
How To: Program a PHP forum
This video covers creating and programming a a PHP-based web forum. Topics include basic layout, login and logout, Admin start, creating categories and subcategories, creating topics, and more...


This video covers creating and programming a a PHP-based web forum. Topics include basic layout, login and logout, Admin start, creating categories and subcategories, creating topics, and more...

There are some very powerful tools in CINEMA 4D that you can use very quickly to create some 3D graphic elements. Once you start practicing you'll find it may be easier to create your own reference than to find the "just right" one on the web. So, if you're in need of some barbed wire, for reference or otherwise, check this tutorial out. Of course, it takes quite a bit longer to actually SHOW you how to create the barbed wire (creating the barb, wrapping it around the wire, using MOGRAPH in o...

Since launching its web-based AR platform in 2018, 8th Wall has continued to push the boundaries of what brands can do with AR experiences outside of native apps.

The response to the COVID-19 pandemic means that social distancing has become the new normal. It also means that more Americans are using video conferencing to connect with colleagues working from home or friends and family in quarantine because of the new coronavirus.

One of the most common web application vulnerabilities is LFI, which allows unauthorized access to sensitive files on the server. Such a common weakness is often safeguarded against, and low-hanging fruit can be defended quite easily. But there are always creative ways to get around these defenses, and we'll be looking at two methods to beat the system and successfully pull off LFI.

Information gathering is one of the most important steps in pentesting or hacking, and it can often be more rewarding to run things on the target itself as opposed to just running scripts against it remotely. With an SQL injection, a hacker can compromise a server and, ultimately, upload and run the "unix-privesc-check" script locally in order to further identify possible attack vectors.
Canary tokens are customizable tracking links useful for learning about who is clicking on a link and where it's being shared. Thanks to the way many apps fetch a URL preview for links shared in private chats, canary tokens can even phone home when someone checks a private chat without clicking the link. Canary tokens come in several useful types and can be used even through URL shorteners.

When your iPhone goes missing, it's serious business. Depending on your usage, your whole life might be connected to your iPhone, not the least of which includes debit cards, credit cards, and Apple Pay Cash stored in Apple Pay. While it's nearly impossible for someone to use your money with Apple Pay, it's still a good idea to disable it until you find your iPhone, just in case.

Web 2.0 technology has provided a convenient way to post videos online, keep up with old friends on social media, and even bank from the comfort of your web browser. But when applications are poorly designed or incorrectly configured, certain flaws can be exploited. One such flaw, known as CSRF, allows an attacker to use a legitimate user's session to execute unauthorized requests to the server.

The iOS App Store is a big place, offering over two million applications in total. However, there are actually some apps you can and should install on your iPhone that the iOS App Store doesn't include. And no, these apps do not require any difficult jailbreaking or complicated sideloading techniques — they are really simple to install.

When it comes to your security, you want the best of the best. Why settle for mediocre service with something as valuable as your protection? Malware continues to make its way onto the Play Store, leaving millions of devices vulnerable. You need an app that will shield your devices from both the latest malware threats and threats nearby. And when it comes to antivirus apps, there is only one choice.

The Watch Dogs video game series came out in 2014, enamoring audiences with the idea of a seemingly magical smartphone that could change traffic signals, hack web cameras, and even remotely control forklifts. This may sound like science fiction, but The Sonic uses a customized flavor of Kali Linux to allow you to unleash the power of Kali from any smartphone — all without the need to create a hotspot to control it.

The pictures we upload online are something we tend to think of as self-expression, but these very images can carry code to steal our passwords and data. Profile pictures, avatars, and image galleries are used all over the internet. While all images carry digital picture data — and many also carry metadata regarding camera or photo edits — it's far less expected that an image might actually be hiding malicious code.

The dark web is an intimidating place for a newbie hacker, but it's a powerful tool once you've learned to navigate it safely. To help you out with that, this guide will cover some need-to-know information for traversing the dark corners of the internet while keeping your identity and data safe. (Hint: Using Tor is not enough.)
Canvas fingerprinting is the web's trickiest privacy threat, but it's not impossible to stop. With all the media attention it's gotten lately, it's time we lay out exactly how to detect and prevent this invasive tracking technique.

Welcome back, my novice hackers! There are SOOOO many ways to hack a system or network, which means you need to think creatively in order to be successful.

Now the werewolf and the vampire are no longer threats, but we have heard reports of the giant spider going on drinking binges and webbing up large buildings and even entire towns in the California wine regions as well as in Kentucky bourbon country. It even left a slurred message on our answering machine about plans to step up the devastation this October 31st. We can’t protect each of you from this sticky conclusion, but we can offer a suggestion: build your own giant spider web and you wil...

Google Chrome is finally here, and everyone can benefit from a faster, streamlined web browser. This video will cover all the basic functions and features of the new Chrome we browser, so if you're thinking about switching, this is a must-see.
Microsoft ASP.NET is a free technology that allows programmers to create dynamic web applications. ASP.NET can be used to create anything from small, personal websites through to large, enterprise-class web applications. All you need to get started with ASP.NET is the free .NET Framework and the free Visual Web Developer. In this tutorial, you'll learn how to call your first web service in .NET. In just few minutes you'll be up and running with your own web service in .NET framework in ASP. F...

There are a lot of things on your computer that can reveal information about you when you are surfing the Internet. If you are like me, then you will do anything to maintain your privacy and prevent those little leaks of information from happening. Here's a list of a few of the "threats" that can reveal information about you:

In this video we learn how to alter your IP address. To do this, you will need to go to this website: http://shadysurfing.t35.com. After you go here, you will be directed to the site, click on the left hand side toolbar to display your IP address. Then, go to the web based proxy and search for the site you want to visit. From here, the site will pop up under a different IP address. You can use there at school or at work, whenever you don't want the information for where your IP address has be...
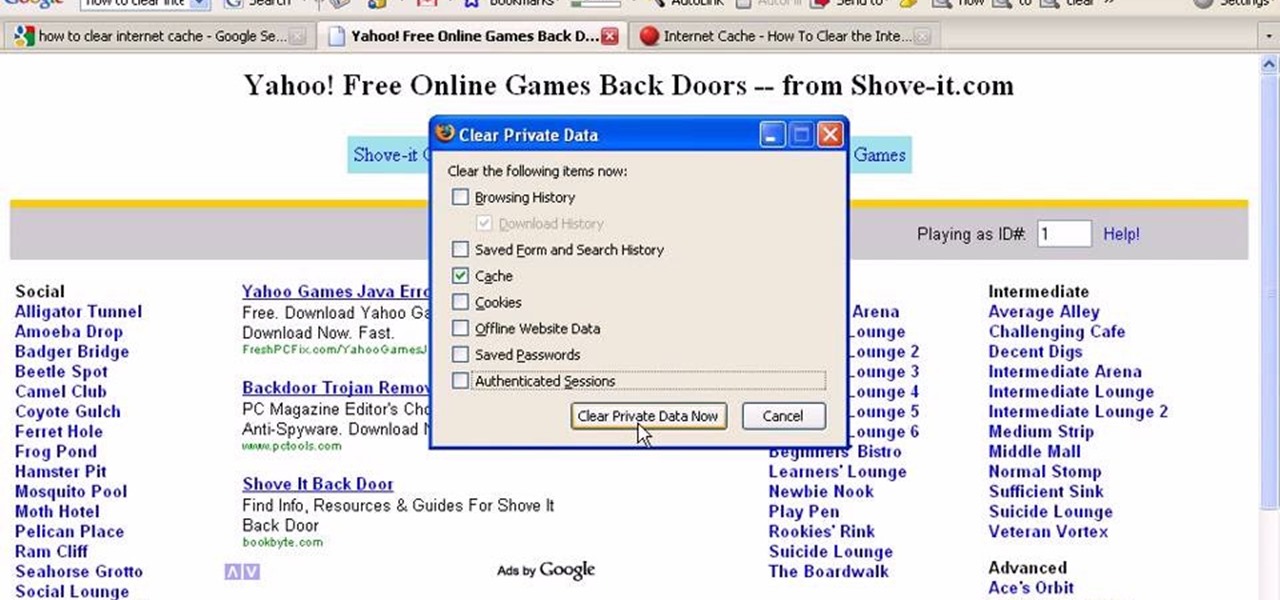
In this tutorial, we learn how to clear your internet cache using Firefox. This only takes a few minutes and can help your browser run much more quickly. First, you will need to log onto Firefox on your computer. After this, you will need to go to the tools menu and then click on 'clear private data'. A new box will pop up, when it does you will need to check the box next to 'cache'. Once you do this, click on the bottom button and then it will load and clear it out. It's just as simple as th...

If you're like us, then after a long day working at the computer, coming home to browse the web on the computer, and then checking our Blackberries and updating our Twitters, you're feeling exhausted but can't seem to wind down enough to fall asleep.
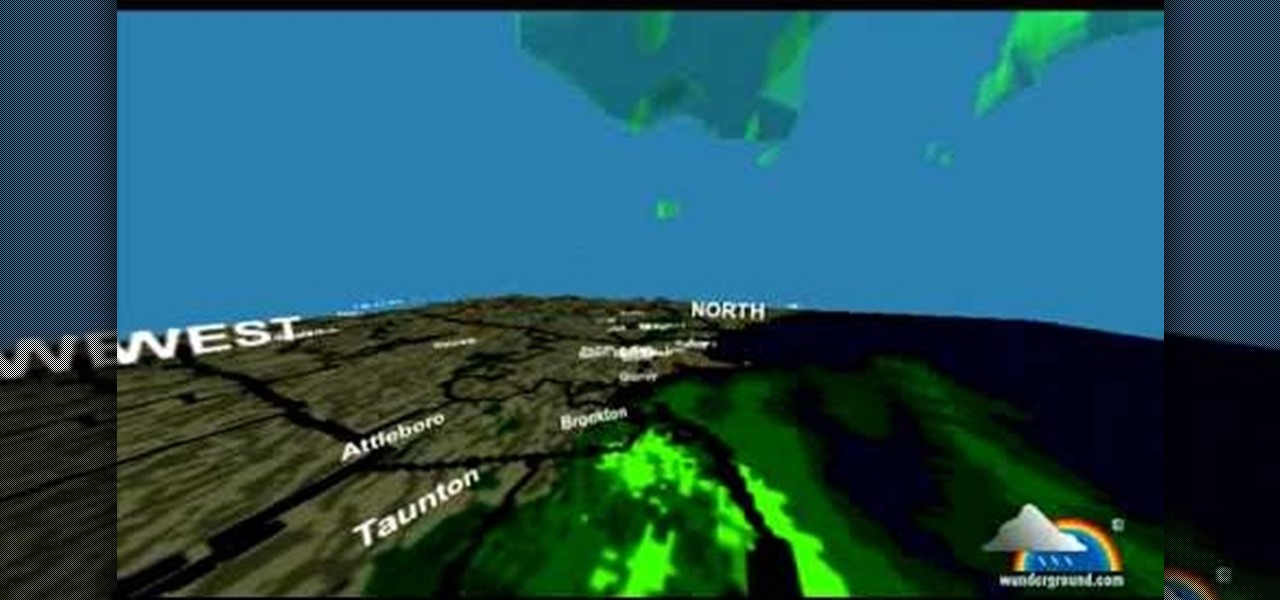
You can see the weather in 3D like First person shooter style by using the site called wunderground. So first go to the site and type whatever you want like Boston, Massachusetts to see the weather of there. You will find a

Sarah teaches us how to do a Dias de las Muerto look for Halloween in this tutorial. First, apply a pure white makeup to the entire face, including the lips. After this, wipe makeup off from around the eyes and draw a circle around them, including the top of the eyebrows down to the top of the cheeks. Next, apply a black flower like shape over the circles you just created. After this, apply a dark green paint to the inside of the eyes, covering everything in them. Next, apply dots at the top ...

If you're curious about how powerful your PC is, the Windows Experience Index can give you a snapshot of its capabilities and help you decide if it's good enough for you. This video will help you understand the basics of what the Windows Experience Index can do in Windows 7.
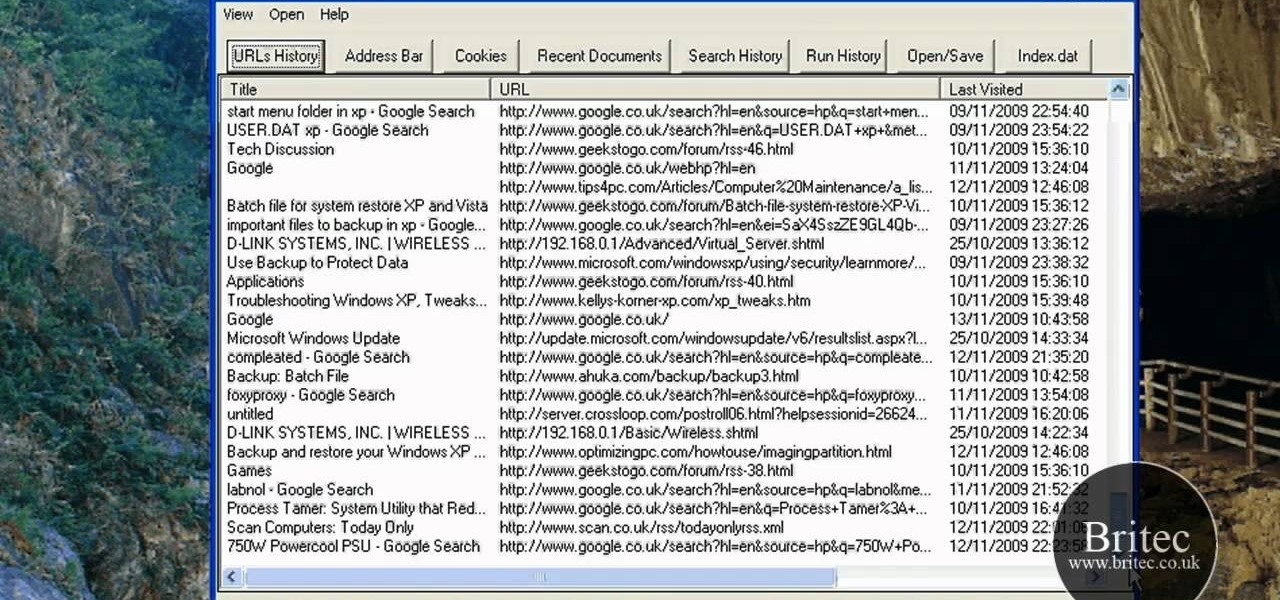
Interested in reading the list of web addresses in an index.dat file on a Microsoft Windows computer? This clip will teach you everything you'll need to know. With WinSpy, it's easy! So easy, in fact, that this home-computing how-to from the folks at Britec can present a complete overview of the process in just over two minutes. For more information, including detailed, step-by-step instructions, take a look.
One thing that irks everyone, customer and seller, is fraud. And if you have an e-store, you're unfortunately going to come across some credit card fraud. There are some ways for you to protect yourself, your company and your customers from credit card fraud, and Volusion has five tips for you. From picking the correct e-commerce provider for your store, watching up for unusual large orders, to how to be proactive and avoid any case of fraud.

In this video tutorial, viewers learn how to get high definition wallpapers using Google. Begin by opening your web browser and go to the Google website. Then click on Images from the top menu and type in "HD wallpapers" in the search bar. Now click on Google Search. In order to get the best picture quality, be sure to select Large images from the Showing drop-down menu. Once you found an image of your liking, click on the image to have it full sized. Now right-click on the images and select ...

In this video tutorial, viewers learn how to clear their cookies in Mozilla Firefox. Begin by opening the web browser. Then click on Tools from the top menu and select Options. In the Options window, click on the Content tab and deselect "Block pop-up windows". Click OK. Now click on Tools and go to Options once again. Click on the Privacy tab and click on Clear Now under Private Data. Make sure that Cookies and Cache are checked and click OK when finished. This video will benefit those viewe...
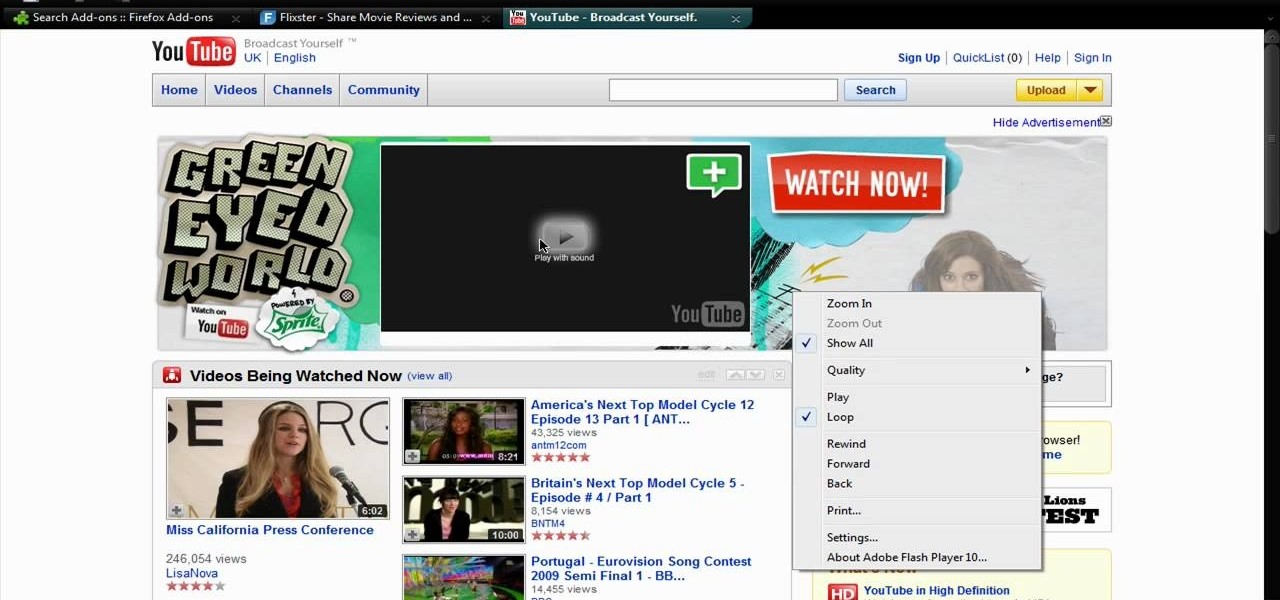
In this video tutorial, viewers learn how to disable ads with the Ad Block Plus add-on in Mozilla Firefox. Begin by going to the Firefox add-on site and search for "ad block". Then click on "Add to Firefox" to install it. Once installed, users will be able to block out any advertisements. Users are able to add a filter subscription. To block an image, right-click on the image and select "Ad Block Image". Users are able to customize their ad block filters to only allow certain advertisements. ...

mIQ? What is it exactly? It's a handy web service that helps you manage your mobile life, with free and easy online access to all of the content and information stored on your mobile device. How does it work? Best Buy has answers. The Best Buy Mobile team explains how simple it is to use mIQ to backup all the data on your cell phone, including messages, photos and contacts.
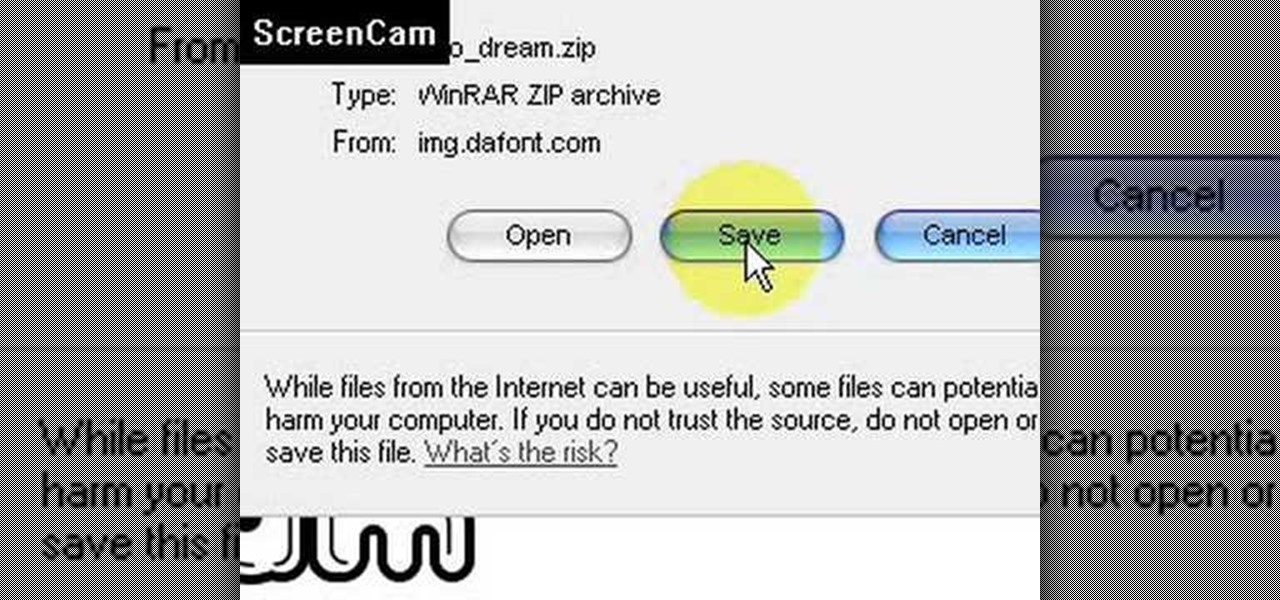
This video is about how to install new fonts in Windows XP. The first step that you will need to do is open your web browser then search for fonts. If you have found the site, just simply click on it. Then the next step is have a browse and look for the font you like. Once you have found the font that suits you best, just simply click the button "download" then save the file in your computer. Once you have saved the file in your computer, simply right-click the file and click on the "extract ...
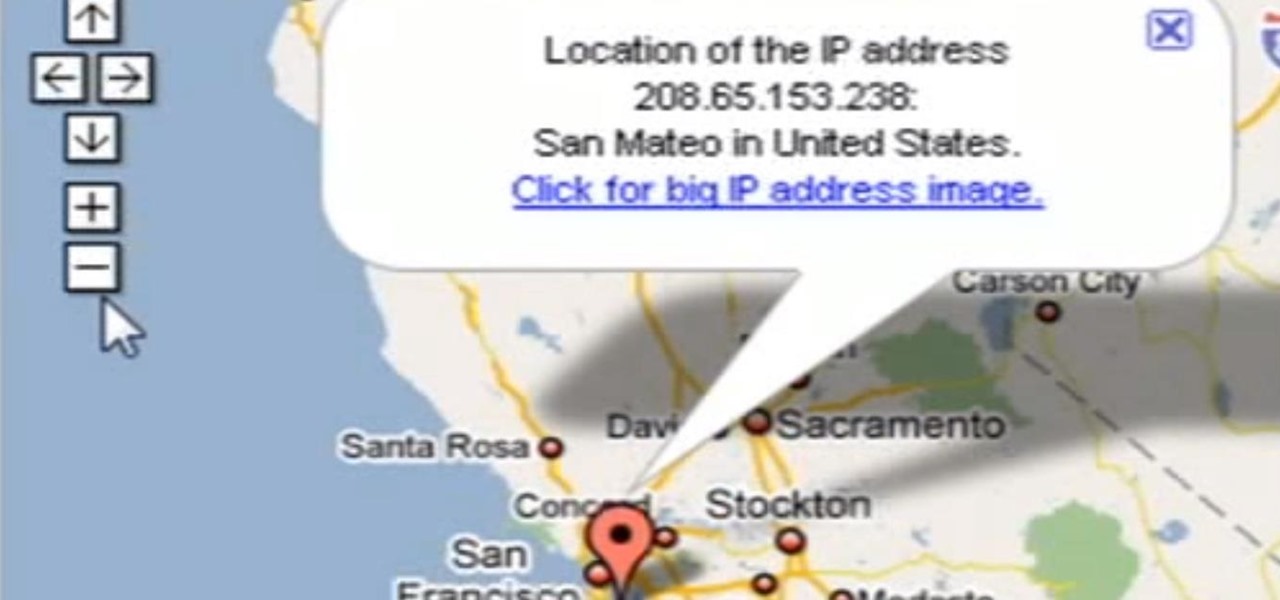
Need help tracing an IP address to a location? Well, Tinkernut has a clear and effect way to help out.
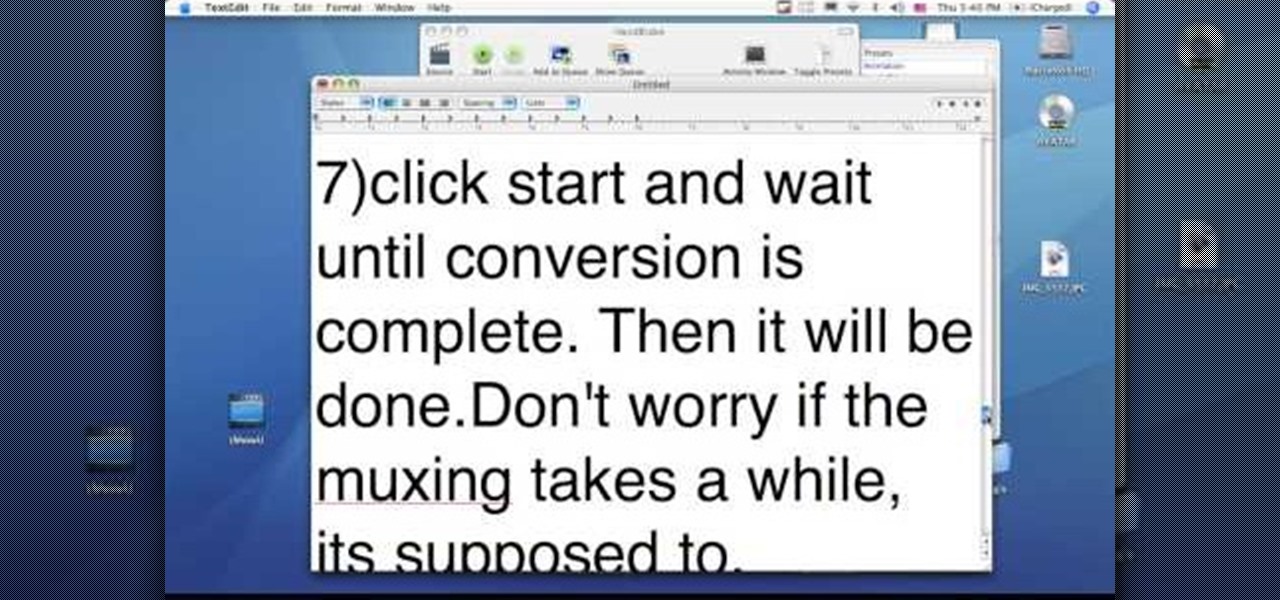
This video tutorial from dproxisback presents how to download and install Handbrake DVD ripping tool.To avoid installation problems, carefully choose application version for each type of computer and operating system.Open your internet browser and visit http://handbrake.fr/?article=download web page.Choose correct version for your type of operating system (MacOS, Linux, Windows).Download and install the application. Run Handbrake once it's installed.Click File-Select Source. Browse for your f...

In order to access your wireless router settings in a Windows PC you need to use a command called ipconfig. The purpose of this command is to find out what your IP is. Go into the command console and use ipconfig to find out what it is but instead of noting down the IP address, we actually have to note down the default gateway values for the task at hand. Now all you need to do is open your web browser and insert the default gateway values from before into the address bar. By doing so you wil...
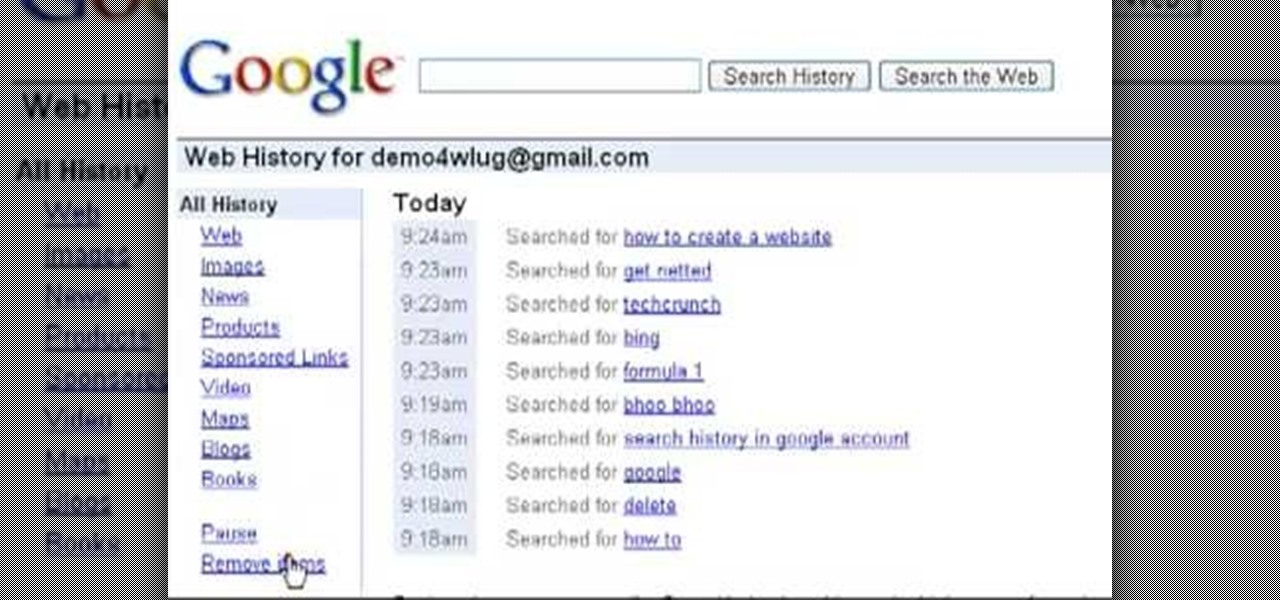
Want to clear the search history from your Google account? Well follow these simple instructions and return your history to the original settings! First log into your Google History Account at google.com/history. Next scroll down and locate "Remove Items" on the left hand side tool bar. Click on this. Next locate "Clear entire Web History" towards the top right of the screen. Then the final step is to click "Clear History". Follow through the tutorial video to get rid of all of the annoying s...

Learn how to delete your old Yahoo account from this video in simple steps. First open your web browser on your computer and go to the Yahoo home page. Now sign into your account using your username and password. Now copy and paste this link "http://edit.yahoo.com/config/ delete_user" in your address bar. Enter your password to confirm the deletion of your account. Finally enter the code to confirm and delete your account.
This video shows you how to easily remove the tracking Cookies from your web browser. Normally, if you use AVG Free, it will detect the tracking cookies but not delete them. This video will show you how to manually remove that tracking cookies without using any software. The first thing you have to do is click Start menu, then search for Run. In the Run windows, paste the following: C:\Users\YOUR PC NAME\AppData\Roaming\Microsoft\Windows\Cookies , and hit Ok button. Delete all the files that ...

Computer forensics expert Steve Burgess gives a highly informative tutorial on how to recover deleted emails in Outlook and Eudora. The most critical factor affecting the recoverability of deleted web-based emails, according to Steve, is whether the PST file, which stores all the emails, has been compressed after the mail was deleted. If this hasn't been done it is possible to hack into this file and recover the deleted email. Text-based emails, like those one creates on programs like Eudora,...