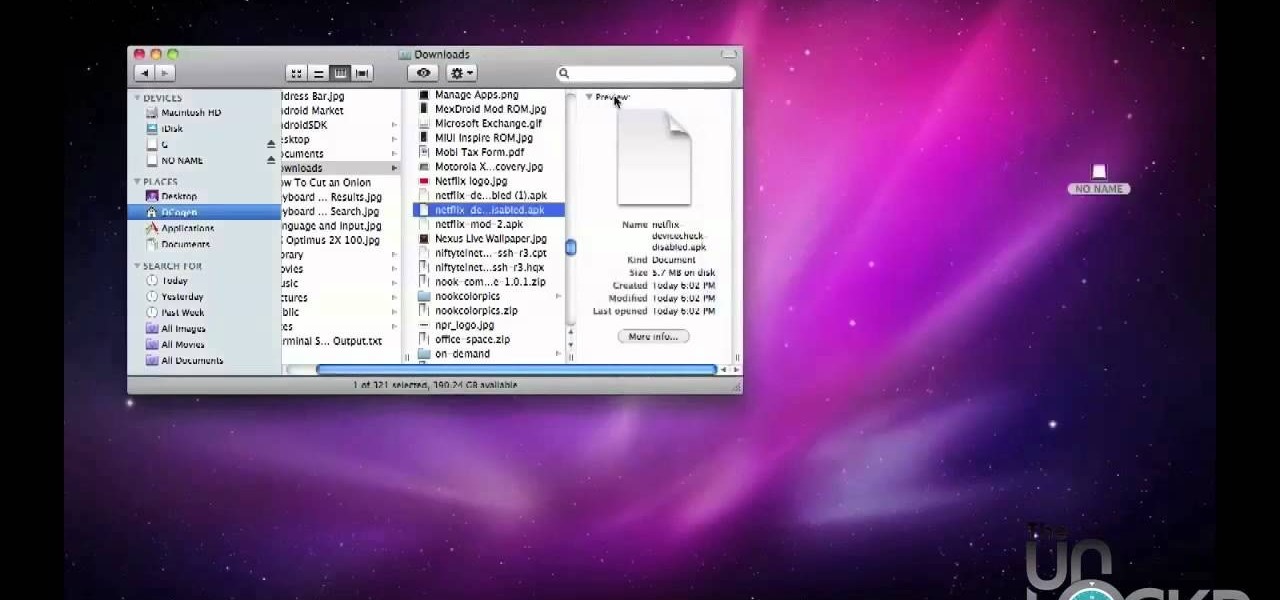
Want to watch Netflix Watch Instantly on your Android device? Watch this video and follow these instructions to learn how to hack any rooted Android device with an APK to work with Netflix. Watch thousands of streaming movies and TV shows with your hacked Android tablet or smartphone.

Is your laptop not holding a charge anymore? Don't buy a new one, hack the old one! Laptop batteries can cost upwards of a hundred dollars, but with new lithium batteries and some soldering tools, the new one works just as well. Watch this video computer circuitry tutorial and learn how to hack a dead laptop battery.

This video tutorial demonstrates a simple hack for improving the WiFi reception of a USB adapter. To replicate this hack yourself, you'll need the following materials: (1) a WiFi USB adapter, (2) a USB extension cable, (3) a metal strainer, and (4) a pair of scissors. For detailed, step-by-step instructions on improving your WiFi adapter's signal levels, watch this how-to video.

Compromised uTorrent clients can be abused to download a malicious torrent file. The malicious file is designed to embed a persistent backdoor and execute when Windows 10 reboots, granting the attacker remote access to the operating system at will.