
Hack Like a Pro: Using Nexpose to Scan for Network & System Vulnerabilities
Welcome back, my budding hackers!


Welcome back, my budding hackers!

As you already know, Hong Hong has been rocked in recent weeks by protests against their Beijing overlords. Promised free and fair elections, Beijing has reneged on this promise and is now telling Hong Kongians (that's what they're called, aren't they?) that they will only be able to vote on Beijing-selected candidates. All that is interesting from a political perspective, but from a technological perspective, the more intriguing story is how the protesters are communicating. Faced with their...

The noodle is a noble thing. And while I love ramen and pasta, I have a real soft spot in my heart for macaroni salad (especially the kind that comes with Hawaiian plate lunch) and the type of pasta salad that's dished up during picnics and barbecues.

Each day, we read about another security breach somewhere in our digital world. It has become so commonplace that we hardly react anymore. Target, J.P. Morgan, iCloud, Home Depot, and the list goes on and on.
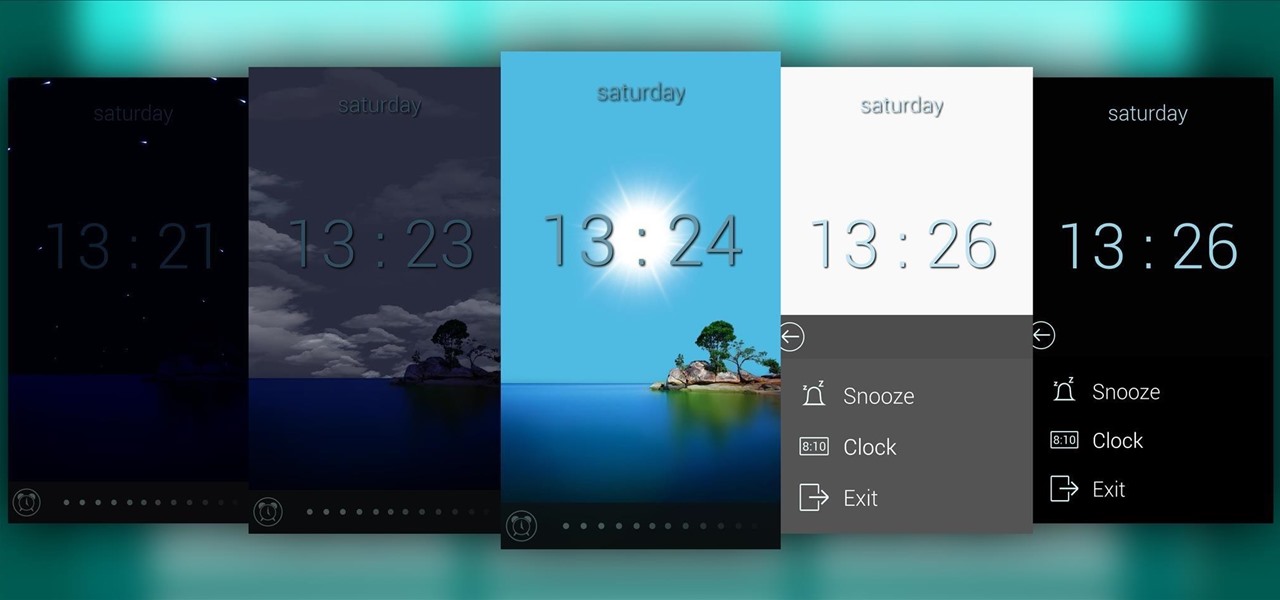
Most alarms just make noise to wake you up, and it can be a bit jarring coming off of a deep sleep to suddenly being woken up by a blaring sound. On the flip side, if you're a heavy sleeper, this might not even be enough stimuli to snap you out of your 8-hour coma.

To prevent melted ice cream from leaking out of the pointy bottom of a cone, plug the hole up with a marshmallow before adding any ice cream on top. This will also give you a nice treat when you're almost finished, as the marshmallow will absorb some of the ice cream.

Welcome back, my budding hackers! When we are looking for ways to hack a system, we need a specific exploit to take advantage of a certain vulnerability in the operating system, service, or application. Although I have shown you multiple ways to exploit systems here in Null Byte, there are still many more exploits available that I have not yet shown you.

It happens to everyone: you set a lock screen password in a hurry and cannot remember it the next day. To unlock your device again, you need to reset the password (or PIN, pattern, etc). There are two official methods of doing this.

Buried deep in the code of many Google apps is a set of debugging options. These options, which are designed for developers to help test the way their apps interact with Google's own, are normally hidden from view.

Want to learn how to make Peppa Pig with Play-Doh? Here is our attempt on showcasing a tutorial on how to make Peppa Pig with Play-Doh.

Lock screen apps are a dime a dozen, but every now and then one pops up that defies expectations. We've already covered some good ones for the Samsung Galaxy S4, including Picture Password Lockscreen (which gives you secret unlock gestures), SlideLock (which improves notifications), and TimePIN (which gives you a more clever PIN).

Automated tattoos are now a reality, with 3D printers being hacked into tattoo machines. Multiple people have posted videos of their 3D printer that can "print" tattoos, with one of the more impressive ones shown in the two videos below.
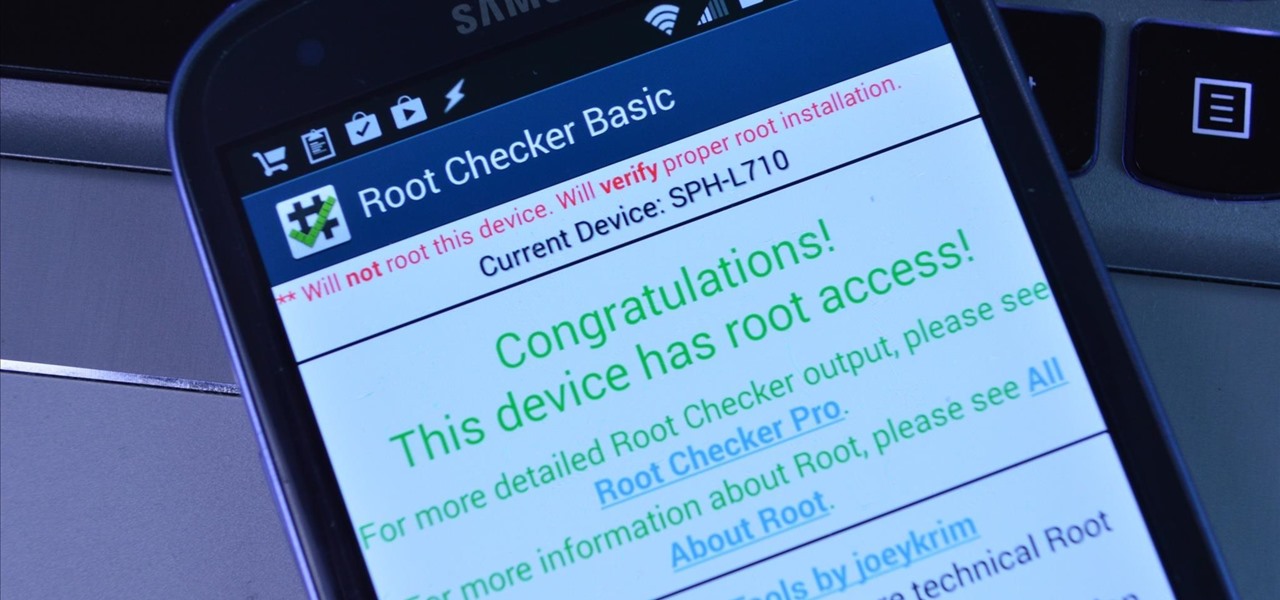
Rooting an Android device used to be a nightmarish labyrinth of .zip files and command prompts, confusing seasoned modding veterans and newbies alike. Thankfully, the process has gotten simpler over the years, with various "one-click" rooting tool kits surfacing and working for nearly every major Android flagship on the market.
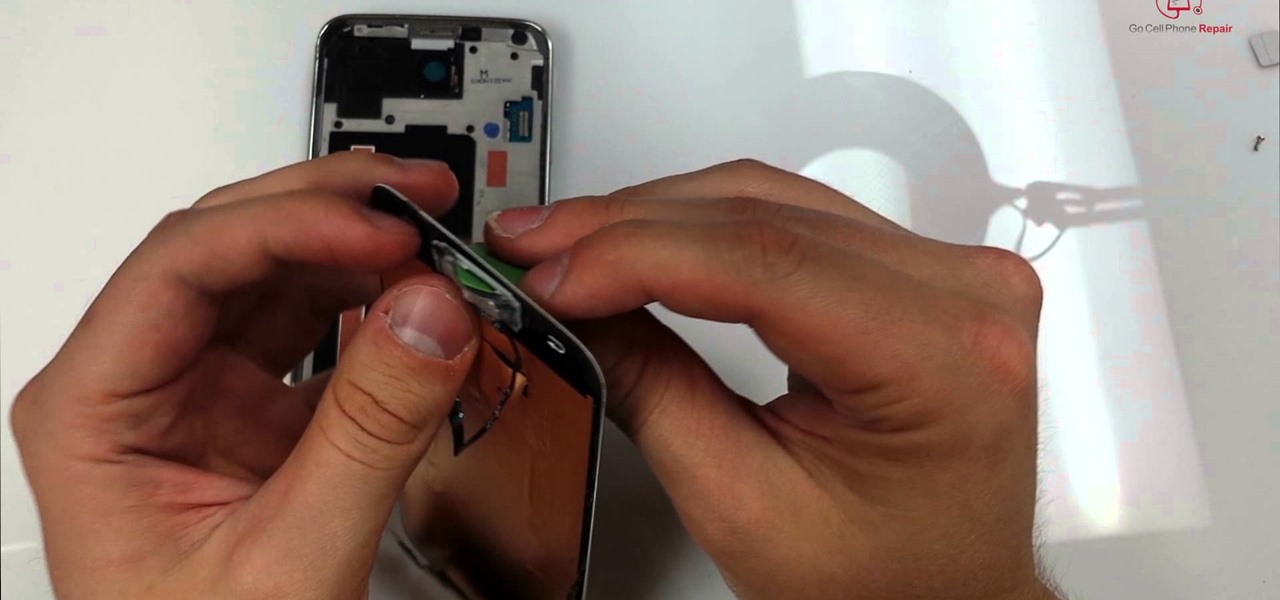
The Samsung Galaxy S5 display can be replaced by most do-it-yourselfers with some basic mechanical skills and a few inexpensive tools. The good news is that once you replace your display assembly your screen will be good as new with no bubbles or dust on the inside. The replacement part is a bit pricey but that is a good percentage of the cost involved with manufacturing this device. Below is a video showing the entire process from start to finish. It's best to turn on your volume for the nar...

While text messaging has become one of the most frequent ways we communicate with our friends, the missing body language, tone of voice, and eye contact can make it difficult to tell when someone is being dishonest. That said, it's not impossible. There are a number of subtle hints you can train yourself to recognize that will to help you detect written lies hiding in your SMS and iMessages. Here's what you should look out for.

Video games have come a long way over the last 30 years. In the late-'80s, Atari, Nintendo, and Sega were taking gaming from arcades to living rooms. Back in 1994, the Super Nintendo and Sega Genesis were in bedrooms everywhere, and over the next couple of years, were slowly being replaced by Sega Saturn, Nintendo 64, and the first ever Sony PlayStation.

While Snapchat's latest update brought messaging and video chatting, it also ruined something for us softModders—KeepChat. With KeepChat, we were able to save pictures and videos sent to us without the other person being notified. It was pretty slick, and I was beginning to miss it.
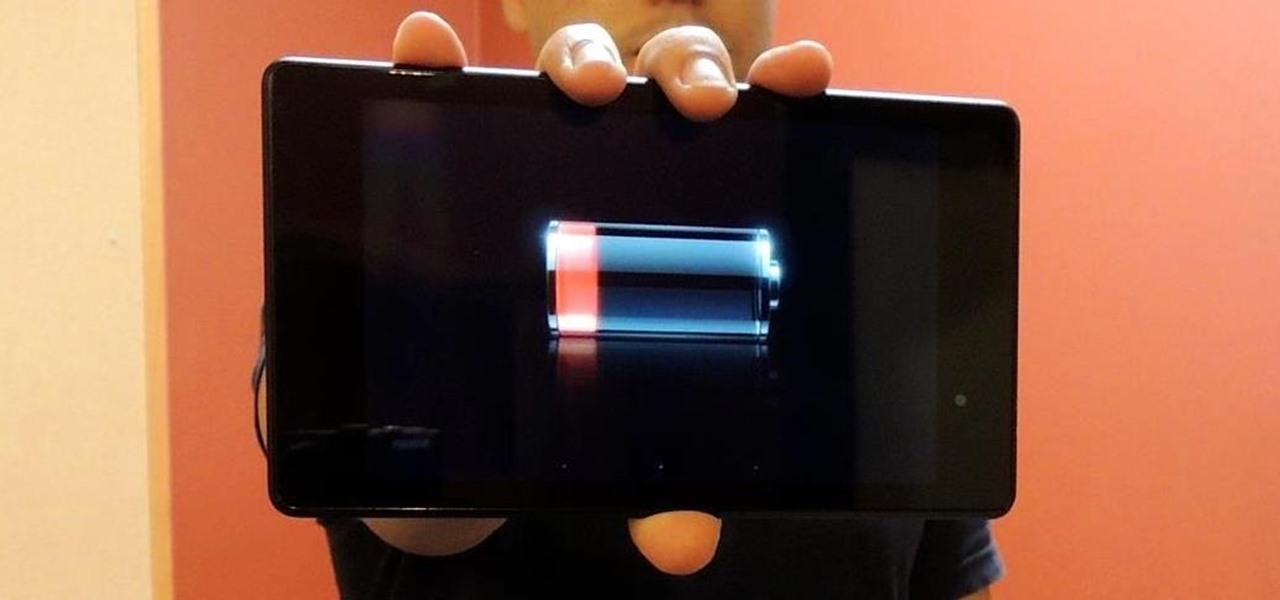
Battery life is precious to all mobile device users, and nothing is worse than running out of it. The only thing that can save a device from the dreaded low battery warning is the charger, but who carries those around?

Welcome back, my hacker apprentices! To enter the upper echelons of hackerdom, you MUST develop scripting skills. It's all great and well to use other hacker's tools, but to get and maintain the upper hand, you must develop your own unique tools, and you can only do that by developing your scripting skills.

If you lend someone your phone, even if it's just for a second, there's a chance they can enter an app and see something you'd rather they didn't. Whether it's a personal email or a private photo, there are plenty of reasons why you'd want to keep snoops out of certain apps.

Welcome back, my greenhorn hackers! In my continuing effort to demonstrate to you how to hack the ubiquitous Windows 7, we will going after that notoriously vulnerable Adobe Flash that is on nearly every client Windows system (you are not likely to find it on servers).
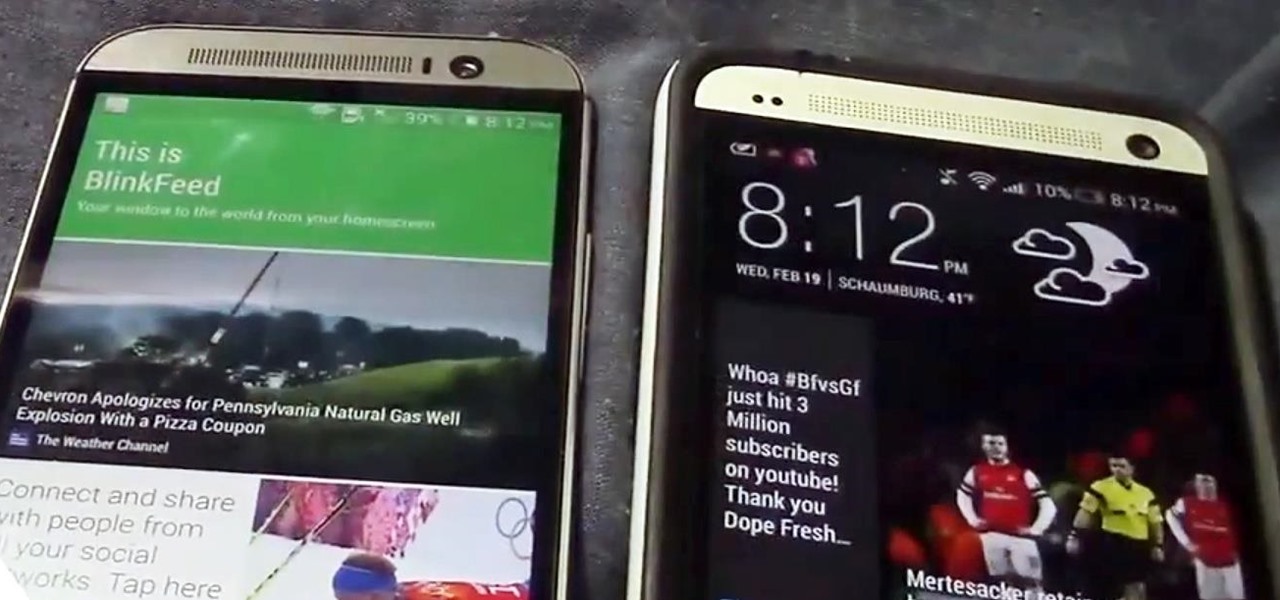
Confirming a lot of what we already knew, now we have a physical walkthrough video on HTC's new flagship, the M8. Or, maybe the "New HTC One", but let's hope that's not the name of the final product. Before we get to the video, here's what we already know:

The status bar is an omnipresent force on our Samsung Galaxy S3s; always there to give us that vital information about battery life, date and time, Wi-Fi access, and much more. But there's just something about that default black bar that's so...boring.

When lending our iPhone to our kids, siblings or friends, it's not uncommon to have it returned with what seems like a million apps open in the background. What's worse is being too lazy to close all those open apps, in turn having our battery drain much faster than normal.

Ever since its introduction back in iOS 6, AirPlay has been helping us iOS and Mac users stream content over to an Apple TV or third-party speaker system. It's an incredibly useful feature. However, it's also severely limiting. The few compatible products out there are extremely expensive, making wireless streaming a not-so-easy task.

This year's NFL playoffs have been nothing short of spectacular. With Super Bowl XLVIII coming up on Sunday, February 2nd, people are already gearing up for another classic showdown between the NFC and AFC, and this time it's the Seattle Seahawks versus the Denver Broncos.

Most of us are used to just grabbing a bag and throwing it in the microwave when we want popcorn. It's easy, convenient, and requires little to no cleanup. But what about those times when you're away from home and don't have access to a microwave?

Just days after news spread that Snapchat could be exploited by spammers, an anonymous group of hackers have released the private information of over 4 million users of the popular photo-sharing application.

Every time Apple releases a new product or software update, people quickly figure out exploits in order to bypass the lock screen without having to type in the passcode. It happened last year in iOS 6, so it's not surprising that it happened again in iOS 7.

Welcome back, my aspiring hackers!

Welcome back, my greenhorn hackers! I've been writing these Linux tutorials in an attempt to fill the void in the education of some aspiring hackers into the Linux operating system. There is a lot to know, and in this tutorial, we'll look at Linux file permissions. Step 1: Checking Permissions
There are a ton of cool features available on your Samsung Galaxy Note 2, but if you're a softModder, you can make your phone do just about anything.

Welcome back, my hacker wannabees!

With more people joining the internet scene each day it's important that it's security is.. well it has to be good. Of course everything can be hacked and that's the way hackers work. They know there IS a vulnerability but they don't don't know the rest. in this article i'll try to explain the big difference between HTTP and HTTPS
Pringles are just as well known for their cylindrical packaging as for their suspiciously addictive fried crisps. Yes, that's crisps—not chips.

Most of us have a designated spot where we like to charge our devices, but no one likes to look at a giant, tangled mess of cords. That's why inductive chargers are so awesome. They allow for wireless charging, and are a lot easier on the eyes. But what if you don't even want to leave the charging module sitting out? This relatively simple hack by YouTube user lobbamobba lets you hide the charging module inside a nightstand or other piece of furniture so that you can juice up your device with...
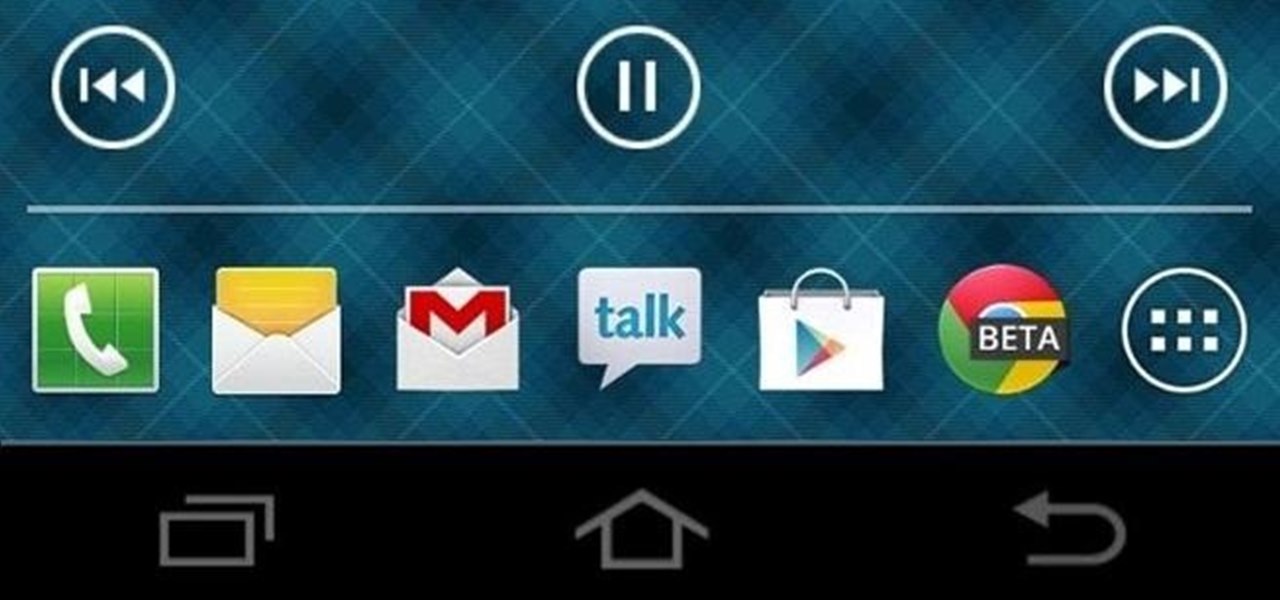
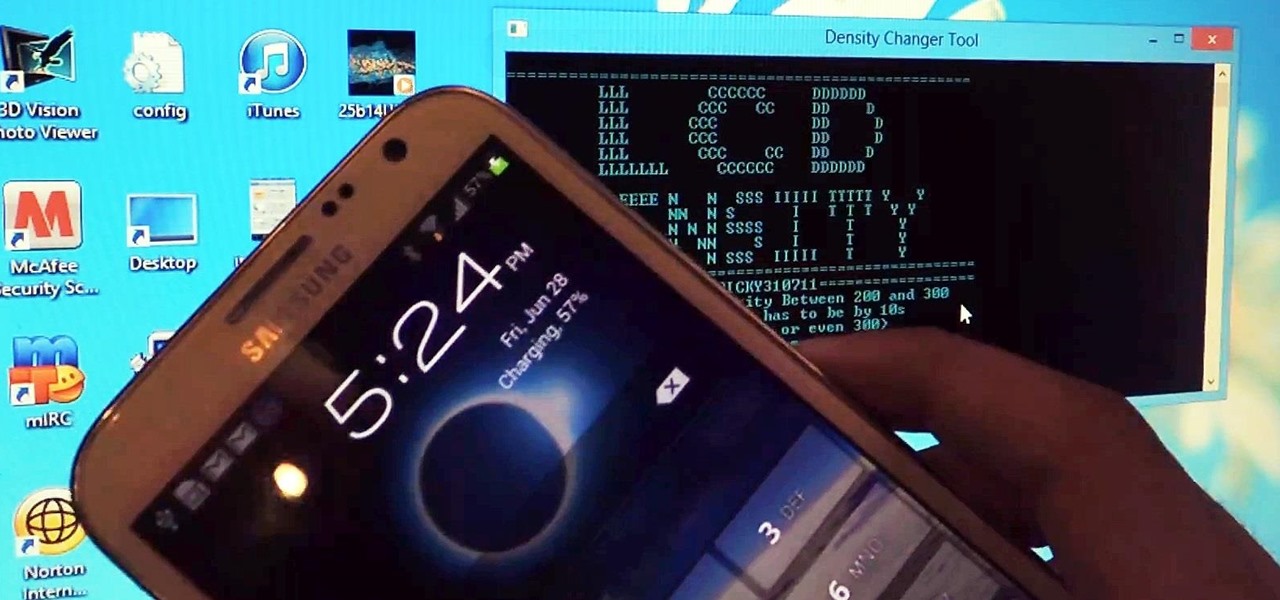
Samsung bucked the trend and threw hard keys onto the Galaxy S3 while most manufacturers are going the soft key route. This hack will add on-screen buttons to your TouchWiz-based ROM. You'll need a root file manager with a system writable text editor—I recommend ES File Explorer for this, but feel free to use whatever you want. If using ES, hit Menu, Settings, go down to Root Settings, and check Root Exploerer, Up to Root, and Mount File System.

I loved the Gold Rush unit back in third grade. We went up to the American River and panned for gold, and my panning skills balled above all. I got like three tiny pellets. Of course, it was all fool's gold, aka pyrite, but it was still pretty legit. And this was before wearing gold chains was cool—or not.

For the most part, keyboard shortcuts are great. They save you some time and make it easier to do everything right from the push of a button. But like most things in life, there is always a caveat, and in this case, for me—it's a huge one.

Males fight for dominance in order to gain access to the limited supply of female eggs. This is why male birds expend energy on brightly colored plumage, but female birds do not.