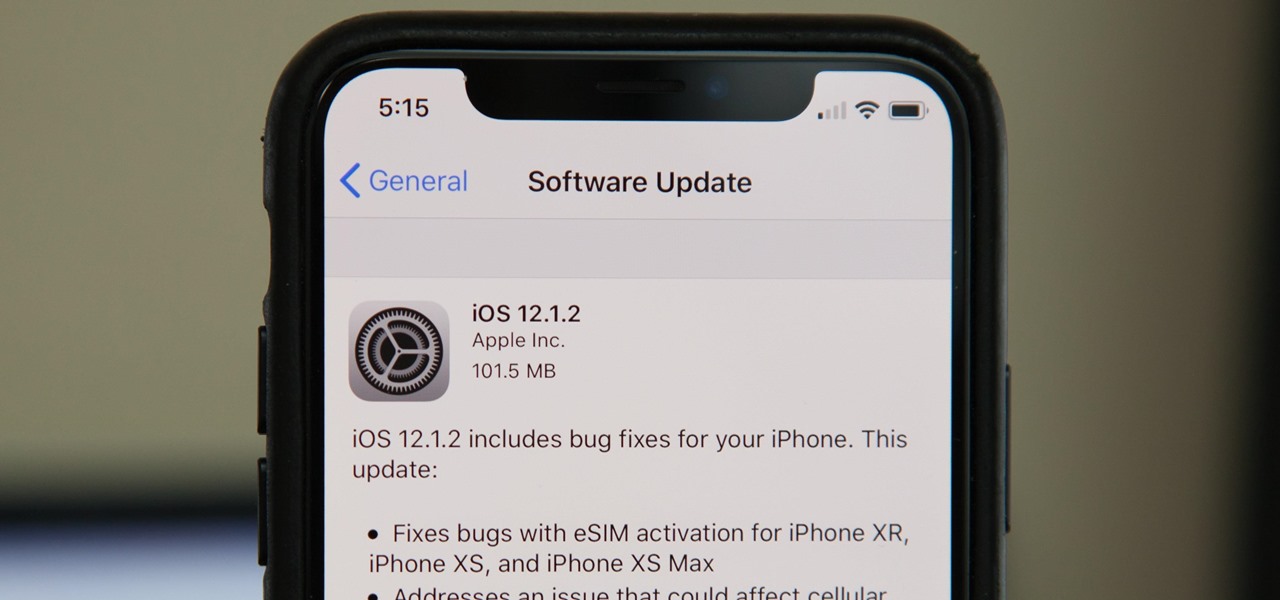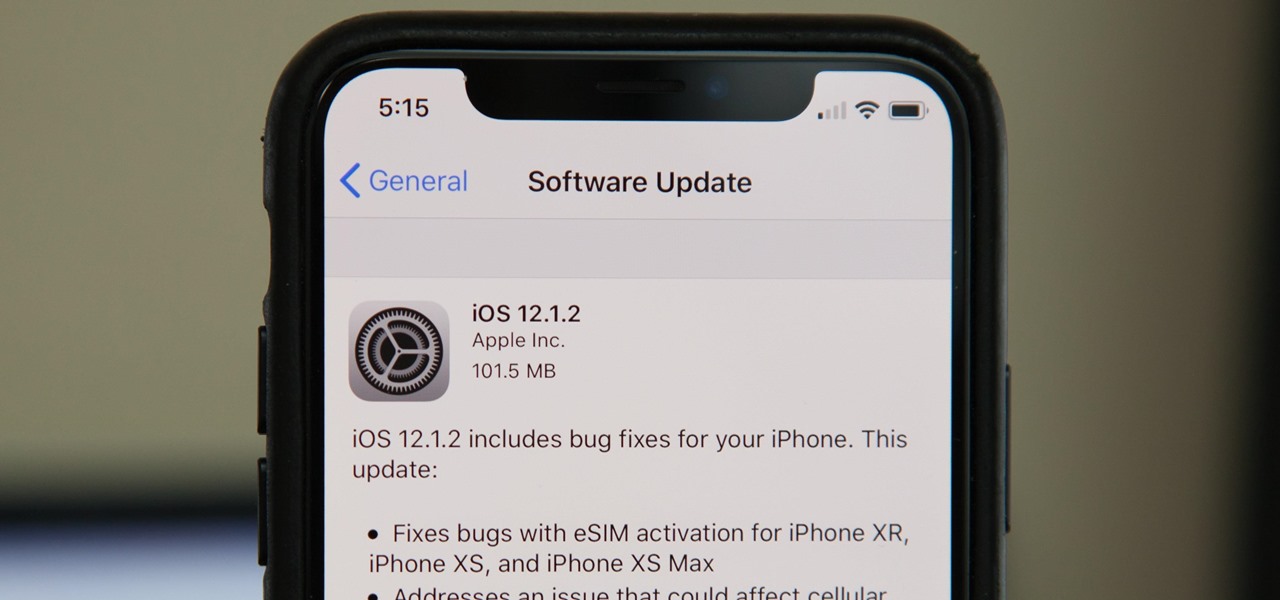
Without a second beta like most other beta versions, Apple released iOS 12.1.2 to all iPhone users on Monday, Dec. 17. The update comes just one week after the iOS 12.1.2 beta went live, so why did it have such a quick turnaround? The answer likely revolves around eSIM issues on newer iPhone models, as well as legal issues with Qualcomm.

Many online users worry about their accounts being breached by some master hacker, but the more likely scenario is falling victim to a bot written to use leaked passwords in data breaches from companies like LinkedIn, MySpace, and Tumblr. For instance, a tool called H8mail can search through over 1 billion leaked credentials to discover passwords that might still be in use today.

Apple just released the first version of the iOS 12.1.2 beta to developers on Monday, Dec. 10. The update arrives mere days after the Cupertino-based company seeded the official version of iOS 12.1.1 to the public, itself of which had been in beta development since Halloween.

Public testers, Apple just released the first public beta for iOS 12.1.2 on Tuesday, Dec. 11. The company had already released the developer beta on Monday, Dec. 10, and just like clockwork, the public beta version was right on its heels.

In recent years, medical professionals have demonstrated how the HoloLens can assist in surgeries, ranging from collarbone repairs to spinal surgeries to cosmetic procedures. Now, the largest children's hospital in the United Kingdom is also ready to deploy the technology.

Customizing the lock screen, status bar, and other aspects of your Galaxy's UI usually requires root. Thankfully, Samsung has reintroduced a well-regarded app that gives you the freedom to tailor parts of your Galaxy's interface in just a few simple steps.

Hackers rely on good data to be able to pull off an attack, and reconnaissance is the stage of the hack in which they must learn as much as they can to devise a plan of action. Technical details are a critical component of this picture, and with OSINT tools like Maltego, a single domain name is everything you need to fingerprint the tech details of an organization from IP address to AS number.

Taking a cue from the smash hit Super Mario Maker, Bandai Namco has soft launched PAC-MAN Maker in Canada ahead of a worldwide release. This is welcome news for mobile gamers, as you won't need a console to enjoy this classic arcade game when it finally touches down stateside. But if you want to give PAC-MAN Maker a shot right now, we've got you covered.

Deleted bank statements and private photos are still within an attacker's grasp, so don't think that emptying your recycling bin is enough to keep your files from coming back to life. It's possible for a hacker to recover compromising files and images from a backdoored computer completely without the victim's knowledge.

The new Android 9.0 Pie update is bringing a feature that stock Android has been lacking — screenshot editing. OEM skins like Samsung's TouchWiz have had this for years, and Apple added it to iOS just recently. But now that it's in stock Android, it'll be included with every phone going forward — trouble is, most people will have to wait for the update. Thankfully, you can get this feature right now on any phone.

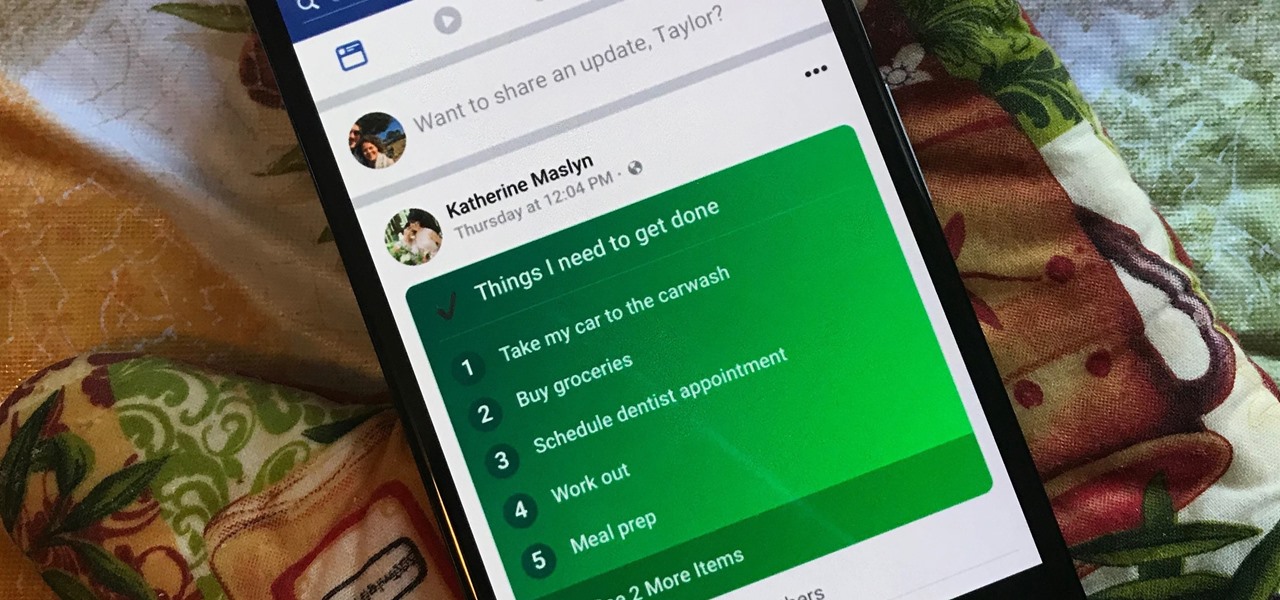
Facebook's status update box has received many new features over the years. You can go live, sell something, and even create a poll. But since all this was added, the status update box has been relatively stagnant. That's finally changing again with Facebook's newest addition: Lists.

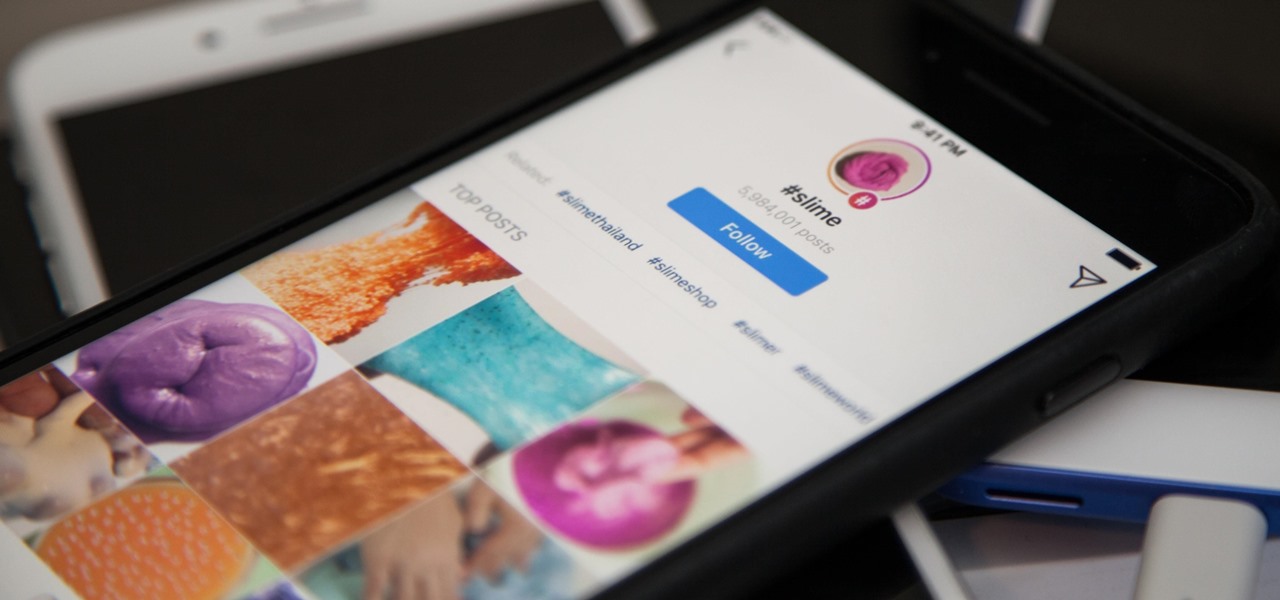
Hashtags are the backbone of Instagram. They connect photos from users all around the world and give visibility to users who don't have many followers. Now, Instagram has added more functionality to this indispensable tool, and this new feature lets you follow hashtags in your main feed right alongside all the pics and videos you see already from people or companies you follow.

An attacker with shell access to a Linux server can manipulate, or perhaps even ruin, anything they have access to. While many more subtle attacks could provide significant value to a hacker, most attacks also leave traces. These traces, of course, can also be manipulated and avoided through methods such as shell scripting.

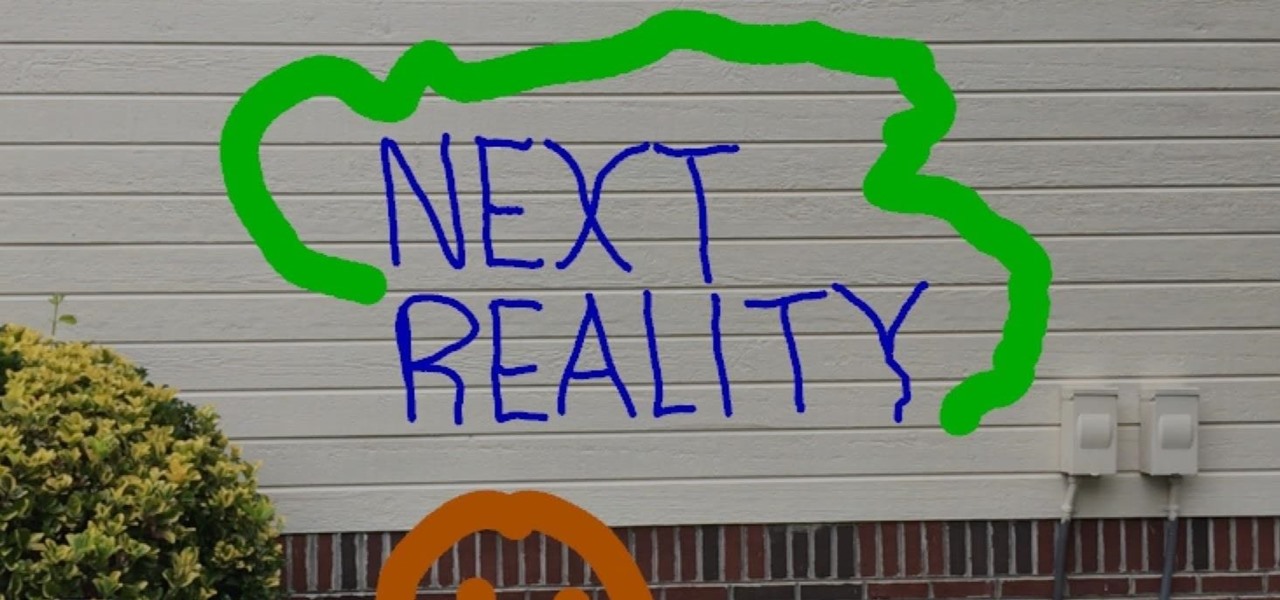
If you've ever wanted to be a graffiti artist, but you also frown upon vandalism, then augmented reality is for you.

Recently, I ran across SecGen, a project which allows a user to create random vulnerable machines. I absolutely love vulnerable machines, since a vulnerable VM is a safe and legal way to practice hacking tactics, test out new tools, and exercise your puzzle-solving skills.

Sharing your Wi-Fi password is like giving an unlimited pass to snoop around your network, allowing direct access even to LAN-connected devices like printers, routers, and security cameras. Most networks allow users to scan and attempt to log in to these connected devices. And if you haven't changed the default password on these devices, an attacker can simply try plugging them in.

As we all know, and certainly have marked on our calendars, it's World Emoji Day! Considering that over five billion emojis are sent daily on Facebook Messenger alone, emojis deserve to be celebrated, and Apple's doing just that. On this monumentous day, the tech giant is gifting us all with images of its newest emojis. From dinosaurs to headscarf-clad women, the releases are sure to please emoji fanatics throughout the world.

If you need a tiny, flexible attack platform for raining down human-interface-device (HID) attacks on unattended computers, the USB Rubber Ducky is the most popular tool for the job. By loading the Ducky with custom firmware, you can design new attacks to be effective against even air-gapped computers without internet access. Today, you'll learn to write a payload to make "involuntary backups" through copying a targeted folder to the Ducky's USB mass storage.

Type 1 diabetes is an attack on the body by the immune system — the body produces antibodies that attack insulin-secreting cells in the pancreas. Doctors often diagnose this type of diabetes in childhood and early adulthood. The trigger that causes the body to attack itself has been elusive; but many research studies have suggested viruses could be the root. The latest links that viruses that live in our intestines may yield clues as to which children might develop type 1 diabetes.

In this article, I am most likely going to humiliate myself by showing you all the horrible hashtagging I am wont to do. When it comes to hashtags, well, everybody knows if you desire any chance at all of getting noticed on Instagram, you got to hashtag.

Someone out there is testing an unknown mid-range phone codenamed "Heart," and it has a 16% lead in speed on the Oppo F3 Plus and is just 15% shy of the Samsung Galaxy S8+, according to GSM Arena.

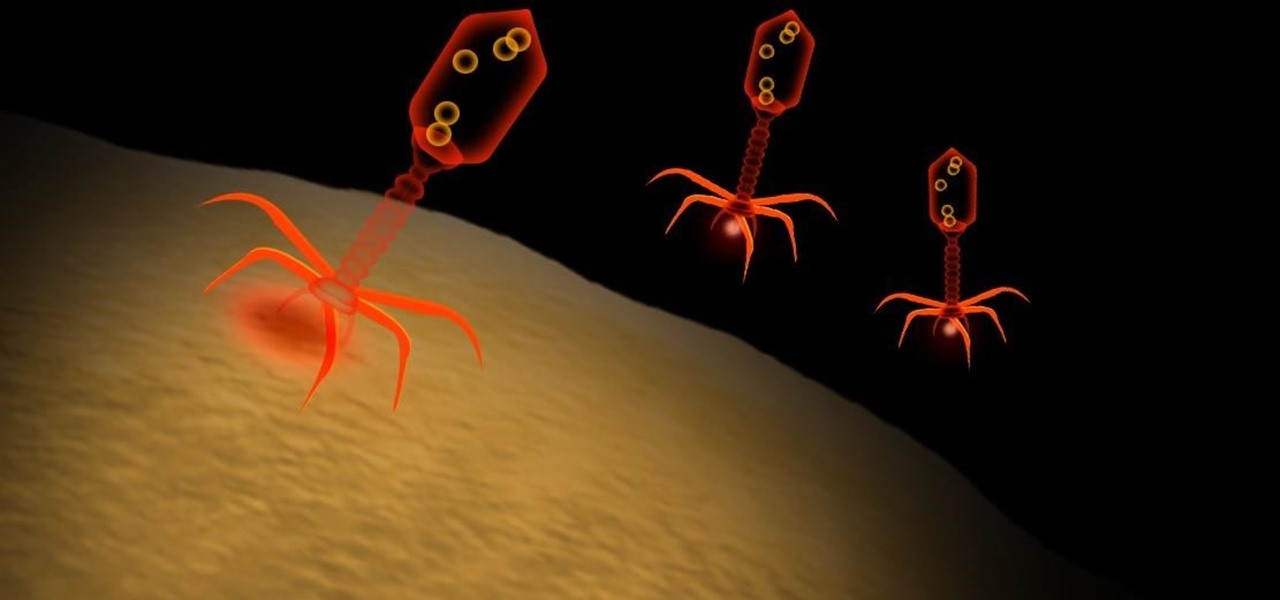
Take a close look at the image above. These bugs spread a deadly parasite that infects thousands of people each year. They also live in the US, and it's important to know where they are and whether you need to worry that they're carrying a dangerous infection.

Texas has become only the latest state to face an unfortunate outbreak of mumps, but so far seems to be the hardest hit. On April 12, two days before the CDC's report was released, the Texas Department of State Health Services released a health advisory indicating this is the highest instance of mumps reported in 22 years.

Today, December 7, it was officially announced that Magic Leap has found their replacement for the recently departed Brian Wallace. Magic Leap CEO Rony Abovitz has tapped Brenda Freeman, former EVP and Chief Marketing Officer of National Geographic Channel, as their new Chief Marketing Officer.

With all of the bare-bones setup out of the way in our Mac for Hackers series, your Apple machine should be ready to run a significant amount of pentesting tools. We can pull tools from GitHub and compile them, we can pull dependencies or tools from Homebrew, we have both Python and Ruby. Everything is ready to go and now it's time to start building a toolbox on our local host.

We already know that Samsung's Galaxy S7 is one of the most versatile smartphones ever made, complete with edge-to-edge displays, water resistance, and a huge battery. But what's versatility without durability? How much punishment can the Galaxy S7 take? Let's play a game of Samsung Galaxy S7 Punch-Out!! and see what happens.

Welcome back everyone. I apologize for the lack of training articles, but I've been rater busy lately. I've recently picked up a second job and my college courses are now back in session, so I'm a bit strapped for time.

Most people are familiar with the fact that vinegar adds sourness to a dish, in varying degrees from light acidity to puckering acid. However, vinegar can also be used in lieu of salt when seasoning the final touches to sauces, soups, and stews.

When they were purchased by Google back in 2011, Motorola underwent a sweeping change in software philosophy. All throughout the UI on their flagship devices, edgy design patterns were replaced by clean, minimalist interfaces akin to vanilla Android. This philosophy has continued on as Motorola's signature, even though they have since been sold to Lenovo.

In recent weeks, some people have been shunned from the Null Byte community because they expressed "black hat" aspirations. This is because Null Byte is the "white hat" hacker training/playground. Although most of us think we know what that means, it does beg the question; "Who and what is a white hat hacker?"

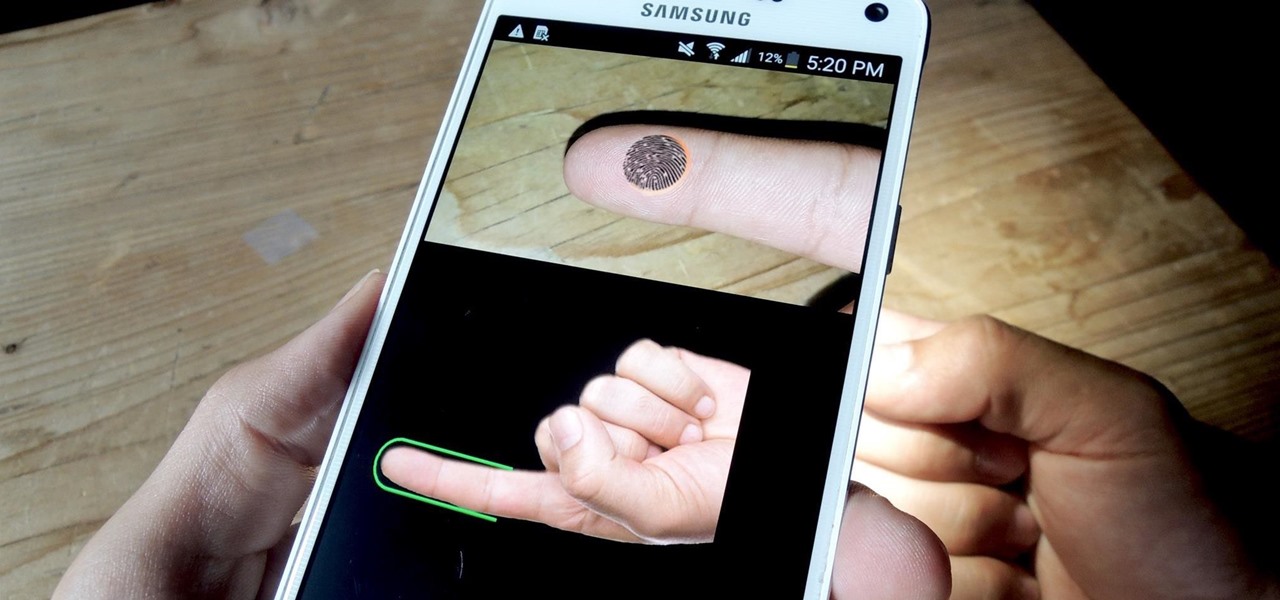
If you have a specific app you want to lock so that others can't access it, the most secure way of doing so is with biometrics. While there are options to lock apps with either a PIN or pattern, these can easily be figured out with a simple glance over your shoulder. It's much more difficult for someone to crack your fingerprint ID, unless they chop off your finger, of course.

T-Mobile's "Uncarrier" initiative has done wonders for my wallet and my data usage. Before I had to deal with being throttled down to 2G speeds after passing my data limit, but thanks to their unlimited data plans, I'm free to use as much LTE data as I possibly can. The only downside is, when sharing data through a mobile hotspot (tethering), T-Mobile imposes a 5 GB limit (which was recently upped to 7 GB for some).

NOTICE: Ciuffy will be answering questions related to my articles on my behalf as I am very busy. Hope You Have Fun !!!

Welcome back, my hacker novitiates! In an earlier tutorial, I had introduced you to two essential tools for cracking online passwords—Tamper Data and THC-Hydra. In that guide, I promised to follow up with another tutorial on how to use THC-Hydra against web forms, so here we go. Although you can use Tamper Data for this purpose, I want to introduce you to another tool that is built into Kali, Burp Suite.

Welcome back, my hacker novitiates! Every so often, a MAJOR vulnerability appears that makes millions of systems vulnerable to attack. The most recent, named Shellshock, basically leaves every Mac OS X, Linux, and UNIX system on the planet vulnerable. As nearly two-thirds of all web servers on planet Earth run one of these operating systems (primarily Linux), that's a whole lot of systems out there waiting to be harvested.

Every now and then, you'll bite into the end piece of a perfectly good cucumber only to get an unwelcome bitter and acrid taste. This happened to me for years, no matter how carefully I selected my cukes, although I generally had better luck with ones I got from local growers and the farmer's market.

The folks behind StumbleUpon have created a video service that is just as awesome at introducing you to new content as their website service is.

Log in to your LinkedIn profile, and you'll immediately be prompted to check out who's peeked at your profile. With one click, you can discover how many recruiters, companies, and random people have viewed your online resume.

Welcome back, my novice hackers! There are SOOOO many ways to hack a system or network, which means you need to think creatively in order to be successful.