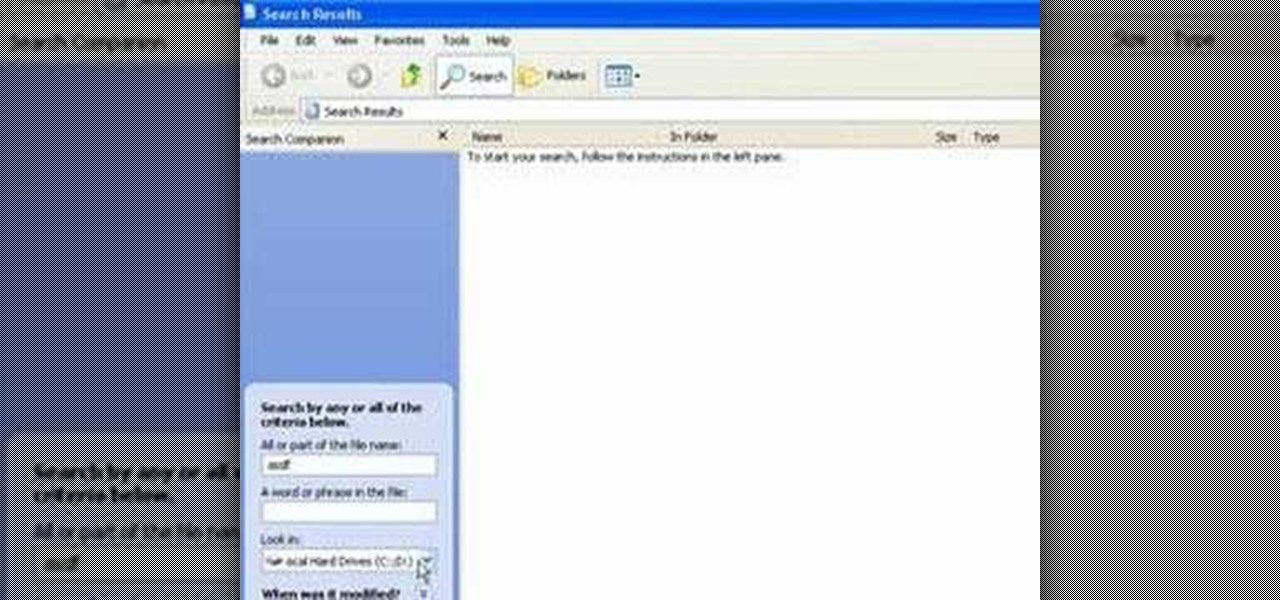
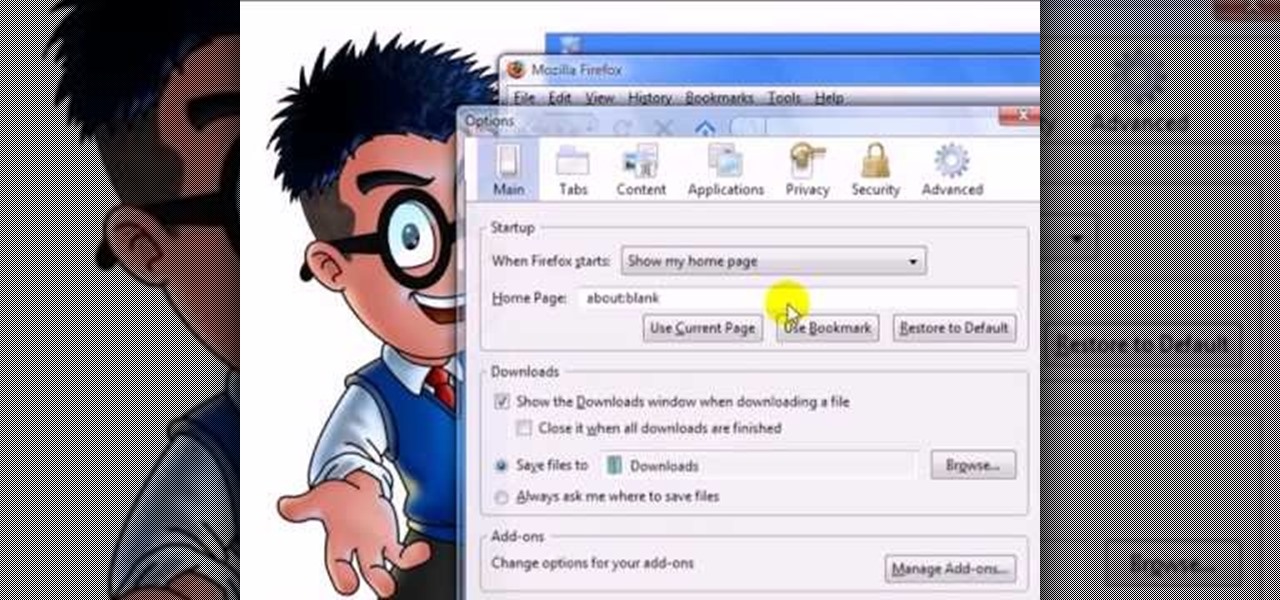
In this video tutorial, viewers learn how to clear their cookies in Mozilla Firefox. Begin by opening the web browser. Then click on Tools from the top menu and select Options. In the Options window, click on the Content tab and deselect "Block pop-up windows". Click OK. Now click on Tools and go to Options once again. Click on the Privacy tab and click on Clear Now under Private Data. Make sure that Cookies and Cache are checked and click OK when finished. This video will benefit those viewe...

In this how-to video, you will learn how to change your start menu text. You will need resource hacker and regedit in order to perform this. First, open resource hacker. Click file and open. Go to 37, and click on 1033. Change 578 to whatever you want the text on the start menu to be. Press compile script. Next, save this file. Now, open regedit and go to software. Go to shell and click modify. Change the value data to the name of your .exe file, which should be saved in the windows folder. N...

In this Electronics video tutorial you will learn how to update your iPhone and iPod Touch firmware 3.0. You will need iTunes 8.2 and the firmware from Deposit Files. Go to the website and download the firmware. This will take some time. Use Firefox browser for the download. Now make sure your device is clean, i.e., it is not jailbroken and connect it to the computer. Then open up iTunes on the device for this hold down ‘power’ and ‘home’ until the device switches off and then powers on. Once...

Keith M. Bower explains the meaning of mean and standard deviation. This educational video gives insight in the basics of statistics. The relations between population mean and sample mean and between population standard deviation and sample standard deviation are explained. The mean gives an idea on the central tendency. Standard deviation gives an idea about how spread out the data are. Keith also explains how these two parameters, the joint sufficient statistics, define a normal distributio...
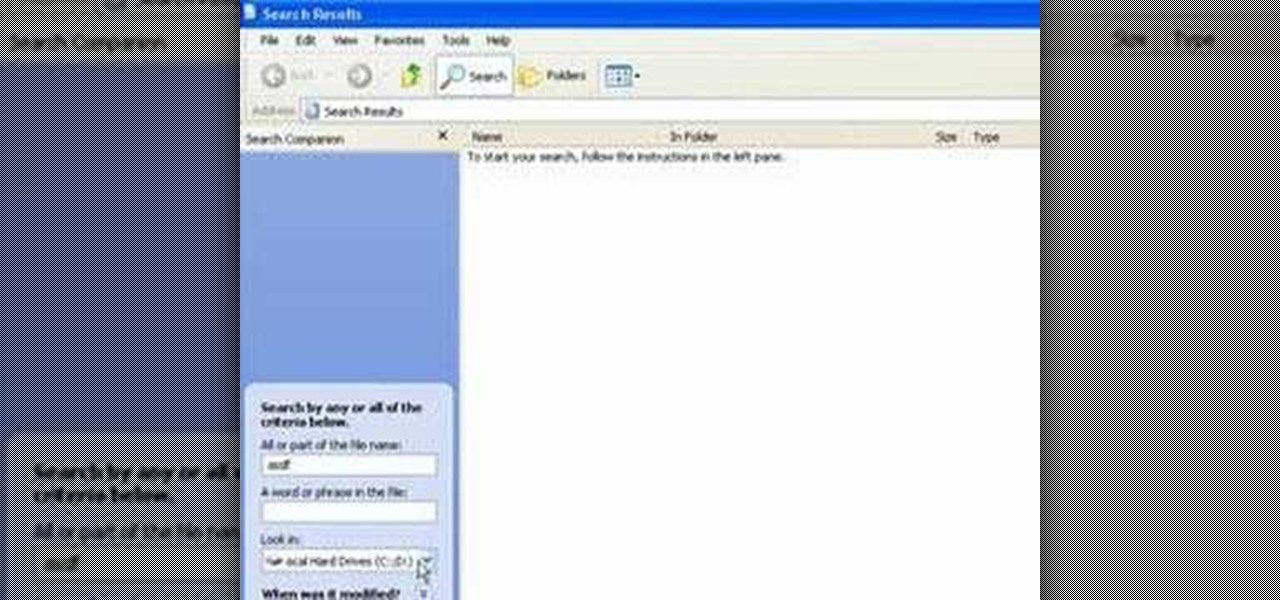
In this video tutorial, Mike shows how to find a missing file in Windows XP and Vista with three different options. In the first option, open Windows Explorer or My Computer. Then open the recycle bin to check for your missing files. If you don't see your file there, close the recycle bin and go to Start and then Search. Look for your file by searching for the file by name to find the location of your missing file. You don't have to know the entire file name to do a search. If that does not w...

This video demonstrates the steps to restore your iPhone or iPod Touch to original factory settings. This is a way to undo or repair any damage to your phone caused by downloading unauthorized files or corrupt files. Be aware that this will delete all the files that are on your device including music, pictures, videos and contacts, so use this method when all others fail. First connect the device to a computer via USB and select the device in iTunes as shown. Go to the device's information pa...

In these PHP basics video the tutor shows how to do form processing. Handling forms in PHP is basically the main functionality of PHP. The forms in HTML take the values of a from and send them to the PHP in real time to do the form processing. In this video the tutor shows how to make a HTML form from the scratch inserting a form into it with some fields and buttons. Now he makes the form post a method to a PHP page when you submit it. Now he shows how to make a PHP file from the scratch by w...

With this useful video, you will learn some tips and tricks about how to delete your web browser history, passwords, cookies, also cache form data and temporary internet files.

Look at the Main Menu on our screen. If the Icons on the screen do not respond to your commands, it means that the system is corrupted. To fix this problem, hold and press down the Power and Menu button at the same time for about 6-8 seconds or until you see a black and white Apple logo right on the middle of the screen; after the icons disappear. This means that your system is rebooting without losing any of your original data. This ensures the system functioning properly again as soon as yo...

This video tutorial shows you how to scan an image in the Runtime GetDataBack software for NTFS. The image was made in the tutorial for RAID Reconstructor when recreating a RAID 0. Why do you need to scan an image? For data recovery that you recreated with RAID Reconstructor. An image is the exact same thing as a hard drive, except that it's in a file format. So, backup your computer's drive, with this video to help, using GetDataBack.

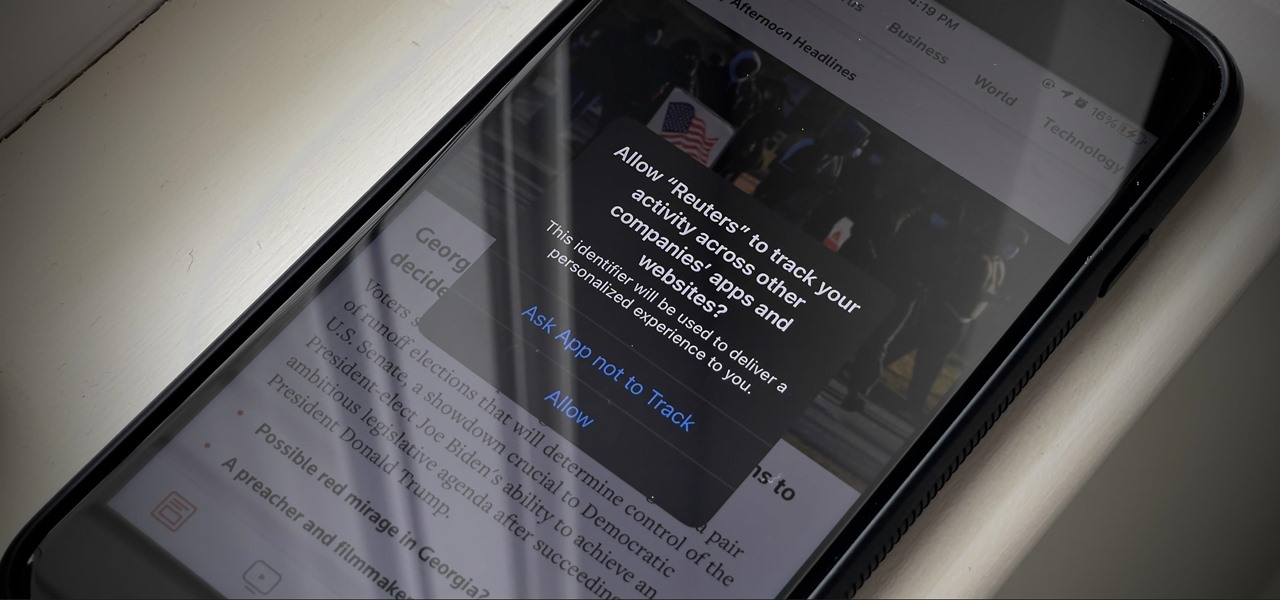
If you're like me, you're not too keen on being tracked. So when an app asks you if it can track your iPhone activity across other programs and websites for ads or data brokers, the answer is pretty much always "no." If you're tired of choosing "Ask App Not to Track" over and over again, there is a way to stop apps from even being able to ask in the first place.

Many of us choose to use an iPhone — as well as other devices in the Apple ecosystem — because of the company's dedication to user privacy and security. If you need more proof of that commitment, look no further than iOS 14.5, released April 26, which adds new tools to protect our data while browsing the web and more control over the data installed apps collect on us.

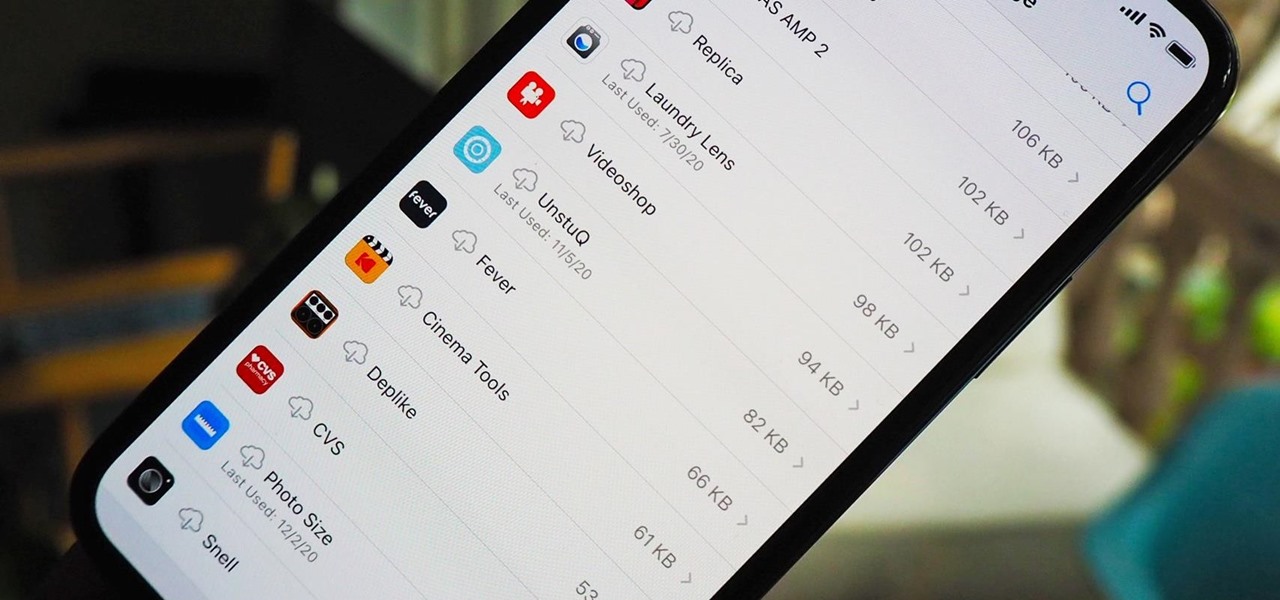
Since iOS 11, your iPhone has been capable of offloading hardly used apps to free up storage space for more useful data. But offloading only gets rid of the app's binary, meaning its documents and data are stored on your device in case you reinstall the app. That can take up a lot of space itself, so it's good to periodically review files for offloaded apps and purge the content you no longer need.

The next big phase of iOS 14 has started with the release of the iOS 14.4 beta. Right now, the developer-only beta features only one known item. Apple introduced the ability to scan App Clip Codes in iOS 14.3 with the Code Scanner control, and now in iOS 14.4, you can launch a local App Clip experience via Camera, NFC, Safari Smart App Banner, or iMessage.

Fresh software updates can be amazing or a nightmare, but they're mostly the former since new and updated features can give your iPhone improved functionality. There are over 200 benefits in iOS 14 alone, and hopping on the iOS 14.2 beta includes new emojis and fresh wallpapers. For the longest time, however, being away from Wi-Fi meant no update for you. That is, until now, thanks to 5G.

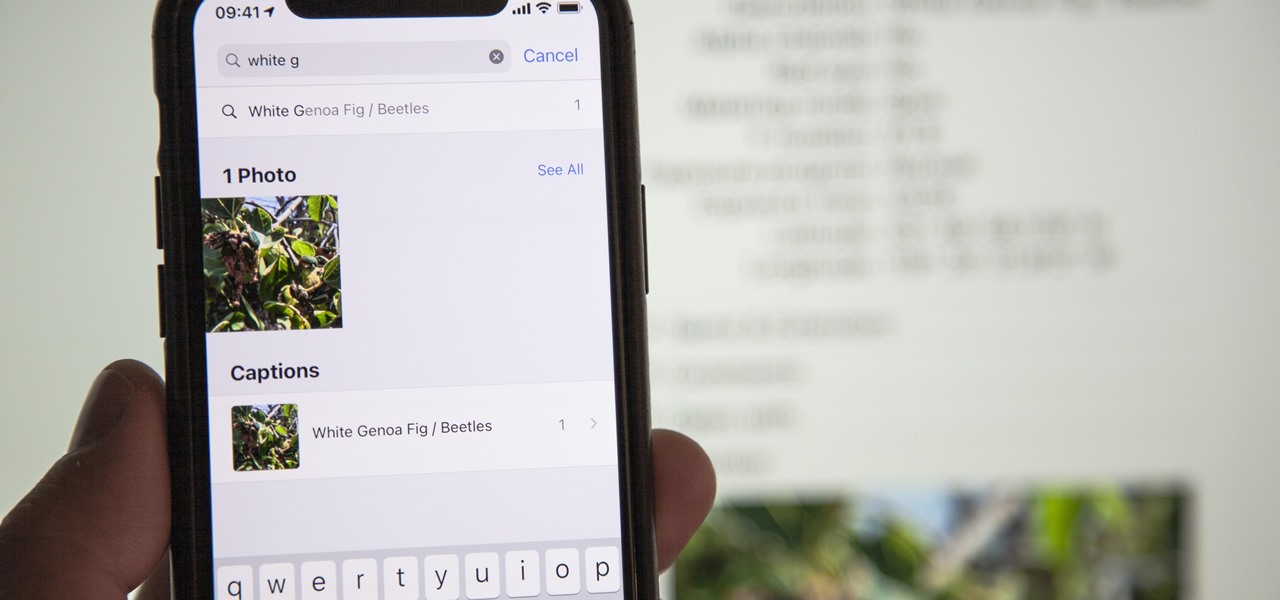
If you've been an iPhone user for quite some time, you probably have quite a bit of photos and videos in iCloud or on your device. Unless you know the date, location, or event, it can be pretty hard to find a specific memory. Even with intelligent search suggestions, AI-created categories, and multi-keyword filters, you still may not be able to find what you want. The new iOS 14 update changes that.

We're living in a world that runs on Big Data. As the driving force behind everything from self-driving cars and Google algorithms to the latest medical technology and financial platforms, massive sets of increasingly complex data lie at the heart of today's most exciting and important innovations.

Anything from work or a missed flight to a worldwide pandemic (COVID-19, anyone?) can make it difficult or nearly impossible to see your loved ones. You can make phone calls or send iMessage, text, or email messages, but nothing compares to seeing family and friends right in front of you. That's where FaceTime comes in.

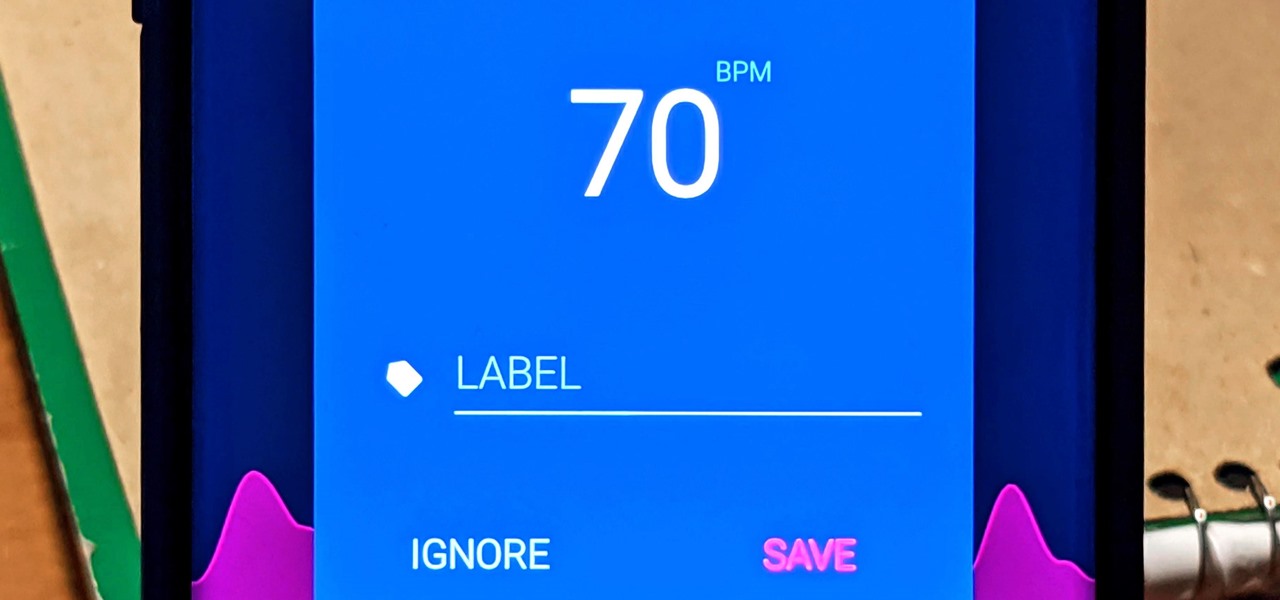
With the rise of smartwatches and wearables, you'd almost expect to need one to get a heart rate reading. While these devices can be helpful, not everyone has or wants to wear a gadget all the time to track their BPM. Luckily, when you combine Google Fit with a popular third-party heart rate measuring app, it will make things easy for you.

When Apple acquired the popular Workflow app in 2017, many were worried that it would either get replaced with something much worse, or just disappear entirely. Thankfully, Apple put these concerns to rest with the launch of Shortcuts. In iOS 13, Shortcuts is becoming more powerful than ever, providing functionality on the iPhone that the original Workflow team could only dream of.

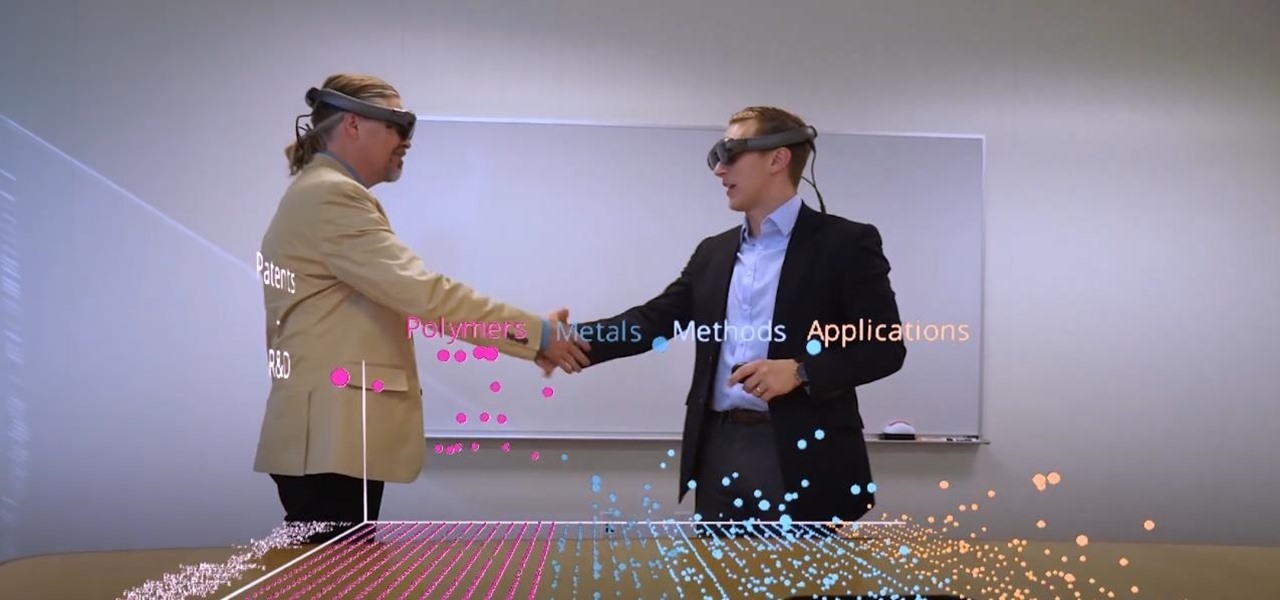
Thanks to the expanding universe of augmented reality tools being made available, increasingly, anybody can liven up sleepy office meetings with immersive computing.

When it comes to the athletic footwear retail game, it's just not enough to just sell shoes anymore.

While the eyes and ears of the iPhone world are singularly fixated on iOS 13 and its suite of over 200 new features, Apple was actively piloting iOS 12.4 in tandem with the big iPhone update, in preparation for the release Apple Card. Today, Apple has finally seeded iOS 12.4 stable, 116 days after its first beta version, and there's still no concrete evidence that Apple Card itself will show its face.

If you find yourself with a roommate hogging limited data bandwidth with video games or discover a neighbor has invited themselves into your Wi-Fi network, you can easily take back control of your internet access. Evil Limiter does this by letting you control the bit rate of any device on the same network as you, allowing you to slow or even stop data transfer speeds for them completely.

For many, the stock version of Android is often considered the epitome of what the operating system should look and feel like by default. It's clean and clear of unwanted extra apps that come pre-installed with the system, provides a fluid and fast user experience, and runs on just about any device that has an unlocked bootloader to install a custom ROM with the stock version ready to go.

Hot on the heels of all the talk about Google's newest Android Q update, known as Android 10, there's a new beta to check out. OnePlus is one of the many partners that can now offer its users a chance to test the latest version early. That means you can install the newest Android Q beta right this second on your OnePlus 6, 6T, or 7 Pro just like Google's Pixel smartphones.

For lack of a better word, a missing iPhone sucks. Not only do you lose a physical device that cost you a small fortune, but there's also the probability you'll never see your precious data again. Hackers and thieves might, just not you. To keep this from ever happening, there are preventative measures you should take, and the sooner you do them the better.

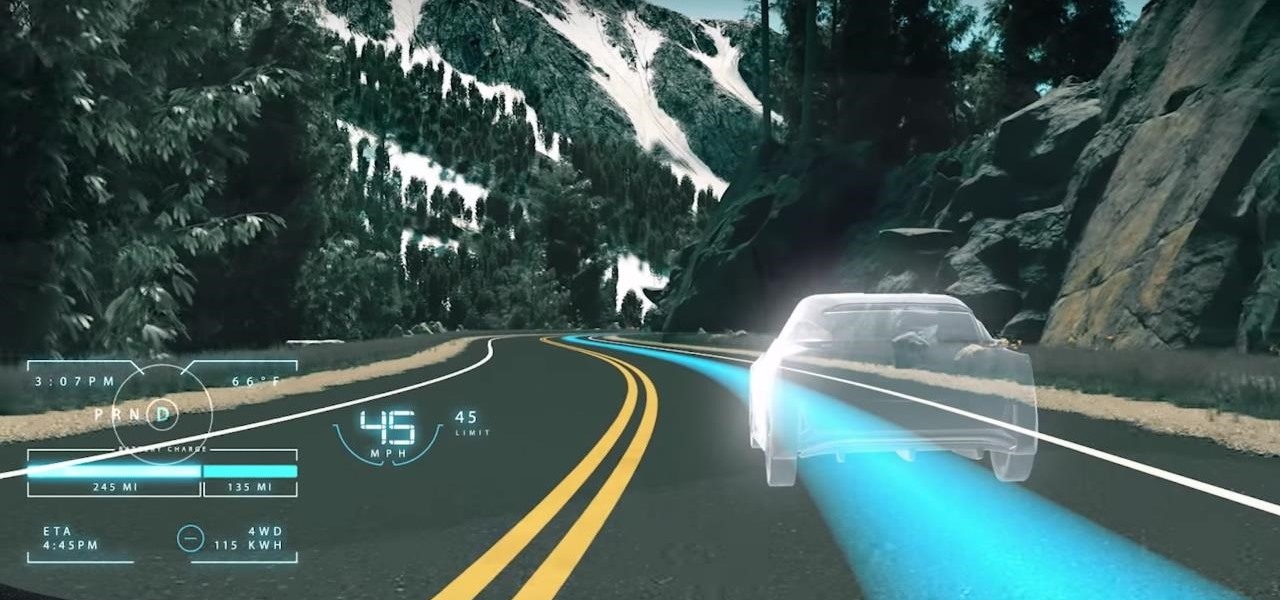
While the technology companies continue to drive forward with autonomous vehicles, Nissan's vision of the future of self-driving automobiles lies in a cooperative experience between human and machine, facilitated by augmented reality.

Whether it's for health reasons or just to look better, many of us want to get in shape. It's a long process that starts with nutrition, and dieting is never easy. Fortunately, there are some great food-tracking apps that will make it a lot easier to become a healthier version of yourself.

For anyone using open source information to conduct an investigation, a balance between powerful tools and privacy controls are a must. Buscador is a virtual machine packed full of useful OSINT tools and streamlined for online research. This program can easily be set up in VirtualBox, and once that's done, we'll walk you through some of the most useful tools included in it.

As it prepares to ship its first product by the end of the summer, Magic Leap has managed to impress yet another high-profile investor in telecommunications giant AT&T.

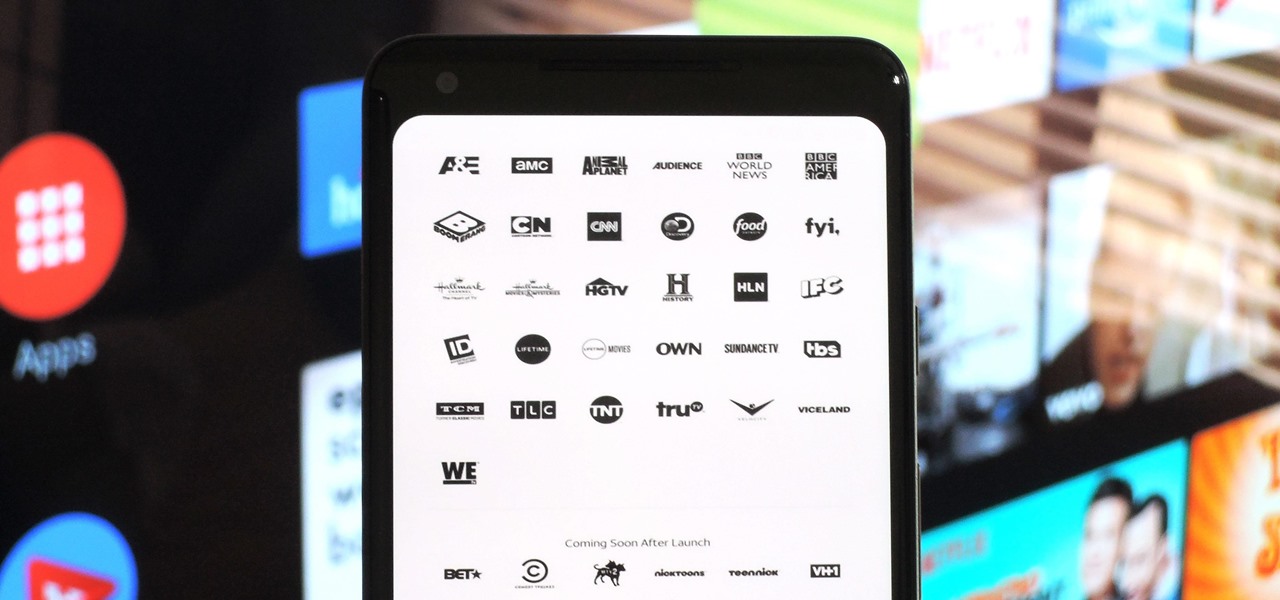
After a district judge approved the $85 billion merger between AT&T and Time Warner, we knew AT&T would be quick to reap the rewards of capturing Time Warner's media properties. Today, we get our first look at this with two cellular plans from AT&T. What makes these plans unique is they include a new cord-cutting service called WatchTV.

When it works, Android's Smart Lock feature is incredible. There's no need to enter your PIN when your phone "knows" it's in your hands — just unlock and go. But Smart Lock, particularly its Trusted Places feature, can be finicky sometimes.

For SQL injection, the next step after performing reconnaissance and gathering information about a database is launching an attack. But something seems off .. in the real world, it's usually not quite as simple as passing in a few fragments of SQL code to an input field and seeing all that glorious data displayed right in the browser. This is when more advanced techniques are needed.

In the arms race between ARKit and ARCore, Google scored a big win with the announcement of its Cloud Anchors shared AR experiences platform at Google I/O on Tuesday.

Know thy enemy — wise words that can be applied to many different situations, including database hacking. It is essential to performing adequate reconnaissance on a system before even thinking about launching an attack — any type of attack — and this is no different for SQL injection.

We know Android 9.0 will have the formal designation of Pie, following Google's age-old tradition of naming their OS after items you'd normally find on a dessert menu. And thanks to a slew of new features that centers around your overall security, P could also stand for Privacy.

Design flaws in many routers can allow hackers to steal Wi-Fi credentials, even if WPA or WPA2 encryption is used with a strong password. While this tactic used to take up to 8 hours, the newer WPS Pixie-Dust attack can crack networks in seconds. To do this, a modern wireless attack framework called Airgeddon is used to find vulnerable networks, and then Bully is used to crack them.

The Play Store hasn't been the most secure place for apps lately. A quick Google search for "Play Store malware" will give you a taste of some of the malicious apps that snuck their way onto Android's official app store. Google is aware of the problem and they're tying to fix it, but their new Play Protect program doesn't have a great track record, so you might want to look elsewhere.

Proxies can be quicker to use than a VPN for specific applications, like web browsers or torrent clients. Both services will hide your true IP address, but a VPN is slowed down because it encrypts all data through a VPN network, while a proxy just acts as a middleman for fetching and returning requests from a server on your behalf. When speed is needed, go proxy.