Many popular IoT devices have terrible security. For instance, a hacker who's on the same Wi-Fi network as a Sonos speaker can assume direct control over the device's behavior. If an IoT device doesn't secure the messages used to control it over a network, it's easy for somebody to write a few Python scripts to make it do whatever they want.

You can easily deck out your favorite phone with great wallpapers, ringtones, and icons, but what about fonts? Not all Android skins let you change the system font, and even when they do, the options are often limited to a few choices. Certain root apps can open up the system font to customization, but some of these can cause problems now that Google introduced a security measure called SafetyNet.

With just one line of Ruby code embedded into a fake PDF, a hacker can remotely control any Mac computer from anywhere in the world. Creating the command is the easy part, but getting the target to open the code is where a hacker will need to get creative.
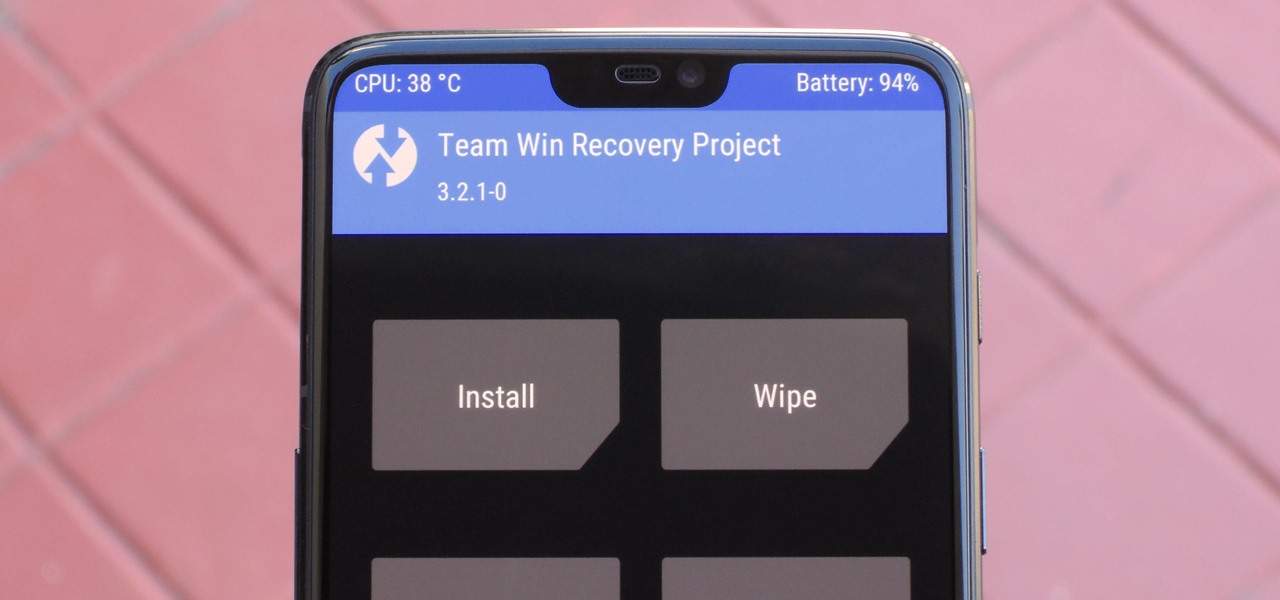
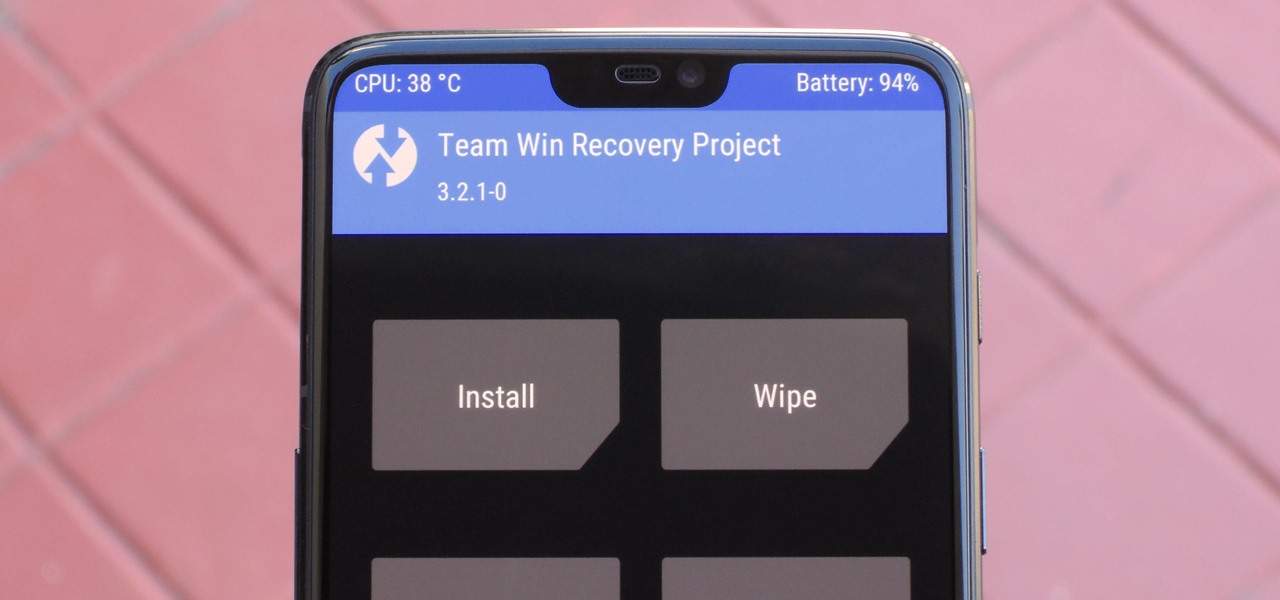
When it comes to modding Android, there's no better tool than Team Win's TWRP custom recovery. You can use it to root your phone, flash mods like Magisk or Xposed, and even replace the entire operating system with a custom ROM like LineageOS — honestly, there's not much this utility can't do.

If you ever want to root your OnePlus 6, install TWRP, get Magisk and Xposed, or flash a custom ROM, the first thing you'll need to do is unlock your bootloader.

Nmap is possibly the most widely used security scanner of its kind, in part because of its appearances in films such as The Matrix Reloaded and Live Free or Die Hard. Still, most of Nmap's best features are under-appreciated by hackers and pentesters, one of which will improve one's abilities to quickly identify exploits and vulnerabilities when scanning servers.

The internet is constantly under siege by bots searching for vulnerabilities to attack and exploit. While conventional wisdom is to prevent these attacks, there are ways to deliberately lure hackers into a trap in order to spy on them, study their behavior, and capture samples of malware. In this tutorial, we'll be creating a Cowrie honeypot, an alluring target to attract and trap hackers.

Cross-compilation allows you to develop for one platform (like Kali) and compile to run on a different platform (such as Windows). For developers, it means that they can work on their platform of choice and compile their code for their target platform. For hackers, it means we can compile exploit code for Windows from Kali.

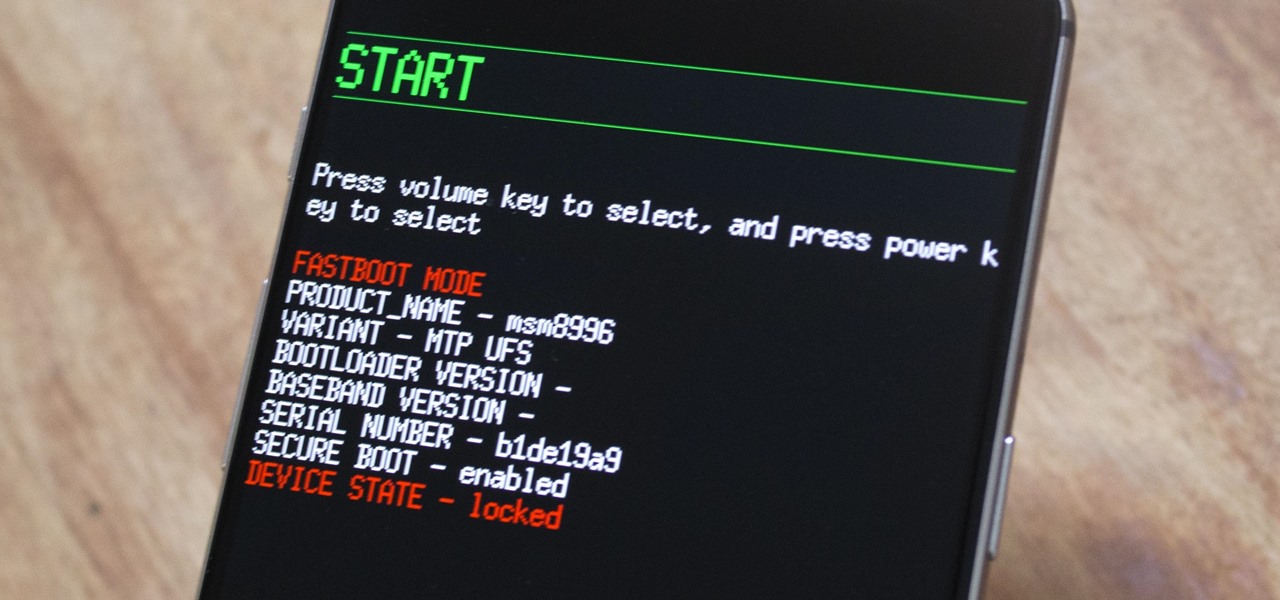
The OnePlus 3 and 3T are two of the most modder-friendly devices to be released in 2016. Not only that, but they're both extremely solid phones which happen to sport a very reasonable price tag. Among the things that make these devices such a joy for tinkerers is the fact that they have an unlockable bootloader, receive timely kernel source releases, and are actually quite easy to root.

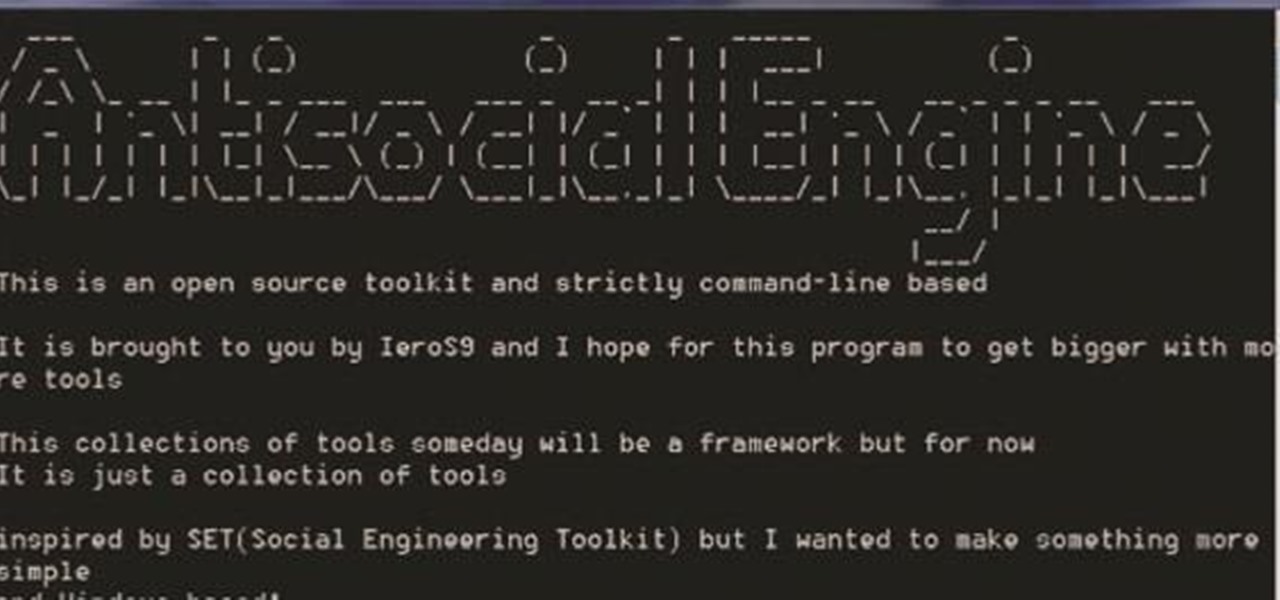
A.E Hi again this is my second post on nullbyte. The first one was on how to make a remote screenshot captor, now I will give you a presentation for a project of mine(I have named It Antisocial Engine) that It is not something extraordinary but will help many guys.

When attempting to compromise a target, we want as much control as possible over the victim. Metasploit's meterpreter allows us to have immense control over the victim, the only issue is that sometimes we can't land a meterpreter. We may only be able to land a standard shell, but fear not, there is a way to upgrade our shell into the all powerful meterpreter!

Welcome back, my fledgling hackers! Sometimes, for a variety of reasons, we can only get a command shell on our target system. For instance, with Metasploit, it's not always possible to get the all powerful Meterpreter on our target system. In other cases, we may be able to connect to a command shell via Netcat or Cryptcat.

Heartbleed, move over. There's a new bug in town, and this time it's also affecting Mac and Linux computers. It's called Shellshock (its original official title is CVE-2014-6271), and it's currently got a 10 out of 10 severity rating over at the National Cyber Awareness System. While some updates have been issued to fix this bug, they were incomplete, and your system is probably still vulnerable, as it has been for the last probably 20 years.

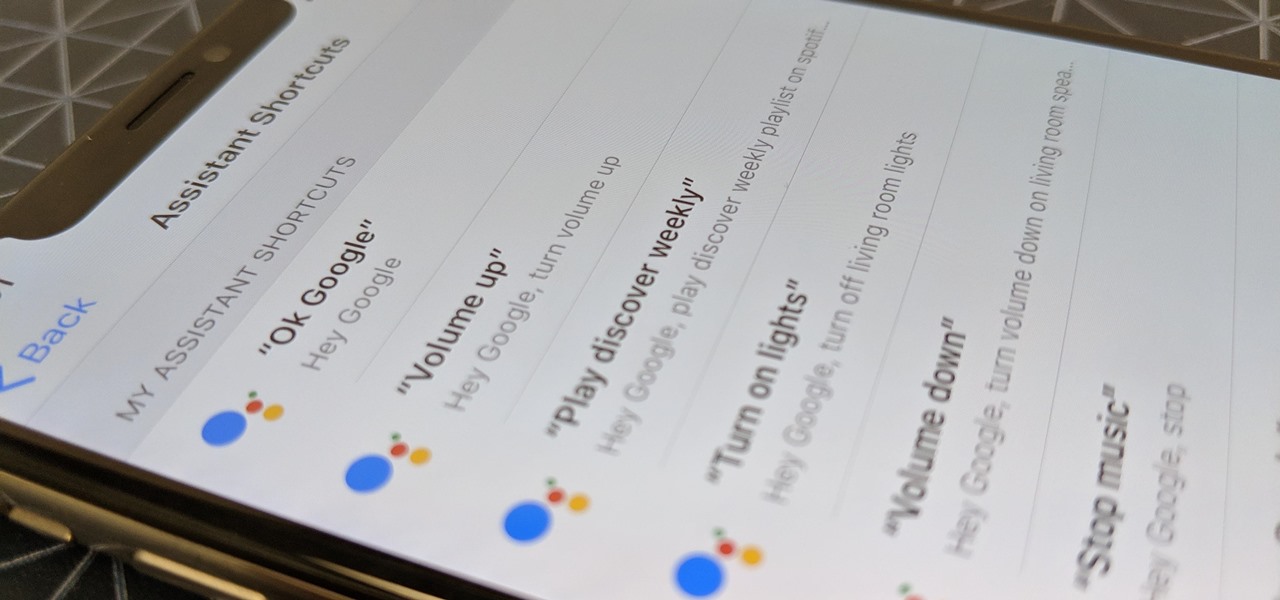
When Google introduced their new launcher alongside the Nexus 5, one of the most innovative features was the "always listening" voice search, meaning that at any time you were on your home screen, triggering a Google search was as simple as saying "Okay, Google."

Welcome back, my budding hackers! I've written several listener guides on creating a malicious PDF or malicious Word document that would carry in it a payload with the Meterpreter, or reverse shell enabling you to own the system. One of the hurdles to using these techniques is the antivirus (AV) software on the target system. For instance, if you try to email a malicious PDF or Word doc, it's likely that the victim system will alert the victim that it contains a virus or other malware.

Welcome back, my budding hackers! Previous to this tutorial, we've focused mostly on hacking the target system. If we're successful in owning the target system, we'll then want to make certain that the system administrator doesn't know we were there, and that he or she cannot track us.

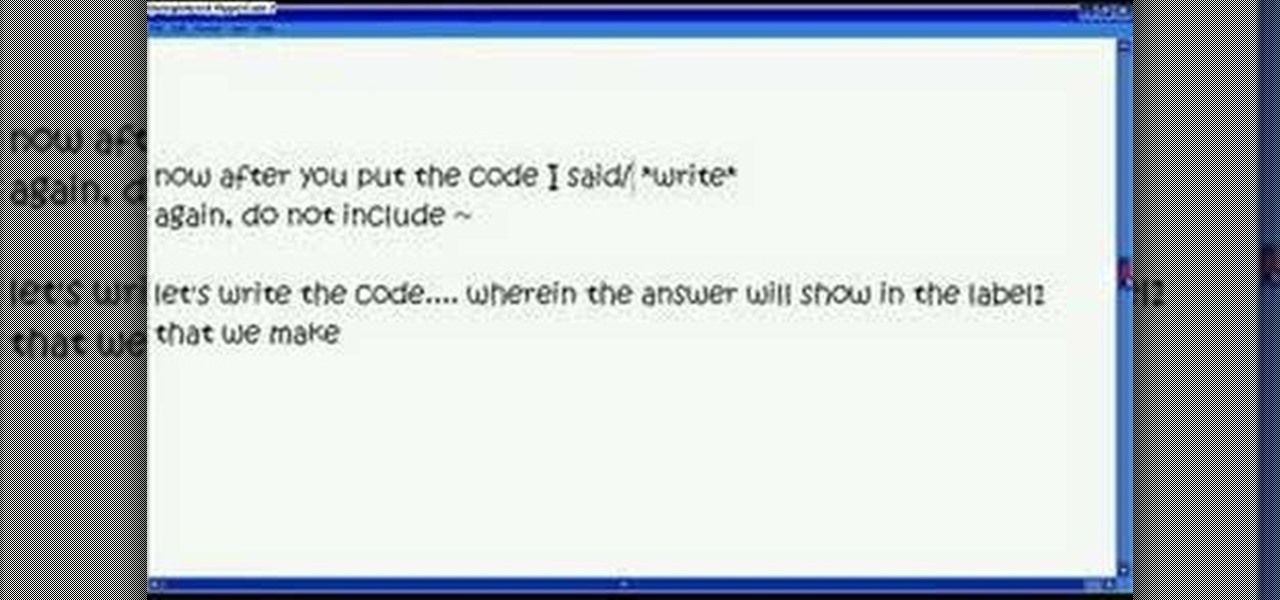
In this video, we learn how to use Visual Basic to convert temperature units. To start, make two command buttons. After you have created these, make sure you label them. The first command button should say "celsius to fahrenheit" and the second should say "fahrenheit to celcius". After this, make one text box and one label box. Now you will convert celsius to fahrenheit using the formula "F=(9/5*C) + 32". and you will be able to use this to convert temperature units. Save this and use it for ...

In this video tutorial, you'll learn how to use keyboard shortcuts within Google Gmail to speed up common and repetitive tasks. For all the details, including step-by-step instructions, and to get using these useful key commands yourself, take a look.

In this tutorial, we learn key commands that will allow you to sleep, restart or shutdown an Apple computer running the Mac OS X operating system. They're easy to use and remember and this video presents a complete guide. For more information, including a full demonstration and detailed, step-by-step instructions, watch this helpful home-computing how-to.

In this tutorial, we learn how to set up and use custom key commands on an Apple computer running the Mac OS X operating sytem. It's an easy process and this video presents a complete guide. For more information, including a full demonstration and detailed, step-by-step instructions, watch this helpful home-computing how-to.

Take an animation created in one project and import it into a different project! There are several ways to accomplish this - you can make a new layer or just use the copy command. However, an easier method is to set up your libraries in Adobe Flash CS5 to be shared.

The Image Size command lets you scale an image on screen or in print. Whether you're new to Adobe's popular raster graphics editing software or a seasoned professional just looking to better acquaint yourself with the program and its various features and filters, you're sure to be well served by this video tutorial. For more information, including detailed, step-by-step instructions, watch this free video guide.

If you have a new Hyundai that is equipped with a head-unit GPS, check out this tutorial. In this video, you will learn how to use Hyundai's 2010 GPS model. This GPS is touchscreen and responds quickly and easily to your commands. So, follow along and get started on your destintion.

See a number of useful key commands that will allow you to quickly resize and adjust the relative hardness of your brushes in Adobe Photoshop CS4. Whether you're new to Adobe's popular graphic editing program or a seasoned design professional looking to better acquaint yourself with the new features and functions of this particular iteration of the application, you're sure to benefit from this free software tutorial. For more information, watch this designer's guide.

Addicted to keyboard shortcuts? Interested in adding a few more to your arsenal? This home computing how-to from the folks at CNET TV demonstrates a number of intermediate- and advanced-level shortcuts sure to speed up your Microsoft Windows Vista workflow. For the specifics, and to get started using these useful Windows key commands yourself, watch this handy how-to.

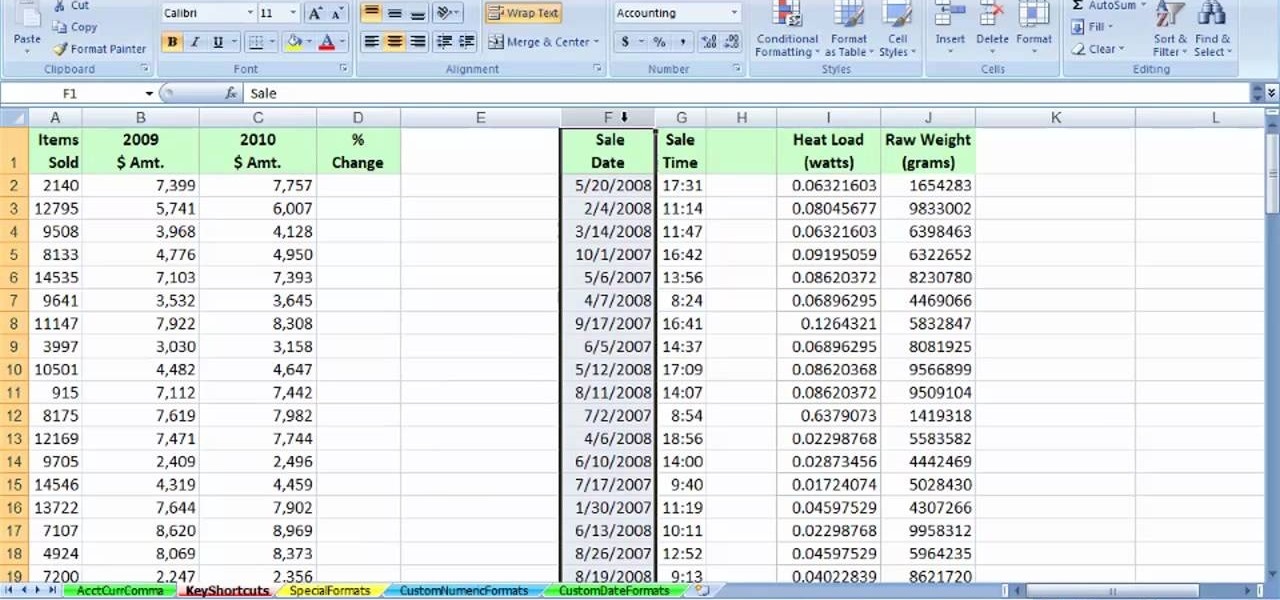
Speed up your MS Excel workflow with these handy formatting key commands. Whether you're new to Microsoft's popular digital spreadsheet application or a seasoned business professional just looking to better acquaint yourself with this particular iteration of the program, you're sure to be well served by this video tutorial. For more information, including step-by-step instructions, watch this free video guide.

Speed up your Nuke 5 workflow with the handy key commands dmeonstrated in this clip. Whether you're new to the Foundry's popular node-based compositing application or a seasoned post-production professional just looking to better acquaint yourself with Nuke 5's new features, you're sure to be well served by this video tutorial. For more information, including a detailed overview, watch this free video guide.

This video teaches you how to change your computer's account password using the DOS command prompt. The first step is to get to the command prompt, you can do this simply by clicking run in the start menu and typing "cmd." You next type "net user" which will show you all of the user accounts on the computer. Choose the one you would like to change the password for and type "net user (account name)." It will then ask you for a new password, you may type anything you like here keeping in mind t...

Watch this video to learn a simple cheat that will make your paper longer. Good trick to know when you are in a crunch and need to stretch your class paper. You will need to use your existing term paper and either Microsoft Word or Open Office to use the Find&Replace command. Here's some forums you can post anonymously with other like-minded, less scrupulous people: http://academicdishonesty.net

This Photoshop CS3 for beginners tutorial introduces new Photoshop users to the rectangular marquee tool, the fill command and working with text. You will learn how to create a "senior pic" type graphic using some simple text and basic shapes created with the rectangular marquee tool in Photoshop CS3.

Have you ever wanted to take a screenshot of your desktop to use in a presentation or to send to a coworker? In this video tutorial, Mac Genius Joy will show you how to take a picture of all, or part, of your screen with the Mac OS X key commands. For more, and to learn how to take your own screenshots in Mac OS X, watch this video tutorial.

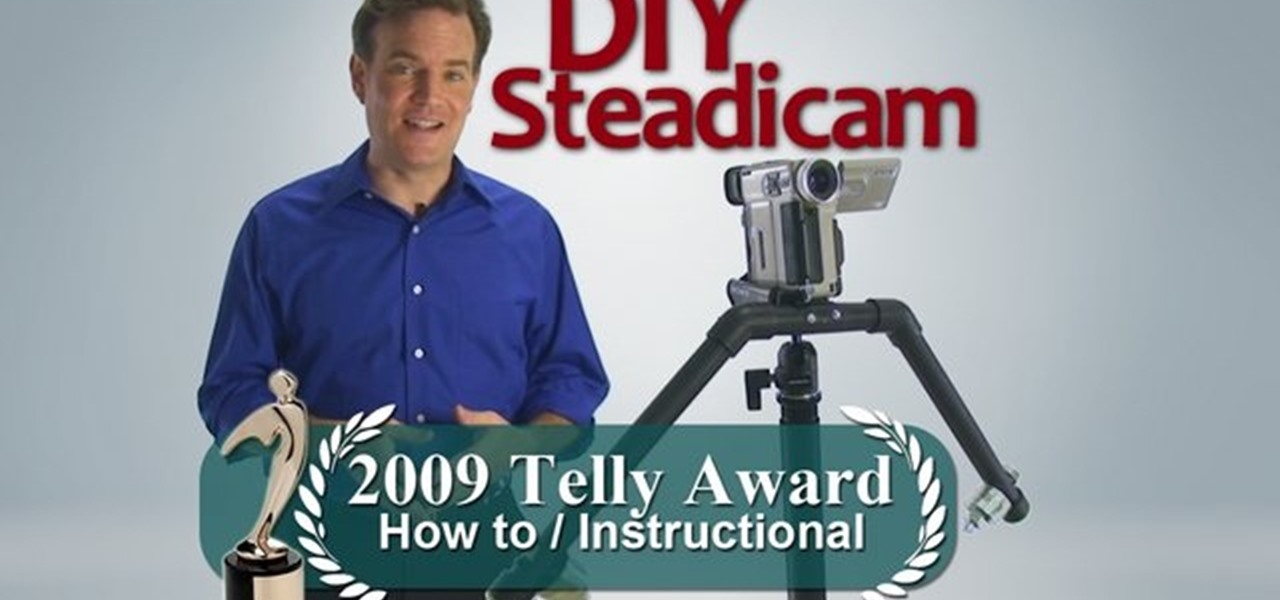
Garret Brown's original Steadicam® is an icon that revolutionized filmmaking. Being the first and the best, it naturally and justifiably commands a premium price. It is for this reason that homemade DIY Flying Camera Supports have been around since at least 1977, just one short year after Mr. Brown's invention. With this tradition in mind, learn the two fundamental principles behind the Steadicam and how to build your own Flying Camera Support by watching this video filmmaking tutorial.

Birds can be taught to perform tricks, just like dogs. This video tutorial shows techniques for how instruct a pet cockatiel to follow simple commands. Learn how to train a Cockatiel to do tricks by watching a professional parrot trainer show you step-by-step how he taught his Cockatiel the "How To Flex" trick.

Correctly identifying the underlying technologies that run on a website gives pentesters a considerable advantage when preparing an attack. Whether you're testing out the defenses of a large corporation or playing the latest CTF, figuring out what technologies a site uses is a crucial pen-tester skill.

The next libSSH or OpenSSH exploit may be just around the corner. Keep your SSH service out of Shodan's database before hackers find new ways to bypass the password protecting the server.

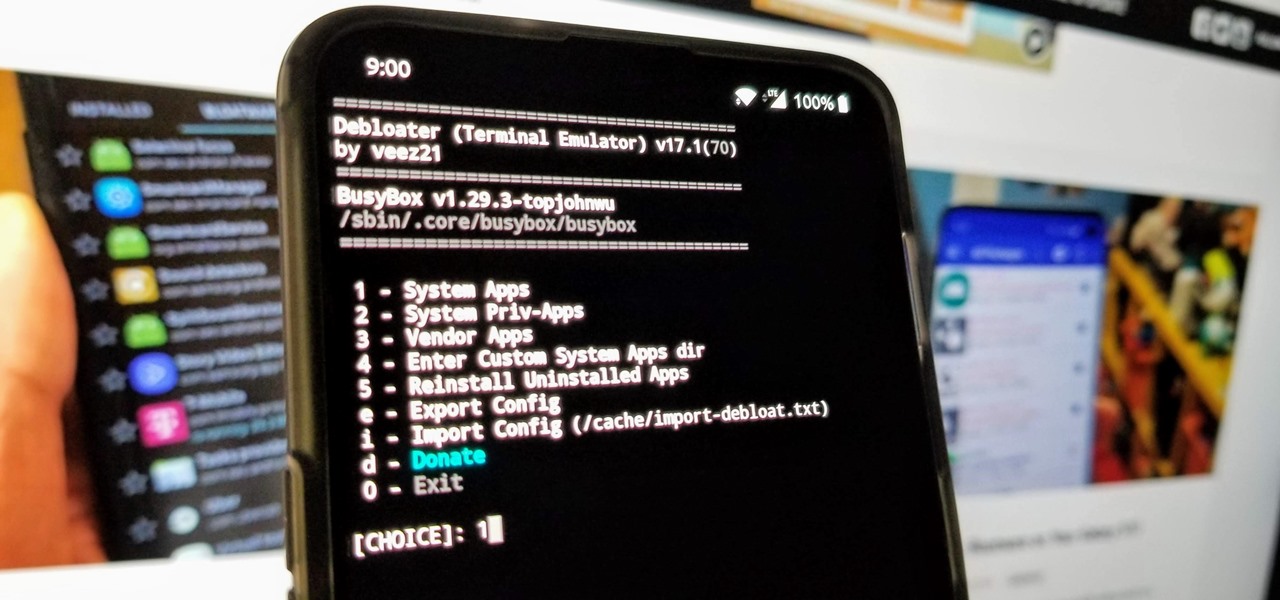
When you get a new phone, the last thing you want to deal with is a ton of preinstalled programs staring back at you. They not only clutter your home screen with apps you'll probably never use, but they're also wasting space on your internal storage and potentially draining battery. To truly uninstall them, you'll need root — but even then, it can be hard to pin down all the apps that should be removed.

When it comes to rooting and modding any Android device, ADB and Fastboot commands will quickly become your two new best friends once you realize the power they have. From unlocking your bootloader to flashing any file you could ever want — if you're serious about the modding and customization game, you'll want to become acquainted with these commands as soon as possible.

Using Siri to perform tasks on your Google Home device was never possible until Apple released Siri Shortcuts in iOS 12. Actually, it wasn't possible until Google added support for Siri Shortcuts for Google Assistant in Nov. 2018. No matter the timing, the important thing here is that you can use Siri to command Google Assistant which, in turn, can command Google Home.

Hacker's are always looking for new ways to exploit systems and exfiltrate passwords, even in hashed form. Sophisticated brute-force attacks powered by high-end GPUs can perform millions of password attempts per second. But Ubuntu and Debian users aren't completely helpless. There are ways to harden the hashed password to better defend against Hashcat attacks.