Have you ever been in the situation where someone whose taste in books you respect and generally agree with recommends a book that you have seen from time to time and you’ve always thought it looked just “Meh” and then you finally read War Dances which is by the same author and it’s amazing and funny and sad and you think, why didn’t I read The Absolutely True Diary of a Part-Time Indian, like, three years ago? No? Is that just me?
This book surprised me. I read it for 2 reasons. 1) It seemed like one of those decently famous books that I should probably have read.

A Self-Protection Guide 1) You can help protect yourself from violent crimes.

Smartphones are crazy awesome. You can do your banking, track your children, find directions, and even pretend to have a mustache. The only thing that these personal supercomputers are missing is physical interaction with the environment.

Metal is a great material to work with. It's rigid, tough, malleable and conductive, but sometimes the part we need doesn't exist in any store. In order to create custom pieces, you need to either melt the metal and cast it in a mold, or heat it until it's soft enough to shape with your hammer. Properly melting metals can be a bit dangerous in our home shop, but we can make a coffee can forge for all of our home blacksmithing needs.

Professionally and academically speaking, I am a computer scientist, but I also enjoy lock picking as a hobby, so I thought I would share what knowledge I have with this. Before we start doing anything, first we need to understand the fundamentals of how locks work and then acquire and familiarize ourselves with basic lock-picking tools.

Today, we are going to combine what we learned from the Introduction to Cryptography article with our Java programming skills. If you are new to Java, check out Matthew's Learn Java: Part One for a quick beginner's lesson, or check out some of the Java tutorials directly on Oracle.

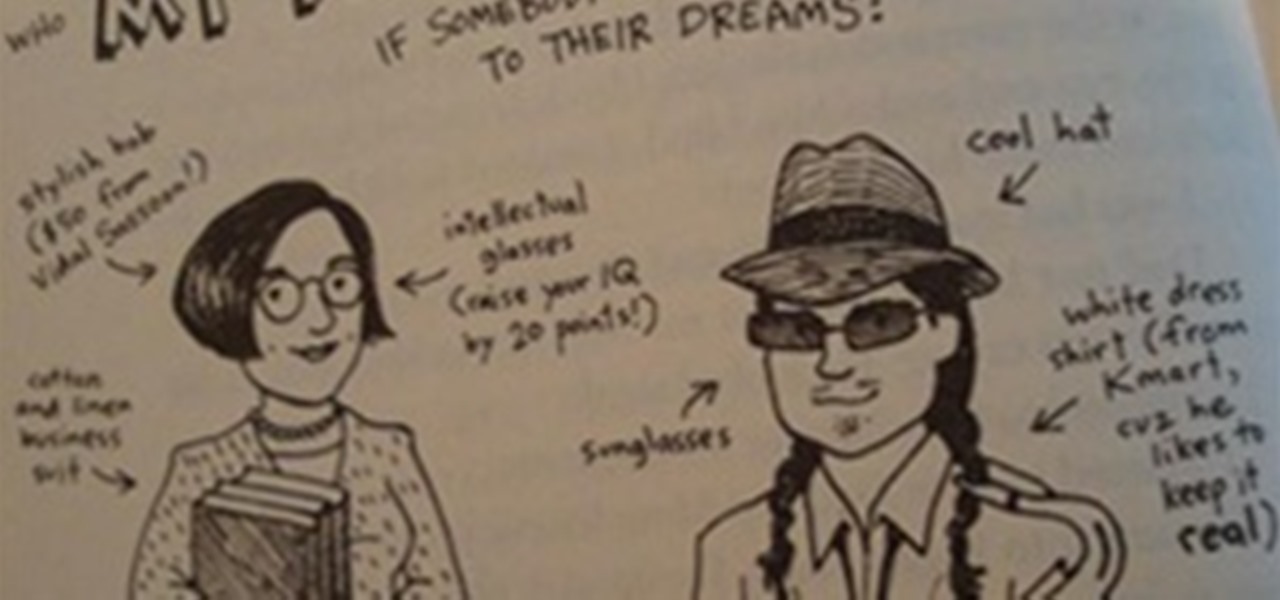
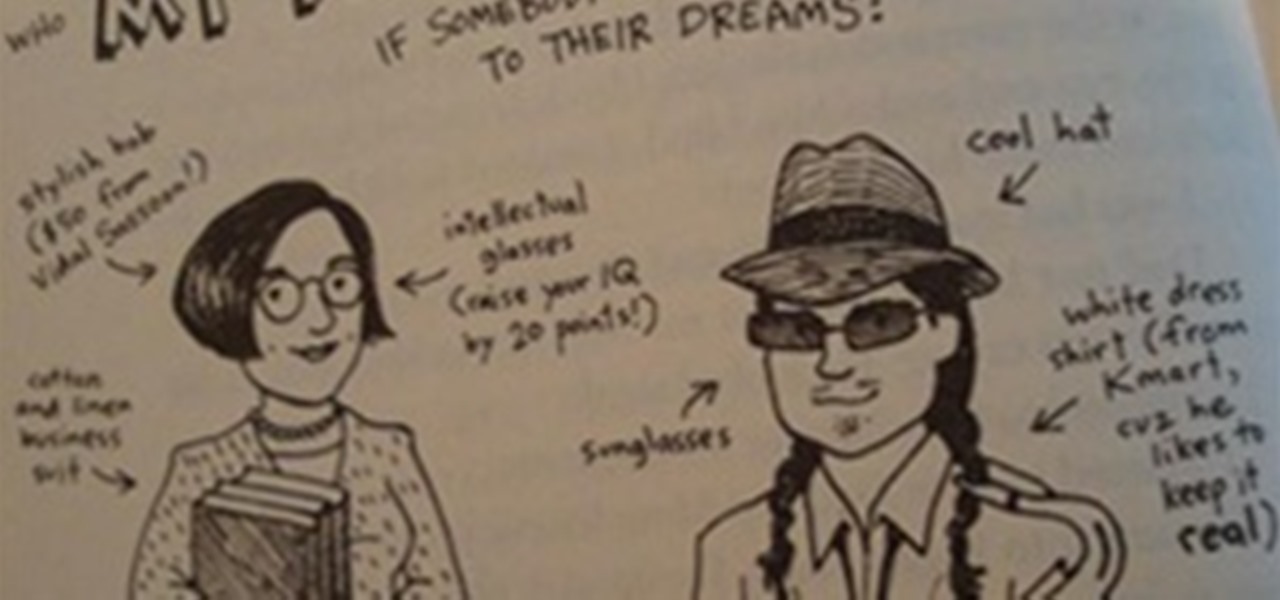
Ink & Paint was originally intended to provide a place for the sharing of graffiti and street art related news and the spreading of the street art culture. However in recent months I have noticed a distinct lack of "lowbrow" art in the WHT community. Don't get me wrong though, I'm a HUGE nerd. I love null byte, I love the Minecraft world, and all the tech posts that are becoming increasingly more common. It's awesome. However the nerd in me and the artist in me both want to see more comics, s...

The community here on Null Byte has always been great and helpful in sharing their know-how, even before I took up admin duties in this World. I jumped at the chance of leading Null Byte because I enjoy teaching and informing people on all of the important need-to-know things out there, but more so than that—there is a deeper reason.

Who doesn't love Star Wars? No one, that's who. And if you love Stars Wars, logic would follow that you like lightsabers, so central are they to the tale's mythology. It's part sword, part laser, and makes a sound like a humming motor have multigasms. If I saw one in real life, I would struggle not to lick it, even though that would mean death.

How underrated are cacti in Minecraft? Cactuses can be used for so many wonderful things, so why not have a great way to farm them? Cactus is known for its use in making "cactus green," which is a colored dye that can aid in making cyan wool, lime green wool, and green wool. Cacti can also be a great defense mechanism against mobs and other players and can help make death traps even more lethal.

Sometimes, at the end of a build, you may find yourself saying, "I'm pretty much finished, but what should I do next?" One element of a build that is always good to revisit once you're finished is the floor. It's not really a significant part of a building, but it can help make your construction look even better. Having a plain wood or cobblestone floor is fine, but depending on the style of the build, you may want to make it a little more interesting.

For our final part of recognizing crowd control, we shall look at the mind. It's the most complicated thing in the universe, but also the most easily influenced. What makes us to gullible? What methods to commercials, companies and the media use to influence our position on things? These are just a few of the questions we will answer.

This article is going to cover the basics of link building. Why do we want to build links? First of all, what is a link? A link is a hyperlink, actually. You click on it and it brings you to another webpage. I'm sure you've all clicked on links before. Well, what we want to do is we want to build links from other sites back to our own site. Why do we want to do this? Google’s problem, as I see it, and this is based on thousands of hours of research, reading articles and watching videos and li...

Brainwashing is something that happens to us every day, whether you believe it or not. It doesn't take fancy tools or space-age technology. Even if our country didn't intentionally brainwash people (believe me, they do), our country's media is brainwashing people nonstop. Just sit back and think about it for a second—about the way things work in the world and media. But before you do that, let's learn what brainwashing really is.

Sometimes, paying for the whole Xbox LIVE service might seem like a waste of money. You're constantly experiencing lag, you've got people modding and cheating, kids are being loud and obnoxious over the mic, and your kill-to-death ratio is getting dumped on. Basically, the whole multiplayer experience just isn't cutting it anymore—you want to go back to the classic world of single player. Well, there's always downloadable content—simply known as DLC.
1.) If you do not know something, keep our mouth shut.* No-one, I repeat no-one, is interested in your uneducated guesses about why something is the way it is, or why someone did something a certain way. At best, you will trick them into temporarily thinking you know what you’re talking about. At worst, you will convince them that you are speaking the truth and they will perpetuate your bullsh*t to others. Do not contribute to making the world a more foolish place just because you had to say ...

Last Friday's mission was to accomplish solving HackThisSite, realistic 1. This is the first in a series of realistic simulation missions designed to be exactly like situations you may encounter in the real world. This first mission, we are asked to help a friend manipulate the website voting system for a Battle of the Bands vote count in his favor.

In this article, I'll show you how to create a simplistic AES python based text encryptor. You'll need python 2.7 and PyCrypto (found here). The code is fairly simple, a user enters an encryption key (which basically tells the program how to scramble the text, using an algorithm), then the text to be encrypted. The program takes the key and text and inputs it into the "cryptograph" or code-based algorithm from PyCrypto. PyCrypto can use 16, 24, or 36 character encryption keys, but for the sak...

There was a huge ban wave recently on Xbox Live. In the unfortunate event that you decided to do something against Microsoft policy, and have consequently gotten yourself banned from Xbox Live, you may have come to the realization that doing whatever got you banned from Xbox Live in the first place was not worth the risk.

There’s a race on to see who'll be the Instagram of moving pictures. This makes sense, since many of our phones are clogged with video that, so far, no one is going to see. Wouldn’t it be great if there were a simple app that could take our video content, edit it for us, and then publish it to all of our networks?

Hardware hacks are something I feel we don't get enough of at Null Byte, so today I figured I would introduce a fun one. I've always been a curious hardware hacker. Taking things apart and learning how their internals work has always been a part of my nature. Quite some years ago, my father showed me a really cool trick on how to hack normal radios to scan frequencies that are normally non-listenable. This little hack allowed us to scan frequencies belonging to law enforcement, and even frequ...

Last week I had a quick look at V.I.K.T.O.R, the anthropomorphized automated editing app that lives on your iPhone, and today it’s time to put it to work.

Scrabble Bingo of the Day: * FINNESKO [n/pl.] A finnesko is a boot made of tanned reindeer skin, with the reindeer's fur on the outside. It's an especially good, warm boot for subarctic regions. These boots originate from the Sami, indigenous people from the cultural region of Sápmi, located across four countries in the Arctic Circle; Norway, Sweden, Finland, and Russia. This area is also referred to as Fennoscandia.

In my recent article, How to Make a Mini Cannon with a Lighter, I demonstrated how to make a powerful combustion cannon out of parts salvaged from a standard BBQ lighter. The mini cannon was originally made to fire airsoft pellets, but I felt it was time to revive the project with something new.

Null Byte is looking for moderators. More threats to computers exist every day. Not only do we have computer viruses and malware, but we have rootkits and other nasty pieces of code that can log your keyboard strokes or even add your computer to a botnet to attack other websites. Your computer can be infected even if you have anti-virus software installed. I can't stress enough how easy it is for a hacker to write a piece of code that gets around every piece of anti-virus software.

I can't believe it, but I've actually read about dozens of people getting their iTouch, iPhone, or iPad stuck in a bricked recovery loop and then going out to buy a new one. This is overly unnecessary. When it gets stuck in the recovery loop, some people mistake themselves by thinking that it is impossible to get the device back into DFU (Device Firmware Upgrade) mode. Getting the device back into DFU mode would at least allow us to jailbreak the device, essentially bringing it back from its ...

With those icy winter months setting in, it's time to start sipping your bourbon warm. Spike your classic eggnog, hot chocolate, and even lattes with a splash of Wild Turkey bourbon. Below, five recipes to add a little fire to your typical cold weather beverages. Adjust the recipes to get more servings, and you've got some great ideas for Christmas party favors.

Christmas just wouldn't be the same without cookies. Besides the gifts, it's the one thing that keeps the family (not to mention Santa) coming back each year. As with any family gathering, there's bound to be some chaos this holiday season, but as long as you've got a good supply of Christmas cookies, there should be peace and harmony.

After a stressful day, there's nothing more relaxing than a smooth glass of straight, room temperature whiskey to help unwind. On hot days, popping a few rocks in does the trick. And on cold days, hot toddies are truly amazing.

Cheers to another completed Community Byte project! Things went well regarding timeliness and being friendly to the other coders and students. If you've got ideas for our next mission, or an idea for a tutorial, submit them to me. Friday, our mission was to take out HackThisSite, basic mission 5. This mission focused on JavaScript, again. This time there is a little bit more security in place.
How To Write A Poem There are a million ways to start a poem. unfortunatly I wont be able to explain all of them, actually I can't explain them. Everyone has their own way of writing. If you are a beginer you will eventually find your own way. I will show you some ways that could help you write your own poem.

Welcome to Minecraft World! Check out our advanced tutorials and come play with us on our free server.

Welcome to Minecraft World! Check out our advanced tutorials and come play on our free server. Minecon 2011 went really well. If any of you World Members attended, please post about your experience to the community corkboard. The opening ceremony was amazing! Here's a video of the release: After the release, we attended the panels for Scrolls and Cobalt. We then attended the Official Mojang Panel.

Welcome to another Community Byte announcement from Null Byte! The goal of the Community Bytes is to teach people in a co-operative, hands-on manner. Learning from experience and immersing yourself in a subject is the best way to learn something foreign to you, so that is exactly what we do! In our sessions, we have started to both code and complete HTS missions. This means that there is something for everyone here, so make sure you join us.

Back when I was a Windows user, I know I'm not the only one who has experienced password loss—that moment where you just can't remember your password. Sometimes it happens to the best of us. So, how can we get into the system without paying a local geek or geeksquad to do it? First, we have to look into how Windows stores their passwords.

With the rather large success of the Community Byte activities, both programming and HackThisSite, I have decided to continue to do both activities every session! With that said, when programming sessions occur, they will be lead by Sol Gates in Gobby. Also, the programming mission will no longer be to code a tool, we have changed it to be even more "noob friendly". This means that instead of coding a tool, you will be walked through puzzles and challenges that must be solved by coding a scri...

A degree in nursing from Kaplan University addresses the challenges and scenarios real nurses work through on a daily basis. Kaplan University’s Master of Science in Nursing (MSN program) is based on relevant material to help ensure our students are prepared for their careers. Our online nursing degrees are based on flexible coursework; students enrolled in the Kaplan University School of Nursing program are already nurses and there is no easier way to cater to the ever-changing schedule of a...

Lisa Nichols, contributing author of The Secret and one of the great inspirational speakers of our time, believes the best way to stay motivated when continuing your education is to “begin with the end in mind.” Pushing forward through challenges is what makes accomplishment so gratifying. Every accomplishment leads to personal growth. Nichols believes that making the completion of your degree “non-negotiable” means that you will not settle for anything less.

As we all know, security is a big thing here in Null Byte. We've talked quite a bit about ways to encrypt traffic and become anonymous on the internet, some of which entail using proxies, VPNs, and SSH tunnels. We've also talked about preference using SSL pages in practice for safe logins. These are all great protocols and tools, but aren't without their flaws and inconveniences.