My girlfriend was going away for a few weeks, but where she was going, there was no easily accessible Internet. She works mostly on the web, so it was imperative that she have a decent Internet connection during her travels. So, tethering her phone was the only real possibility.

Having a website people can easily navigate is common sense. It can save taxpayer dollars & help your agency achieve its mission. Here's how to dramatically improve your website by focusing on your customers' needs & adopting some basic usability techniques.

To make customizing a template as easy as possible, it is important that you pick a template that is closest to what you’re after, this includes the layout, the images and the color schemes. Keep this in mind.
Download Cheat Engine You can get Cheat Engine here. After downloading, install it on your computer.

Oily skin can make your makeup smear, disappear, and look greasy. Our celebrity makeup artist, Deborah Altizio, shows you how to apply makeup to oily skin in this video. Primer
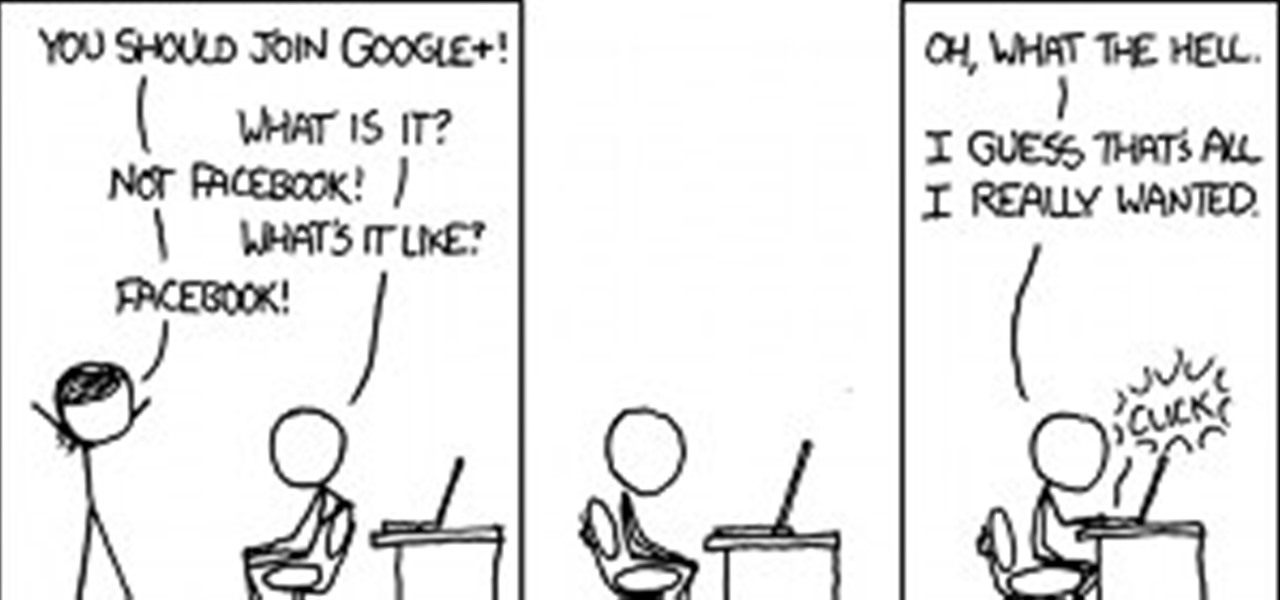
The visual beauty of images on Google+ means that it's not just a great place for photographers to shine, but also serves as a befitting promotional space for web comic artists. Below, 7 talented individuals who have utilized the Google+ platform.

We all want a faster, more efficient web browsing experience. Some immediately flocked to Google Chrome as soon as it was released, because of its super fast speeds. Others restrained themselves and continued to wait for Microsoft and Mozilla to play catchup. And the time is almost here for all Internet junkies to improve their game.

You've all probably heard about Apple's attempts to thwart iPhone 4 users from opening up their own devices, thanks to their sly maneuvers in switching out everyone's screws with those funky pentalobular screws. But one thing Apple will never learn— they will never have complete control. Where there's a will, there's a way. And if someone wants to fix their own iPhone or modify it slightly, they're going to do it, regardless of what screws bind it together.

To use an adjustable overcast foot on a sewing machine, watch this video sewing tutorial. It is ideal for stitching and finishing stretch fabrics or fabrics that unravel easily. Prevents seam from puckering, even when stitching wider seams. Turning the screw, adjust wire to seam width so needle swings over wire on right side. Stitch slowly with edge of fabric even with red guide and stitch going over wire. Use an adjustable overcast foot on a sewing machine.
In case you haven't figured out already, our government is always on the move to figure out new ways to extend their control. The CISPA, for one, is one of the best examples, along with "re-education" programs, and racial divide (Trayvon). What I've noticed in the past few months is that their new "ideas" are coming out at an increasingly alarming rate.

Watch out Macs. Flashback is back. Variations of the trojan have reportedly infected 600,000 Mac computers around the globe, with about 57 percent in the U.S. and another 20 percent in Canada.

In this article, I'll show you how to easily "hack" Facebook, Twitter, YouTube, and any number of similar account types with an Android app called FaceNiff.

If you've read my darknet series, you've probably got a pretty good idea of what I2P actually is and is capable of. One of the features of I2P is that it's designed with P2P file sharing in mind. Using a built-in service called I2PSnark, you can host and seed torrents quickly and easily!

In the last article, we left off with the Tor network and its hidden services. As I mentioned, Tor is not the only option in the game, and I want to offer a general introduction to I2P.

Welcome to the Mad Science World! Hold onto your radiation-shielded hard hats—we're going to be posting a ton of great how-to articles and videos every week, showcasing the maddest of the mad science experiments on the web. We hope you will be inspired to try these projects at home, but always remember—safety first!

Welcome to WTFoto, a community dedicated to scouring the internet for great WTF photos and encouraging you to do the same. Check out all of our upcoming weekly tutorials and competitions to learn how it's done and jump into the fray. Here's how we roll:

Eventually, we plan on doing some root the box competitions here at Null Byte, but we're still looking for a server to play on. Anyone want to donate one? You won't regret it. Root the box is like 'king of the hill', except you have to hack a server and maintain access. Each server will have numerous known security holes, but until then, let's get back to the regular weekly coding sessions and realistic hacking missions on HackThisSite.

Here's something fun for the Null Byte community to do—a coding competition! This week, I wanted to get everyone involved by offering you all a nice library of possible program types to choose from and try to code. At the end of this competition, all of the submitted programs will be reviewed by the community and myself. The coder that receives the most votes will be dubbed THE BEST.

We'd like this to be one of the last HTS mission announcements, at least for now. As soon as Null Byte finds a server to play with (anyone want to donate one?), we are going to start doing root the box competitions, which is like king of the hill, except you have to hack a server and maintain access. Each server will have numerous known security holes. But for now, back to the normal flow of things...

We're aiming for this to be one of the last HTS mission announcements, at least for now. As soon as Null Byte finds a server to play with, we are going to start doing root the box competitions, which is like king of the hill, except you have to hack a server and maintain access. Each server will have numerous known security holes. But, for now, back to the normal flow of things...

Hello and welcome to another InfoSecurity World tutorial. The intent of this article is to teach one how to encrypt sensitive files. When set up correctly with a strong password, it would be almost impossible to hack. Even the FBI have had issues decrypting this software. I'm here to teach you how to create a general encrypted container—not the complex hidden TrueCrypt volume.

I want to write this article because in my childhood, I had experienced internet stalking which ultimately ended in physical stalking which then lead to several attempted abductions. I have now learned how to use the internet safely, who to communicate with and I've learned how stalkers work.

Nikola Tesla. He was the man behind some of the greatest inventions of all time, including radio and alternating current. But perhaps his most visually fascinating invention is the Tesla coil. While maintaining a low current, it can produce dangerous high frequencies and voltages that can well exceed 1,000,000 volts, discharging it in the form of electrical arcs very similar to lightning.

The community tore up the first realistic mission last week. You've applied the techniques learned in the basic missions to a real scenario, so I'm pretty content. The realistic missions are where the learning gets intense and where we can apply real knowledge to extremely realistic situations. We will also be continuing the normal Python coding and hacking sessions. These sessions are created to bring our community together, to learn from each other, and grow together. Everyone is welcome, f...

As you may or may not know, MegaUpload - one of the largest file sharing services has been taken down by the feds.

Community byters, it's time to get serious. We are finally moving on to the realistic missions in HackThisSite. This is where the learning gets intense and where we can apply real knowledge to extremely realistic situations. We will also be continuing the normal Python coding and hacking sessions. These sessions are created to bring our community together, to learn from each other, and grow together. Everyone is welcome, from novice programmers to aspiring hackers.

We're officially seeking Null Byters on a weekly basis who would enjoy taking their time to educate the community. Contributors will write tutorials, which will be featured on the Null Byte blog, as well as the front page of WonderHowTo (if up to par, of course). This is a job meant for anyone with the will to share knowledge. There is no need to be intimidated if you fear you lack the writing skills. I will edit your drafts if necessary and get them looking top-notch! You can write tutorials...

This year's Consumer Electronics Show is nearing an end so of course it's an occasion for the 'best of' lists. To save you time I thought I'd compile my 'best of' the 'best of' lists.

There's a ton of videos on the web of musicians playing homemade PVC instruments, but I just recently stumbled upon the impressive work of PVC pipe player Kent Jenkins, aka Snubby J. His most recent video features a duet with his faux-twin, playing "Wizards in Winter" by the Trans-Siberian Orchestra. Turns out, he's been a PVC maestro for awhile now and even auditioned for his inspiration, the Blue Man Group, at the age of seventeen. Though he wasn't picked, they saw potential in him and aske...

Welcome to the 10th Community Byte session for coding in Python and completing the challenges presented to us by HackThisSite. These sessions are created to bring our community together, to learn from each other, and grow together. Everyone is welcome, from novice programmers to aspiring hackers.

We're officially seeking Null Byters interested in teaching others! Contributors will write tutorials, which will be featured on the Null Byte blog, as well as the front page of WonderHowTo (if up to par, of course). This is a job meant for anyone with the will to share knowledge. There is no need to be intimidated if you fear you lack the writing skills. I will edit your drafts if necessary and get them looking top-notch! You can write tutorials of any skill level, and anything you feel like...

We're continuing to deliver editing app tips, tricks and reviews-a-plenty here at Edit on a Dime. Let's look at what we talked about this week:

Welcome to the sixth Community Byte for coding in Python and beating the challenges presented to us by HackThisSite. These sessions are created to bring our community together, to learn from each other, and essentially grow together. Everyone is welcome, from novice programmers to aspiring hackers.

Get the New Google Navigation Menu Although Google introduced the new Google bar last week, I still didn't have the new look yet. I was curious to see if I could find it, and discovered that +Maximiliam Majewski found a workaround to get access to the new Google bar. It's no longer the black navigation bar at the top of the page, but rather a drop-down menu on the left-hand side, from the Google menu. Install a browser extension that allows you to edit the cookies.

Having an SSH or Secure SHell to tunnel your traffic through is something we have talked about many times at Null Byte. As we know, it allows us to securely route and encrypt our traffic through a remote server, effectively anonymizing us and protecting our traffic from all forms of analysis—simultaneously. We have gone over how to make a home SSH tunnel. However, the question has come up, "How can I get an SSH tunnel to somewhere other than my computer?" This would be useful in a situation w...

Since today (11/11/11) is the last 6 digit binary date this century, I thought we should look at some kinetic binary calculators.

Andrew Lipson builds sculptures based off of Mathematical objects using standard Lego bricks. He has built models of knots, Mobius strips, Klein bottles, Tori, Hoberman spheres (using Lego technic pieces), and recreations of M.C. Escher works.

Dungeon Defenders is finally out on the PC, Xbox 360, and PS3. We've previously featured the tower defense RPG, and if you haven't had a chance to check out the PAX interview with Trendy Entertainment, now would be a good time.

Cross-Site Request Forgery (CSRF, pronounce "sea-surf") is a common web exploit. However, for unknown reasons it's not used very often. It plays on a given website's trust in a web browser by executing another website's form action, for example, sending money to another person. It's usually placed in abnormal places like HTML image tags.

Have an HTC smartphone? Chances are that some of your stored personal data has been hijacked by malicious apps on your device. Android apps that have permission to access the Internet, which is pretty much every ad-supported app out there, can snag valuable information such as email addresses, location history, phone logs, text messages, and more.