This video tutorial tells you how to create a free VPN with the website itshidden.com. The first step in creating your VPN on itshidden.com is to make an account on itshidden.com. Register with your own username and password. Then when you've made an account log in to it so that you can use the rest of the website. Next you go to control panel, and then network setup. Then you will have to click through the instructions in order to create a new network. Next you will have to create a new conn...
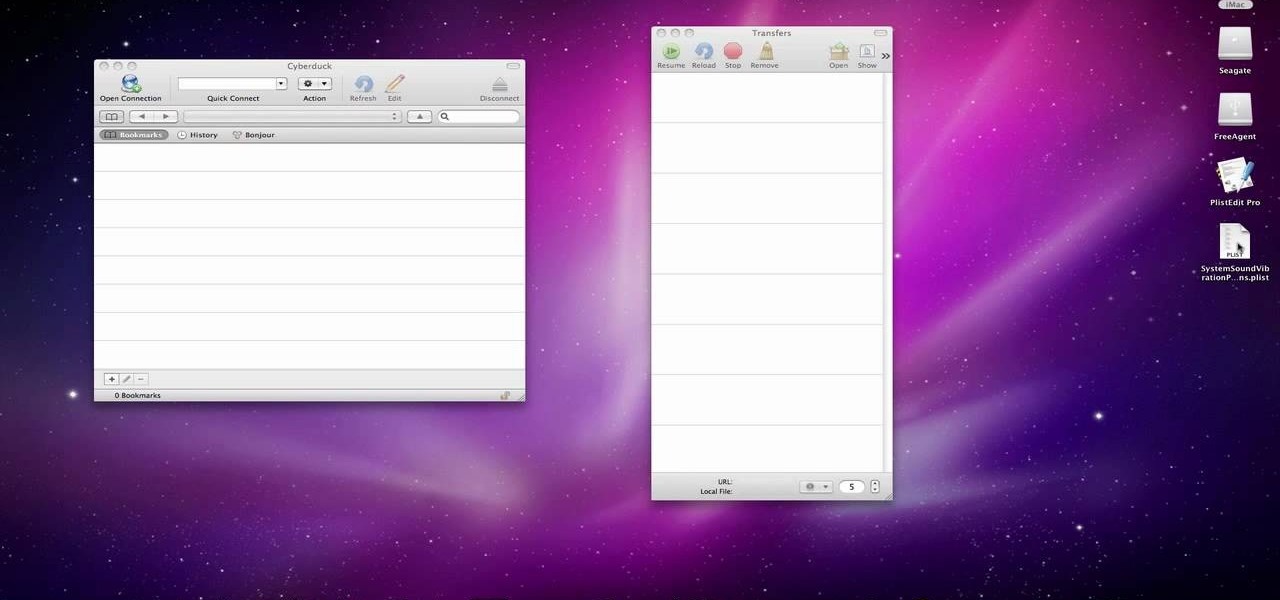
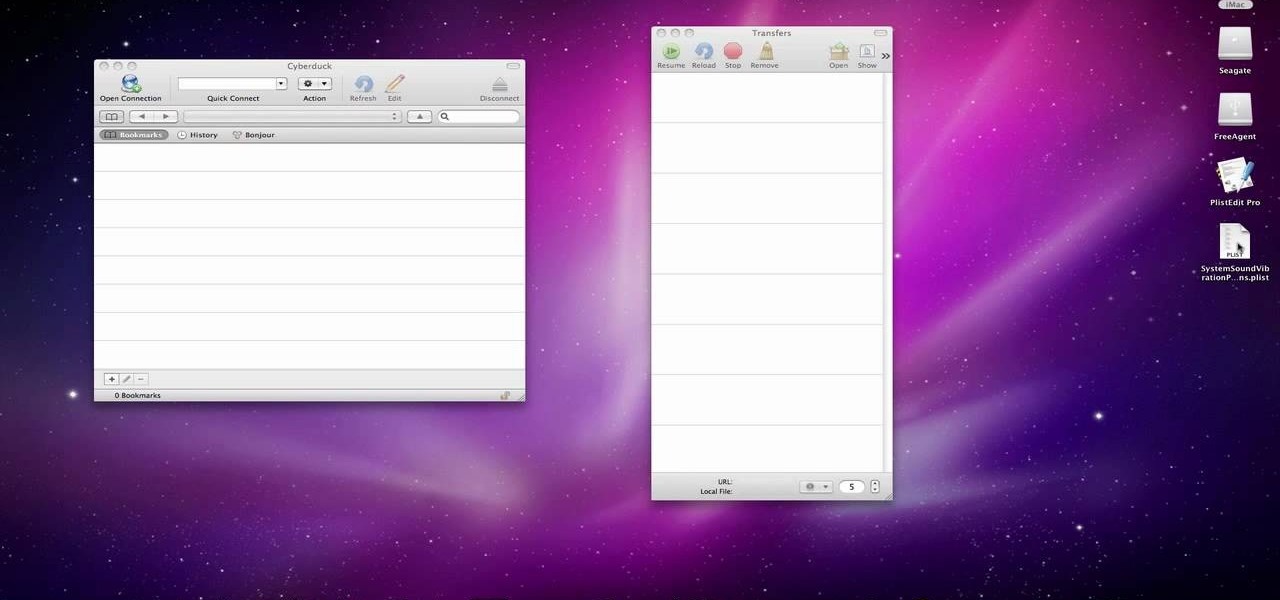
In this video we learn how to make your iPhone vibrate your notifications longer. For this you need an SSH program like cyberduck. You also need plist edit pro. Once you have SSH in your phone, go to system, library, private frameworks, celestial framework, then find vibration patterns. Double click that. Download it to the desktop. Open it. Open up the plist file. Go to default, look at total duration, click into that to change the time of the vibrate duration. Change the On Duration too. No...

This video tutorial from DrJailbreak shows how to reset your SSH password on iPhone or iPod.If you changed your password through Rock with your Mobile Terminal and forgot it, this is what you are going to do to set your root and mobile password back to alpine.First you will need iFile application. Open Cydia and browse to http://repo.beyouriPhone.com. Navigate to Be Your iPhone Repo and scroll down to iFile. Download and install.Open iFile and navigate to /Private/etc.Scroll down and open mas...

Chau-Minh, a private tutor, discusses cramming and how to do it effectively. This video does not intend to endorse cramming, but if you are probably screwed then you might as well see it. When you cram, don't expect to get a high grade because you lack time. To pull out a high grade, we need to do deletion. Deletion is just like chopping a branch to make the tree smaller. The tree would signify the lectures of your professor. Crossing out the topics that are discussed rarely by the professor ...

Jim from the "My Temp Number Helpline" teaches us to block outbound caller ID on your phone. The first way to do this is to open up the dial pad and enter *67 before the number you want to dial. This will show up on the receiving line as "Private Number" or "Unknown". To permanently block the number you go into your phone's settings. Then click on the word phone. Then click where it says "Show my caller id". If this setting is off, then your number is blocked on all outbound calls. This is us...

In this video tutorial, viewers learn how to save money on beauty products. In-store cards and frequent buyer programs can save a lot of money. When you scan the CVS Extra Care card at checkout or in-store kiosk, coupons based on your purchase will be printed automatically. It will give good discounts. Web only offers are becoming popular. Private sale sites have also become popular. You simply sign up on the site and take offers that the site has. This video will benefit those viewers who ar...

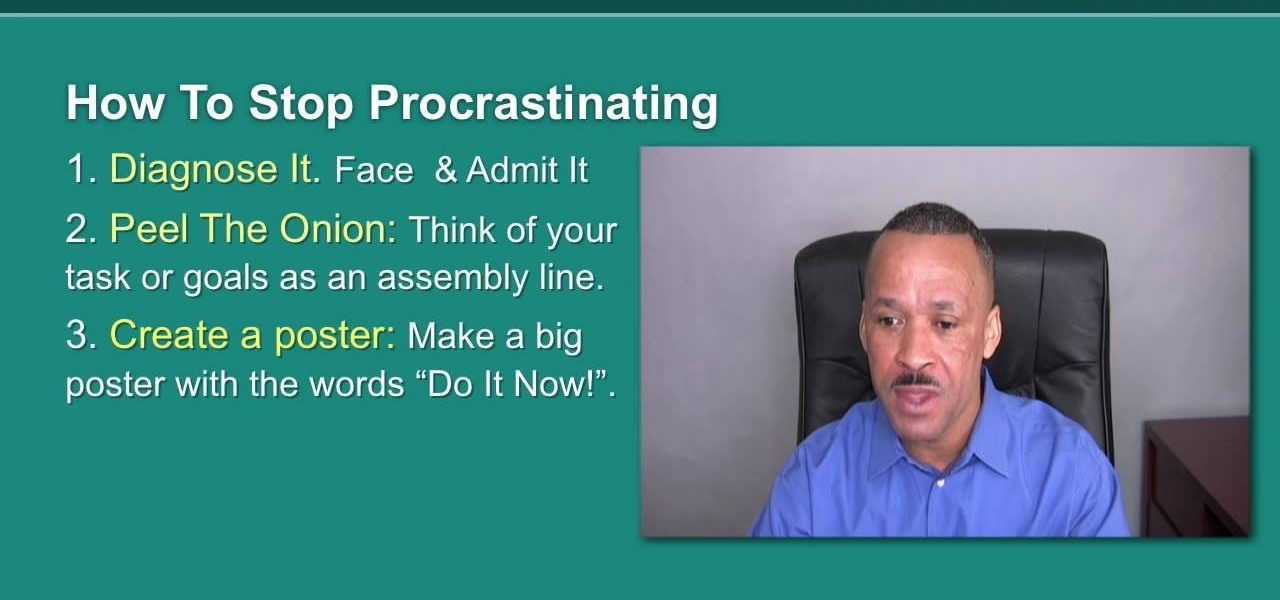
glemo teaches you how to stop procrastination. This is like termites eating at the foundation of a house. It eats you up inside and you need to learn self control and discipline. You have to discipline yourself to do the things you do now, or you will feel regret later. First off, you need to diagnose your problem and admit it. Think of your life or your activity as an onion. There are different layers and different components. You need to break your task into smaller ones. You have to trick ...

Steps to clear the cache on Firefox and delete unnecessary temporary files from your computer. In your Firefox browser go to TOOLS. Click on OPTIONS. Then go to PRIVACY tab. Click on PRIVATE DATA section and click on SETTINGS. Now you can clear the following items: browsing history, download history, saved form information, cache, cookies, saved passwords, authenticated sessions. Check what you'd like to remove, specially the cache option. Mow click on OK button. click on CLEAR NOW and click ...

In this video the instructor gives tips on how to erase a PC hard drive. An MIT study shows that 74 percent of the discarded hard drives contain private data on them that can be read and recovered by others. So you should learn how to completely erase all the data so that no one can recover or read from it later. Now formatting the drive or deleting a few files wont do it. For this you will need to have a proper software that meets or exceeds that US Department of Defense standards for data r...

Syncing Twitter with Facebook is what we learn to do today. Go to your left hand corner and click applications. Go to browse more application and type in Twitter sync. It will pull up the application. Click on that. Go to tweet sync on Facebook and then become a fan. Then you will go to application. There are some nice options so you're not swamped with tweets. Now click on if you have a private Twitter account and enter your Twitter id. Now whatever you tweet or Twitter will automatically be...

To upload pictures to your Facebook account, this video instructs, you'll want to start by knowing where the exact picture or pictures you're wanting to upload are located on your computer. Then, from your main Facebook account page, click on "photos". From here, you decide how private to make the photo. Then, remembering the location of the photo you wish to upload, you must go there and click on it. That done, you can choose a caption for the photo, and click confirm. The biggest social sit...

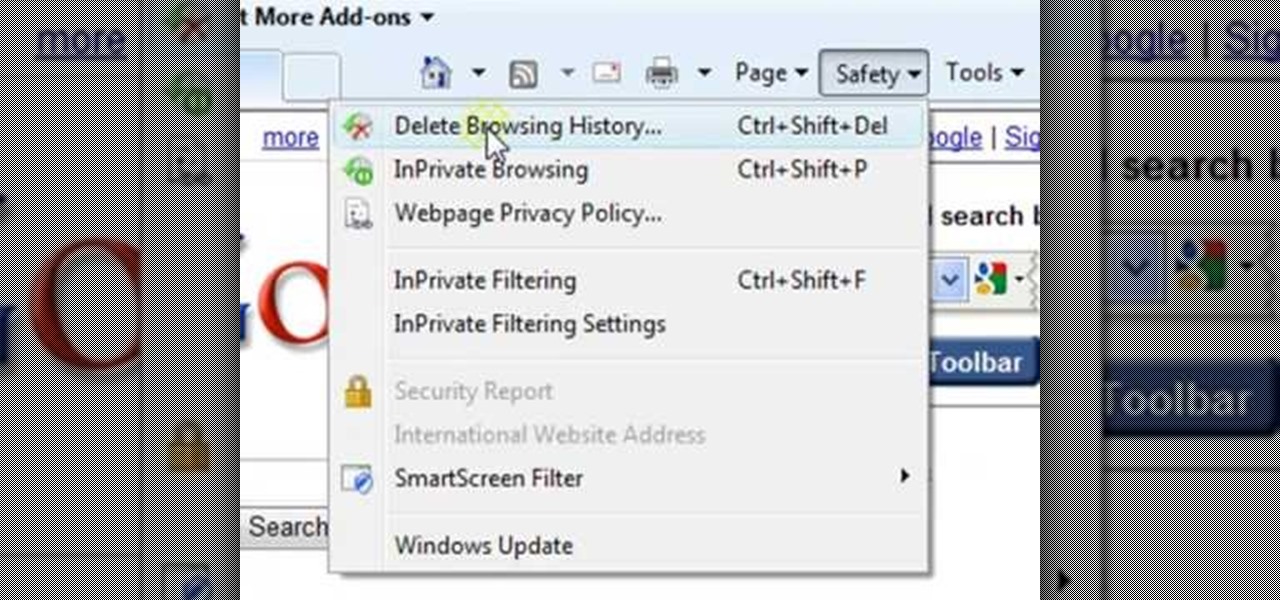
ClearTechInfo presents a how-to video on clearing Internet Explorer 8's browser history. Computer users are reminded that the only silly question is the question not asked. In the video, the viewer is shown that by clicking the button marked "Safety" in Internet Explorer 8 the "delete browser history" option is revealed. As long as each option is clicked, the history for the computer user is deleted. The browser history, cookies, cache, and passwords can all be deleted with the click of the b...

In this video the instructor shows how to remove vocals in a audio using the Adobe Audition 3 software. He says that one cannot remove vocals 100 percent but just reduce them to a minimum compared to the rest of the sound. He shows you a sample track first which contains vocals.

In this video, Dr.Travis Fox explains how you can tell if your partner is cheating through eye cues. Many people will search and hire even private investigators to find out the truth. Dr. Fox in this video says to "save your money." He tells you about certain indicators that are used to read if they are lying. For example, looking to the left or looking down might indicate that they are lying to you. He does say that it is not 100% always correct but works well in a lot of cases.

In this tutorial by Shooting Eggs, you'll learn how to create your own "ocean in a bottle". The supplies are very simple and cheap, probably stuff you've already got around the house. But the finished effect is pretty impressive.

Learn how to do a Gravitron triceps dips drop set. Presented by Real Jock Gay Fitness Health & Life.

Learn how to do chest focused Gravitron dips. Presented by Real Jock Gay Fitness Health & Life. Benefits

Learn how to do cable Russian twist. Presented by Real Jock Gay Fitness Health & Life. Starting Position

Learn how to do tube assisted dumbbell curls. Presented by Real Jock Gay Fitness Health & Life. Benefits

In this AeroCast episode, Anthony Bottini discusses the Power Off Stall maneuver as performed in the Piper Warrior (PA-28-161), referencing the procedures and standards outlined in the UND Aerospace Warrior Standardization Manual. All performance tolerances are based on the performance standards set forth by the FAA Private Pilot Practical Test Standards. Power Off Stall practice is vital in increasing a pilot’s proficiency in regards to stall recognition and stall recovery techniques during ...

The ability to browse the web in coffee shops, libraries, airports, and practically anywhere else you can imagine is more than convenient, but convenience has risks. Using public Wi-Fi allows others to spy on you easily. Even your own internet service provider can see every website you've ever visited. Don't fall into the trap of protecting your identity, data, and devices after it's too late.

Smartphones have so much sensitive information attached to them. If you share your home with others, then you know the pains of trying to keep anything private. Photos are surely among the things you'd prefer to keep to yourself, so OnePlus has you covered.

After drawing attention from nostalgic Gen Xers for its Motorola Razr reboot with a foldable screen, Lenovo has a new augmented reality smartglasses concept that the company hopes will also turn some heads.

Commenting on Facebook pictures is a commonality. But you may not want to share your private and personal pictures on Facebook. Maybe you just want a select few to comment on your photos. Fear no more, you can send your pics and get private comments using Google Photos.

Thanks to its encrypted messaging, WhatsApp can be a platform for secure communication with friends and family. One drawback, however, is that the app would let anyone add you to a group chat, regardless of if you approved it or not. This lack of control over your own account is over, as WhatsApp now lets you decide who can add you to a group chat.

As penetration testers, we sometimes need to securely store customer data for prolonged periods. Bruteforce-resistant, vault-like containers can be created with just a few commands to protect ourselves from physical attacks and unintended data disclosures.

Two characters from the popular sci-fi animated comedy Rick and Morty have already made their way into augmented reality courtesy of ARKit experiments. Now, it's possible to become one of them on the iPhone X.

If you've received a spam message in Signal Private Messenger, you know that anyone can contact you as long as they have your linked phone number. But when it comes to the people you're actually trying to have a private conversation with, how do you know it's really them?

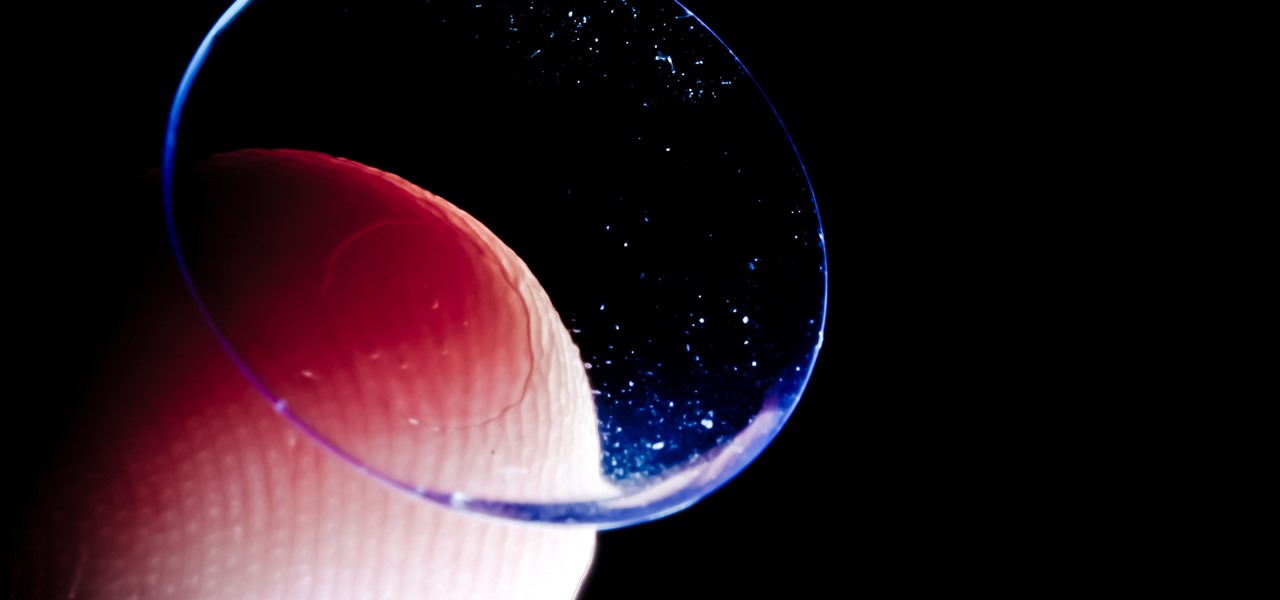
Acanthamoeba keratitis (AK), a rare eye infection caused by the Acanthamoeba ameba found in tap water, affects a few dozen people in the US every year. In some cases, it can have devastating effects, like what Irenie Ekkeshis has experienced; She was blinded by AK in her right eye due to a contaminated contact lens.

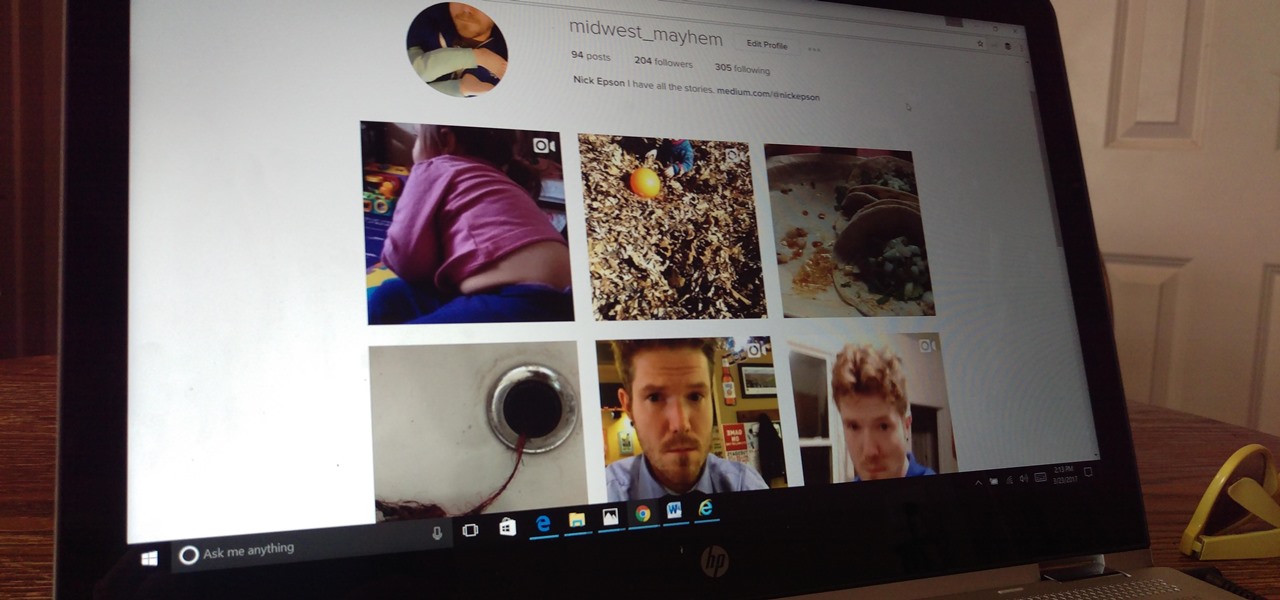
The photo-centric Instagram app is a great way to share "evergreen" pictures and videos when compared to Snapchat and Facebook's new Messenger Day feature. But like all social media, keeping the account secure is an essential aspect, as it restricts unwanted viewers from seeing your content and can prevent unauthorized users from accessing your account. Instagram has several methods for locking down the account including a new two-factor authentication (2FA) mechanism.

Samsung is rolling out the Android 6.0 Marshmallow update for Galaxy S6 and S6 edge today, February 15th, and with it come some good improvements to how S6 edge users can utilize the handset's curved screen.

This tutorial is for those who've purchased an account with Private Internet Access to hide your VPN and would like to set it up in Kali. Please note, you can chose to run your PIA service from your Windows computer without configuring it in linux as long as you'll be using a NAT connection. Using a NAT connection will allow your Windows machine and Kali Virtual Machine to use the same IP address, hence if your IP is hidden on one, it will be hidden on the other.

Welcome back, my rookie hackers! "How can I travel and communicate over the Internet without being tracked or spied on by anyone?" It's a question many Null Byteans have asked me, so I have decided to write a comprehensive article addressing this issue.

When you have a parent who cooks—and has you act as sous chef—the kitchen automatically becomes a less intimidating place. In other words, kids who know their way around the kitchen will most likely become adults who cook for themselves, which also means that they'll eat more unprocessed whole foods, save money, and maintain a healthy weight.

This is a simple design built from reclaimed wood and purchased ¼” wood slats. It cost very little and only took a couple of hours to complete the build. The goal was light weight, shallow and wide for collecting leafy vegetables, easy to handle and somewhat attractive.

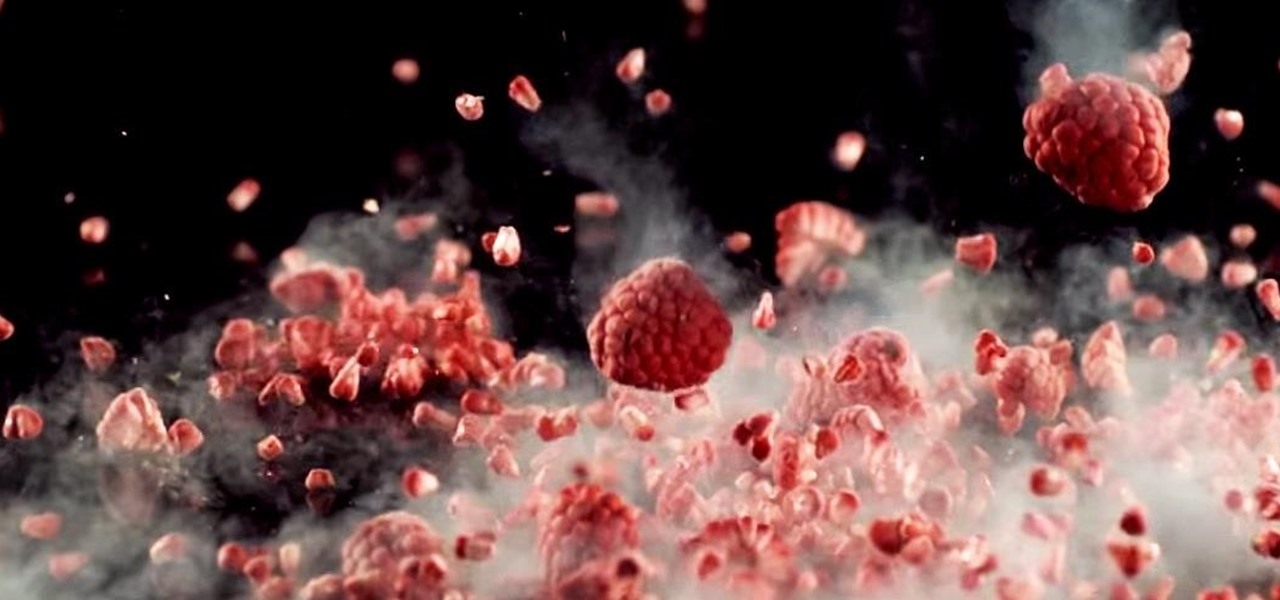
"Cooking" with liquid nitrogen seems like one of those activities that should be strictly limited to pros who are appearing on Top Chef, but it's the only way you'd ever be able to make Dippin' Dots at home. If that isn't enough of a reason for you to get some LN2 for your kitchen, check out this dose of pretty:

One of Android's strengths when compared to other mobile operating systems is its ability to set third-party apps as the default handler of certain file types. Instead of being stuck with pre-installed system apps when it comes to opening files and links, you're free to choose a better-fitting alternative.

This is how I upgraded my 2002 Monte Carlo End Link and Sway Bar Bushing to Polyurethane ones from MOOG. My factory hollow sway bar broke and it was replaced with a 33mm solid one from Dorman.

In this "Quick Clip," I tried dunking inflated balloons into a container filled with liquid nitrogen until they were completely flattened and seemingly destroyed. Once out of the liquid nitrogen, the balloons come back to life and reinflate on their own—without even touching them!

This science experiment deals with sublimation of dry ice into carbon dioxide (CO2) gas. In the video, I'll demonstrate how pushing a quarter into a block of dry ice makes the quarter scream and shake vigorously.