How To: Mix a grasshopper cocktail
Rob "Riki Tiki" Roy and guest co-host Jill Collins bring you another fun dessert drink. You will need creme de menthe, creme de cacao, and milk. Learn how to make this sweet minty grasshopper cocktail.

Rob "Riki Tiki" Roy and guest co-host Jill Collins bring you another fun dessert drink. You will need creme de menthe, creme de cacao, and milk. Learn how to make this sweet minty grasshopper cocktail.

In this how to video, host Tim Carter demonstrates why the size of your overmount stainless steel sink determines whether you should install your sink before or after the countertop is in place. With this home improvement tutorial you can install a stainless steel sink in your house. Just watch this video first.

A laundry chute is a very useful thing to have in your house, especially if you have children. In this tutorial by the DIY network, host Amy Matthews designs and installs a laundry chute. Watch this remodeling how to video and you can install a laundry chute into your own home.

One of the most challenging yoga poses is the handstand. In this yoga how to video, our host, demonstrates the proper preparation for practicing a handstand. If this is your first time doing a handstand have someone else present for extra support.

This yoga bow pose, as our host suggests, is great for soccer athletes. After a long game stretch out those sore upper leg muscles with a this yoga pose. Watch this how to video and learn how to do the bow pose in yoga.

From Mezcal to Blue Agave, learn to choose tequila well with LX.TV host Shira Lazar at LA's L Scorpion. There is a right way to drink tequila, and three types of tequila most don't pay attention to. Learn how to choose a good tequila by watching this video tutorial.

The yoga cactus arm movement helps establish stability underneath the shoulders and upper arm area for inversions and back bends. This yoga how-to video demonstrates how to use the cactus arm movement to transition into cigarette girl action. Cigarette girl action is a name that Kira Ryder, our yoga host, has assigned to a movement she uses in her yoga classes. Watch and learn how to transition from cactus arms into cigarette girl movements in yoga.

Learn a how to become more aware of your tailbone while practicing yin yoga. Watch this Yoga How-to video as our host demonstrates a few poses that focus on tailbone awareness. Becoming more aware of certain areas of the body, such as the tailbone, will help improve your yoga practice.

Learn how you can avoid viruses and getting sick with this how to video. Amanda McQuade Crawford, medicinal herbalist and host of What a Relief! explains what a virus is and how to keep your immune system strong, naturally. Watch this tutorial and you will be healthier in no time.

A marrow is also called a zucchini or a squash. Watch this how to video as our host shows you how to cook up some homegrown marrow. Stuff the zucchini with minced meat for a meal that everyone will enjoy.

Grab some gloves and pick some nettle leaves from the wild. Nettle leaves tend to make a great addition to soups but tea? Watch this how to video as our host demonstrates how easy it is to make nettle tea.

In this how to video learn exactly what Thai yoga massage is and how it can benefit you. Our host will teach you the basics of this yoga massage technique that will help you with your energy lines.

In this how to video, host Meghan Carter discovers the essential facts about outdoor ceiling fan that you need to know before buying one for you home.

Watch as out hosts show you how to make a pinless nappy/diaper for a newborn baby. This method of folding reusable cloth diapers help to avoid irritating the naval area.

Meghan Carter visits Chef Jason Hill to discover the secret to creating beautiful and delicious edible centerpieces. Jason, host of the YouTube Channel Chef Tips, shared the essential elements for an attractive green and purple grape centerpiece as well as how to make something your guests will want to eat. You can also try creating the olive tower.

Watch as our host reveals his grandma's secret recipe and shows you how to make the perfect iced tea at home. You wont even need to boil any water.

For this who want to create an easy romantic hair style, then this is the video for you. Our host will show you how to create soft spiral curls using velcro rollers and a curling iron.

Sean Astin hosts AFI's filmmaking tutorial series, LIGHTS, CAMERA, EDUCATION! Here, we explore "The Pitch" or presenting your ideas for your film script.

This how to video will show how to pick up the gusset of a knitted sock. Our host will teach you how to do so with either a crochet hook or a knitting needles.

Suspended ceilings have come a long way from rice cake-looking panels supported by a metal frame. To show you how far suspended ceiling tiles have come and why they are so practical host Meghan Carter visited Armstrong to get a first-hand look at drop ceiling tiles.

Marble countertops look beautiful in any style kitchen or bathroom. To help you make the most of your money, host Meghan Carter visits Vermont Marble Museum to discover how to select the right marble countertops for you and how to protect them for staining.

In my first installment in this series on professional hacking tools, we downloaded and installed Metasploit, the exploitation framework. Now, we will begin to explore the Metasploit Framework and initiate a tried and true hack.

In this tutorial, Jenny Jones invites you into her bedroom to show you how to give yourself an easy, 6 step at-home facial. Keep your skin young and bright with these fantastic tips from America's favorite talk show host.

Elvira, Mistress of the Dark, was created in 1981 by Cassandra Peterson. She was the hostess of a local Hollywood horror movie show that became nationally syndicated. Elvira was the first horror host to be nationally syndicated, first person to be broadcast in 3-D on TV, and first female celebrity to do a national beer campaign and market her own beer.

Post-exploitation is often not quite as exciting as popping the initial shell, but it's a crucial phase for gathering data and further privilege escalation. Once a target is compromised, there's a lot of information to find and sift through. Luckily, there are tools available that can make the process easy. One such tool is Postenum.

While we haven't covered Amazon Web Services, or AWS, on Null Byte before, Amazon's cloud computing platform is ripe for attack by hackers, pentesters, and cybersecurity researchers. It's also an excellent cloud hosting service to build or use vulnerable-by-design AWS setups and frameworks.

While much of the world is currently in some form of quarantine due to the COVID-19 pandemic, augmented reality (AR) gives us all the opportunity to see virtual content while stuck in our homes.

You may not have thought of dorks as powerful, but with the right dorks, you can hack devices just by Googling the password to log in. Because Google is fantastic at indexing everything connected to the internet, it's possible to find files that are exposed accidentally and contain critical information for anyone to see.

EternalBlue was a devastating exploit that targeted Microsoft's implementation of the SMB protocol. Metasploit contains a useful module that will automatically exploit a target, as long as it's vulnerable. But what if we wanted to exploit this vulnerability without Metasploit holding our hand? It can be done using a Python file to exploit EternalBlue manually.

Particular vulnerabilities and exploits come along and make headlines with their catchy names and impressive potential for damage. EternalBlue is one of those exploits. Originally tied to the NSA, this zero-day exploited a flaw in the SMB protocol, affecting many Windows machines and wreaking havoc everywhere. Here, we will use EternalBlue to exploit SMB via Metasploit.

Giving up your Wi-Fi password can be giving up more control than you think. Because of the way Chromecast and other IoT devices communicate, anyone on the same Wi-Fi network as your device can often make it do whatever they want. With a script called "Cast All the Things," we can hijack a Chromecast to play nearly any kind of media with a single command in terminal.

If you've grown bored of day-to-day hacking and need a new toy to experiment with, we've compiled a list of gadgets to help you take password cracking and wireless hacking to the next level. If you're not a white hat or pentester yourself but have one to shop for, whether for a birthday, Christmas present, or other gift-giving reason, these also make great gift ideas.

If you're using a mobile device, it's a pretty safe bet that your apps are sending lots of information back and forth from their servers. To make sure there is no inappropriate data collection going on, it's worth setting up a web proxy to spy on this traffic, so you know exactly which apps are "phoning home" and when.

While there are a variety of privacy-focused search engines available like StartPage and DuckDuckGo, nothing can offer the complete trust offered by creating one's own search engine. For complete trust and security, Searx can be used as free metasearch engine which can be hosted locally and index results from over 70 different search engines.

Conducting phishing campaigns and hosting Metasploit sessions from a trusted VPS is important to any professional security researcher, pentester, or white hat hacker. However, the options are quite limited since most providers have zero-tolerance policies for any kind of hacking, good or bad. After researching dozens of products, we came out with 5 potentials that are ideal for Null Byte readers.
With the addition of the OpenSSH client and server in the Windows 10 Fall Creators Update, you no longer have to rely on third-party programs to open an SSH server and connect to a Windows machine. While still a beta feature, this represents a long-overdue update fulfilling a promise made back in 2015.

Whether you're white hat, black hat, or some shade in-between, navigating through a network is a core part of hacking. To do that, we need to be able to explore a network to discover the addresses of gateways, interfaces, and other attached devices. When ifconfig just isn't enough, you can steer your way around a network with a convenient tool called Ship, the script for everything IP.

Last week, augmented reality startup Proxy42 released Father.IO, a multiplayer game that turns any indoor or outdoor space into a laser tag arena.
Whether or not a microbe is successful at establishing an infection depends both on the microbe and the host. Scientists from Duke found that a single DNA change can allow Salmonella typhi, the bacteria that causes typhoid fever, to invade cells. That single genetic variation increased the amount of cholesterol on cell membranes that Salmonella and other bacteria use as a docking station to attach to a cell to invade it. They also found that common cholesterol-lowering drugs protected zebrafi...
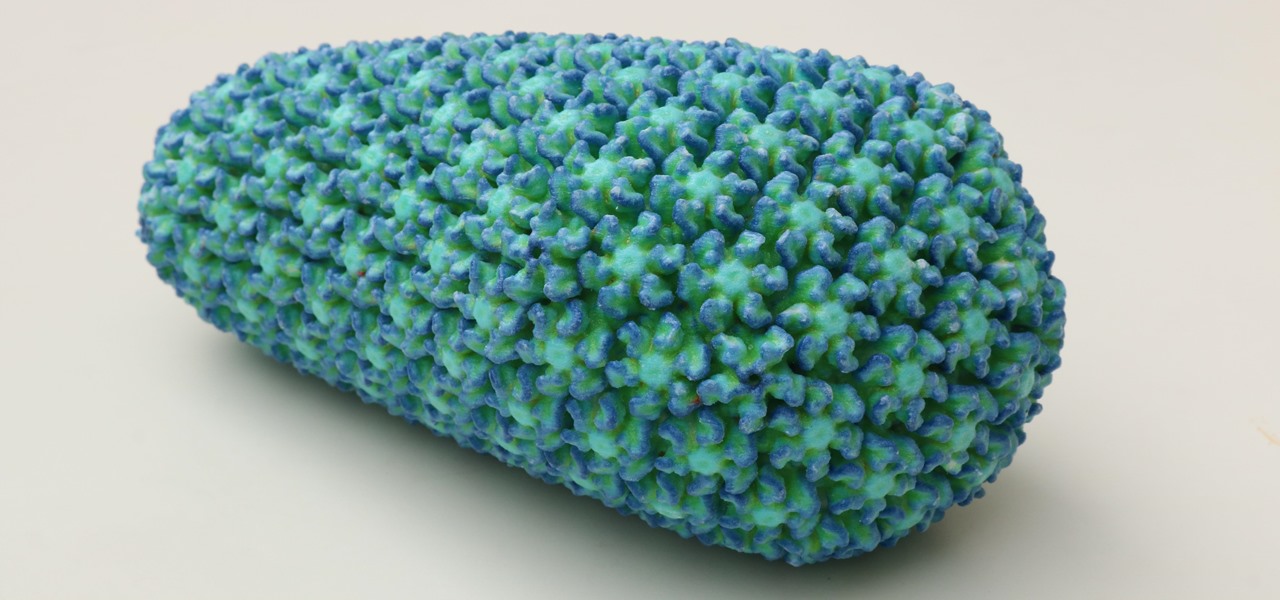
While some researchers look for drugs to treat HIV, other scientists delve deep into the virus itself for answers on how it causes infections.