
How To: Origami a simple medium heart
Learn how to make an origami heart. Use a medium square of paper to make your origami heart.


Learn how to make an origami heart. Use a medium square of paper to make your origami heart.

An opening strategy used by Black to have a strong attack against White queen/pawn openings. The Benoni Defence and variations have been used by the likes of Bobby Fischer and Kasparov, to name a few. Learn it!

The Danish Gambit opening allows for rapid attack development for White. This video explores the book line moves, along with possible counter-play by black.

Matt covers some lines with a black ...Bg4. He found the first game with analysis on the Kenilworth Chess Club site. Most of the analysis he gave for this game is taken verbatim, but he does mention a couple side variations that you should be curious about. So watch!

We look this time at 1.d4 d5 2.e3 e6 3.Bd3 Nc6, a move order I am calling the Teichmann Defense, after the player who first used it. It seems like a little-explored and reasonable approach against the Stonewall. So pay attention.

This is a discussion of a tricky line against the Stonewall, the Horowitz Defense (2...Nf6 3.Bd3 Nc6). White allows Black to spend three moves capturing the light squared Bishop and bringing White's pawn from c2 to d3, preventing a ...Ne4 invasion. This makes for very dynamic play.

This video discusses basic techniques for diving and defensive volleyball positioning when being attacked by the left, right, and middle hitter of the opposing team.

This week, the thread heads teach us how to make our t-shirts cooler, by cutting slits all over them. Not only are they stylish, but they make you look like Wolverine just attacked you. Awesome!

Everyone seems to be talking about Elon Musk's new futuristic Tesla Cybertruck, the vehicle that either looks like a cool moon rover or an outlandish video game replica, depending on your tastes.
Less than a month after launching its augmented reality Swim Goggles, wearables startup Form is preparing to add a major new feature for aquatic athletes.

Firewall solutions for macOS aren't impervious to attacks. By taking advantage of web browser dependencies already whitelisted by the firewall, an attacker can exfiltrate data or remotely control a MacBook, iMac, Mac mini, or another computer running macOS (previously known as Mac OS X).

If you're worried about the security of your Mac, there are easy measures to prevent the most dangerous attacks. Named after the tactic of accessing an unattended computer in a hotel room, we can thwart "evil maid" attacks with Do Not Disturb and LuLu, free macOS tools by Objective-See that keep an eye on unattended computers and flag suspicious network connections that indicate a malware infection.

It only takes a few commands to manipulate a MacBook's secure HTTPS traffic and pluck login passwords out of the encrypted data. Let's take Facebook and Gmail hacking to the next level by intercepting Safari and Google Chrome web traffic in real time.

Command injection is a technique used by hackers to execute system commands on a server, usually via a web application or some kind of GUI. This can happen when an application provides some sort of functionality to the user involving the use of system commands. When the input is not properly sanitized, commands not originally intended to be run are allowed to be executed.

Beginners learning brute-forcing attacks against WPA handshakes are often let down by the limitations of default wordlists like RockYou based on stolen passwords. The science of brute-forcing goes beyond using these default lists, allowing us to be more efficient by making customized wordlists. Using the Mentalist, we can generate millions of likely passwords based on details about the target.

Armis Labs has revealed eight vulnerabilities, called "BlueBorne", which put 5.3 billion Android, iOS, Windows, and Linux devices that use Bluetooth at risk. With it, hackers can control devices, access data, and spread malware to other vulnerable devices through networks. In this post, we will learn about the vulnerabilities, then look at how to find devices that have them.

In five short years, three generations of ultra-low-cost Raspberry Pi devices have challenged the boundaries of what a person can do with a $35 computer — especially with Kali Linux.

The Raspberry Pi is a credit card-sized computer that can crack Wi-Fi, clone key cards, break into laptops, and even clone an existing Wi-Fi network to trick users into connecting to the Pi instead. It can jam Wi-Fi for blocks, track cell phones, listen in on police scanners, broadcast an FM radio signal, and apparently even fly a goddamn missile into a helicopter.

Valentine's Day is right around the corner... which is the perfect excuse to ignite your inner cupid and bake a heart-shaped cake. If you have a heart-shaped cake or springform pan, you're all set. If not, don't worry—you don't need one! With a little ingenuity, you'll have a beautiful heart cake using the pans you already own.

Sulfuric acid is mixed with sugar, which is attacked by the acid. The final products are carbon, water vapor, and sulfur dioxide gas.
Samsung Galaxy S5 has an exciting feature through which you could measure your heart bit. So this video will show you how to measure your heart rate with Samsung Galaxy S5. Watch the video and follow all the steps carefully. Employ the technique in your Galaxy S5 phone.

Your heart is constantly work for you, yet you think nothing of it—and Samsung wants to change that. They stuck a dedicated heart-rate monitor on the Galaxy S5, they're putting one in the upcoming Note 4, and they're bound to slap one in every Galaxy device thereafter.

So, what has Arnold Schwarzenegger been up to since his role as the Governator? Besides his resurgence in Hollywood and spooking gym members as Howard Kleiner, he's getting culinary on us.

How to make Macrame Heart, step by step, DIY tutorial. Gift for Valentines Day. You can use this Heart as a keyring, necklace, pendant, etc...

Learn how to make Macrame Ring with a Heart, by following this step by step, DIY tutorial. Makes a nice gift for Valentines Day.
How to make a heart shaped fried egg for a Valentines day breakfast. Short and simple guide showing you how to make a delicious breakfast for your loved one.

In this guide, you'll learn how to make an origami double-heart specially for Valentine's Day. Design is by Francis Ow, made by Teofila Vasileva. What You Need:
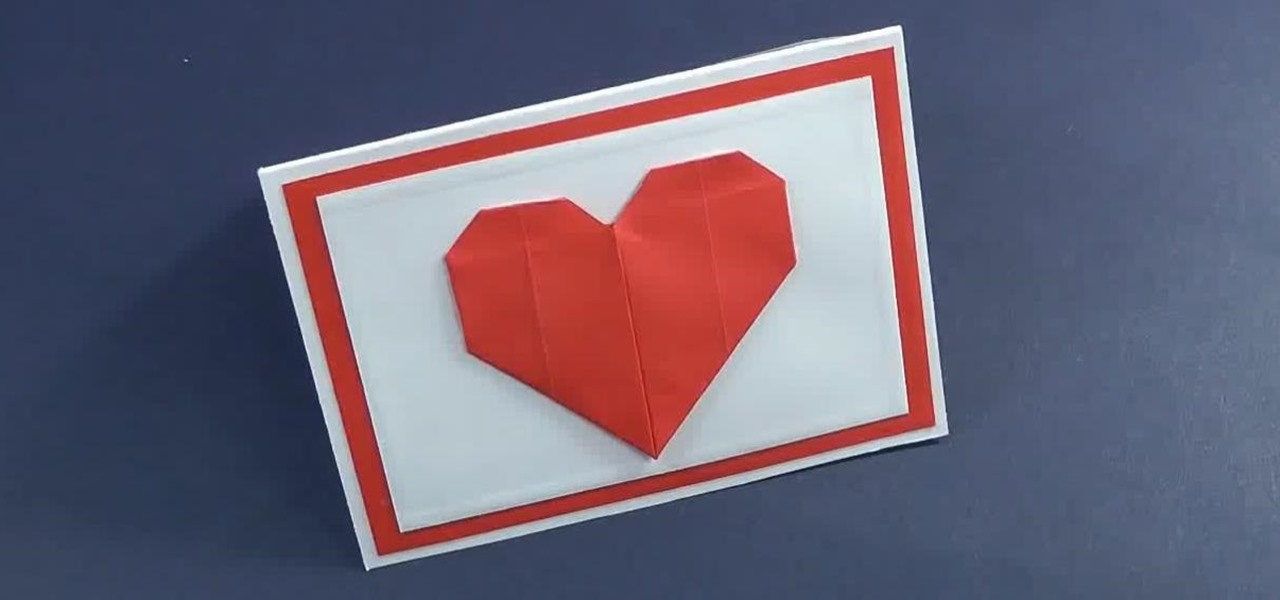
Valentine's Day is a beautiful day associated with true love. Surprise your loved one or friend and show you care with this mini Valentines card with origami heart. You need not more than 10 minutes to make the card. First You Need to Make an Origami Heart

How to make a macrame Heart, step by step, tutorial. You can use this Heart as a keyring, necklace, pendant or other decorations..

In this tutorial, we will teach you how to defend yourself against an attacker with a knife. It's the best MMA for self-defense, especially for teenagers.

Welcome back, my hacker novitiates! Many of you have probably heard of a man-in-the-middle attack and wondered how difficult an attack like that would be. For those of you who've never heard of one, it's simply where we, the hacker, place ourselves between the victim and the server and send and receive all the communication between the two.

Welcome back, my fledgling hackers! In the first part of my series on Wi-Fi hacking, we discussed the basic terms and technologies associated with Wi-Fi. Now that you have a firm grip on what Wi-Fi is exactly and how it works, we can start diving into more advance topics on how to hack Wi-Fi.

Tablets can be incredibly useful in many situations, and the kitchen is no exception. Whether you're following a recipe, using an app to convert cups to tablespoons, or getting your Gosling fix, there are a lot of reasons you might keep your tablet nearby while you're cooking.

We have another BioShock: Infinite achievement tip for you. This achievement (aka trophy for the PS3ers out there) is called Heartbreaker, and requires you to kill and Handyman by only shooting at its heart. If you haven't encountered a Handyman yet, take a look at just how much work went into creating these badass baddies.
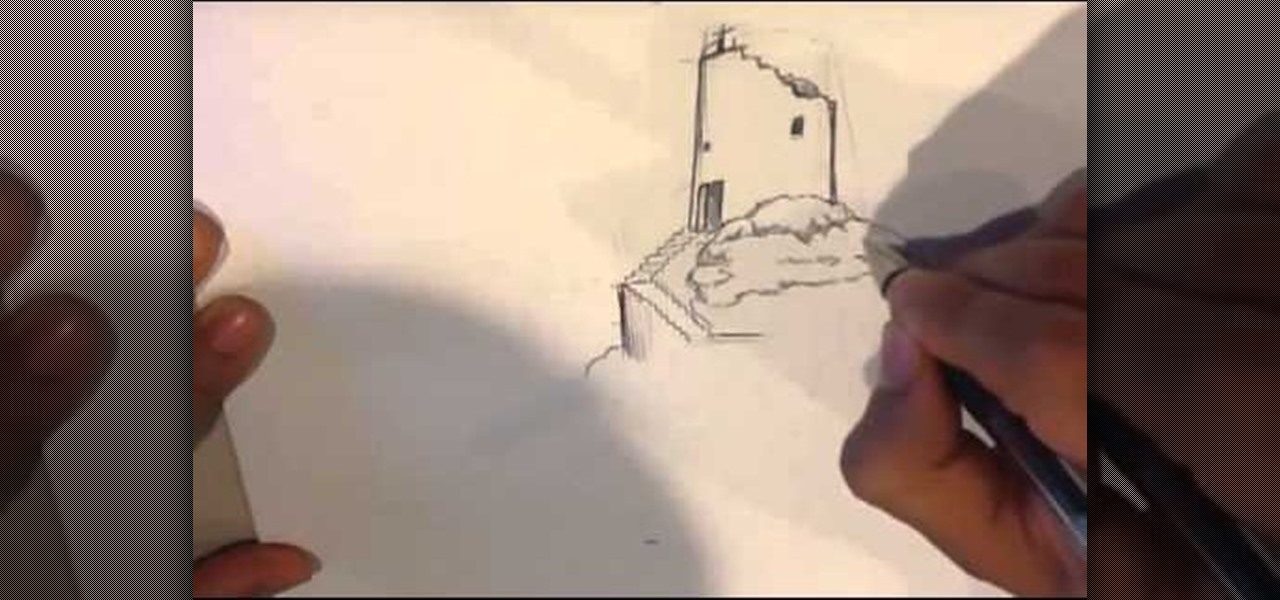
When the castle has been attacked there are only ruins left. Here is the drawing video by which i go over drawing medieval ruins. Goes with other how to draw fantasy , art videos, and art tutorials. I go through my thought process in detail at :
At the beginning of Kingdom Hearts, Sora lives on Destiny Islands along with his two best friends, Riku and Kairi. Learn How to draw Sora of Kingdom Hearts. For the full tutorial with step by step & speed control visit: how to draw.
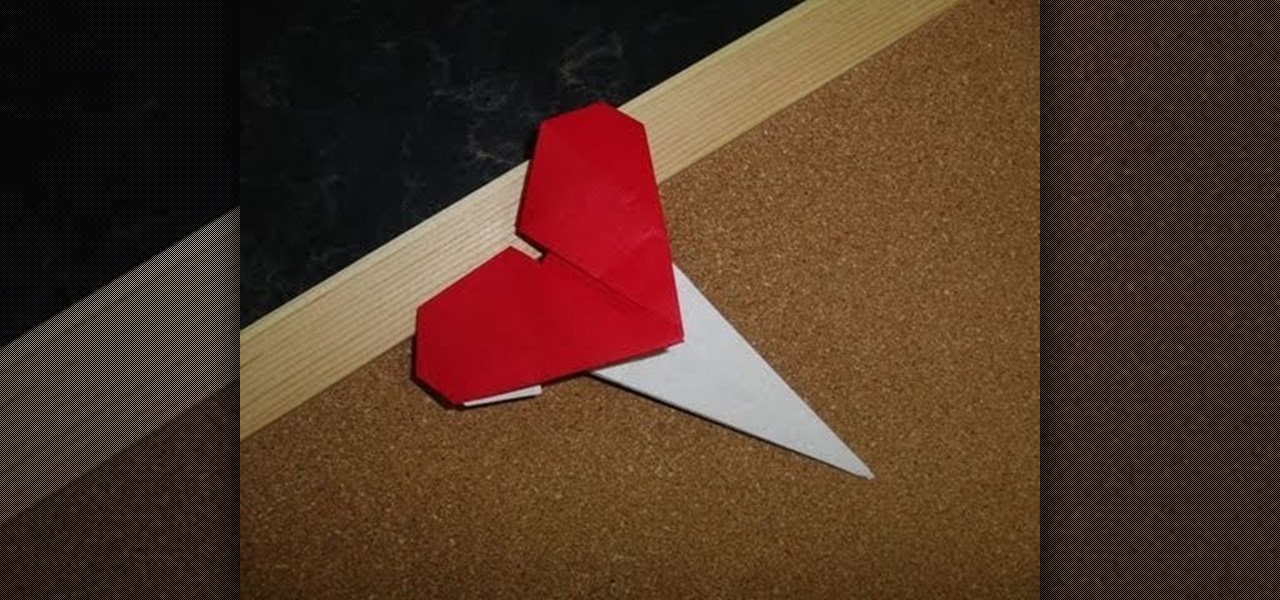
Wear your heart on your sleeve - literally - by crafting this origami heart pin. Show some love for Cupid's holiday by creasing and folding your way to origami perfection.

Broken crayons kind of suck. They make it hard for you to stuff all your crayons back into your crayon box uniformly, plus then you have to ditch the wrapper and it all looks like a mess.

In this Magic & Parlor Tricks video you will see the ‘impossible’ card trick. This card trick is performed by Andy field. First he removes all the 4 aces from the pack and puts them face up on the table. Then he chooses a card from the rest of the pack shows it to the camera without seeing it himself. It is the king of hearts. He then puts the card back into the deck somewhere in the middle. Now he takes the 4 aces in his hand all facing up, gives a little jig and out of the 4 one ace turns f...
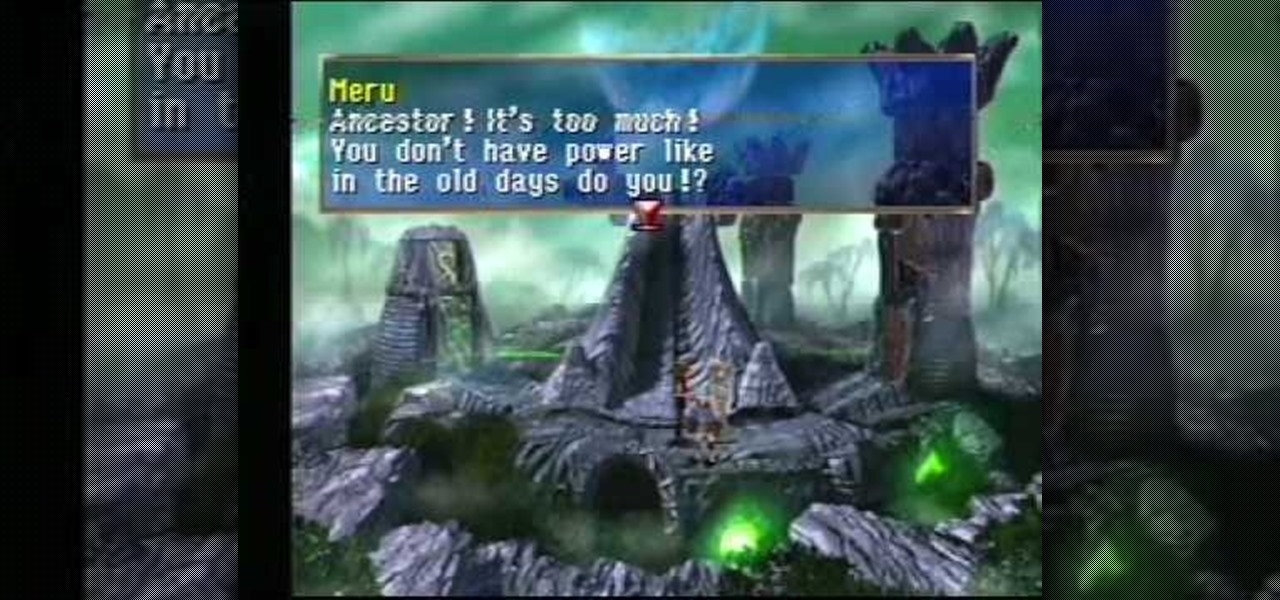
You'll find yourself in Kadessa and Deningrad in this installment of The Legend of Dragoon for PlayStation. This video walkthrough takes you from where Dart and company are exploring Kadessa, they fight and defeat the Grand Jewel for possession over the Dragon Block Staff, the party leaves Kadessa just as the Divine Dragon is launching an attack upon Deningrad, the Winglies try to teleport the party to Deningrad but they are too late to stop the attack, the party rush to the castle and make s...