Welcome back, my budding hackers! One of the keys to becoming a professional and successful hacker is to think creatively. There is always a way to get into any network or system, if you think creatively. In previous tutorials, I have demonstrated ways to crack passwords on both Linux and Windows systems, but in this case, I will show you a way to get the sysadmin password by intercepting it from a Remote Desktop session.
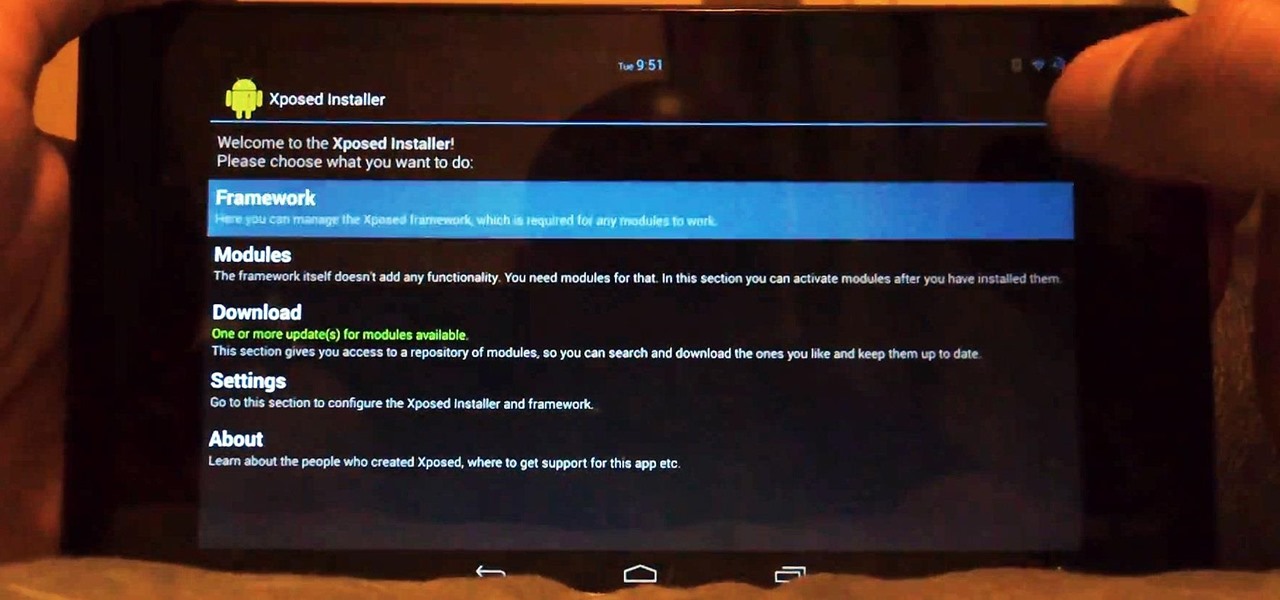
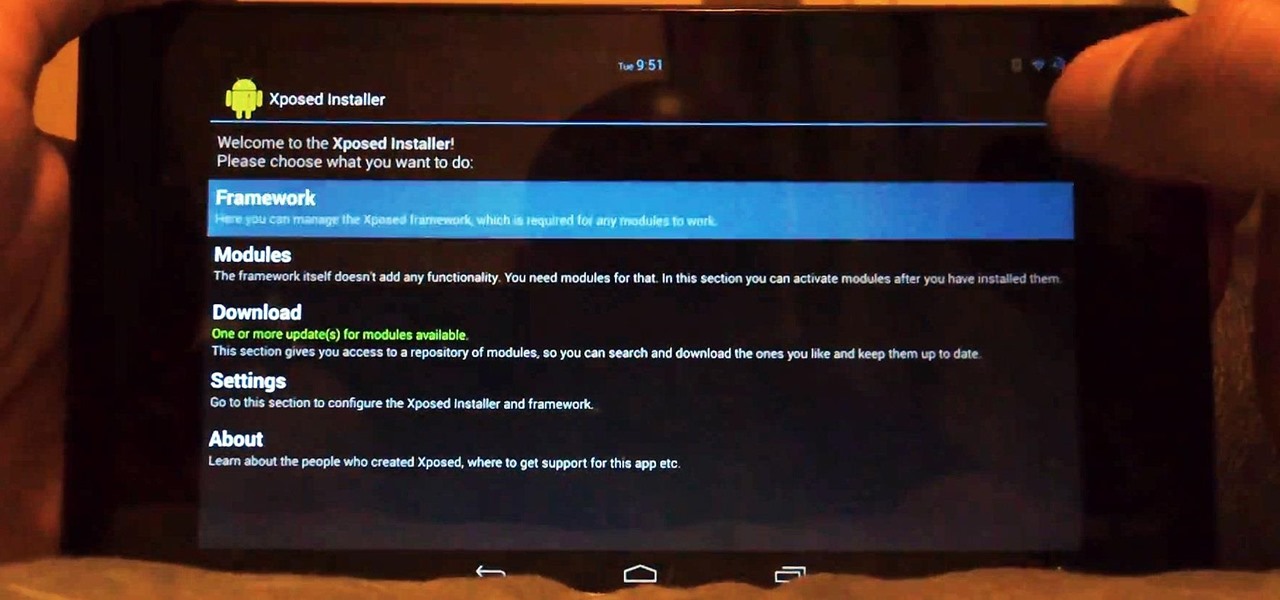
Customization of our Android devices, outside of what Google and mobile carriers allow us to do, used to mandate that our devices were rooted and running a custom ROM.

A good cutting board is almost as important as the utensils you use on it. The wrong type can cause your blades to dull faster, and certain materials hold onto juices (and therefore bacteria) from food. You can wash a plastic board with just about anything, but what about wood?

Ever since the FBI took down the Silk Road and Dread Pirate Roberts last month, many questions have been raised about whether Tor still provides anonymity or not, and if it's now broken. I'll try to address that question here today succinctly from multiple angles, keeping it as simple and plain-language as possible. The Closing of Silk Road

We all know about PRISM. The Surveillance Program allowing the U.S Government to access private user information. Such as, Google Searches, Tweets, Facebook Posts, Private Images, and other private user data. "Hiding" yourself can be very difficult, but it is possible. I'm here to show you How to Become Anonymous & Browse the Internet Safely.

For most people, the battery life on a DSLR is more than sufficient, but if you want to do a really long exposure or time-lapse, one charge might not last long enough to get the shot you want. You can always connect it to an extension cord to charge while you shoot, but that can be really annoying to work around.

Did YOU know...that African Americans have the highest rate of colorectal cancer, and that it is more likely to be advanced at diagnosis? The age for colonoscopy in ACG guidelines dropped to 45 for African Americans in 2009. This digestive ditty about colon cancer screening in Black Americans pays homage to Beyonce's iconic Single Ladies video. Help us to get the word out--Email this link to your African American colleagues and friends and post it to your Facebook or Twitter pals! We can prev...

So many times, you turn on your computer, you open your front door, or you sit down on the couch to watch some well-earned TV, when you think -- Gosh! If only I could do this or this, life could be so much easier! And then, if you were a boring person, you would slouch even further down on the couch and continue to watch those reruns of The Sopranos.

No matter how many PSAs are published on the topic, studies continue to show that we are generally terrible at creating secure passwords and PINs. Using the same password (or variations of it) for multiple sites is another huge no-no that the majority of people ignore, and even though you should change your passwords frequently, most of us don't.

The reason Amazon's Kindle has become so popular over the past several years is due to the amount of digital books one can fit inside—over 1,000 for the smallest Kindle. Gone are the days of lugging around heavy books to school and the airport. Instead we can fit our e-readers snugly inside our bags and never worry about forgetting a book.

What's your Twitter handle worth? If it's considered "desirable" (aka short and simple), it'll get you around 100 bucks, or, if you prefer, the affections of a teenage girl.

Earlier this week, Spiderlabs' vulnerability researcher Jonathan Claudius discovered a key in Windows 7 and 8 registries that makes it easy for anyone with physical or remote access to a computer get a hold of the user's password hints. When the "UserPasswordHint" key is read, the hints are displayed as a code that looks encrypted, but Claudius noticed a pattern of zeroes that could be easily translated back to plain text with a decoder he made in Ruby. He added this functionality to the Meta...

The man in the video shows us how to peel an egg open in 5 seconds by slamming the egg down on the counter (not to hard but at a sufficient speed) and rolling it for a bit then peeling it off with ease. As shown with the comments on the video's page, this task is not as simple as the title states. It takes a lot of practice to crack the egg just right without smashing it, but if done correctly, gets you that perfect, out of the shell, hard-boiled egg. This video teaches you that practice make...

Handyman teacher Hub Kirkpatrick gives a demonstration of how to install shutters to the exterior of one's home. These vinyl plastic shutters are meant to enhance the beauty of the exterior of a house without costing too much. Hub recommends using six 3-inch, hex-headed bolts for each shutter so that it is secured firmly in place. He also adds a cautionary note that one should take care not to over-tighten the bolts because that could result in dimpling and cracking of the plastic shutter.

Find out how everything in a chemistry lab works, from pipettes to burners to recrystallization to storage. You'll get precise instructions on how to work and perform certain scientific duties in the chem lab, whether it's chemical or just ordinary high school science.

Do you like alcohol? Do you like eggs? Well, this is the perfect video tutorial for you!

You can make this delicious stuffed chicken breast recipe in less than 20 minutes at home. Stuff your chicken breast with or your favorite ingredients. For this recipe you will need: flour, eggs, 4 chicken eggs, smoked salt, cracked pepper, garlic, spinach and mushrooms. You can add tofu or turkey bacon for and added crunch. Roll your stuffed chicken breast and sear them on hot pan.

Looking for a great buttercream recipe? Then you have come to right place. Watch this how to video to learn how simple it is to whip up some butter cream to decorate your cakes with.

Your smartphone stays with you everywhere you go, so it's only a matter of time before you spill coffee all over it or drop it on the ground. For some of you, it has already happened, perhaps even multiple times. That's why we thought it was important to find out which flagship phones are the most life-proof.

Skulls. What spooky Halloween décor or staging of Hamlet is complete without a skull or two popping up? For ghoulish special effect and/or setting a dramatic scene, skulls are absolutely integral. Well, with some artistry, hardware supplies, and a good dose of patience, you can create your own inexpensive prop skulls for use however you please.

Today's cheerleading incorporates difficult stunts and gymnastics into the routines. ESPN even now broadcasts the National High School Cheerleading Competition nationally! Madonna, Paula Abdul, Sandra Bullock and even Ronald Reagan were all cheerleaders! So if you or your children want to crack next year's squad, learn from our expert Shyra Fernandez. Shyra will show you the correct way to perform various advanced jumps and stunts that will get you on your way to being a "crack" cheerleader.

In this video, we learn how to make Maui style chicken noodle soup. You will first need to chop garlic, carrots, celery and onions and put them into a pot with water and chicken thighs. You can now season the pot with Hawaiian salt, cracked pepper, chili pepper and sesame oil. Let this simmer for full flavor. When finished, strain the pot and remove the chicken from the bone. Now return chicken and vegetables to the pot now with egg noodles and corn fresh from the cob. Let this simmer until t...

You’re on a mission to make the perfect fried egg and inevitably a little piece of eggshell falls in. Your egg is not ruined. Just take a larger portion of the shell and dip it against the escaped shell. No, more surprises in your breakfast.

Those smooth oval shells just seem to jump right out of your hands. When an egg hits the floor it is a gooey mess but not need to use an entire roll of paper towels trying to pick up the pieces. Cover with salt and the mess and be swept up after only a few minutes.

Those moisture cracks in your concrete driveway could have been prevented. This how to video hows you how to keep your concrete driveway protected and looking good. Its a total DIY project.

A simple recipe for this anytime food. Ingredients

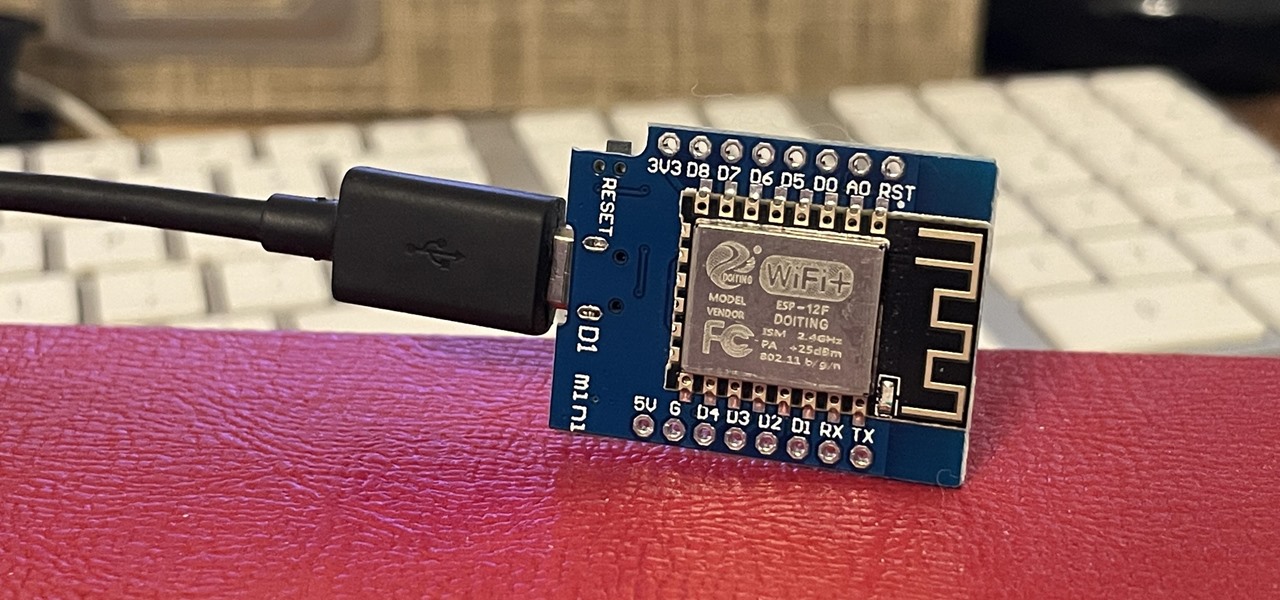
If you've wanted to get into Wi-Fi hacking, you might have noticed that it can be pretty challenging to find a safe and legal target to hack. But you can easily create your own test network using a single ESP8266-based microcontroller like the D1 Mini.

Wi-Fi networks come in two flavors: the more common 2.4 GHz used by most routers and IoT devices, and the 5 GHz one offered as an alternative by newer routers. While it can be frustrating to attack a device that moves out of reach to a 5 GHz Wi-Fi network, we can use an Alfa dual-band adapter to hack Wi-Fi devices on either type of network.

If you want to carry a variety of network adapters without looking suspicious, a perfect solution is accessing them through Airserv-ng. Tucked away in the Aircrack-ng suite, this tool allows a hacker to plug any number of network adapters into a Raspberry Pi and access them over a Wi-Fi or Ethernet connection.

If you're ever faced with a situation of handing over your iPhone to law enforcement (or getting it taken forcibly), whether by the police, feds, or court system, there are things you can do to prevent them from getting access to all that potentially self-incriminating data. And it takes less than a second.

A rainbow table can be thought of like a dictionary, except instead of words and their definitions, it holds combinations of characters on one side and their hashed form on the other. What is a hash and why would you want to know what random combinations of characters are hashed into?

Any internet user will need to download files eventually, and most simply have faith that what they are downloading is trustworthy. This doesn't give much clarity into the contents of the file, but if the file's author published the original checksum, comparing it to the SHA-256 hash of the downloaded file can ensure nothing was tampered with.

Besside-ng is the hidden gem of the Aircrack-ng suite of Wi-Fi hacking tools. When run with a wireless network adapter capable of packet injection, Besside-ng can harvest WPA handshakes from any network with an active user — and crack WEP passwords outright. Unlike many tools, it requires no special dependencies and can be run via SSH, making it easy to deploy remotely.

Now that Fyre Festival co-founder Billy McFarland is charged with fraud, this is the perfect time to list off those top 15 influencers who promoted tickets to the disastrous event to their loyal followers, right?

Containers are isolated software instances representing applications, servers, and even operating systems—complete with all of their dependencies, libraries configuration files, etc.—and they're taking over the corporate world. The ephemeral, portable nature of containers help them stay current and speedy, and they can work on pretty much any computer, virtual machine, and cloud.

As a former repair tech, I've heard the same reasons over and over as to why people opt not to purchase phone insurance. Some cite the cost—why pay extra every month for insurance when you're careful with your phone? Deductibles are expensive, so why not just spend that money on a repair instead of getting a refurbished phone as a replacement?

With Passover soon upon us, many Jews are dreading a week (or eight days for Conservative and Orthodox Jews) of making matzo, the staple of their diet. Matzo is also known as "the bread of affliction," and I'm pretty sure it's because by day three or so you're convinced that matzo is the 11th plague.

Your slow cooker isn't just for making lunch and dinner—it's also perfect for making a complete and super delicious breakfast with little work.

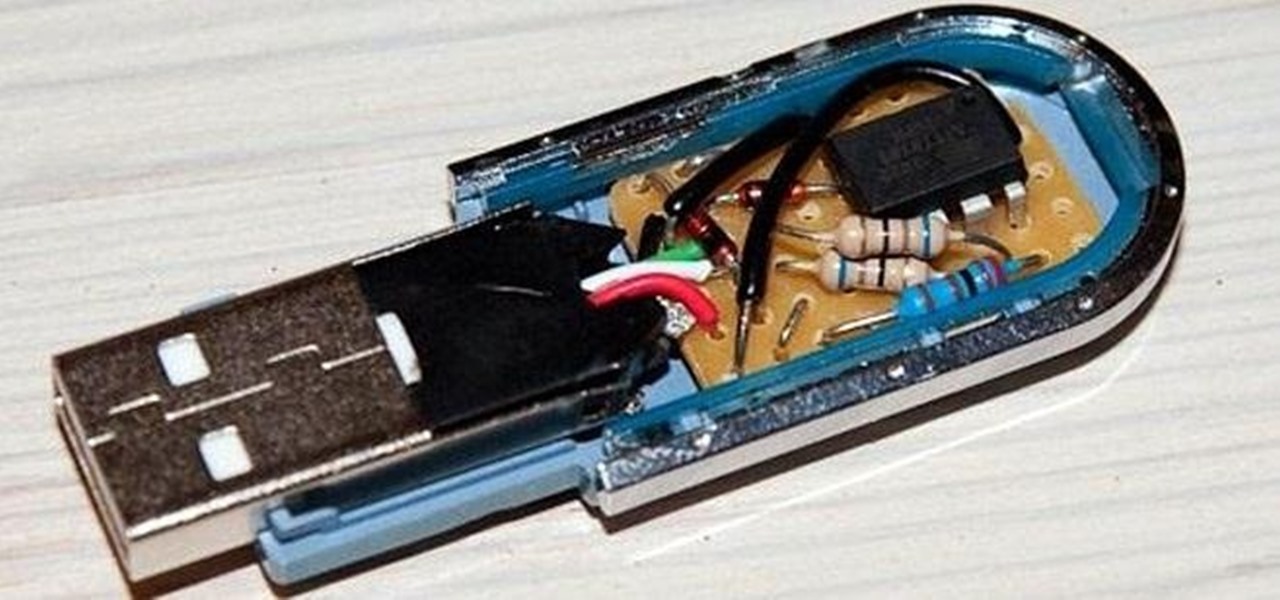
Welcome back, my novice hackers! Episode 6 of Mr. Robot has come and gone and, as usual, it did not disappoint. Once again, our hero, Elliot, has used his extraordinary intellect and hacking skills to awe and inspire us.