In this video, Mark Donovan of Home Addition Plus shows you to remove ceramic tiles from a shower. Before you begin, remove the shower head and shower handle, leaving the walls bare. A lot of dust and debris will be produced so you should wear safety glasses and to protect the shower pan from damage, you should cover it up. Card board should suffice. Starting from the bottom, place the chisel on the edge of the tiles and tap it with a hammer. For the tiles in the middle, you can use a flat ba...

Bed Bug control for luggage is the best way to protect your luggage from infestation. What you will do is, open your luggage and any zippers you may have on your luggage and spray it down the best you can. You will want to spray the seams and any closed area inside and outside you luggage. You should also spray down your handle and wheels (if available). Bed bug control will keep the germs from different hotels or any where you travel, so that it doesn’t follow you back home.

Nobody likes being suckered by a con, but when you're the one doing the con, it's a completely different story. Especially when it's something as classy as Three-Card Monte. If you know the tricks and have the moves, there's no reason why you can win every time, like a good dealer should.

Electric garage doors are a great convenience -- until, of course, they break. The bad news: a dozen things could be to blame. The good news: many are easy to fix yourself. Watch this video to learn how to repair your garage door opener.

Solving puzzles can be hard, especially when it comes to Rubik's Cube. Erno Rubik's puzzles are extremely difficult, three-dimensional mechanical cubes, unless you're determined and can handle a few mathematical algorithms, then they're easy, or at least not impossible.

Solving puzzles can be hard, especially when it comes to Rubik's Cube. Erno Rubik's puzzles are extremely difficult, three-dimensional mechanical cubes, unless you're determined and can handle a few mathematical algorithms, then they're easy, or at least not impossible.

So, your children have the same old boring Fisher-Price Power Wheels that all the other kids on the block have. Do you really want your child to be like all of the rest? No, I didn't think so. Turn those miniature Power Wheels, Dumar or Peg Perego vehicles into a little bit of realism, if you can handle it. All it takes is a little modification and you'll be wishing you were five again. With a few simple hacks, your son and daughter will be burning rubber, jumping curbs and burying those othe...

Sometime we can't ride our bike everywhere and we need need to take public transportation. This instructional how-to video shows you how load your bicycle onto a bus rack. Follow along and learn the proper way to ride the public transportation with your bike.

This is a short tutorial on safety on how to start skating hybrid with your dog. Heelys are great because they let you keep control of your dog. You can brake and handle your dog much better than on other skates. Find a smooth, clean street or parking lot, and make sure your dog is just as protected as you are. Learn how to pull a dog on skates by watching this video pet trick tutorial.

A bunny hop is the foundation for many BMX bike tricks and it involves getting both wheels of the bike off the ground. Learn how to bunny hop from our BMX biking expert in this extreme sports video tutorial. Take action: pull up on the handle bars, pull back end up with the pedals, and practice. Patrick, the instructor in this how-to video from Live Strong, resides in Campell, CA and has been riding for several years. His sponsors include Mongoose Bikes, Fox, Monster, and Calabasas Cyclery.

Flatland is a freestyle BMX bike riding style on smooth, flat surfaces without any ramps or jumps. Learn how to flatland from our BMX biking expert in this extreme sports video tutorial. Take action: feather the brakes, shift your weight, and practice, but remember not to pull up too hard on the handle bars. Patrick, the instructor in this how-to video from Live Strong, resides in Campell, CA and has been riding for several years. His sponsors include Mongoose Bikes, Fox, Monster, and Calabas...

Young children have growing bodies and need healthy snacks for supplying nutrients and energy, especially preschoolers. Their little stomachs just can't handle it. Therefore, it's very important to incorporate some snacks into their daily routine. Try these tips for buying snacks for preschoolers in this nutrition how-to video.

Core Data is a powerful data-management framework introduced with Mac OS X v10.4 Tiger. When you take advantage of Core Data, it slashes the amount of custom code you need to write in order to manage application data. Opening, saving and undo management can all be handled by Core Data, freeing you to concentrate on creating unique features for your application. This video tutorial, which presents a general introduction to using Core Data, will walk you through the process of building a simple...

This tutorial video sequence will show you how to solve the V-Cube 6 and V-Cube 7 Rubik's Cube style puzzles. These V-Cubes are difficult to solve, but like most puzzles, become easier to handle with practice. Good luck, V-cubers!

In this video tutorial, Chris Pels will show how information can be passed from one page to another using a query string. First, see how to construct a query string including variable names and values from information on a data entry form. Next, see how to access the query string information when the page is posted including how multiple query string variables are handled. As part of the server side processing of query string information, see how to implement validation for existence of query...

Ever wanted to become a programmer? This Delphi Training Series: Programming 101 is a sequence of training videos designed to teach the complete beginner how to become a programmer using Delphi.

If you're looking to improve your browsing experience, then a VPN is the right way to go. If you're tired of censored or geographically blocked sites and wary of companies selling your data, then a good VPN can be your answer to a problem that limits every aspect of your experience online.

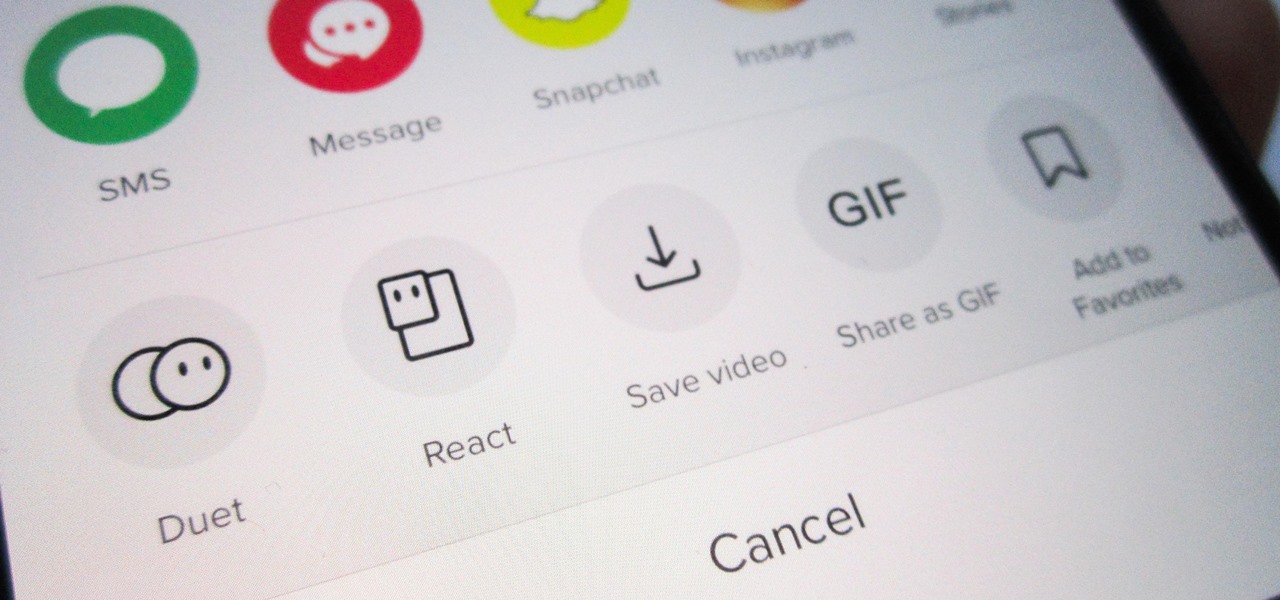
Many of us install TikTok just to see what it's like, but most of us stay for good. Inevitably, that involves creating an account. The problem is, TikTok assigns you a username, usually based on your email address — an odd choice for a platform made for self-promotion. If you're not happy with your random TikTok handle, you can change it.

While the story of augmented reality headset maker Osterhout Design Group has come to an end, the epilogue of its demise continues.

Unless you want to make your TikTok account totally private, anyone that uses the app — with or without an account — can view your profile and all the videos of you performing new dance moves, singing along to popular songs, and recreating your favorite TV show scenes. Even worse — they can download those videos.

Web application vulnerabilities are one of the most crucial points of consideration in any penetration test or security evaluation. While some security areas require a home network or computer for testing, creating a test website to learn web app security requires a slightly different approach. For a safe environment to learn about web app hacking, the OWASP Juice Shop can help.

One of the leading chipmakers for smartphones is getting ready to announce a new processor made specifically for augmented and virtual reality headsets.

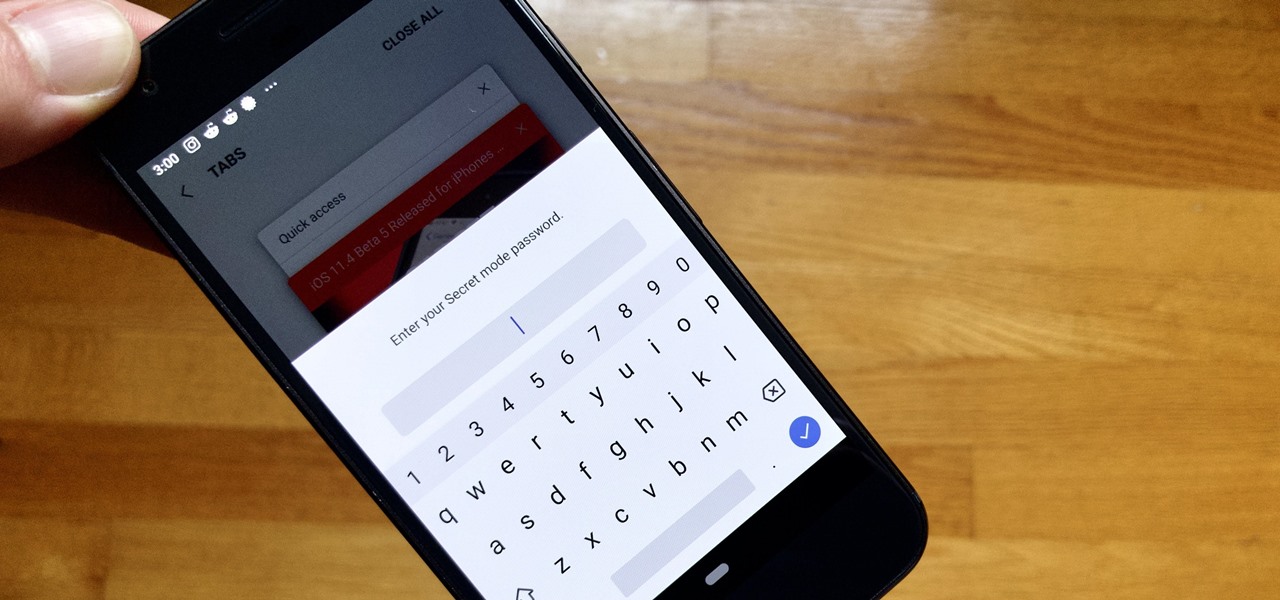
Whichever web browser you use, each comes with a way to surf the net "secretly." While nothing on the internet is truly anonymous, private browsing modes can help keep your movements hidden from those who might have access to your data. The "secret mode" for the Samsung Internet app goes a step further on Android, by locking your private browsing behind a unique password.

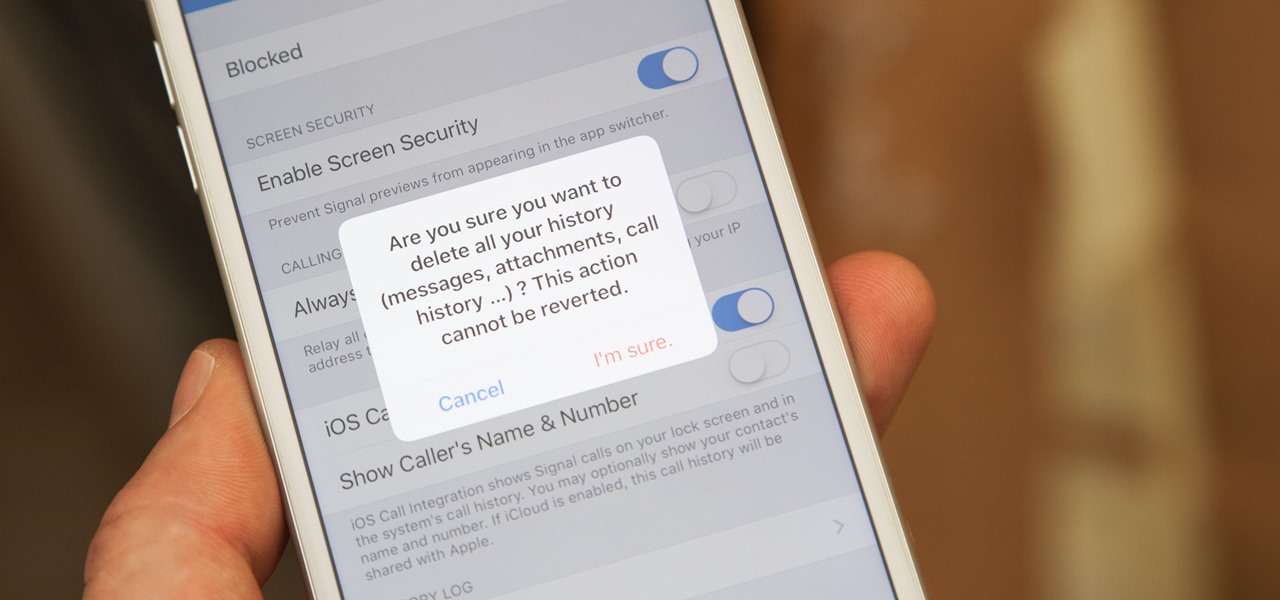
If thieves, hackers, law enforcement, or other would-be enemies should ever gain entry to your smartphone, they could also access conversations you've had in Signal Private Messenger. To better secure your encrypted communications, you can password-protect the whole app and its contents — but only on Android. Even then, it's necessary to perform data deletion on a periodic basis, if not immediately.

A spokesperson from the Nissan and Renault Alliance told Driverless the group is testing self-driving electric "robo-vehicles" for future mobility services and is "not ruling out anything" for future services the group might offer, as the alliance widens its driverless business model to include both fleets and private sales.

With the FBI getting access to iPhones, and apps like Waze being used to track people's locations, you've got to wonder just how safe and secure your smartphone is... or isn't. When you consider everything you do on your phone, from taking and sharing pictures to mobile banking, keeping your information safe is a crucial step that may seem out of your hands.

Microsoft is working hard to make Bing a good alternative to Google for more than just looking up images of the "human anatomy" that Google and a lot of other search engines filter out of their results.

Let’s be honest: you’ve thrown a few delicate, "hand wash only" clothes into the wash with your jeans. Maybe you’ve even ruined a sweater or two. There are so many things to look out for when doing laundry, and they’re easily ignored or forgotten, especially when it comes to drying.

As you may have already heard, the worst bug in OpenSSL history went public yesterday, dubbed Heartbleed. While we can go deeper into the technical details of it later, the short version is that OpenSSL, the library used to encrypt much of the web running on Linux and Apache has been vulnerable for up to two years.

Let's be honest for a second; we all have sensitive material on our phones that we wouldn't want anyone else to ever see. Maybe it's to protect ourselves or someone else, or maybe it's none of your business why I don't want you to see pictures of my bachelor party. Regardless, sometimes we need to keep things hidden and safe.

We all know about PRISM. The Surveillance Program allowing the U.S Government to access private user information. Such as, Google Searches, Tweets, Facebook Posts, Private Images, and other private user data. "Hiding" yourself can be very difficult, but it is possible. I'm here to show you How to Become Anonymous & Browse the Internet Safely.

To get the "Hail Mary" achievement on Read Dead Redemption, it's going to be quite a challenge. This is almost impossible to do while standing on flat ground, but it is possible.

This achievement can be earned on the Outlaw to the End downloadable cooperative mission in Read Dead Redemption. To get the Dodge This achievement, start a private match with a friend on the Herd mission. Once the mission starts, select the bolt action rifle and the rolling black rifle. Use the bolt action as your primary weapon, and shoot the TNT crate next to the tent on the righthand side. Quickly switch over to your rolling black rifle. Have your teammate use one of the repeaters to weak...

Google is the biggest and best search engine on Earth, and if you are a webmaster and want your website to be a big success it would really behoove you to know as much about how it works as possible. The Google Webmasters series of videos and website were created to teach webmasters, SEO professionals, and others how Google works by answering their questions and giving them insights into how they can best integrate and utilize Google's functionality to improve their business. This video will ...

In this video tutorial, viewers learn how to use Flickr photos in their screen-saver. This task can only be done on the Windows computer. Users will need to download the program from the website provided in the video. Once downloaded and installed, there is an option in the Screen Saver Settings. Users are able to take photos from specific users or groups, or can search through tags and contacts. Further options include selecting the size of the photo and delay between switching the photos. U...

In this clip, learn how to add your own personal files to your Barnes and Noble Nook and make it a portable carrying device. This tutorial will show you all the steps you need to get anything from photos, videos, music files and personal documents onto your e-reader. This process is pretty easy and once you view the clip, you should be all set to start side loading. Who needs an iPad when you have a Nook?

In this video, presented by the experts at the St. Louis Community Credit Union, learn how to prevent thieves from stealing your identity or account information. These days, between paper bills, Internet banking, social networking and all the other ways we interact, there are many ways for crooks to get into our private lives.

When conducting mobile convert surveillance, you will be following someone and it is important to dress appropriately for the environment and carry your surveillance equipment in a bag that will fit into the scene.

When you need to gather information without anyone knowing you will need to utilize covert audio surveillance. There are a variety of ways and technique to most effectively get the information you need.

Have you ever had to close an application with private info in order to let someone else use your PC? LockThis! is a windows application that lets you secure individual programs without the hassle of having to save your progress and closing the program. To use LockThis! just hold the control key and click on the application that needs to be locked and simply enter your password on the dialog that pops up and your done. Now anyone can use your pc without you having to look over their shoulder....