Samsung reintroduced its well regarded Good Lock app, so now you can tweak parts of your Galaxy's interface without the need for root or other labor-intensive mods. Thanks to an awesome add-on, you can even tidy up you phone's status bar — so if you've always wanted to get rid of that pesky NFC "N" icon or any other indicator at the top of your display, you're now just a few taps away.
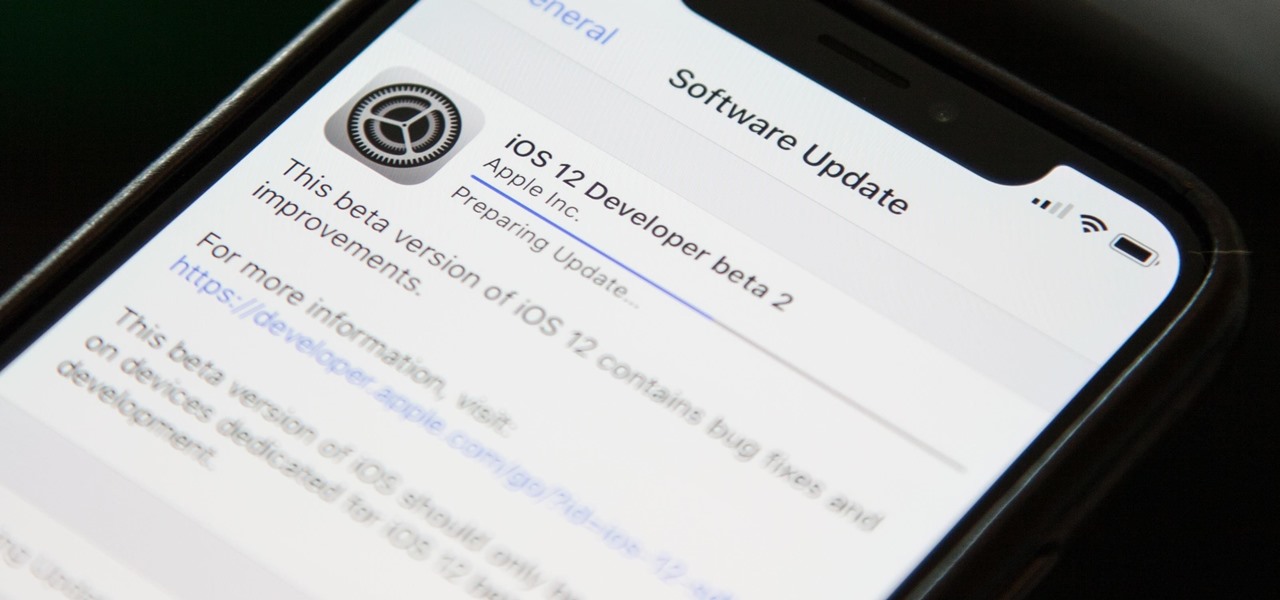
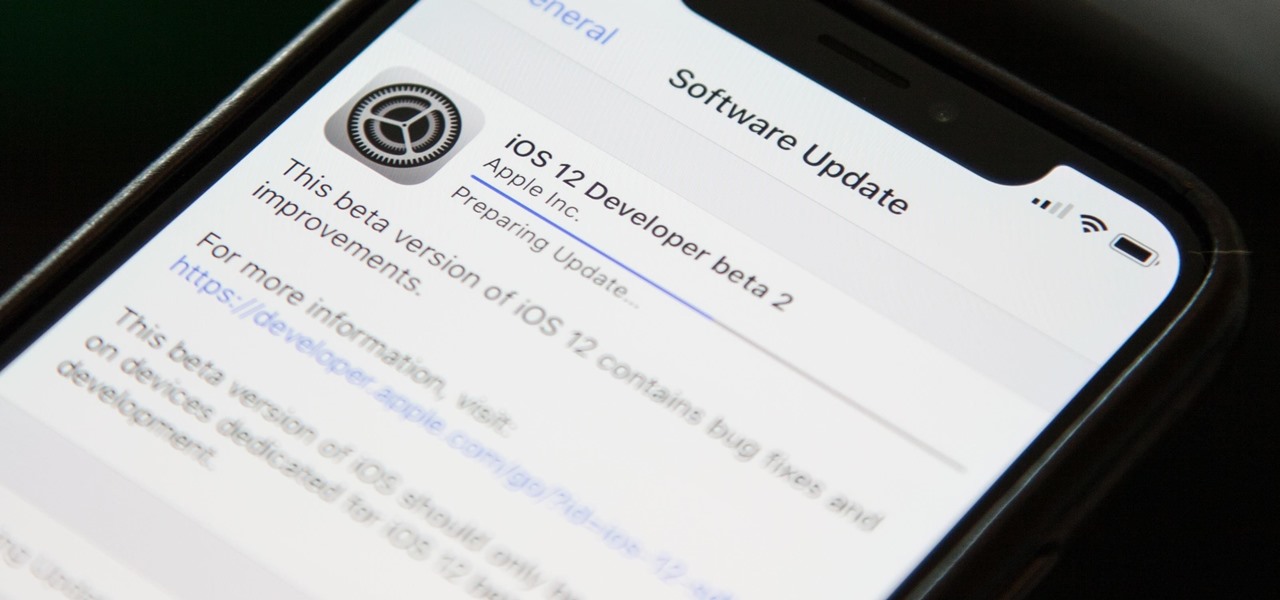
Right on the heels of the iOS 11.4.1 beta 3 release, Apple pushed out iOS 12 beta 2 to registered developers on Tuesday, June 19. Public beta testers received the same version, labeled as iOS 12 public beta 1, six days later on Monday, June 25. Last year, the iOS 11 public beta opened up just five days after the release of iOS 11 developer beta 2, so iOS 12 is pretty much right on track in that regard.
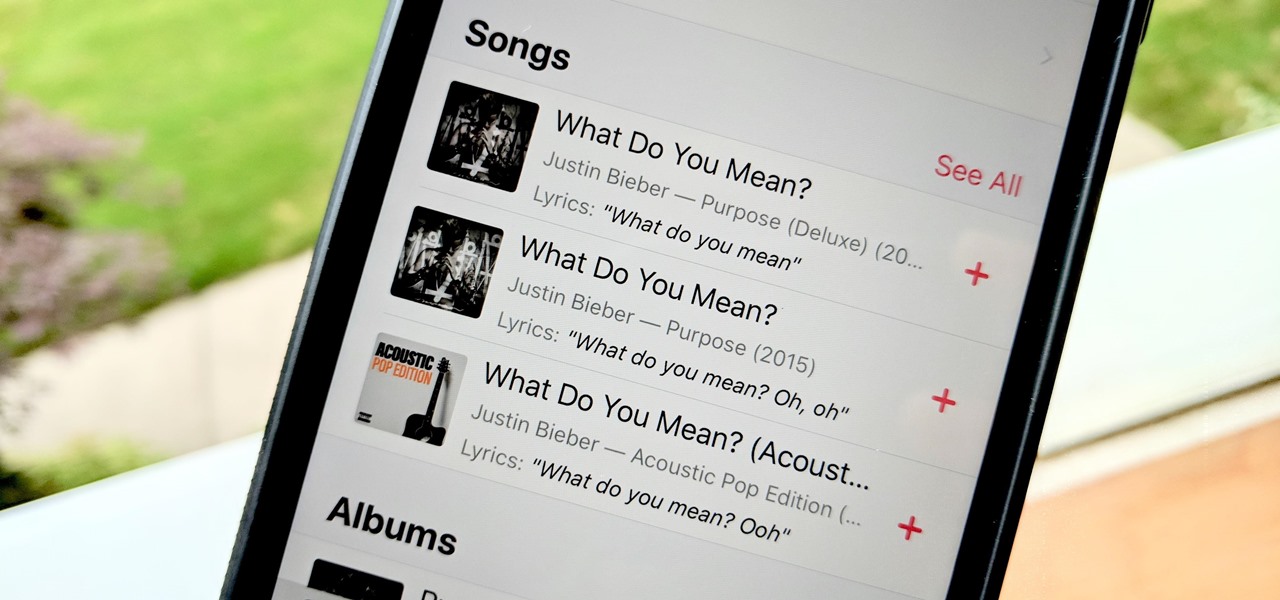
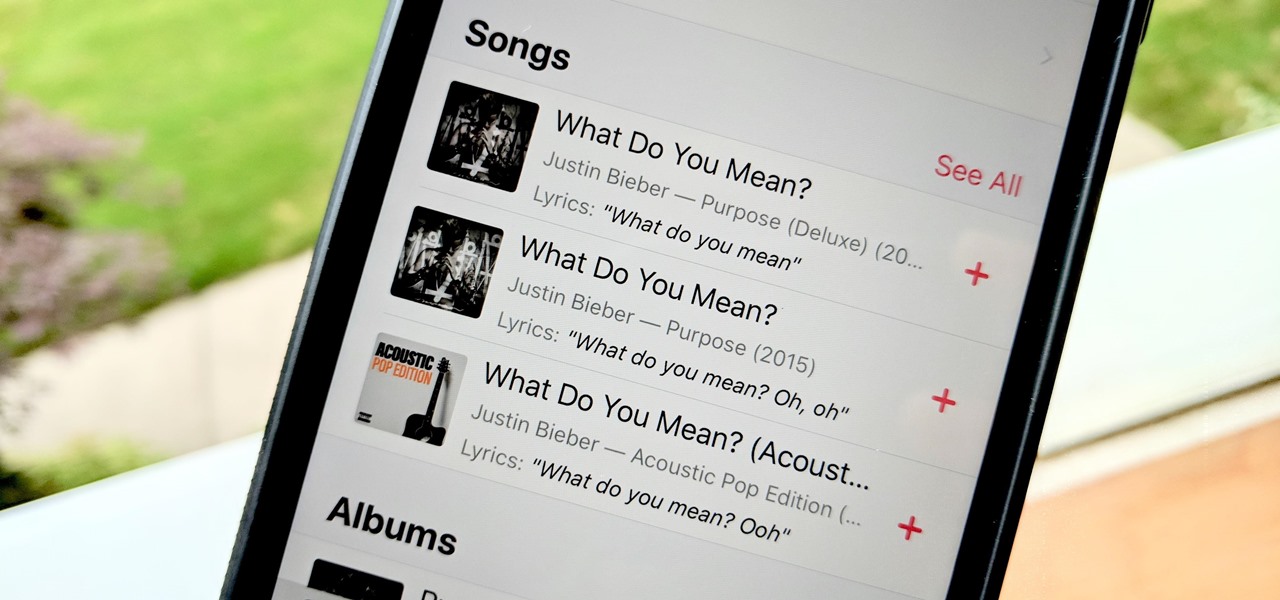
Has this ever happened to you: You're singing a song in your head and want to look it up on Apple Music but you just can't think of its name or even who recorded it? In iOS 12, if you can sing it, you can search for it, as the update lets you find songs in Apple Music by lyrics alone. It's like Shazam, only instead of identifying music by sound, it uses the lyrics in your head.

Ever since 2009, you could send a photo or video that you've already taken right from the Messages app on your iPhone. You would just tap on the camera icon next to the new message box, then choose either to take a new one or select one from your library. If you're running iOS 12, that's no longer the case, but that doesn't mean the capability is gone entirely.

In iOS 12, Apple included new, Snapchat-like effects and stickers for photos and videos in Messages. While these new options are fun, they're missing something that takes away from the appeal, especially since Snapchat, Instagram, Facebook, and similar apps already let you do it.

It's possible to stream a MacBook's entire computer screen without using Apple's Screen Sharing application and without opening any ports on the target device. A hacker with low user privileges on the backdoored Mac may be able to view a victim's every move in real time no matter where they are.

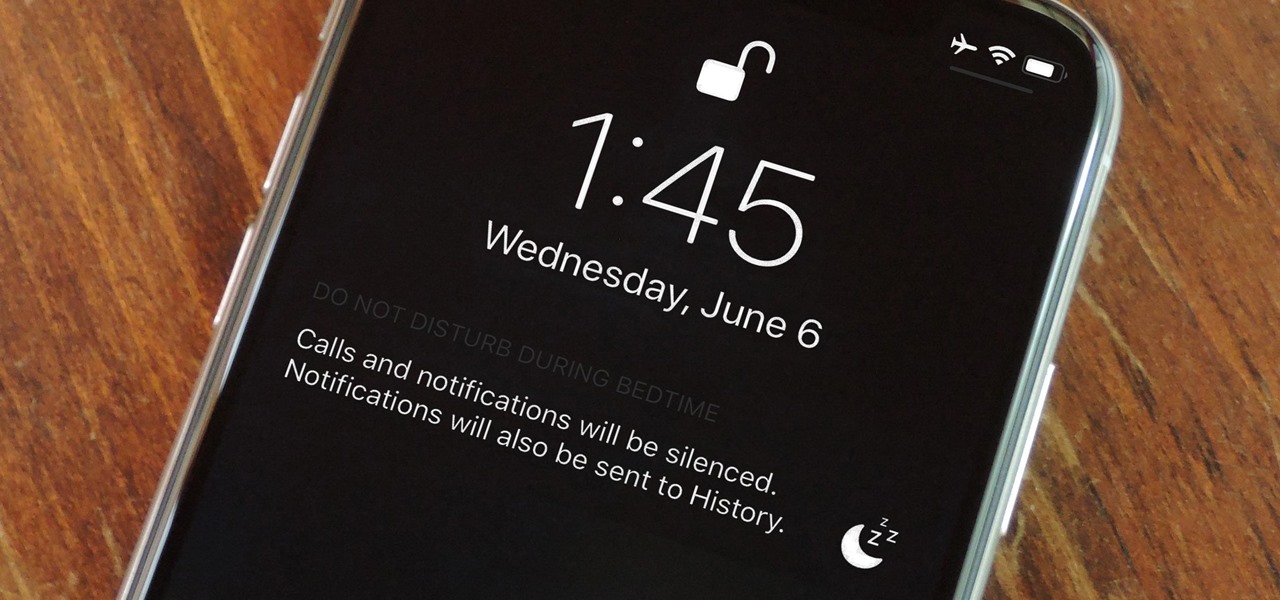
Let's say you wake up in the middle of the night and check your phone to see the time. As soon as you do, you're greeted by a wall of notifications on your lock screen. You just wanted to know how much longer you could sleep, but now your mind's racing after seeing all of the messages you need to deal with. Thankfully, iOS 12's new Bedtime Mode has a solution for this problem.

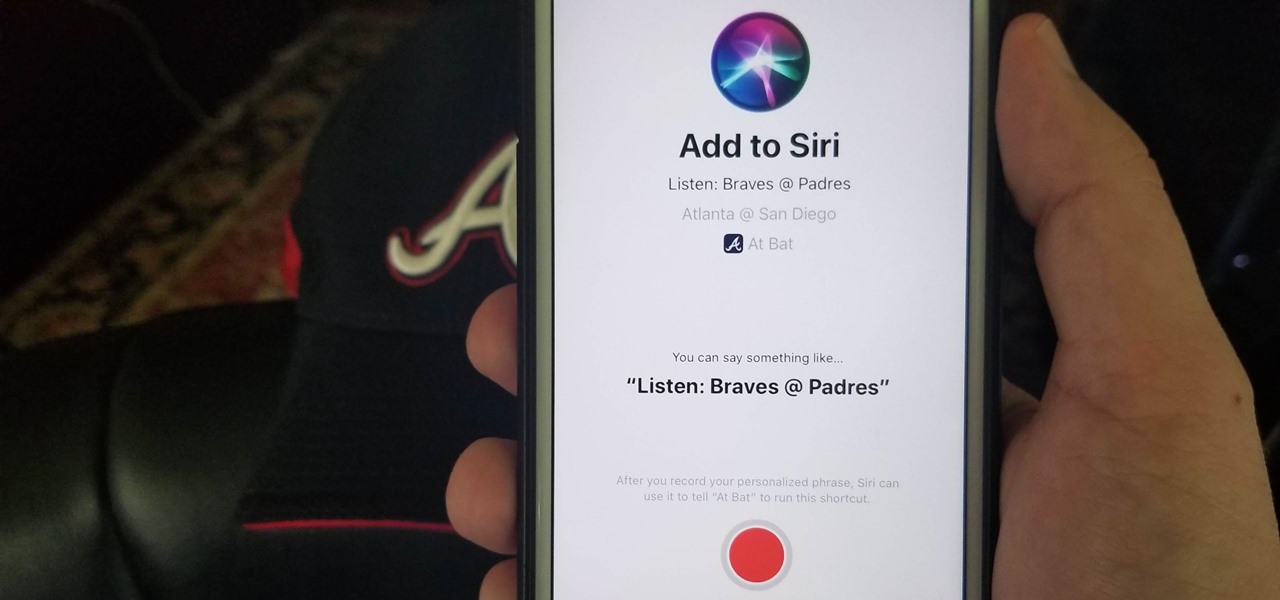
Apple is putting their Workflow acquisition to use with the new Shortcuts feature, integrated right into Siri. It allows you to connect commonly-used actions to a phrase that you activate with Siri. In addition to some of the other speed improvements in iOS 12, Shortcuts helps streamline your mobile experience.

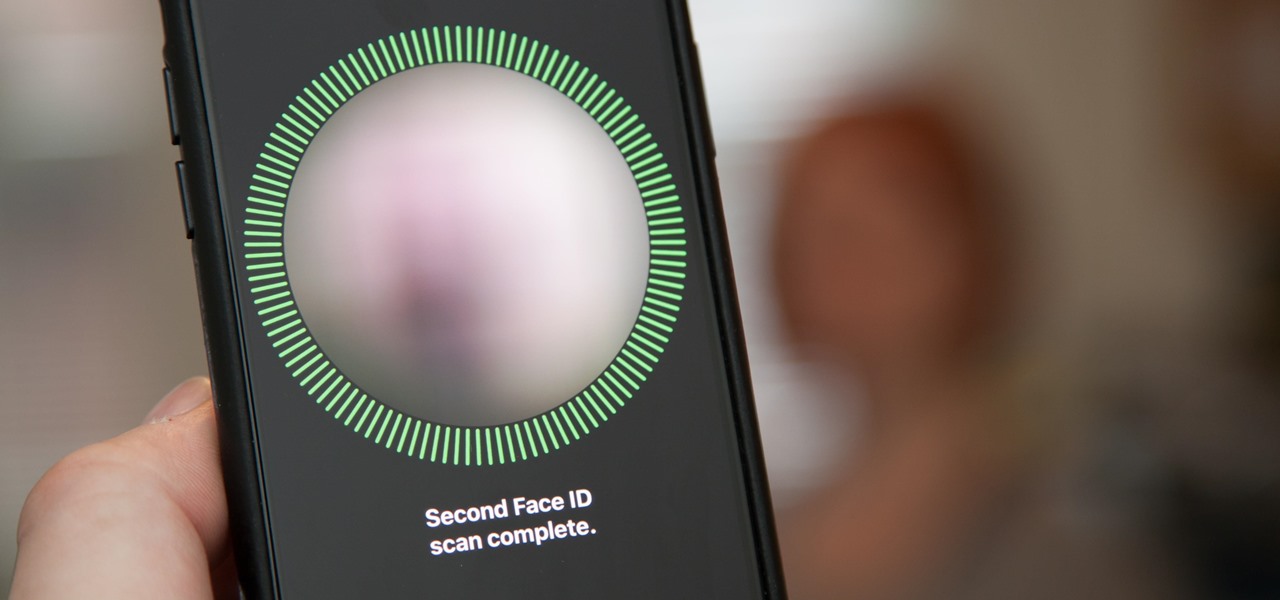
Setting up Face ID is simple, but getting it to work correctly every time is a different story. While there are numerous tips for getting Face ID to work every time you need it on your iPhone X, XS, XS Max, or XR, Apple has added a better option in iOS 12 that lets you add an "alternative appearance."

With tons of titles to choose from on the iOS App Store, you'll never be lacking when it comes zombie shooters. Unfortunately, the same can't be said if you're more interested in base-building and defending against the undead. PlayStack aims to change this, and they've soft-launched Survival City in the Philippines for further development. With a simple hack, you can try the game yourself right now.

Single sign-on (SSO) lets users login across different sites without having to manage multiple accounts. I'm sure most of us appreciate the convenience of seeing "Sign in with …" buttons that let us login with a single username. Hackers, however, see a possible avenue for exploitation, and you'll soon learn how an attacker can exploit a SAML vulnerability to assume another user's identity.

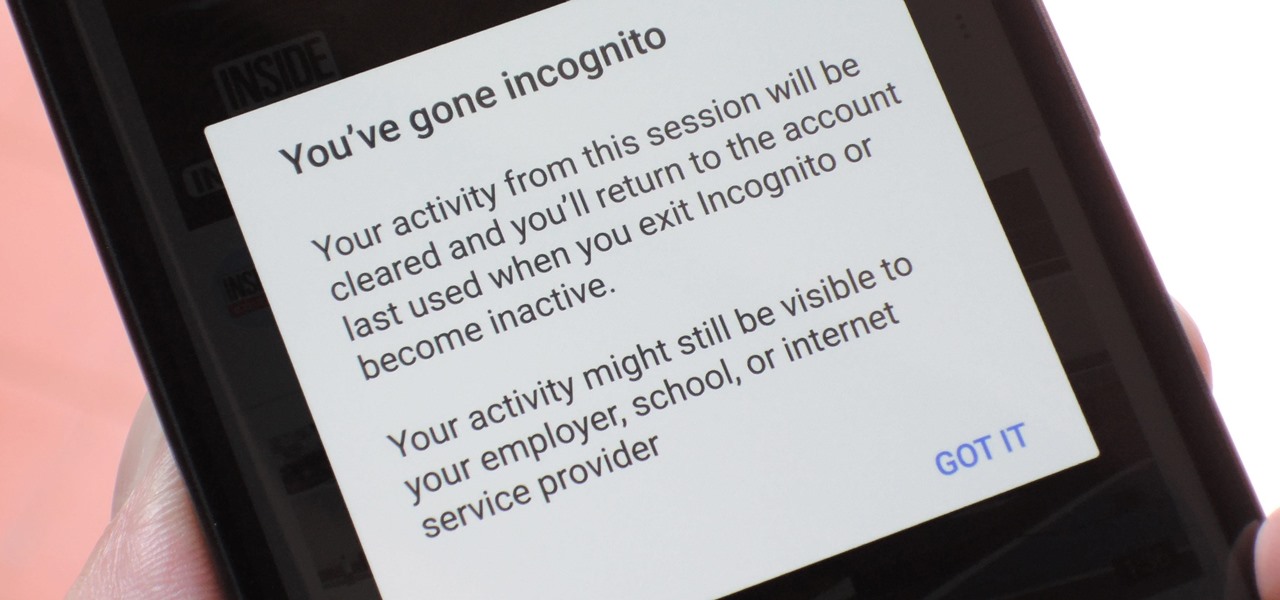
Incognito Mode is a privacy feature that was popularized by Google Chrome, and it recently made its way to GBoard. Now it's coming to the YouTube app to help make your video watching experience truly private.

When it comes to traveling from one location to another with the aide of your iPhone, ensuring your navigation app works as it should keeps you one step ahead of potential hassles. One feature often overlooked is audio settings, and while having no voice prompts is easy enough to ignore while walking or commuting, having no sound to guide you while driving can spell disaster.

Traditional subdomain enumeration techniques create a lot of noise on the target server and may alert intrusion detection systems to an attacker's intentions. For a stealthier approach, there's a tool with the capability of finding hundreds of subdomains related to the target website without alarming the server administrators.

On April 3, 2018, Snapchat announced that the phone and video calling feature that's long been a feature of one-on-one calls would be coming to group chats. Well, late on Monday, April 17, the feature was finally pushed out to everyone for Snapchat groups on Android and iPhone.

Mobile gamers who grew up on J.K. Rowling's fantasy epic have yet another reason to rejoice, as Jam City's Harry Potter: Hogwart Mystery is slated to touch down on both iOS and Android on April 25. But if you can't bear the wait, there's a little hack you can do to give the game a try right now.

When you leave your iPhone on a table or anywhere within somebody else's eyeshot, a private message may pop up on your lock screen that could be read by anyone who sees it. But there's a way to keep others from reading your possibly sensitive text messages and emails without giving up the convenience of lock screen notifications entirely.

There's a fine line between order and chaos in group chats. With all the cross-talk, threads can easily devolve into a random mess that has nothing to do with the original discussion topic. WhatsApp group chats certainly aren't immune to this problem, but they've recently taken a step in the right direction.

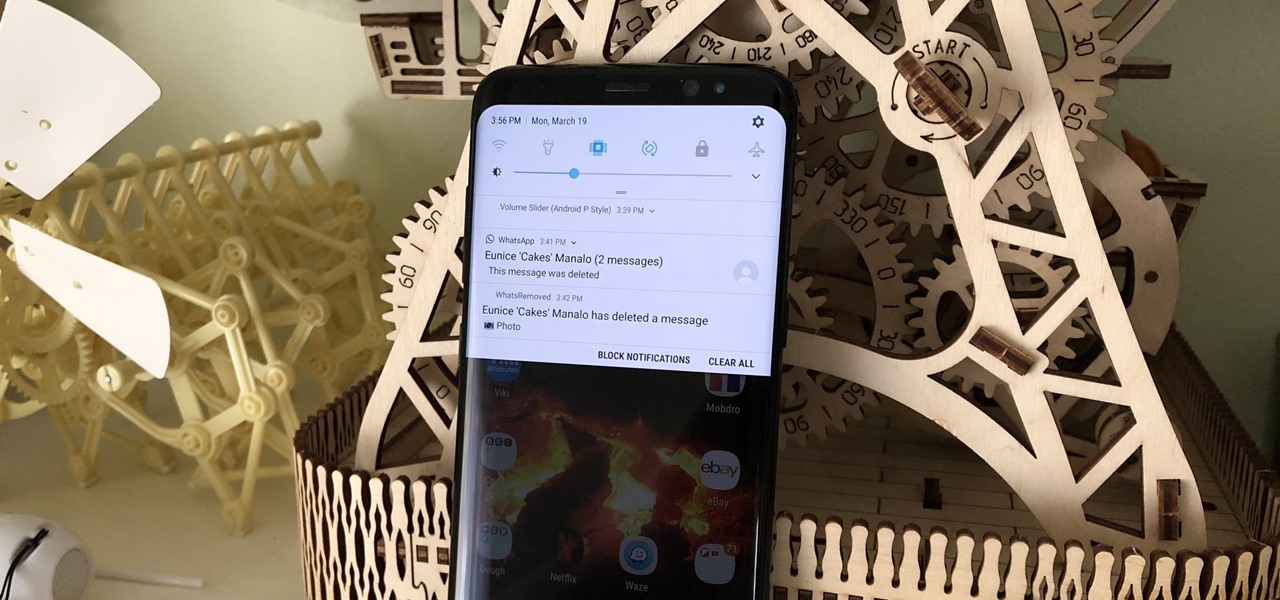
To help keep potential drama at bay, WhatsApp lets you delete questionable messages before the other person even sees them. If you're on the receiving end and you're curious about the deleted text, however, there's an Android app that lets you view erased messages.

Design flaws in many routers can allow hackers to steal Wi-Fi credentials, even if WPA or WPA2 encryption is used with a strong password. While this tactic used to take up to 8 hours, the newer WPS Pixie-Dust attack can crack networks in seconds. To do this, a modern wireless attack framework called Airgeddon is used to find vulnerable networks, and then Bully is used to crack them.

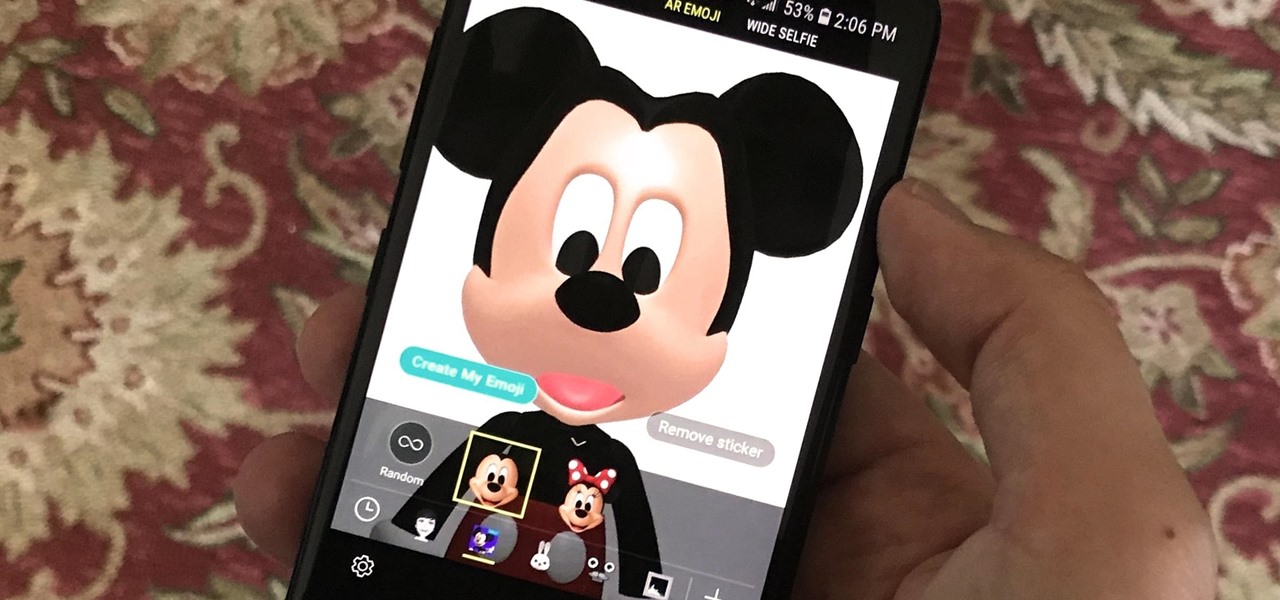
Samsung introduced AR Emojis in the Galaxy S9, largely as a response to the iPhone X's Animojis. However, they appear to be taking on a life of their own by integrating a variety of custom AR Emojis. Among those are ones from the PyeongChang Olypmics and even Mickey Mouse.

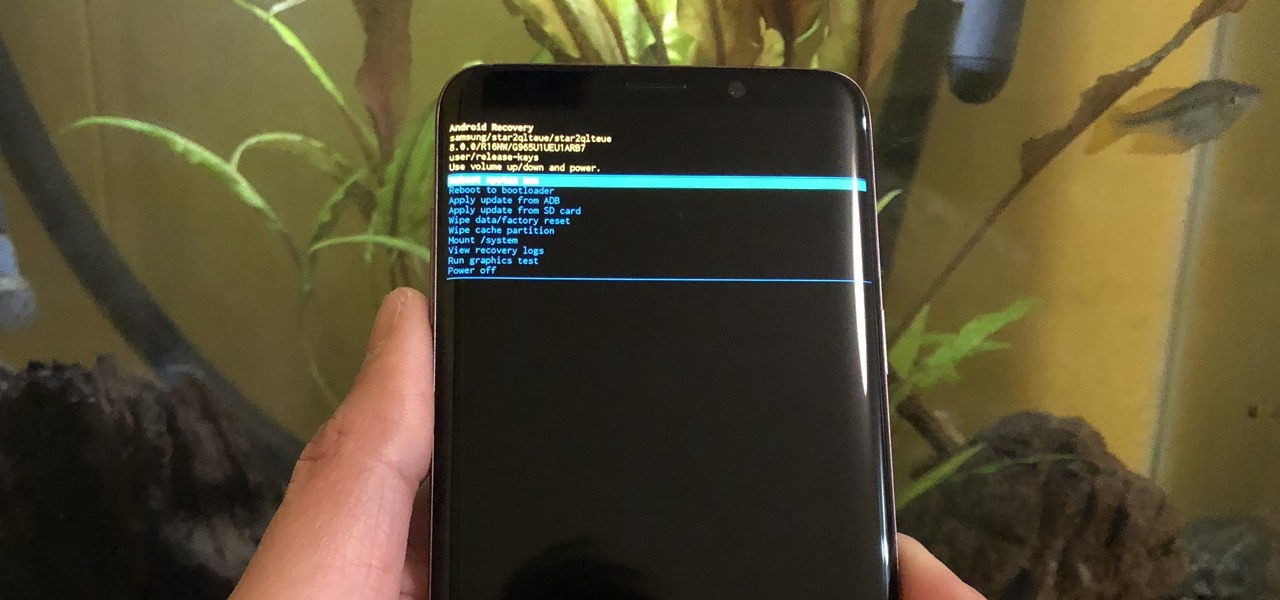
From veteran modders to casual tinkerers, booting into either recovery mode or download mode is something every Galaxy S9 owner should know about. These two pre-boot menus serve a very important purpose — recovery mode is the go-to solution for soft bricks, while download mode allows you to flash firmware files using utilities like Odin and Smart Switch, which can truly be a lifesaver.

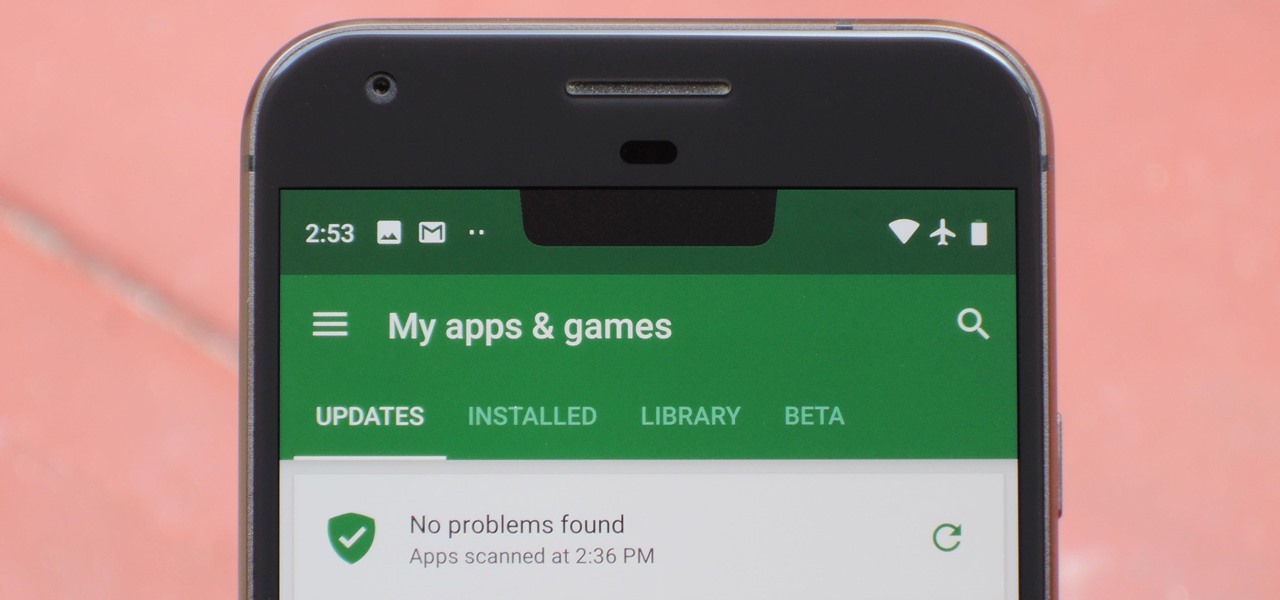
Most Android phones don't even have an Oreo beta yet, but that's not stopping Google from releasing the preview to their next big update. Android Pie is here for developers to test, and with it, one of the more controversial additions in the Android world today — the notch.

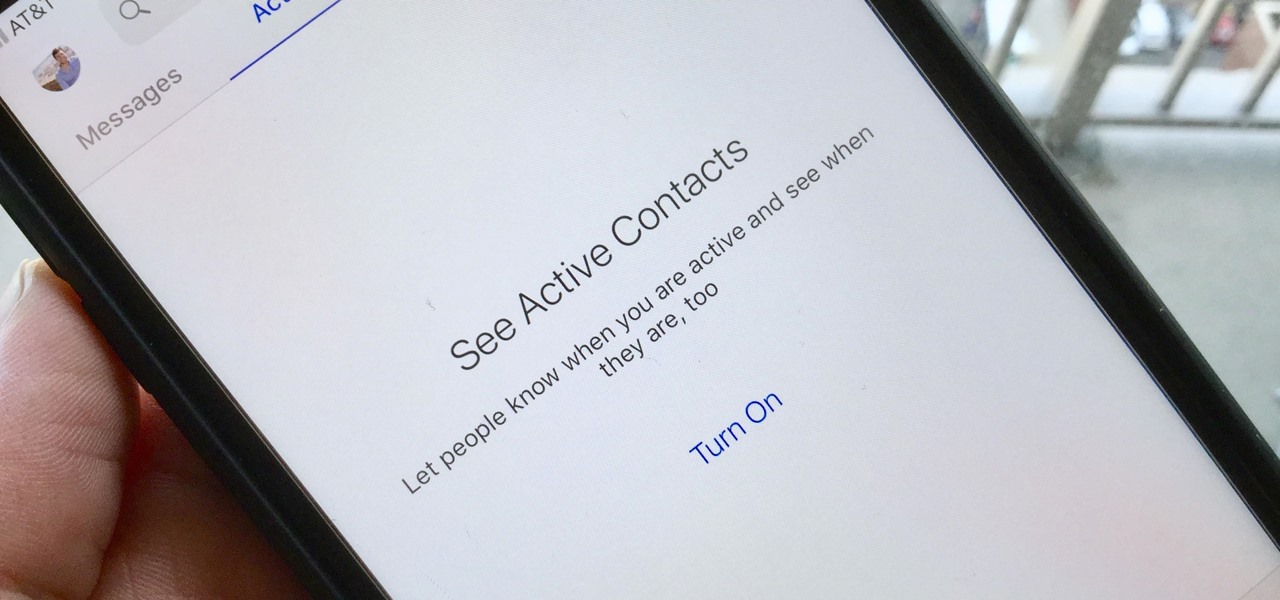
For all of its advantages, Facebook Messenger isn't the best for people who like their privacy. The popular app lets all your Facebook friends know when you're online by default, as well as how long you've been idle, making it impossible to check up with one person without leaving yourself vulnerable to your entire friends list. Luckily, this feature is one you can turn off.

For quite some time, popular messaging apps like Snapchat have had features that let you place stickers on photos and videos to add time and location-based information. To catch up, WhatsApp has now added the same functionality to its messaging platform in an effort to remain among the most well-rounded messaging apps available.

Spring training has begun in earnest, and to mark MLB's soft debut, GLU has soft-launched a followup to the smash hit MLB Tap Sports Baseball 2017 in Canada. While MLB Tap Sports Baseball 2018 is still technically unavailable outside of Canada, you can actually play this game right now through a simple hack.

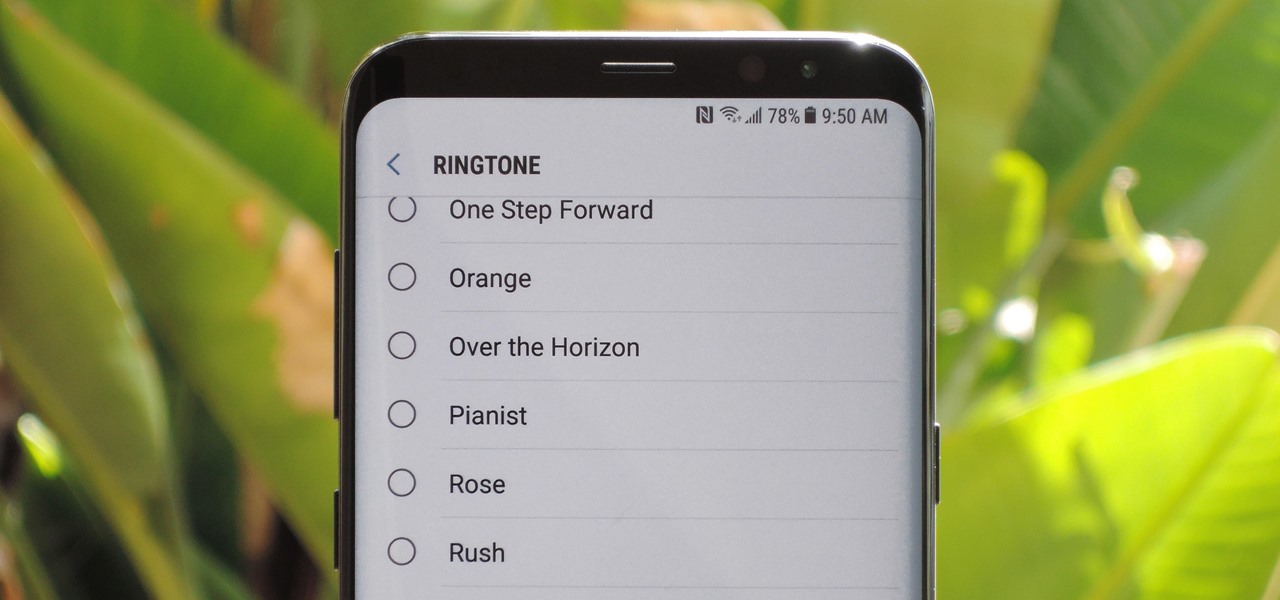
The Galaxy S9 was announced February 25, and it's jam-packed with features like AR Emojis and and a Dual Aperture camera. You really love the cut of its jib, but maybe you don't have the means to get your hands on one. Well now, you can get the Galaxy S9's notification sounds and ringtones, to help you feel like you own one.

Thanks to Samsung Experience 9.0 on the Galaxy S8 (AKA TouchWiz Oreo), we know the upcoming Galaxy S9 is going to enjoy some of the new keyboard changes coming to Samsung's iteration of Android 8.0. Those who preorder the device on March 2 or pick it up on March 16 can expect these changes out of the box, as the S9 will be running Samsung Experience 9.0 on day one.

Apple just released the third beta for iOS 11.3 on Tuesday, Feb. 20, which comes exactly two weeks after the release of iOS 11.3 beta 2 that brought battery health data and performance-throttling controls. At first glance, iOS 11.3 beta 3 seems to be mostly under-the-hood improvements, but we'll know more as we dive into it.

In the previous article in this short series, we learned how to find our neighbor's name using publicly accessible information and how to monitor device activity on their home network. With this information at our disposal, it's time to get into installing and configuring the necessary tools to begin our attack on John Smith's computer.

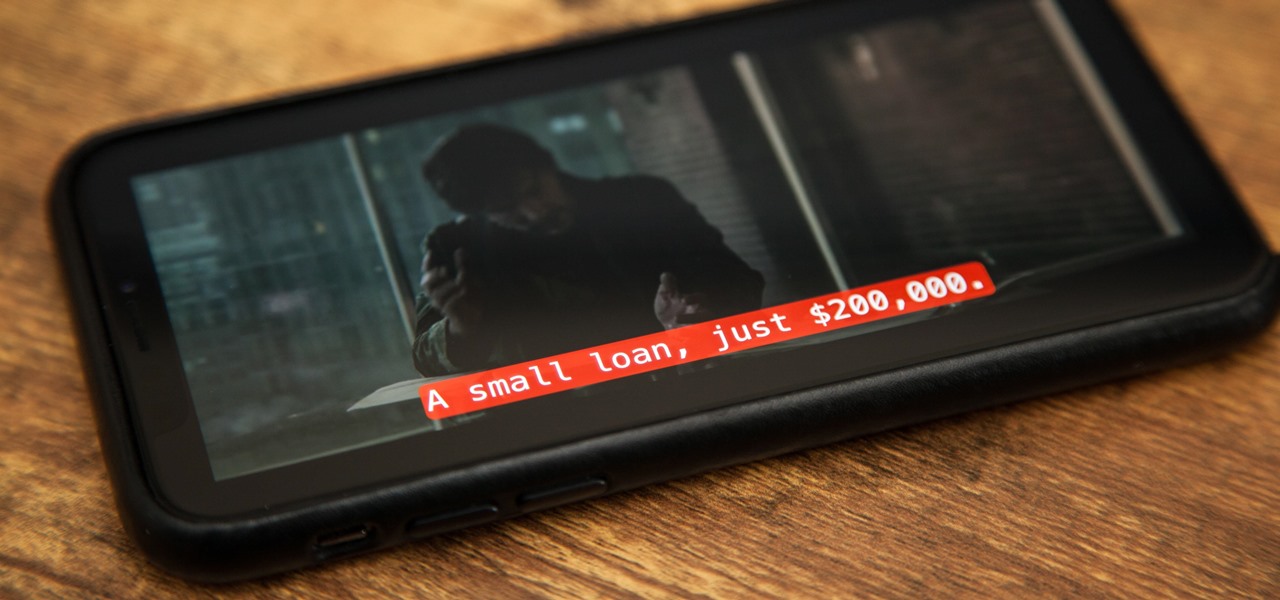
Whether you're watching Netflix on your Android tablet, smart TV, or computer, the process for changing how subtitles and closed captioning appear is the same. Plus, when you customize the font, size, color, and the background, all devices connected to your Netflix profile will update — except for iOS and tvOS devices. A different process is necessary for an iPad, iPhone, iPod touch, or Apple TV.

In addition to the standard "Raise to Wake" option that's been around since iOS 10, the iPhone X, XS, XS Max, and XR have a unique capability that lets you "Tap to Wake" the screen. But these features can get annoying real fast when your screen keeps turning on accidentally, which could even lead to some unnecessary battery drain.

Having your home and work addresses set in Apple Maps makes them incredibly easy to navigate to no matter where you're located. If you move to a new house, stay in a hotel or resort while vacationing, report to a different office, or have multiple job sites to visit regularly, updating these addresses isn't only straightforward — there's more than one way to do it.

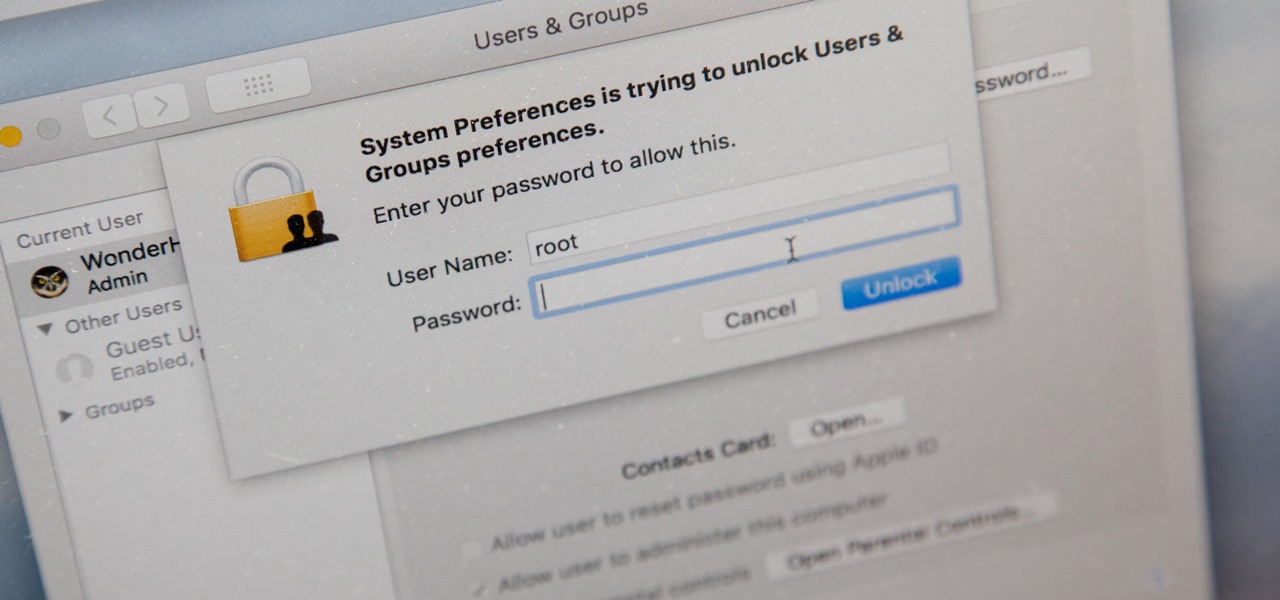
There's a new macOS vulnerability that hackers within physical reach of your computer can use to gain root access to your system and accounts. Just by using "root" as the username and a blank password on a privilege escalation prompt, someone can install malware on your computer, access hidden files, reset your passwords, and more. Root access gives them the ability to do anything they want.

When you run an augmented reality company worth billions of dollars, backed by some of the biggest names in tech, and you haven't even released a product yet, even late night tweetstorms rank as worthy of dissection. Such is the case with Rony Abovitz, CEO of Magic Leap, who decided to spend a little time on Twitter on Wednesday to outline his vision of the future of immersive computing.

Networking is built largely on trust. Most devices do not verify that another device is what it identifies itself to be, so long as it functions as expected. In the case of a man-in-the-middle attack, we can abuse this trust by impersonating a wireless access point, allowing us to intercept and modify network data. This can be dangerous for private data, but also be fun for pranking your friends.

Just as we published our rumor roundup for the HTC U11 Plus, the internet happened: A Facebook video revealed the flagship HTC U11 Plus and the midrange HTC U Life in all their glory. The video was in German and has since been taken down, but according to a translation, it revealed exactly what we should be expecting see at HTC event November 2.

The first big update to iOS 11 since its release in mid-September just came out, so check your iPhone for a software update to iOS 11.1, because there are a few things you'll want from it. While there's no sight of Apple Pay Cash or Messages in iCloud, there are some significant improvements you'll need to know about.

If you were holding out on an iPhone X but still haven't bit the bullet on the $1,000+ price tag, it may be because you're not sure how it will feel in your hands compared to the iPhone 8 or iPhone 8 Plus, which are pretty much the same size as the last three iPhone models you know and love. We can help you figure this out, though, with a simple printout to compare phone sizes in your hand.

In our previous article, we learned how to take advantage of a feature, Dynamic Data Exchange (DDE), to run malicious code when an MS Word document is opened. Because Microsoft built DDE into all of its Office products as a way to transfer data one time or continuously between applications, we can do the same thing in Excel to create a spreadsheet that runs malicious code when opened. The best part is, it will do so without requiring macros to be enabled.