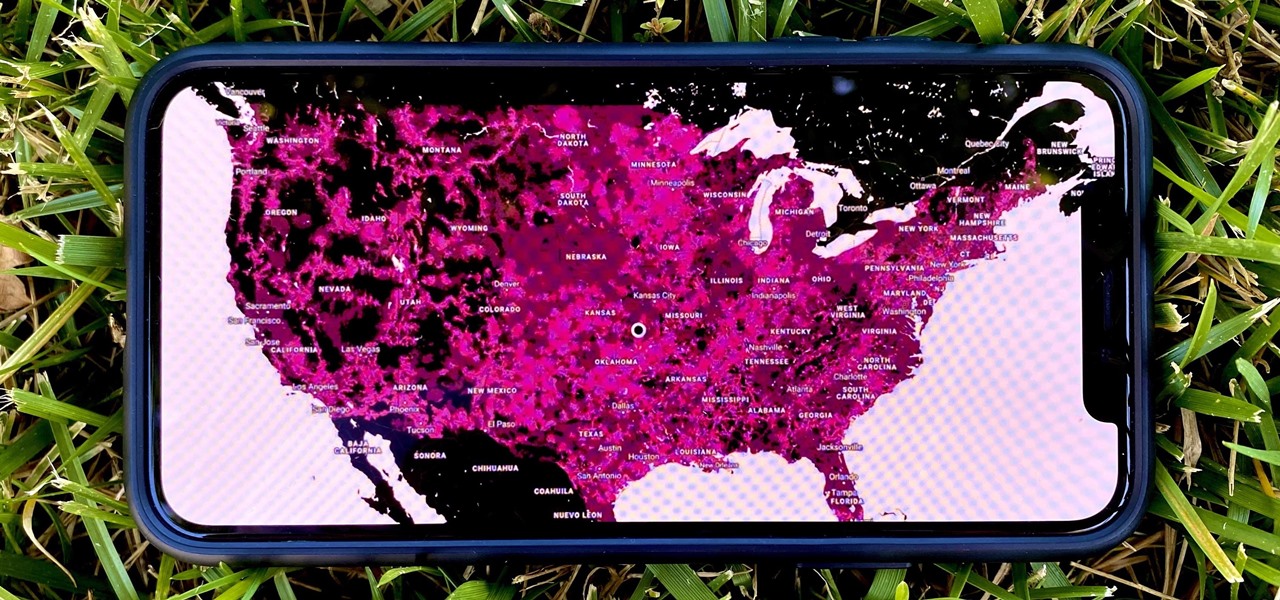
In 2009, 4G LTE networks rolled out in Stockholm and Oslo, replacing 3G as a better upgrade to the mobile data technology that gives us the broadband speeds we have on our mobile devices. Over a decade later, and we have the latest, next-generation wireless network technology among us, 5G, but can you even use it?

After entering into settlement talks with Epic Games over the gaming giant's trademark challenge, Nreal is now ready to open up the floodgates to potential early adopters in the augmented reality space.

Look Around in Apple Maps gives you a high-resolution 3D view of roads, buildings, and other imagery in an interactive 360-degree layout. We haven't had anything like this in Apple Maps since iOS 5 when Google's Street View was incorporated. Now, in iOS 13, seven years later, we have street-level views again, only better. But Look Around isn't available everywhere yet.

On Thursday, yet another piece of the Magic Leap puzzle fell into place at Twilio's Signal developer and customer conference in San Francisco.

Hacking Wi-Fi is a lot easier than most people think, but the ways of doing so are clustered around a few common techniques most hackers use. With a few simple actions, the average user can go a long way toward defending against the five most common methods of Wi-Fi hacking, which include password cracking, social engineering, WPS attacks, remote access, and rogue access points.

While Vuzix is beefing up the processing power of its next-generation smartglasses with the Qualcomm Snapdragon XR1, the company will also give its devices an upgraded display engine.

Confirming a previous report from last week, Qualcomm announced its Snapdragon X1 platform designed for augmented and virtual reality devices during an event at the Augmented World Expo in Santa Clara on Tuesday, with Meta and Vuzix among the first manufacturers to adopt it.

Security-minded users can reduce the risk of phishing by enabling Advanced Protection on important Google accounts, requiring a U2F security token to log in. Using these keys isn't intuitive on most popular smartphone platforms, and you can find yourself locked out if you don't plan ahead. You'll need to learn and practice using U2F keys on your device before enabling this layer of security.

Digital imaging company OmniVision Technologies and the Hong Kong Applied Science and Technology Research Institute Company Limited (ASTRI) entered the CES fray this week with a new reference design for an augmented reality headset capable of 60 degrees field of view (FoV).

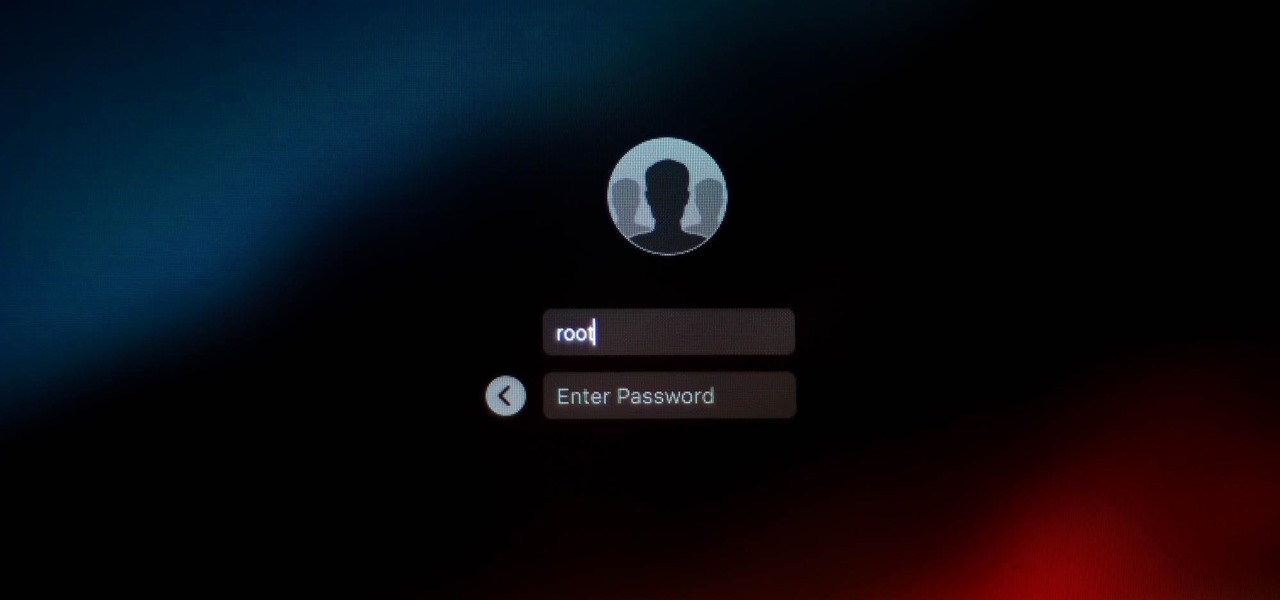
It looks like there is a fatal flaw in the current macOS High Sierra 10.13.1, even straight from the login menu when you first start up the computer. This severe vulnerability lets hackers — or anyone with malicious intentions — do anything they want as root users as long as they have physical access to the computer.

The auto industry continues to shift into high gear to lay the groundwork for driverless cars with an electric vehicle (EV) emphasis.

Modern warfare takes on a more literal translation with the advent of new augmented reality displays revealed recently by the US Army to improve soldiers' situational awareness on the battlefield.

A new survey shows that the majority of companies have an interest in using augmented reality, though adoption remains low. Meanwhile, two companies with support roles in the augmented reality industry are seeing positive financial results.

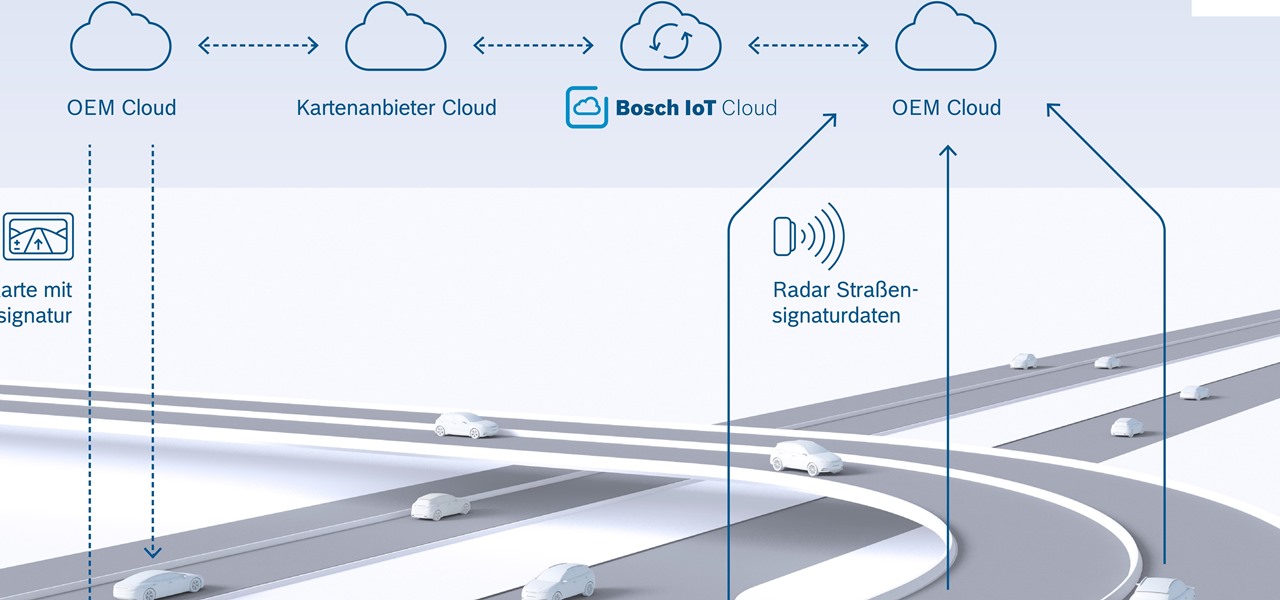
New "radar road signature" technology from Bosch will be used to create maps for high-accuracy self driving. The new map is the first to use radar signals for a localization layer.

Marketing and healthcare, two of the leading industries in the adoption of augmented reality, continue to demonstrate applications for the technology in their businesses. Meanwhile, improvements to augmented reality devices are just around the corner with new developments from two display makers.

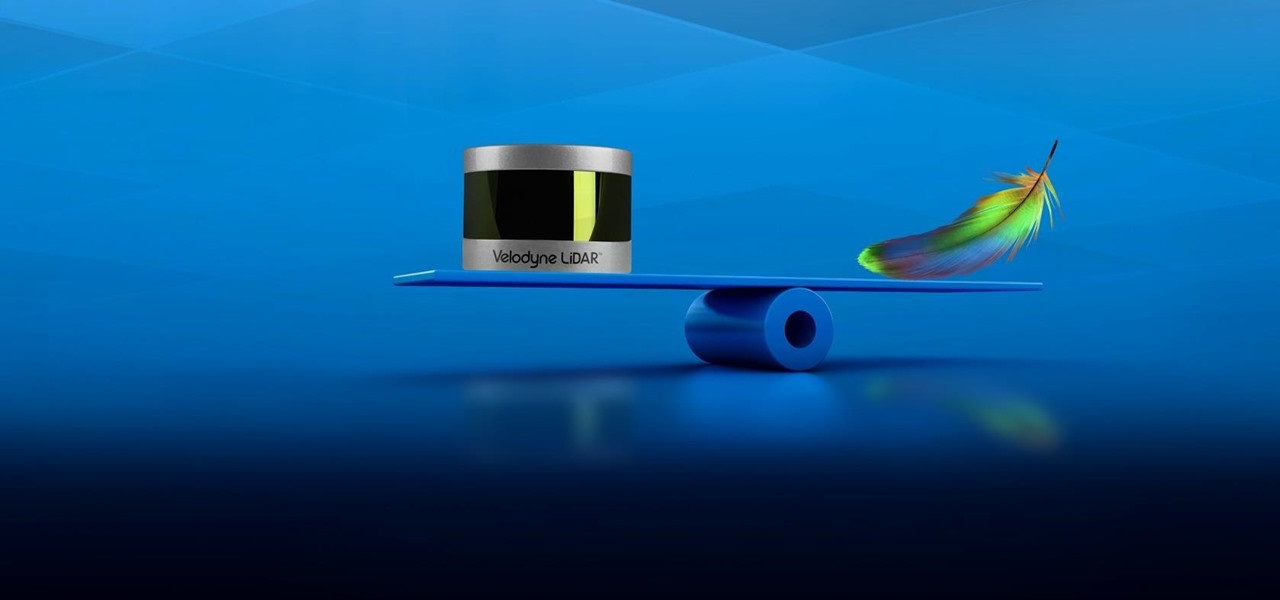
Velodyne wants to set the standard for the driverless industry when it comes to LiDAR. To do that, the Silicon Valley-based team just announced its next step — create a low-cost, fixed-laser sensor that can be embedded into a wide range of automotive and autonomous vehicles. That next step is named the Velarray. A sturdy, compact, and affordable LiDAR laser.

The LG V20 went on sale on September 29, 2016, and is the second flagship phone in the V series to be released by LG. Both the V20 and its predecessor, the V10, have been audio-oriented phones from the start, but the V20 has a much nicer Hi-Fi Quad 32-Bit DAC, which makes the output audio from the 3.5 mm headphone jack sound amazing. It's loud, it's crisp, it's full, and everything from the higher frequencies to the lower ones can be heard.

Logan's Run is one of my favorite movies of all time. The dialog is cheesy, the set design and special effects are wonky, and the main villain looks like he was conceived and built by an eighth grader in shop class—oh, and his name is Box.

The Null Byte community is all about learning white hat hacking skills. In part, this is because I believe that hacking skills will become the most valuable and important skill set of the 21st century.

Welcome back, my tenderfoot hackers! One key area on the minds of all hackers is how to evade security devices such as an intrusion detection system (IDS) or antivirus (AV) software. This is not an issue if you create your own zero-day exploit, or capture someone else's zero-day. However, if you are using someone else's exploit or payload, such as one from Metasploit or Exploit-DB, the security devices are likely to detect it and spoil all your fun.

For every contact photo you add, Android keeps two copies. The first is stored at a 720p resolution, and this is used for high-definition imagery when you're looking at a full-sized contact card. But the second image is only 96 pixels by 96 pixels, and this is used for all thumbnails throughout the operating system.

Bacon isn't hard to cook on the stovetop, but every cook who's been hit by splattering fat knows it's not the most pleasant kitchen task to tackle. If you're cooking bacon for a lot of people, you can avoid this by cooking it in the oven on a roasting rack, DIY or otherwise.

We've all been there: facing a lengthy, complex word that ignores the phonics we were taught in elementary school, unsure of not only its pronunciation, but also its meaning. These words, from autochthonous to esquamulose, are both terrifying and impressive. After all, if someone knows how to use them—and even say them—they must be quite smart. Yet before you begin stuffing every email and presentation with verbose prose, you might want to reconsider what others perceive to be intelligent.

Being in a band, I exposed myself to years of extremely high volumes, so I can't hear as well as I once did. I'm not concerned about going deaf or anything, but I tend to have the volume raised to the max, beyond the "high volume" warning, whenever listening to music on my OnePlus One with headphones.

Pop princess Ariana Grande has had quite the year. She released her second consecutive number-one album and is on the cusp of her first headlining tour in the U.S. early next year.

Pies and soufflés: these are two dishes that can try even the most experienced cook. Berry pies can be especially challenging, since the high water content of cherries, strawberries, blueberries, and blackberries often leads to a big, leaky mess once you cut into your beautiful pie.

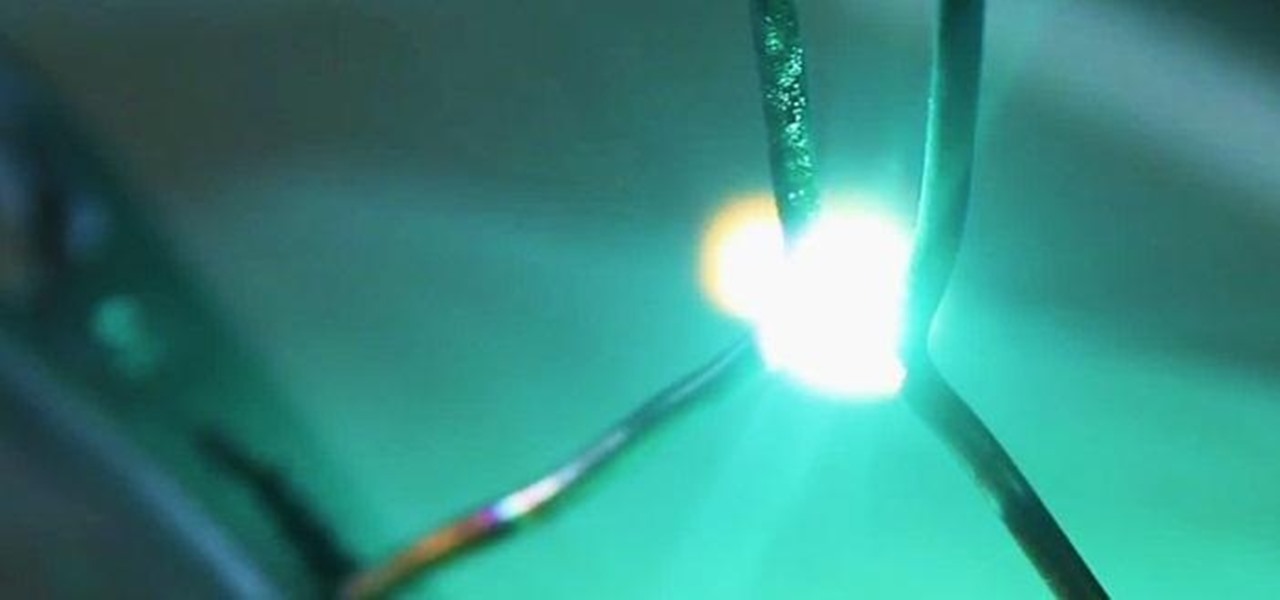
Video: . Dent Repair - Using a Stud Welder Gun

I've been told numerous times that I listen to music way too loud, to the point of potential hearing damage, especially when I have my headphones plugged in. Not only do my friends tell me this, but my Samsung Galaxy S4 likes to nag me as well. Once I pass a certain volume threshold (nine steps) with my headphones, I get that annoying high volume alert. Sorry, my hearing isn't as good as it once was, so let me jam in peace!

We all have our favorite cooking oils, but not everyone knows that they're not all interchangeable. Each type of oil is best for certain jobs, and they all have different smoke points and flavor profiles, which are the two most important criteria in determining which one to use.

While the legality of secretly recording phone calls varies in each country, sometimes it's useful to have audio documentation of conversations you have on your Samsung Galaxy Note 2.

Screenshots are great, but sometimes they don't tell the whole story. You can show off that new app you got or that awesome new live wallpaper, but a screenshot isn't going to get the point across. What exactly am I trying to show you in the screenshot above? You probably have no idea, and that's the point. You can't see the action I'm trying to demonstrate, but in a video you can.

With the microwave oven transformer (M.O.T.) salvaged in a previous project, a simple electrical circuit can be rigged to get high voltage arcs to fly outward and upward along a "V" shaped spark gap.

I'm sure most everyone has some kind of fluorescent light source in their home; those long white tubes that emit a bright white light when turned on, or maybe a few of the CFL power-saver bulbs. These bulbs actually require very little "power" (i.e. a high voltage:almost no current ratio) to emit light. In fact, static electricity is enough to make them flicker. Inside these tubes is a gas, and when electricity flows through that gas, it gets "excited" and produces light.

This is a low ingredient recipe - all you need is about 2 pounds of high quality chocolate and 6-8 cups of sliced and toasted almonds. The trick about making this dessert, though, is all in the technique and getting the almonds into the chocolate. Make a delicious chocolate bark with toasted almonds.

By steeping poblano chilis, sun dried tomatoes and garlic in some high end vodka, you can get a delicious, peppery liquor that does a fantastic job of spicing up Bloody Marys (as well as a variety of other mildly spicy cocktails). Steep for at least 24 hours. Make a poblano chili and garlic infused vodka.

The whole world seems better when you’ve had a full night’s sleep, and if you don’t believe me, you’re JUST FRIGGIN’ WRONG. Studies show that getting enough sleep during nighttime hours can make you less irritable, help you lose weight, and reduce your risk of cancer and other totally bogus-time diseases.

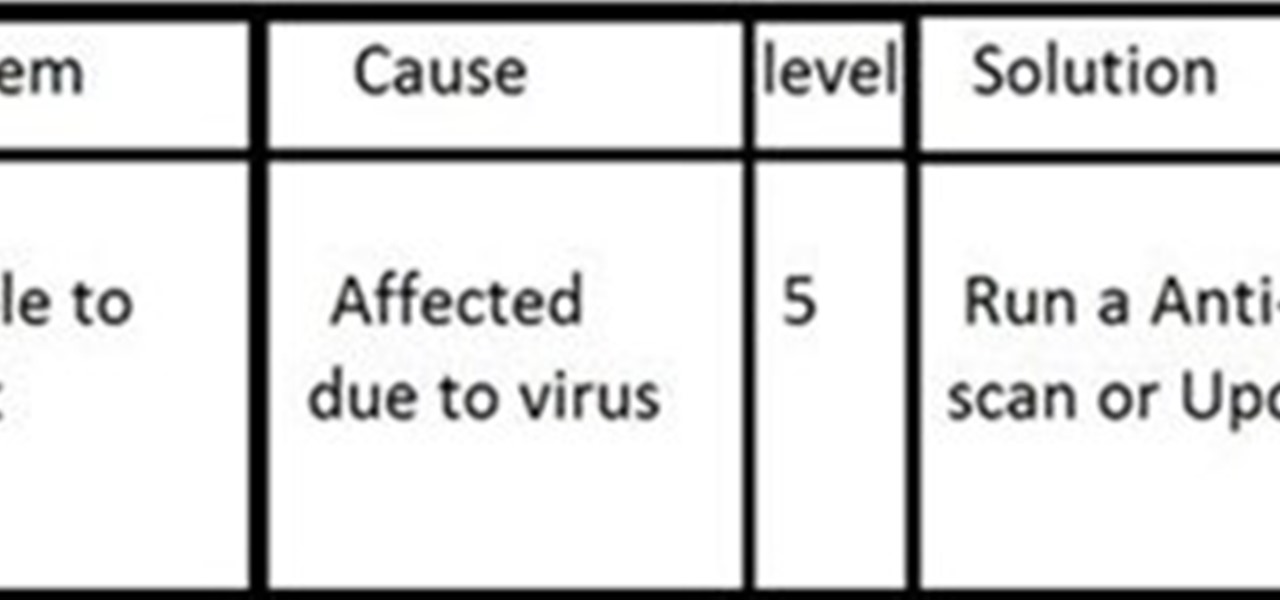
INTRODUCTION The everyday PC user doesn't think much about its PC and problems that can cause critical damage to their data or other stuffs stored on Hard drive and other electronic parts until the problem actually occurs. Once a failure happens, the repairs can be costly and very time-consuming and one also have to sacrifice their data stored on hard drives if the damage is more severe!

This tutorial shows you how to build your own picture frame from scratch. It's a grea tutorial for those interested in saving some money for a high-end frame or for those interested in expanding their woodskills. This tutorial has great insight and tips for making a great looking frame. Sit back and enjoy! Build your own picture frame from scratch.

This is a beauty tutorial from fashion's finest. Get Gisele Bunchen's 40s curls with high fashion tips from the pro's. This is a Modelinia video with expert hair styling advice from pro stylist. You need curls, straight iron and pins. Get sexy Gisele Bunchen's 40's supermodel curls.

imageSynth is plug-in for Adobe Photoshop used for creating seamless textures and for creating high resolution images from low resolution sources. This imageSynth Photoshop plugin tutorial shows you how to use this ultimate organic pattern maker tool! Create seamless textures with imageSynth in Photoshop.