You may not have heard of visceral leishmaniasis, onchocerciasis, or lymphatic filariasis, and there is a reason for that. These diseases, part of a group of infections called neglected tropical diseases (NTDs), impact more than a billion people on the planet in countries other than ours. Despite the consolation that these often grotesque illnesses are "out of sight, out of mind," some of these infections are quietly taking their toll in some southern communities of the US.

Android has several features built into the platform that improve user experience but require extra attention to prevent a security breach. By modifying these settings, you can drastically reduce the possibility of someone exploiting your device or intercepting information.

Beginners luck is a phrase I have always hated. But really, beginners luck comes down to not letting your experience in something get in the way of the idea.
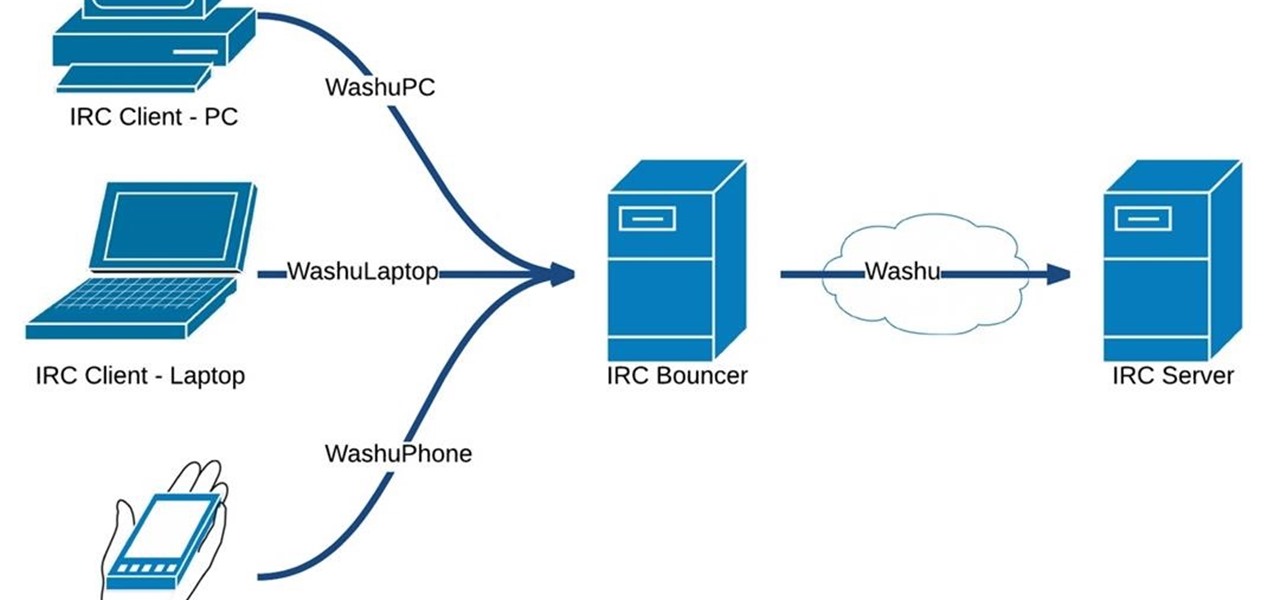
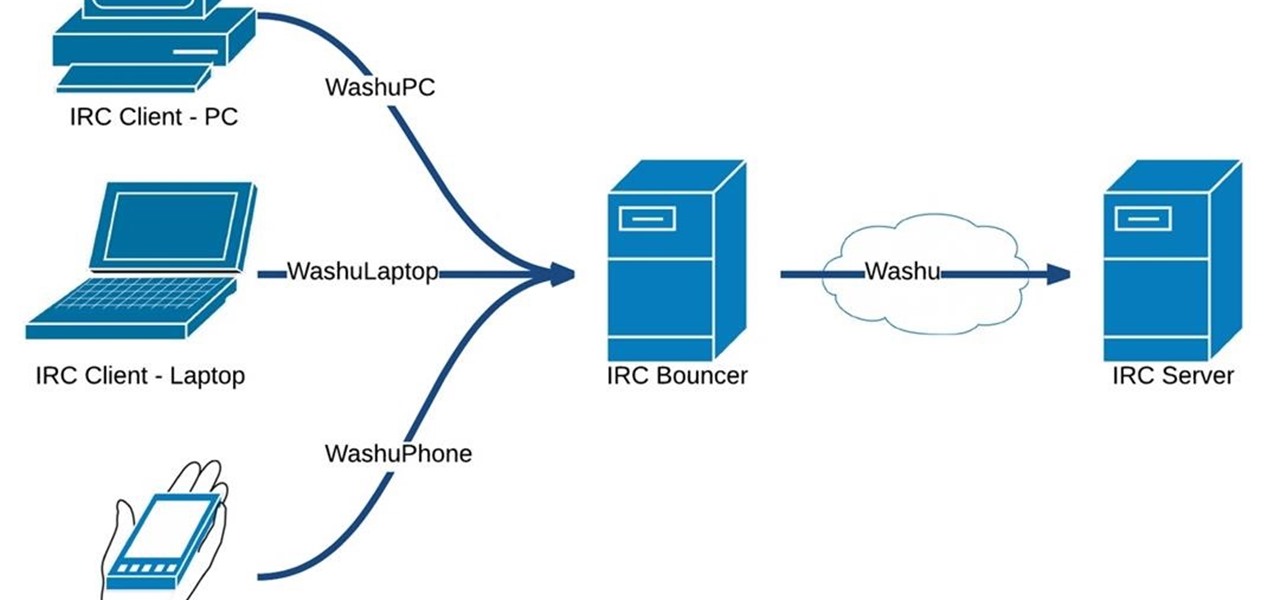
Hello fellow Nullbytiens, today we will be talking about IRC again (if you haven't read OTW's post about head over there now)and more specifically about using 1 nickname with multiple devices or IRC clients.

Many of our members here at Null Byte are aspiring hackers looking to gain skills and credentials to enter the most-valued profession of the 21st century. Hackers are being hired by IT security firms, antivirus developers, national military and espionage organizations, private detectives, and many other organizations.

UPDATE: This post is outdated, the latest version with the correct links and updated instructions can be found at my blog, here - https://techkernel.org/2015/12/19/embed-metasploit-payload-in-apk-manually/

My bathroom is like my own private arcade room. Whenever I'm seated comfortably on the toilet, no one is going to disturb me, so I can play anything I want on my smartphone. You probably do it, too — and your parents, kids, friends, colleagues, and boss — so don't be afraid to admit it.

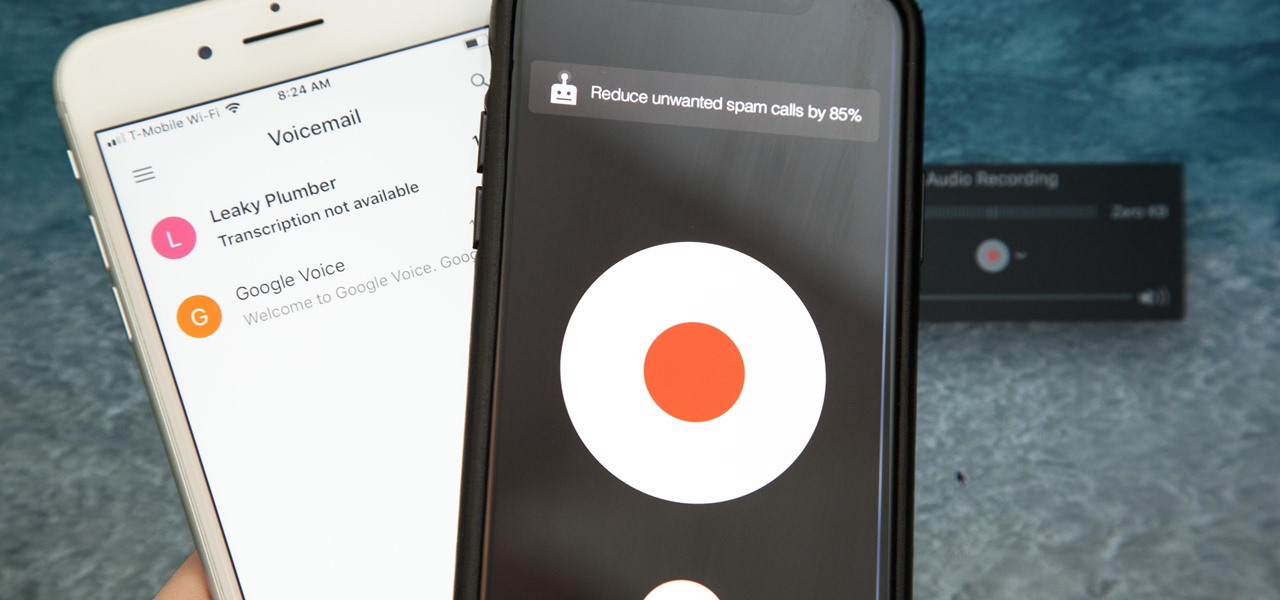
Unruly customers. Crazy exes. Horrible bosses. When you need proof of insanity or just want it for your records, recording a phone call is a must. Problem is, it's not the easiest thing to do on an iPhone — but it's completely possible.

Welcome back, my rookie hackers! As hackers, we are often faced with the hurdle of cryptography and encryption. In some cases, we use it to hide our actions and messages. Many applications and protocols use encryption to maintain confidentiality and integrity of data. To be able to crack passwords and encrypted protocols such as SSL and wireless, you need to at least be familiar with the concepts and terminology of cryptography and encryption.

Welcome back, my greenhorn hackers, and happy New Year! Now that your heads have recovered from your New Year's Eve regaling, I'd like to grab your attention for just a moment to preview 2015 here at Null Byte. I hope you will add your comments as to what you would like to see, and I'll try to honor as many requests as I can.

In recent years, Hollywood has taken a shine to hackers, with hackers appearing in almost every heist or mystery movie now. This can be both good and bad for our profession. As we know, whichever way Hollywood decides to depict our profession is how most people will perceive it.

Many of my aspiring hackers have written to me asking the same thing. "What skills do I need to be a good hacker?"

One of the biggest problems in data security is authentication of data and its source. How can Alice be certain that the executable in her inbox is from the venerable Bob, and not from the not-so-venerable Oscar? Clearly Alice wants to know because if this file is actually sent to her by Oscar, the file might not be a game, but a trojan that can do anything on her computer such as sift through her email and passwords, upload her honeymoon pictures, or even turn on microphones and webcams. Thi...

Are you interested in beginning research of your family's history? I began this journey about 3 or 4 years ago and here is what I found. I've done almost ALL of my research online, and gotten farther, faster and more comprehensively than anyone else who has researched my family the old fashioned ways. This is the kind of thing that technology is made for. Here's how to use it.

Use this safe and easy technique next time you need to replace a shattered light bulb. You Will Need

As the iOS 18 beta continues, Apple's still investing time into fixing up iOS 17. Compared to iOS 17.4 and iOS 17.5, which both had over 30 new features and changes, iOS 17.6 is a relatively small software update for iPhone. But there are still some important things to know about.

Apple just upped its sticker game on iPhone and iPad. We've already had stickers available for Memoji, Fitness activities, and third-party iMessage apps, but only some could be used outside the Messages app. Now we can use stickers practically anywhere from the new stickers drawer, with fun emoji stickers to boot. Even better, we can stickerize the subjects of our own photos and videos, including animations.

Apple's iOS 16.3 update for iPhone had impressive new features, but iOS 16.4 might impress you even more.

With the holidays right around the corner, it's easy to miss a big software update on your iPhone, and by that, I mean iOS 15.2, which was pushed out Monday, Dec. 13. There's a surprising amount of new features and changes in the updated firmware, and there are a few big ones you need to know about.

Amid a troubling resurgence in coronavirus cases, led by the new Delta variant, augmented reality is once again moving back into the spotlight as a solution, especially now that the move to return to offices has been stalled.

Numerous potential exploits are found for every operating system each month, and Android is no exception. Trouble is, lots of Android devices don't receive timely updates — but many are now getting regular monthly security patches to at least shore up these vulnerabilities.

Apple's Find My app just got way more useful. While it's great for locating a lost or stolen iPad, iPhone, iPod Touch, Apple Watch, Mac, and AirPods, as well as anything attached to an AirTag tracker, it's even better now that it works with third-party accessories and gear.

The race for the future of AR wearables gained steam this week with several pivotal developments. First, Apple, the subject of numerous reports and rumors regarding its purported AR headset, is reportedly eyeing an in-person unveiling of the device for later this year, rather than introduce it at its upcoming virtual Worldwide Developers Conference, which would usually be as good a time as any to make a big AR hardware announcement.

Progressive Web Apps hope to one day bridge the gap between websites and apps by giving the former more access to your phone's features, but they're not very common yet. In the meantime, you can take matters into your own hands with an app that uses your system WebView to render websites in a full-screen, borderless window with a few extra features — a lot like a native Android app.

TikTok is a video-platform first, and while visual content is critical to its popularity, what has carried many of these videos to millions upon millions of views isn't only what you see but what you hear.

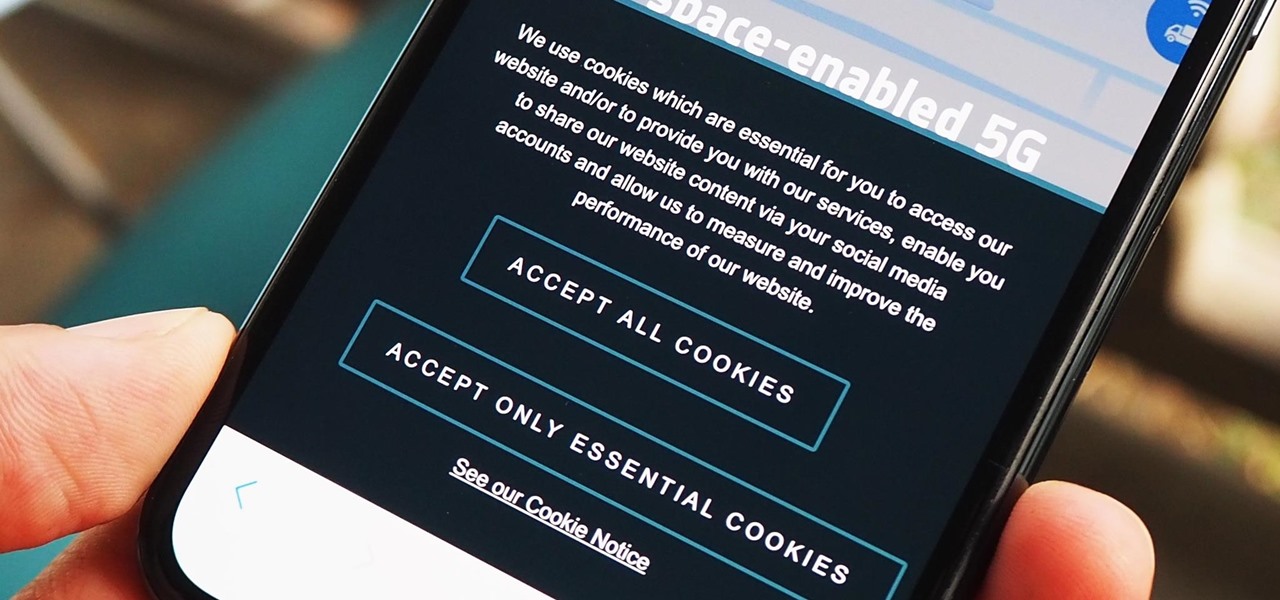
As a means to combat annoying and intrusive advertisements in Safari, Apple added native support for content blockers on the iPhone. Instead of being bombarded by notifications, banners, and pop-ups, content blockers prevent them from opening, which can also be said about those annoying cookie consent notices that many websites now have.

The first Android update of the year is here. On Monday, Jan. 4, 2021, Google started pushing out the January security patch for the Pixel 3 and all newer Pixels, after having ended support for the Pixel 2 last month.

Okay, so you rooted your Android phone .... now what? There are a few ducks you need to get into a row, like backing up your stock boot image, getting SafetyNet sorted, and improving security with biometrics. But there are also awesome root mods waiting for you — just don't get ahead of yourself.

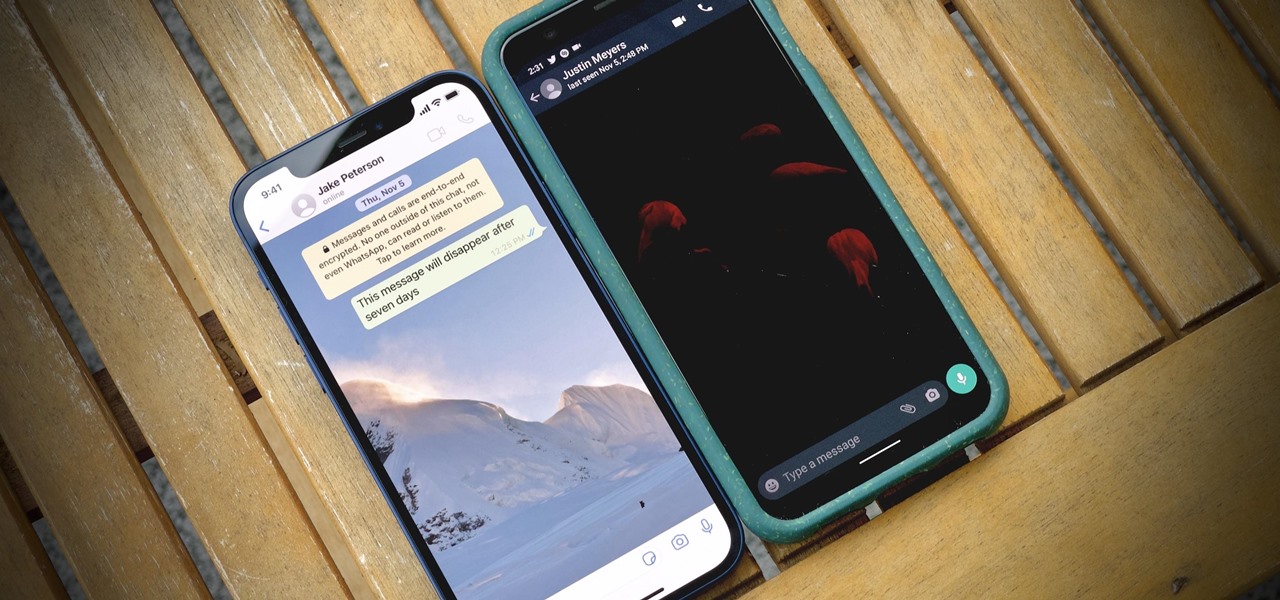
If you're like me, you enjoy using your phone's dark theme at night and light theme during the day. When switching from dark to light and vice versa, many of the UI elements in supported apps adjust accordingly, but you have no control over what does and doesn't change. WhatsApp, on the other hand, does give you some granular control by letting you pick a chat wallpaper for each theme.

For all of its many perks — from the best iPhone camera system money can buy, to arguably the best smartphone display on the market — the iPhone 12 Pro Max is undeniably huge. It has the largest iPhone screen to date despite being 0.46 cubic inches smaller than the iPhone 11 Pro Max in overall size. If you're finding it a little too much to handle with one hand, there are ways to make it much easier to use.

Whether it's an iPhone 12, 12 mini, 12 Pro, or 12 Pro Max, know that these devices are the most powerful smartphones Apple has ever made. Still, bugs happen, and you might find yourself with an app that isn't performing quite as it should. When that happens, it's best to force-close (or force-quit) the problematic app instead of waiting for it to fix itself, which may never happen.

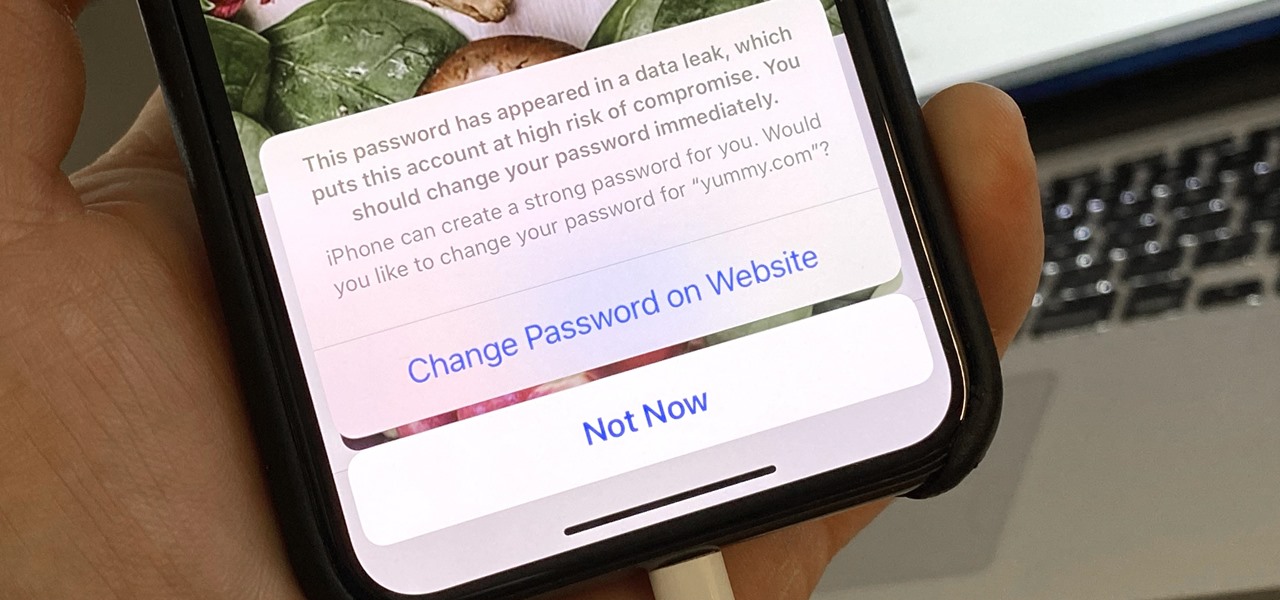
Everything lives online these days, so it's not uncommon to have hundreds of credentials for different accounts on apps and websites. That's why a password manager is a must, and your iPhone has one built right into iOS that you can start using today. In iOS 14, it's gotten even more useful since it can now monitor your passwords regularly to see if any match leaked password lists online.

VPNs add a protective layer between your data and your internet service provider (ISP) or bad actors (hackers), so it makes sense they've become so popular lately. Probably the most common one of these is NordVPN, so we explored its mobile app to find all the options worth checking out.

If Google's apps, namely Gmail, Calendar, and Meet, are at the center of your workday, then a new, frustrating change may upset your routine.

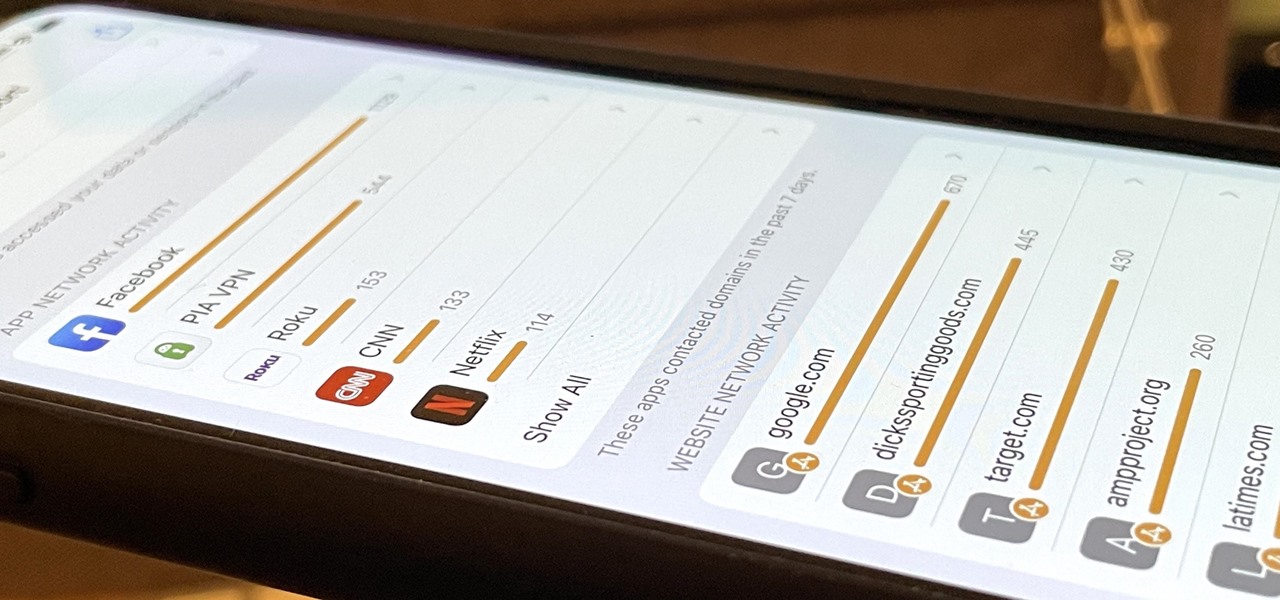
Android has not had the best reputation for privacy and security, though Google has made strides in those departments in recent years.

A modern iPhone is capable of running sophisticated, exquisitely-rendered games that rival titles on current-generation consoles. However, there is some value in classic video game titles, whether you grew up playing games on the Atari 2600, Nintendo Entertainment System, and Sega Genesis or not.

With the Wigle WiFi app running on an Android phone, a hacker can discover and map any nearby network, including those created by printers and other insecure devices. The default tools to analyze the resulting data can fall short of what a hacker needs, but by importing wardriving data into Jupyter Notebook, we can map all Wi-Fi devices we encounter and slice through the data with ease.

We might not be able to hang out with friends in-person during a mandatory lockdown or self-quarantine, but we sure can in "Animal Crossing: New Horizons." Snapping pictures with the new NookPhone feels almost as personal as taking selfies in real life, so, naturally, we want those memories to live on our real phones as well. In pure Nintendo form, however, it's not easy.

In the last decade, the number of people working remotely in the US has increased dramatically, and so has their need for technology and software to supplement that remote work. Whether you work from home or a coworking office space, the requirement for highly compatible and helpful productivity apps is a must if you want to get things done successfully.

For enterprise augmented reality platform makers, remote assistance apps represent one of the greatest opportunities to show off the power of immersive computing. These apps enable experts to guide front-line workers or customers with AR prompts and other content in the field of view of their smartphones or smartglasses.