AVG Free from Grisoft provides you with basic antivirus and antispyware protection for Windows and is available to download for free. The only trick is finding it on the AVG website. In this video tutorial, you'll learn how to find and install AVG on your own Windows PC. Take a look!

RC Car Action Magazine Editor Matt Higgins explains how to modify your antenna cap for better wire protection. Make sure that antenna cap doesn't go flying off. Watch this video tutorial and learn how to secure the antenna cap on an RC vehicle.

A pop filter or pop shield is an anti-pop noise protection filter for microphones, typically used in a recording studio. In this how to video learn how you can make a pop filter out of cardboard and fabric for recording with microphones.
This video shows you how to take off the DRM (which is kind of like copy protection) from music and videos that you bought from a Windows Media Player online store like Urge or Napster.

One unique feature of Firefox Mobile is extensions. Extensions allow users to add in features that didn't originally come with the browser. These add-ons provide an array of features, including improvement to privacy and security.

Facebook is testing a new feature in India. One that could help you protect your profile photos from being used on sites without your permission.

T-Mobile's credit-checking system was recently hacked, and this one is about as bad as it gets. The names of 15 million customers, their date of birth and social security number, as well as driver's license numbers and additional information was illegally accessed, meaning the potential for identity theft here is huge.

Want some protection for the front of your new Arrma-RC Vortex? Here's how!

This gorgeous '60s hairstyle was inspired by the Audrey Hepburn film "Breakfast at Tiffany's." This look is quite elegant and suitable for formal events. Most importantly, it is very easy to create.

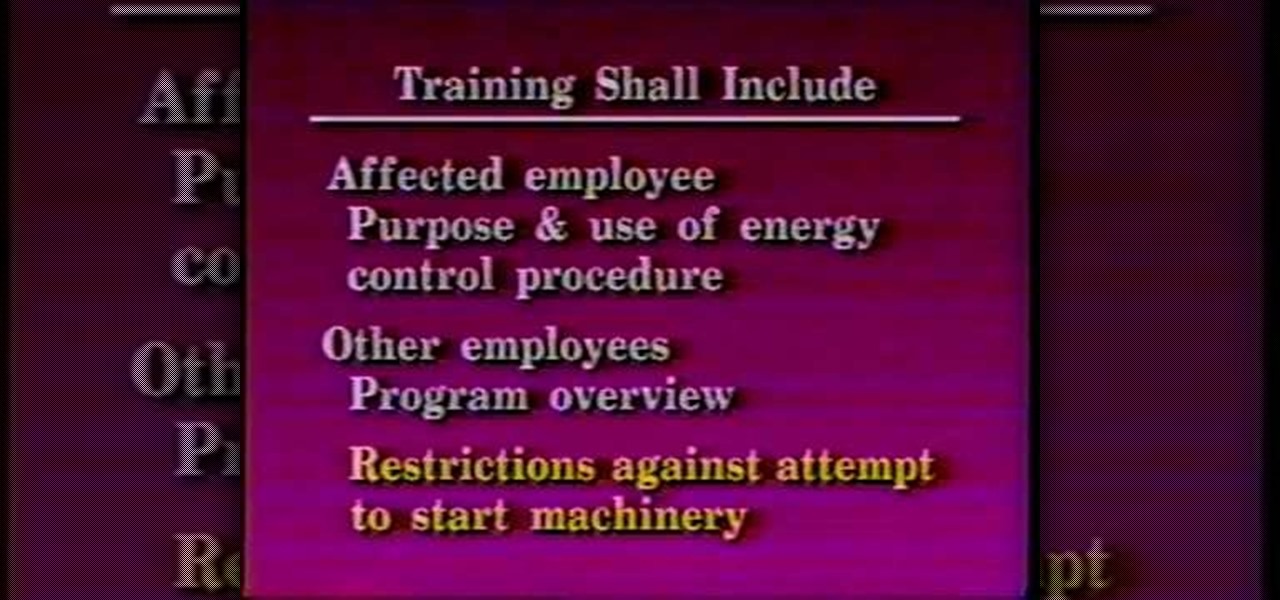
This video aimed at electricians, is designed to help employers and employees what is required in the standard that is applied for the control of energy during maintenance and servicing of equipment and machinery. Employers are required by law to develop proper lockout safety procedures and provide proper protection materials and safety training. This video is highly important for any electrician, apprentice or journeyman, because it will help prevent injury… or even death.

Digidesign has transitioned all of their plug-in software copy protection from floppy drive based key disks to copy protection authorizations that reside on the iLok technology provide by PACE. The following is some information about iLok technology.

In this video we learn how to make a poppet. A poppet is generally used to give protection, healing to the ones we love. It may be our cat, aunt, home, or whatever we like to do it for. Here in this video we make a poppet for an animal. So the requirements are color shields, scissors, lavender and roots (for protection), citrine. Citrine helps in cleansing. Draw the shape of the animal we require on a cloth of two stacks and cut it using scissors. Use the thread to attach the edges. Leave a s...

While Apple is full steam ahead on iOS 18, which is expected to drop sometime next month, it hasn't forgotten about iOS 17, which still dominates most users' iPhones. On Aug. 19, Apple issued a rerelease of its iOS 17.6.1 software for iPhone.

If you're on the hunt for a profitable side-gig, or even a completely new way to to make money, you'll want to take a look at Upwork, a leading freelancing platform that connects skilled freelancers with clients from all over the world.

As smartphone users, we live in dangerous times. The value of phones continues to rise, making them prime targets for thieves. In 2015, the FCC estimated that one million phones are stolen each year, and with several devices starting to hit the $1,000 mark now, these numbers are sure to rise. But what do you do if you fall victim to phone theft?

You know the signs—sneezing, fever, nagging cough, no energy, no appetite. It's the flu, but this time, it's your dog who's down and out. Yes, dogs get the flu, too. However, a team from the University of Rochester Medical Center and their collaborators have developed a new vaccine that may make the doggy flu a thing of the past.

At Apple's highly anticipated special event held today at their headquarters in Cupertino, California, it was announced that their latest software update, iOS 9.3, would be available to the public complete with several new additions. The most notable element of this announcement was two-fold, in the form of new modifications to the Night Shift mode and the Notes app. With regards to Night Shift, the feature is designed to prevent your iPhone from giving you restless nights by adjusting settin...

Check out this Do It Yourself (DIY) RV maintenance and repair video to learn how about RV battery maintenance. Know how to do it to keep your batteries running strong in your recreational vehicle with this RV tutorial video.

Once again, Samsung has certified its flagship Note series with an IP68 rating. With this rating, the Galaxy Note 20 and 20 Ultra have some degree of dust and water resistance.

A powered-off MacBook can be compromised in less than three minutes. With just a few commands, it's possible for a hacker to extract a target's password hash and crack it without their knowledge.

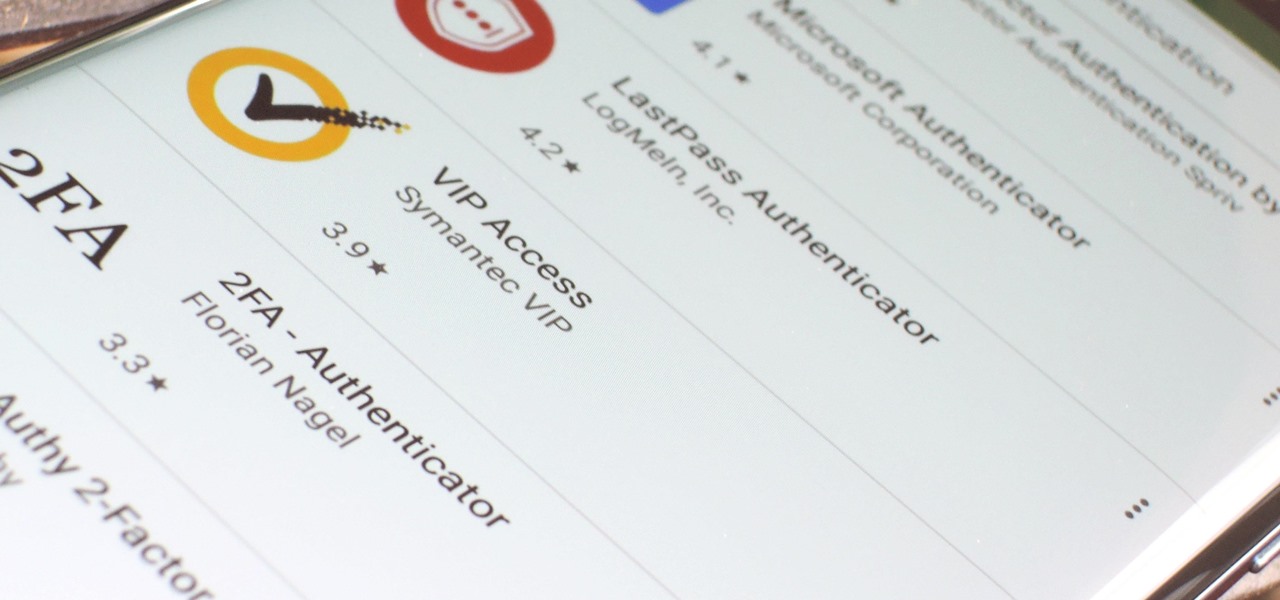
If you want the best two-factor authentication app out there, our pick is Authy. A close second is LastPass Authenticator. If neither of those is to your liking, try Duo Mobile or Microsoft Authenticator. But if you're fine with missing out on great features, then and only then should you look at using Google Authenticator.

Security-minded users can reduce the risk of phishing by enabling Advanced Protection on important Google accounts, requiring a U2F security token to log in. Using these keys isn't intuitive on most popular smartphone platforms, and you can find yourself locked out if you don't plan ahead. You'll need to learn and practice using U2F keys on your device before enabling this layer of security.

Veering from common practice, XDA commenter, "the_commenter", discovered a changelog for the upcoming version of Android 4.4.3 tucked away on Google's servers.

Hack a pair of sunglasses to secretly record audio and video and spend less than $40 in the process with this how-to video. To replicate this hack for yourself, you will need a spy camera and black solar shield sunglasses. For detailed, step-by-step instructions on building your own spy recorder sunglasses, watch this hacking how-to from Kip Kay of Make Magazine.

Kipkay never fails to impress, and this so-called "condom hack pack" is no exception. Who knew there were so many useful uses for a condom besides the obvious! In this Kipkay two-part video, learn how to hack condoms for nine different uses.

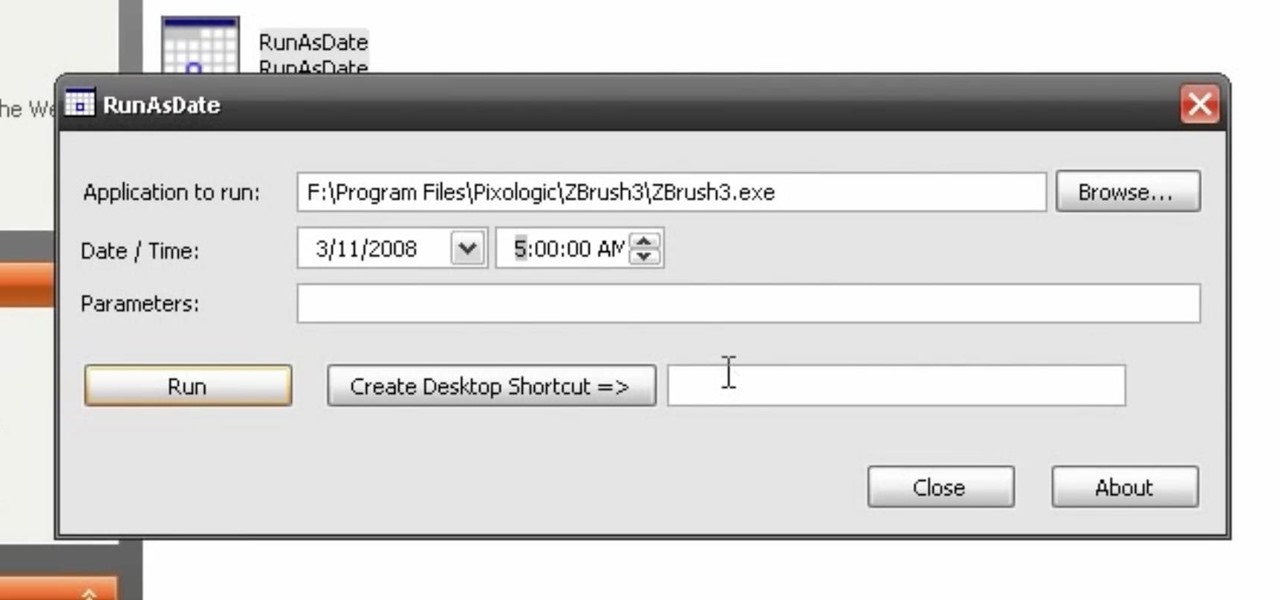
With this video tutorial, you'll learn how to hack demo versions of applications such that they'll run indefinitely. You'll just need to modify the date and time on your computer. Learn how to use trials of programs without them ever expiring instead of buying the real thing with the hack outlined in this how-to video.

You never know when you're going to need a knife. Whether you carry it on your person for protection or simply use it to open stubborn packaging and envelopes, pocketknives are super practical yet also very dangerous if they accidentally open up in your pants.

This hair tutorial is called a wispy bird's nest after its, well, wispy quality and organized jumble of hair strands that forms into a cohesive whole.

Whatever your favorite flower may be, you can't deny that roses are the most romantic and alluring flowers around. In this tutorial, Reiberry bases a delicate hairstyle on the robust beauty of a rose. This pinned-up side bun is unlike any chignon you've ever seen, and though a bit difficult, the results will be well worth the effort.

Using a curling iron on your hair doesn't have to just mean curly hair. By alternating your curling method and holding the curling iron at different angles, you can actually create different types of curls as well as loose waves.

This hairstyle could easily be mistaken for simply missing a spot while you're pinning your hair into an updo during the morning rush, but the lovely rosebud hair accessory ties it all together.

This video explains how to build a shaded vegetable garden. The instructor begins the video my explaining the benefits using a shaded garden as it offers protection from hail, heavy rains and gives you the ability to control the outdoor temperature better. The simplest way to build your shaded building is to place large wood forms into the ground and place wood planks over the top of each and nailing them into place. The entire frame is then covered with a plexiglass roofing to keep out rain ...

“Great beach hair” doesn’t have to be an oxymoron, if you follow our advice in this how-to video. The elements aren't always kind to your hair, but an arsenal can keep your hair in top shape. To help tame your hair at the shore, try leave-in conditioner, anti-frizz spray, straightening cream, clarifying shampoo, baby shampoo, apple cider vinegar, a swim cap, and when all else fails, a hat (which is great protection from the sun-your skin will thank you too). Check out this video hair styling ...

To pick locks, one must either have an expensive lock-picking set or be skilled with whatever they have available to them. Bobby pins, soda cans, and even butter knives can get the job done, but each needs to be reworked into something more appropriate for the lock in question.

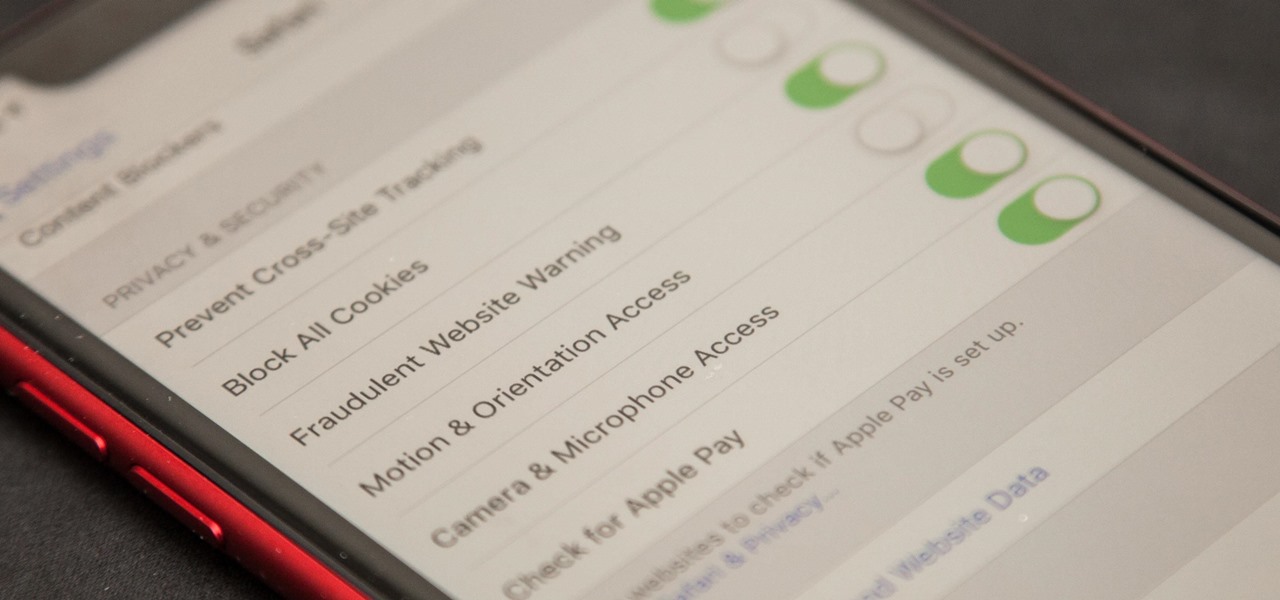
Apple first added the "Do Not Track" option to Safari in iOS 7, which sent a request to site owners and advertisers to not track your browsing activity. By tracking your activity, those third-parties could tailor content to you that you're more likely to interact with. While the feature was always opt-in, it's no longer a feature at all in iOS 12.2 on your iPhone.

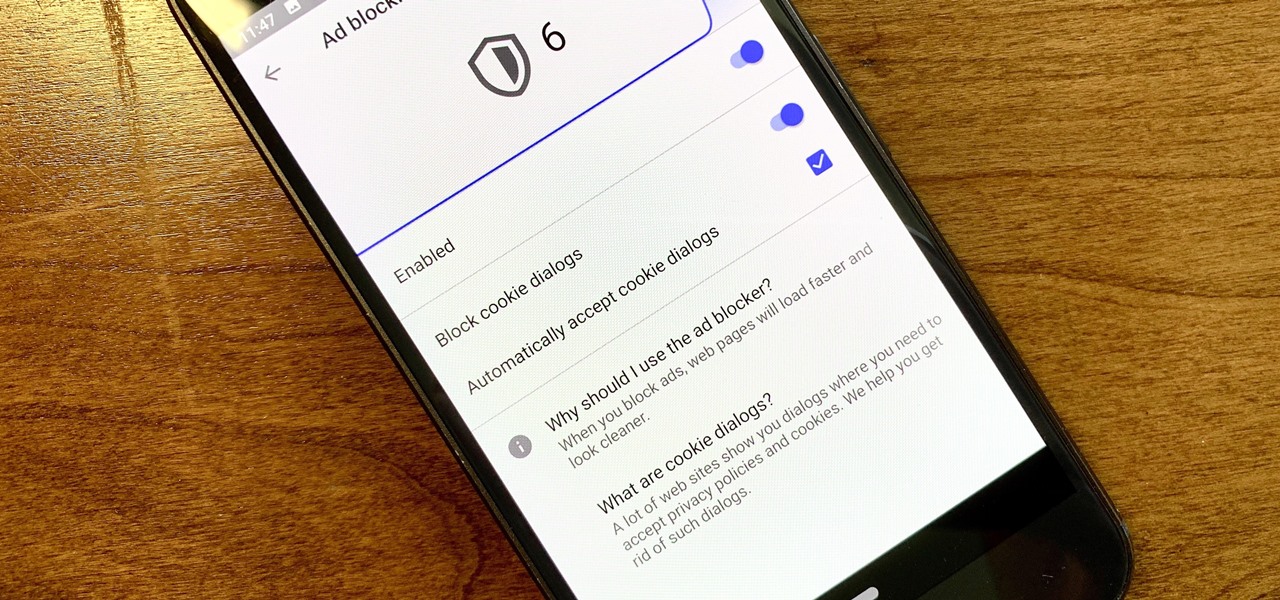
Ever since the GDPR was implemented, it seems every website on the internet needs to inform you of how its privacy policies have changed. If your web browsing experience has been marred by a constant barrage of these cookie pop-ups and privacy dialogs, you should know there's an easy way to block these web annoyances so you never have to tap another checkbox or accept button again.

Project Fi, Google's MVNO, is running a new promotion on the latest and greatest from LG. From July 16 until the 29th, whenever you order and activate the LG G7 ThinQ or LG V35 ThinQ, you will receive a $300 service credit. When you do the numbers, that equals a minimum of three free months of service.

Smartphones are still "phones," which means communicating with others is usually a primary use. Ranging from a simple "hi" to a more personal conversation and even sharing passwords, our messages should remain private so that only the intended recipient sees their content. While many apps tout end-to-end encryption, not all apps prioritize security and privacy.

While it may not be an obvious feature, Apple actually built a way into iOS that lets you hide specific pictures and videos in the Photos app that you want to keep on the down-low, for your eyes only. If you show off your photos a lot or stream slideshows to your TV, this is a great way to keep less appealing content private.

Due to the overnight success of smartphones, millions of people are connecting with others. Currently, over 15 million text messages are sent every minute worldwide. Most of this communication is happening in the open where any hacker can intercept and share in the discussion unbeknownst to the participants. However, we don't need to communicate insecurely.