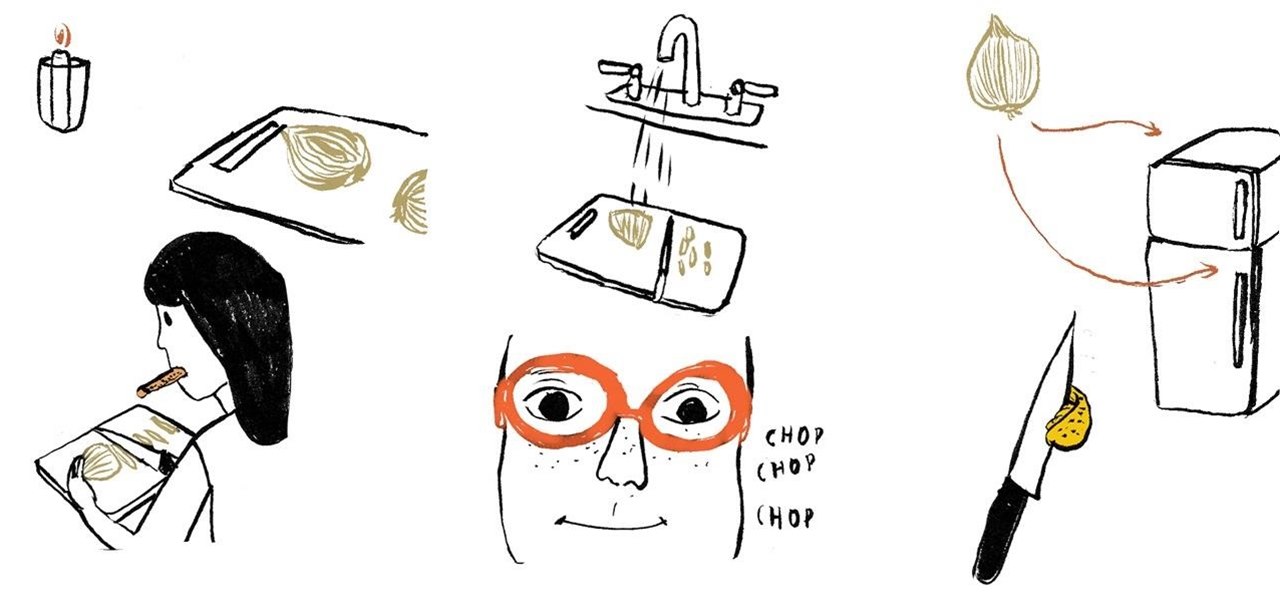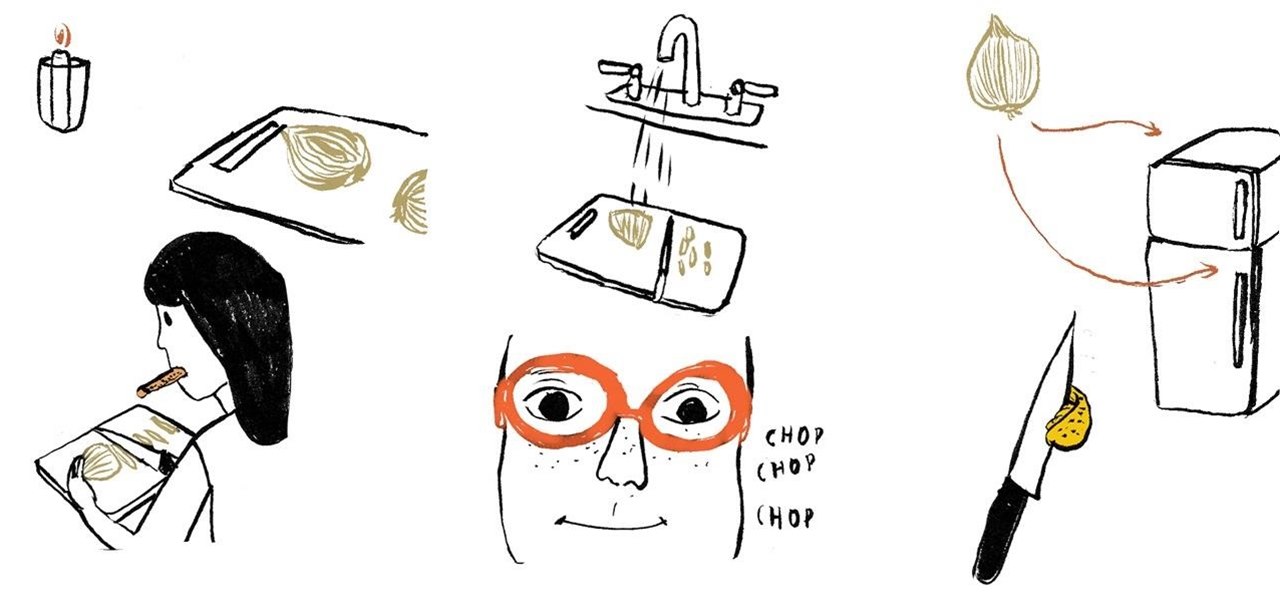
Is it possible to cut or chop onions in the kitchen without stinging eyes and looking as if you just watched the saddest movie ever? Before we get to that answer, it's important to know why we tear up when cutting raw onions in the first place. What is this irritant? Are you reacting to the odor? The answer to the latter question is "no," and the irritant responsible is amino acid sulfoxides.

Glow sticks, a popular favor at parties and outdoor events, and a must-have on Halloween, can be traced back to the United States Navy in the mid-1960s. The military desired improved visibility during night operations, and glow sticks, with their small-size portability and lack of batteries, were a perfect tactical solution.

Food can smell great before, during, and after cooking. A pot of stew simmering away on the stove will tantalize you all afternoon, and there's nothing better than the smell of fresh-baked cookies lingering in the house for hours.
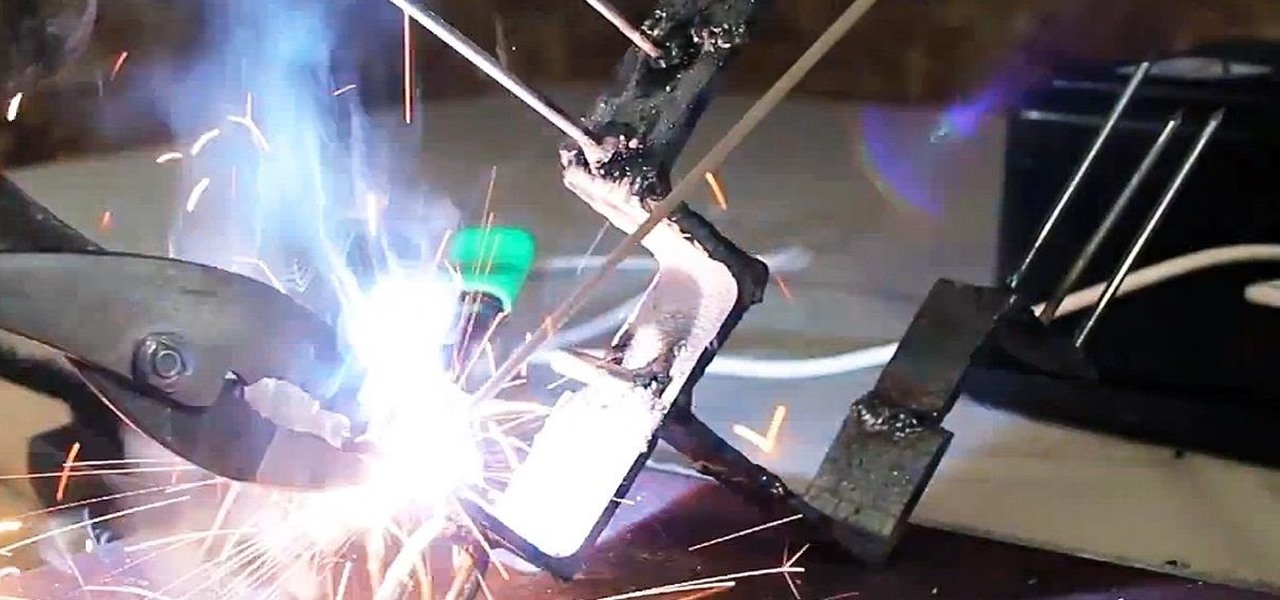
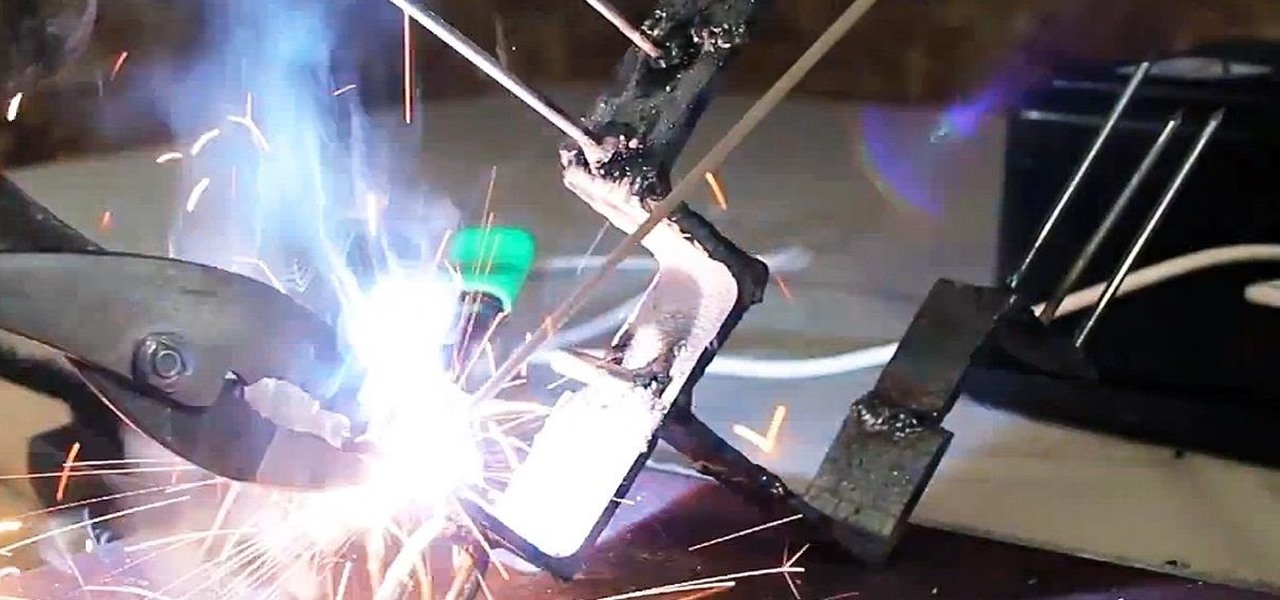
Lurking inside your old junk microwave is an abundance of useful parts that can let you melt metal, spot weld, and make electrifying Jacob's ladders. You can even make a powerful AC arc welder, perfect for making hard-to-solve puzzles and even makeshift weapons for the zombie apocalypse.

We frequently associate plastics with the modern era, starting at around the 1950s with the prevalence of bakelite. However, for all of you "you can't use plastic in Steampunk" purists out there, I have bad news for you:

If you're a Steampunk (or costumer of any variety) and you don't know what Rub 'n Buff is, this tutorial will make your life so much easier. You have no idea.

We see Steampunk props all the time and wonder where the maker found all their pieces. In fact, for some people it's almost like a game to examine each prop and see if they can name all of the original parts.

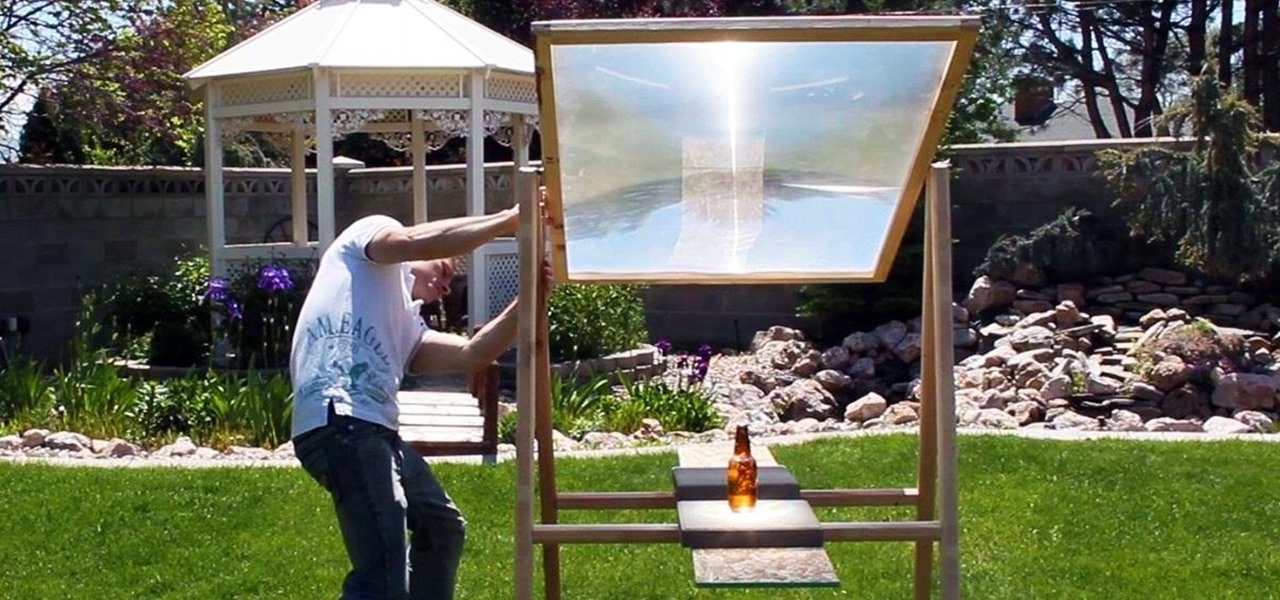
Here is how you can build a frame for your MEGA SOLAR SCORCHER in under an hour, and for less than $8!! This is effectively a 4 foot magnifying lens that concentrates insane amounts of heat from the sun. What would you do with all this free solar power? My design for this custom "Scorcher Frame" is easy to use, and incredibly cheap to make, as you can see in this step-by-step video.

Psy's K-Pop hit, Gangnam Style has taken YouTube, and now the world by storm. Love or hate the song, there is just no way you'll watch the music video only once.

Hi! All the cake lovers, welcome to my first post in the World of Dessert Recipes. I would like to contribute a recipe for the chocolate cake, called Taraba. The original recipe was made in Bosnia. It is one of my favorite cakes, very sweet, but does not contain fruit.

If you're anything like me, you probably rinse your mouth out after you brush your teeth. I know technically you're supposed to not rinse your mouth out after brushing, but I just can't stand the feel of the excess toothpaste in my mouth. It's a surefire way to dry it out.

Vampires and bad dreams aren't the only enemies of the unwary sleeper. Teeth grinding while asleep is an annoying and possibly painful problem afflicting may people. There are a variety of reasons you may grind your teeth but, luckily, there are also a number of solutions to this nocturnal problem.

Riding your bike with and incorrect seat height will make it more difficult to peddle and can be hard on your knees. Ensure a more enjoyable bike ride by taking a couple of minutes and making sure your seat is the correct height.

If you want to see what it really looks like to make rice crispy treats with regular people and people in the kitchen just like you probably have then this video will do just that. RKTs are easy to make but can be a little tricky if you don’t know where you keep the pans.

In order to prepare Nicaraguan Tamales, you will need the following ingredients: chicken, orange, green pepper, onions, celery, garlic, margarine or vegetable shortening, potato, plantain leaves, and cornmeal.

In this tutorial, we learn how to make sonora hot dogs. You will need: tomatillos, chicken broth, refried beans, queso, dried cilantro, hot dogs, lemon juice, bacon, tomato, garlic, jalapeno, mustard, ketchup, and mayonnaise. First, place the cilantro and jalapeno and place into blender with lime juice. Next add in your chopped onion and chopped tomatillos and start to blend while adding in the garlic and chicken broth. Next heat up a large pan with lard, and once it has melted add the sauce ...

There's a little-known secret in the world of microwave ovens that even the manufacturers don't care to tell you in their manuals. And once you know it, you'll never go back to using your microwave as you used to.

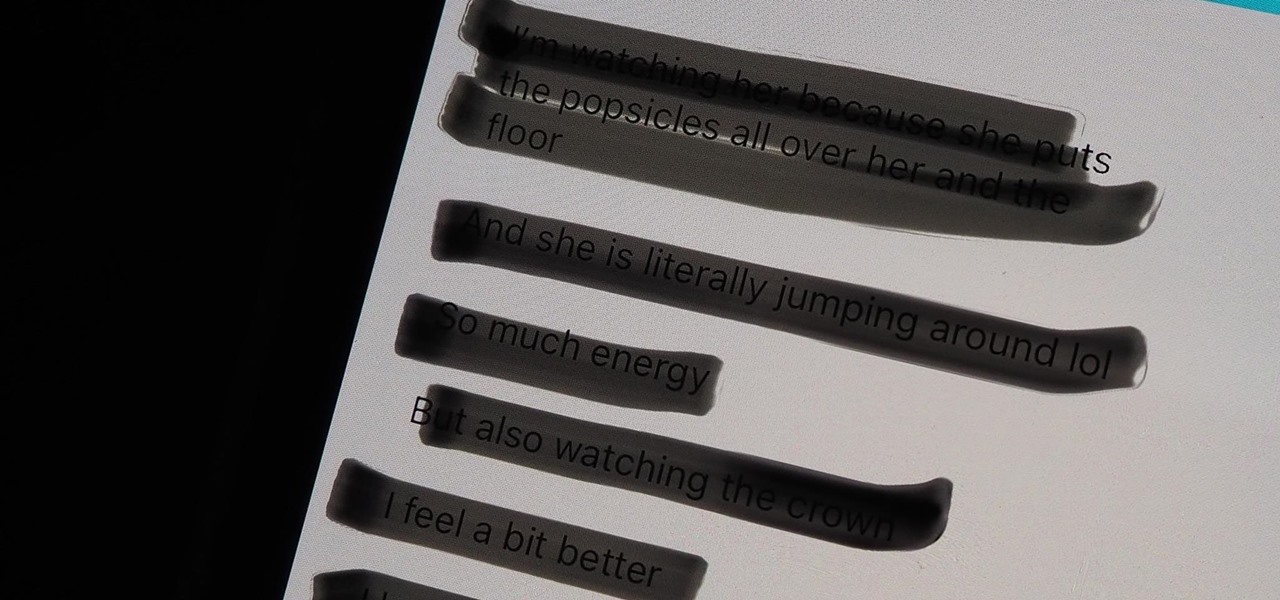
On an iPhone, it's easy to blur or cross out faces and sensitive information found in your images — just use Apple's Markup tool for all your obfuscation needs. Things aren't as simple when it comes to videos. There are no built-in iOS features to blur, redact, or otherwise obscure people, objects, and text in videos, but we've found a free solution that gets the job done well without any watermarks.

These days, most images we post online or share with others come from our smartphones. Whenever personal data is in them, such as debit card numbers, addresses, phone numbers, passwords, and other sensitive information, it's easy to jump into your iPhone's markup tools to black out the text before sharing. But a digital marker may not hide everything.

For many of us, our work phone and our personal phone are one and the same. Just any old phone isn't going to cut it when you need to meet a deadline — a phone with built-in features that make it easier to get things done is almost a must.
Welcome back Hackers\Newbies!

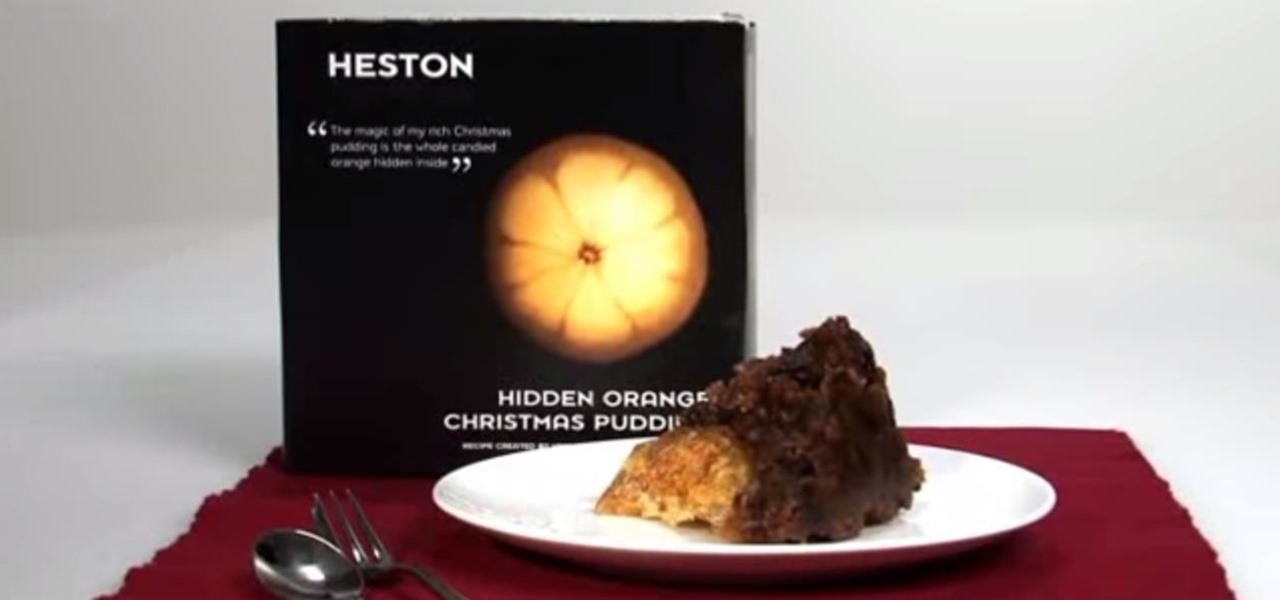
No, not Charlton Heston. The only pudding he ever made was steak and kidney. I'm talking about Heston Blumenthal, world famous chef and pudding lover, and the man behind the "Heston"— a plum pudding with an orange hidden within, brought to you by Waitrose (see video below).

Find out how everything in a chemistry lab works, from pipettes to burners to recrystallization to storage. You'll get precise instructions on how to work and perform certain scientific duties in the chem lab, whether it's chemical or just ordinary high school science.

Find out how everything in a chemistry lab works, from pipettes to burners to recrystallization to storage. You'll get precise instructions on how to work and perform certain scientific duties in the chem lab, whether it's chemical or just ordinary high school science.

How to make a compost pile with green and brown materials

To make instant hot ice or sodium acetate, first pour two jugs of vinegar minus one cup into a large pot. Then, slowly add baking soda to the mixture and stir it. When the vinegar and baking soda no longer react, stop adding baking soda. Next, add the rest of the vinegar to the pot. Boil half of the solution off and cool it down to room temperature. For better filtering, add charcoal to the mixture. Filter out the charcoal with a wire sifter. Heat up the solution again and filter it through c...

You want to create a delicious and flavorful meal for your guests but you don’t want to ruin everyone’s diets with a bunch of unhealthy calories. Grilled salmon is not only moist and flavorful but is extremely good for you.

Here's a great traditional feast with a glazed ham, cheesy scalloped potatoes and beans. This ham meal is super easy to prepare. Watch this how to video to learn how to make a glazed ham that the entire family will love.

In this series of baking videos, you'll learn an easy recipe for making peanut brittle. Chef Brandon Sarkis shows you step-by-step what ingredients and bake ware you'll need to make the candy, how to heat and combine the ingredients, and cook, cool, and crack the perfect peanut brittle.

Everyone should know that assigning complex passwords to sensitive digital accounts is the best practice for protecting yourself against hacking. Those who adhere to password creation best practices also know that keeping up with passwords for every account is nigh impossible, even when using passphrases. This is why using a password manager is highly recommended.

HomePod and HomePod mini are excellent smart speakers if you're entrenched in the Apple ecosystem. They even offer ways to protect your sensitive information from friends and visitors who try to ask Siri to spill your secrets. But there's an extra layer of privacy you can put in place to make sure nobody gains access to any important notes, reminders, and calendar events.

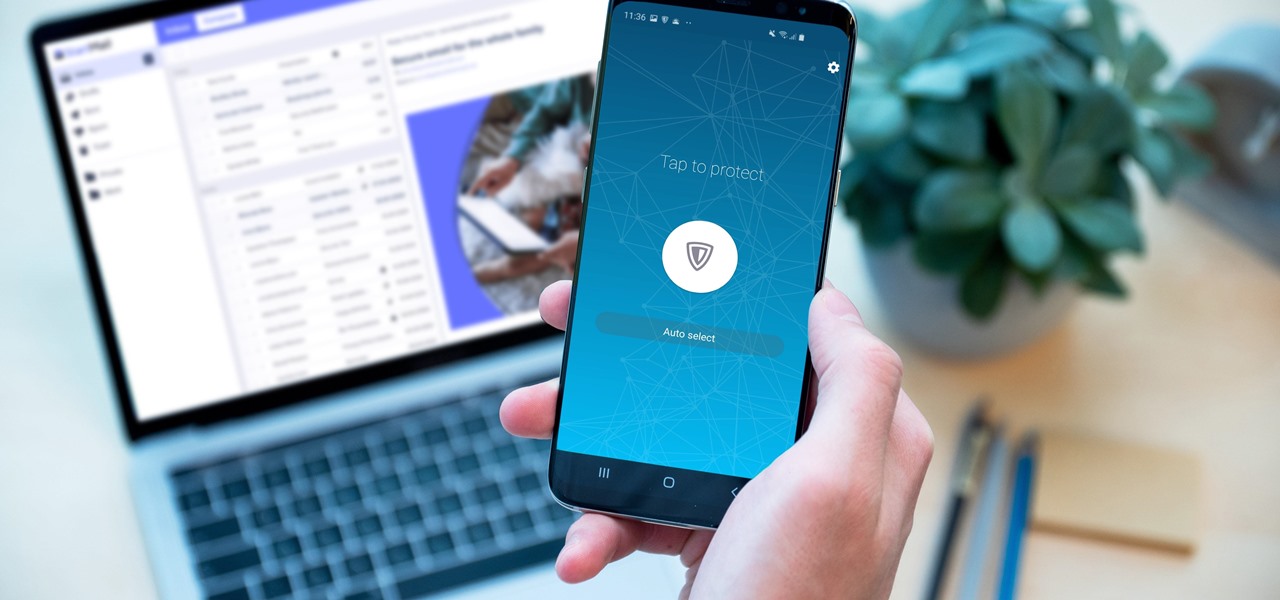
Your sensitive personal data should be strongly protected, and it's never more vulnerable than when you are online. The internet connection is a prime avenue of exposure, and email is one of the least secure forms of communication. Fortunately, there is an easy solution to both of those problems.

The true crime genre has long been popular on television and more recently on podcasts with shows like Serial.

Now that more people are working from home on unsecured networks and personal devices, hackers are having a field day accessing everything from private browsing histories to personal banking information. A virtual private network (VPN) is the first and most important line of defense when it comes to protecting all of your devices from digital intrusions, but not all VPNs are created equal.

Post-exploitation is often not quite as exciting as popping the initial shell, but it's a crucial phase for gathering data and further privilege escalation. Once a target is compromised, there's a lot of information to find and sift through. Luckily, there are tools available that can make the process easy. One such tool is Postenum.

Every single photo you take carries with it a considerable amount of seemingly "invisible" yet important information known as metadata. Although metadata is usually helpful to sort your photographs by location and date, that same information could potentially be used against you, especially if the pictures are taken during a precarious situation.

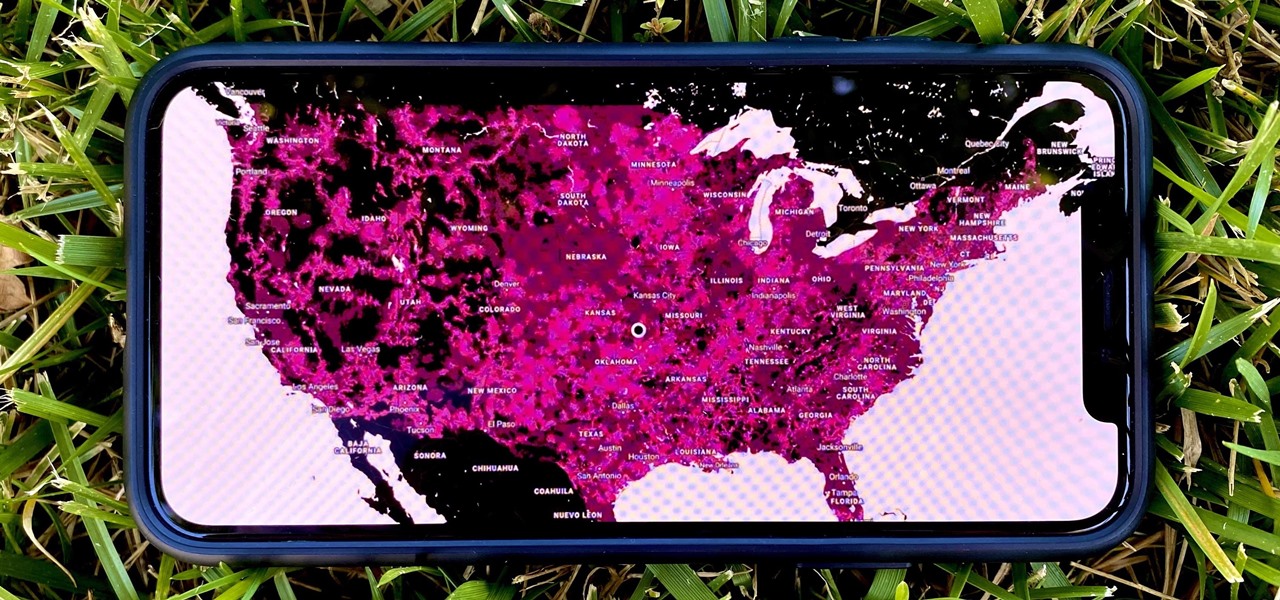
In 2009, 4G LTE networks rolled out in Stockholm and Oslo, replacing 3G as a better upgrade to the mobile data technology that gives us the broadband speeds we have on our mobile devices. Over a decade later, and we have the latest, next-generation wireless network technology among us, 5G, but can you even use it?

No matter how many camera improvements a phone adds, you're always better off using manual mode. Known as "Pro Mode" on the Galaxy S20, this feature can remove Samsung's pre- and post-processing from photos, putting you in total control.

Smartphones are more like computers than actual telephones. Unfortunately, thieves, hackers, and other bad actors know this and are always looking to make money off your personal data. Thankfully, your Galaxy S20, S20+, or S20 Ultra has tools to combat these threats — as long as you know where to look.

Hashes are commonly used to store sensitive information like credentials to avoid storing them in plaintext. With tools like Hashcat, it's possible to crack these hashes, but only if we know the algorithm used to generate the hash. Using a tool called hash-identifier, we can easily fingerprint any hashes to discover the right Hashcat mode to use to retrieve a password.