Passwords are everywhere. We use them to unlock phones, computers, websites, encrypted disks, encrypted files... the list just goes on and on. Savvy users will already have a password manager of some sort that can generate a very strong password on a per site basis. However, these password managers also require a password. Not only that, it has to be something memorable.

Why, for the love of God, do people keep inventing ridiculous devices that make the simplest things more complicated in the name of convenience? This may be a rhetorical question that will forever go unanswered—because these crazy gadgets just keep rolling out, one after the other.

Desserts always taste better when they are sugar-coated—and even more so when they're coated in powdered sugar. In particular, crinkle cookies—cake-y cookies that are chewy on the inside and crispy on the outside—are famous for the powdered sugar that creates their cracked appearance.

I've cracked thousands of eggs in my life, yet I still usually mess up when I make my morning eggs. Sometimes I crack the egg to hard and end up leaving half of the white on the counter. Other times I don't crack the egg hard enough, and end up spending 20 seconds digging with my fingers until I can pry apart the shell. Sometimes I puncture the yolk on the shell, and other times the entire thing slips out of my hands.

Master Lock combination padlocks have been known to be vulnerable to an attack that reduces their 64,000 possible combinations down to 100. I've devised a new attack for cracking any Master combo lock that simplifies the process and reduces the amount of work down to only 8 combinations.

Welcome back, my budding hackers! With this article, I am initiating a new series that so many of you have been asking for: Hacking Web Applications.

Welcome back, my novice hackers! As we saw in my first tutorial on Facebook hacking, it is not a simple task. However, with the right skills and tools, as well as persistence and ingenuity, nothing is beyond our capabilities.

A lot of people rely on the date on the packaging to tell them when food has gone bad, even with eggs, but the sell-by dates are often somewhat arbitrary and are not expiration dates. If you've been tossing your eggs based on the dates on your carton—you could be wasting perfectly good food.

Welcome back, my rookie hackers! A short while back, I began a new series on database hacking, and now it's time to continue and extend your education in that field. As you know, the database contains all of the most valuable info for the hacker, including personally identifiable information, credit card numbers, intellectual property, etc. So, it's the ultimate goal of cybercrime and the APT hacker.

How to cut Drywall, Sheetrock, Plasterboard. THE EASY WAY! G'day Knuckleheads, Uncle Knackers here and welcome to Video Two of my ten part series titled 'My Top Ten DIY Tips' as nominated by you..

Brushing your teeth is a necessity. You don't want to walk around with yellow teeth and stinky breath, and it's common courtesy to those around you to care about your personal hygiene at least that much.

Don't let that stuck drawer aggravate you on a daily basis; find the problem and fix it once and for all.

Brute-forcing is an easy way of discovering weak login credentials and is often one of the first steps when a hacker finds network services running on a network they gain access to. For beginners and experienced hackers alike, it's useful to have access to the right tools to discover, classify, and then launch customized brute-force attacks against a target. BruteDum does it all from a single framework.

It turns out that the video Magic Leap released earlier today was indeed a teaser for the public release of the Game of Thrones experience for meant for all Magic Leap One users.

Every recipe on the face of this planet (okay, maybe a slight exaggeration there) ends with the same six words:

Lenovo unveiled the latest Motorola smartphones, Moto Z and Moto Z Force, today at Tech World '16. As expected, both models include strong magnets on the back that allow users to snap on various Moto Mods attachments such as a battery pack, projector, or JBL speakers.

In this article I will show you how to obtain victim's credentials without cracking any hashes. There are a couple of ways to perform this task (for example dumping the SAM file and cracking the NTLM hashes), but here I will explain how to do it using PowerShell and a bit of social engineering. We are going to create a fake login popup.

Brought to you by Tomcat. Falling snow, warm fireplace, delicious hot cocoa, quiet reading time, mouse. Quick quiz - which one is not like the other? Nothing can ruin a perfectly cozy afternoon in your home like a pest on the loose. With dropping temperatures, you may have some unwelcome residents, like mice, looking for shelter from the cold.

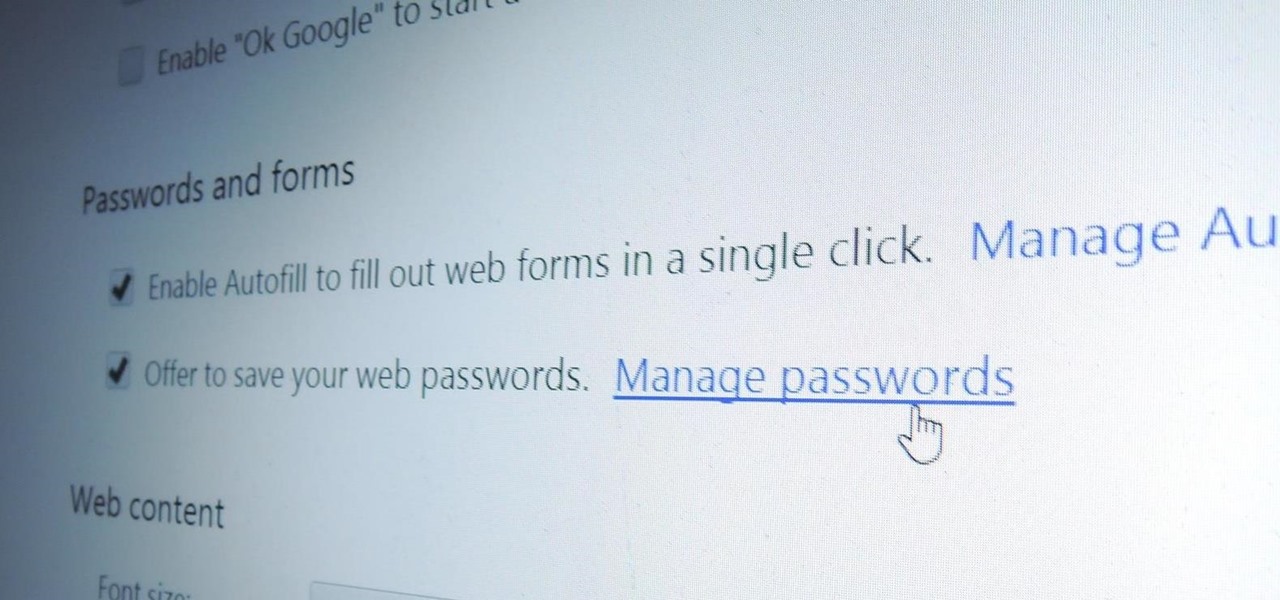
Chrome, Firefox, and Safari all provide built-in features that allow you to save your username and password for your favorite sites, making the process for entering your credentials a breeze when you revisit them.

Netflix releases monthly reports on major ISPs relating to how well their service works on each provider. The purpose is to educate the public on their choice of service provider, but since many of us hardly have any choice at all when is comes to an ISP, it backhandedly works to shame them (if they're even capable of feeling shame under all those millions of dollars).

Welcome back, my neophyte hackers! Have you ever had a neighbor that you're certain is up to no good? Maybe you've seen him moving packages in and out at all hours of the night? Maybe you've seen people go into his home and never come out? He seems like a creep and sometimes you hear strange sounds coming from his home? You know he's up to no good, but you aren't sure what it is exactly.

Welcome back, my fledgling hackers! There's an evil dictator hellbent on destroying the world, and in one of our last hacks, we successfully compromised his computer and saved the world from nuclear annihilation. Then, we covered our tracks so no one would know what we did, and developed a hack to capture screenshots of his computer periodically so we could track of what he was up to next.

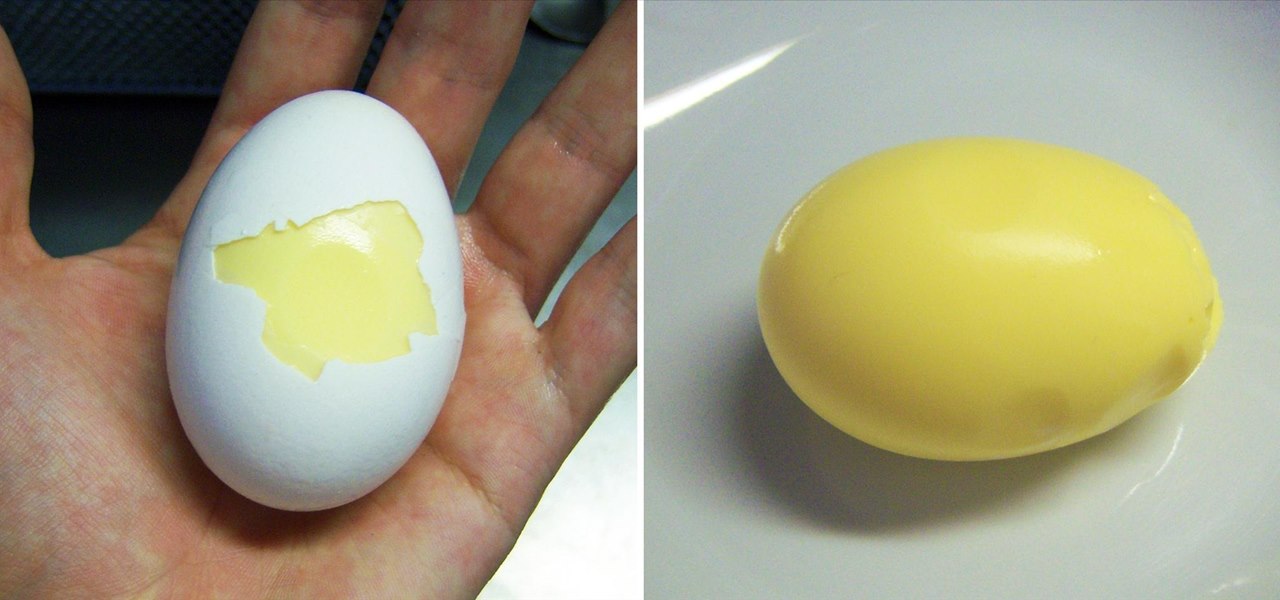
Eggs are one of the most versatile foods imaginable. They can be cooked in tons of different ways, eaten for breakfast, lunch, or dinner, and go with just about anything. Most of us have hard-boiled and scrambled eggs before, but have you ever thought about combining the two? That looks pretty good, doesn't it? But it's not exactly the kind of scrambled and hard-boiled eggs combo I'm referring to. And thankfully, this isn't what I'm talking about either... No, even though balut may look like ...

Let's say you forgot the code to your Master Lock combination padlock. What can you do besides buy another one? Well, there's a surprising abundance of ways to open a combination lock other than with just the combination, some of which will even let you reset the code. Of course, these hacks aren't limited to folks just looking to open their own locks, but let's just assume that's what you're here for.

This video demonstrates how to make a delicious molten lava cake. You need 4 oounces of semi sweet baking chocolate,4 oounces of unsalted butter, 2 eggs, 1/3 cup sugar, and ¼ cup all purpose flour. Let the baking chocolate melt in a double boiler. While it is melting into smooth liquid take a medium sized baking bowl and crack your eggs into it. Then add your sugar to the eggs and blend them. You can use a hand blender or a whisk but it may take longer to blend by hand. Next, take the melted...

Monitoring your blood glucose level is absolutely essential to your health if you suffer from diabetes. You need to keep track of your blood sugar or you could be in danger. This video tutorial will show you the proper way to use a blood glucose meter and give you helpful tips on getting the most out of them.

November 11th isn't just Veterans Day— it's Origami Day in Japan, where they celebrate the traditional art of paper folding. November 11th is also the last day of World Origami Days, a 2-1/2 week celebration held internationally.

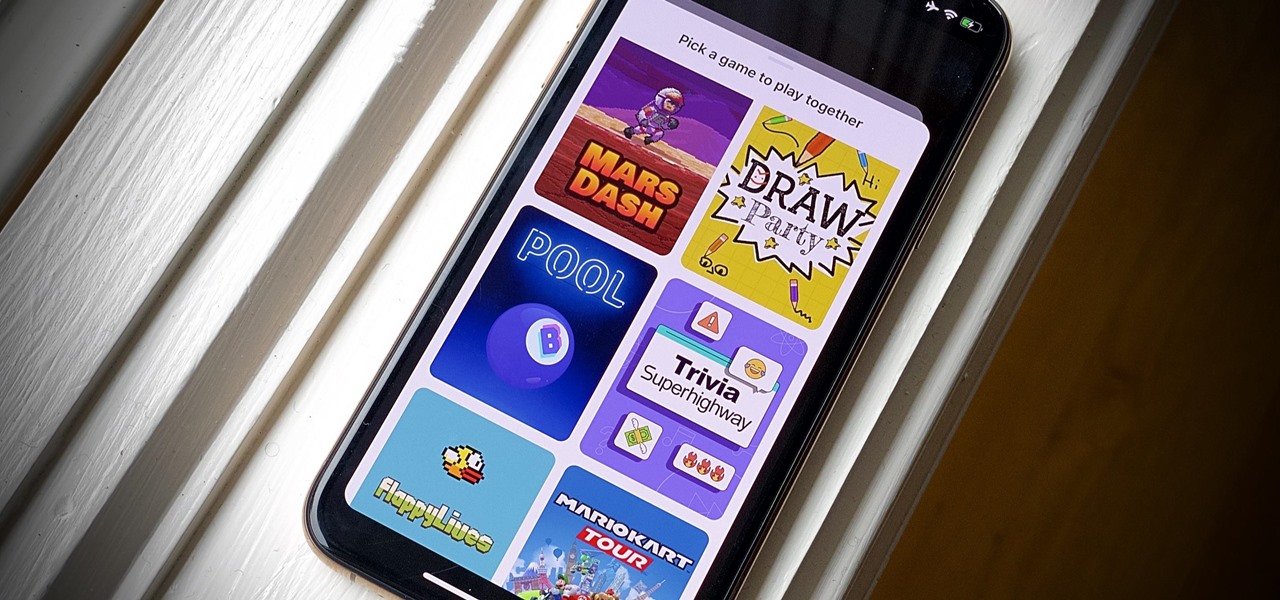
Even for those of us who enjoy spending time alone at home, at a certain point, it just gets boring. We all need social interaction, but with stay-at-home orders, that can be hard to come by. If you're feeling the itch to hang out with friends and have a good time, you should know there are plenty of free multiplayer games for iPhone and Android that will let you do just that — remotely.

There are many ways to attack a Wi-Fi network. The type of encryption, manufacturer settings, and the number of clients connected all dictate how easy a target is to attack and what method would work best. Wifite2 is a powerful tool that automates Wi-Fi hacking, allowing you to select targets in range and let the script choose the best strategy for each network.

If you've grown bored of day-to-day hacking and need a new toy to experiment with, we've compiled a list of gadgets to help you take password cracking and wireless hacking to the next level. If you're not a white hat or pentester yourself but have one to shop for, whether for a birthday, Christmas present, or other gift-giving reason, these also make great gift ideas.

Hacking Wi-Fi is a lot easier than most people think, but the ways of doing so are clustered around a few common techniques most hackers use. With a few simple actions, the average user can go a long way toward defending against the five most common methods of Wi-Fi hacking, which include password cracking, social engineering, WPS attacks, remote access, and rogue access points.

Hashes containing login passwords are transmitted between Windows computers on local Wi-Fi networks. By intercepting and decrypting these hashes using Responder and John the Ripper, respectively, we can learn a target's login credentials which can be later used to gain physical access to their computer.

Word games can expand your vocabulary skills in all sorts of exciting and creative ways. Because of this, both the iOS App Store and the Google Play Store are awash with word games, making it hard to differentiate between good and bad titles. This is especially troublesome if you're looking to purchase a game, as everyone hates to waste hard-earned cash.

Welcome back, my rookie hackers! As hackers, we are often faced with the hurdle of cryptography and encryption. In some cases, we use it to hide our actions and messages. Many applications and protocols use encryption to maintain confidentiality and integrity of data. To be able to crack passwords and encrypted protocols such as SSL and wireless, you need to at least be familiar with the concepts and terminology of cryptography and encryption.

Welcome back, my greenhorn hackers, and happy New Year! Now that your heads have recovered from your New Year's Eve regaling, I'd like to grab your attention for just a moment to preview 2015 here at Null Byte. I hope you will add your comments as to what you would like to see, and I'll try to honor as many requests as I can.

Drawing a woman is a lot like drawing a man, only curvier. You can use triangles to sketch the basic form of a woman, giving you a guideline to sketch in more and more detail until you’ve given her the look you want.

This instructional video shows us how to braid hair with flaxseed gel. First you will need some conditioner, moisturizer and flaxseed gel. You will also need a wide tooth comb. The person who is having their hair done will need to do a cold wash which is washing their hair with conditioner rather than shampoo as it can dry out the hair. First take some styling oil and spray sparingly on the hair. Then massage it on the head. Take some flaxseed gel and spread it on the hair. This gives definit...

In this tutorial, we learn how to use a "no CD" crack to play PC games without a disc. First, go to www.gameburnworld.com and search for your game using the search bar. Once you find the game you want, click on the version that you want. After this, the game will start to download onto your computer using the software you choose. Once it's finished, install it and open up the executable file. Now, move this file and make a copy of it on your desktop. Now you can delete your original copy and ...

You don't have to throw away those broken pots and re-pot the plants inside. In this gardening tutorial, Martin Fish from Garden News shows viewers how to repair cracked pots. With this the tips from this how to video you can save money on plant pots.

How to crack the WEP encryption on a wireless (WiFi) network.